STASH: Securing transparent authentication schemes using prover-side proximity verification
Transparent authentication (TA) schemes are those in which a user is authenticated by a verifier without requiring explicit user interaction. By doing so, those schemes promise high usability and security simultaneously. The majority of TA implementations rely on the received signal strength as an indicator for the proximity of a user device (prover). However, such implicit proximity verification is not secure against an adversary who can relay messages over a larger distance. In this paper, we propose a novel approach for thwarting relay attacks in TA schemes: the prover permits access to authentication credentials only if it can confirm that it is near the verifier. We present STASH, a system for relay-resilient transparent authentication in which the prover does proximity verification by comparing its approach trajectory towards the intended verifier with known authorized reference trajectories. Trajectories are measured using low-cost sensors commonly available on personal devices. We demonstrate the security of STASH against a class of adversaries and its ease-of-use by analyzing empirical data, collected using a STASH prototype. STASH is efficient and can be easily integrated to complement existing TA schemes.
💡 Research Summary
The paper introduces STASH, a novel approach to protect transparent authentication (TA) systems from relay attacks by moving proximity verification from the verifier to the prover. Traditional proximity‑based TA schemes, such as zero‑interaction authentication (ZIA), rely on radio‑signal strength (RSSI) or time‑of‑flight measurements to infer that a user’s device (P) is near a verifier (V). Because these measurements can be forged by an adversary who relays messages over a longer distance, the schemes are vulnerable to relay attacks.
STASH addresses this weakness by requiring the prover to confirm its own physical proximity to the intended verifier before releasing any authentication credentials. The prover does this by recording its approach trajectory using only on‑board inertial sensors (accelerometer and gyroscope). The raw sensor streams are transformed into a discrete sequence of primitives: “movement” (M) or “stationary” (S) and “left” (L) or “right” (R) turns. Turn detection runs at 20 Hz, using a sliding‑window standard‑deviation of the heading angle to identify turns with a precision of about 15°. Movement detection employs a logistic‑regression classifier that predicts motion every second; a hidden‑Markov‑model (HMM) with Viterbi smoothing refines the output into a stable M/S stream. The final primitive stream is a one‑dimensional string that is far more robust to sensor noise than full dead‑reckoning coordinates.
When a proximity‑verification session starts, the prover builds a “candidate” trajectory string for the current approach to V. This string is compared against a set of previously authorized “reference” trajectory strings stored locally on the device. The comparison uses the Needleman‑Wunsch (NW) algorithm, a hybrid of longest‑common‑subsequence and edit‑distance methods. The scoring scheme (match +1, mismatch ‑2, gap ‑1) yields a similarity score; if the score exceeds a decision threshold, the prover deems itself near V and proceeds with the challenge‑response protocol. If the score falls below the threshold, the user is prompted for explicit proximity confirmation (e.g., a button press). Successful explicit confirmation can be used to add the new candidate trajectory to the reference set, allowing the system to adapt to legitimate changes in user behavior.
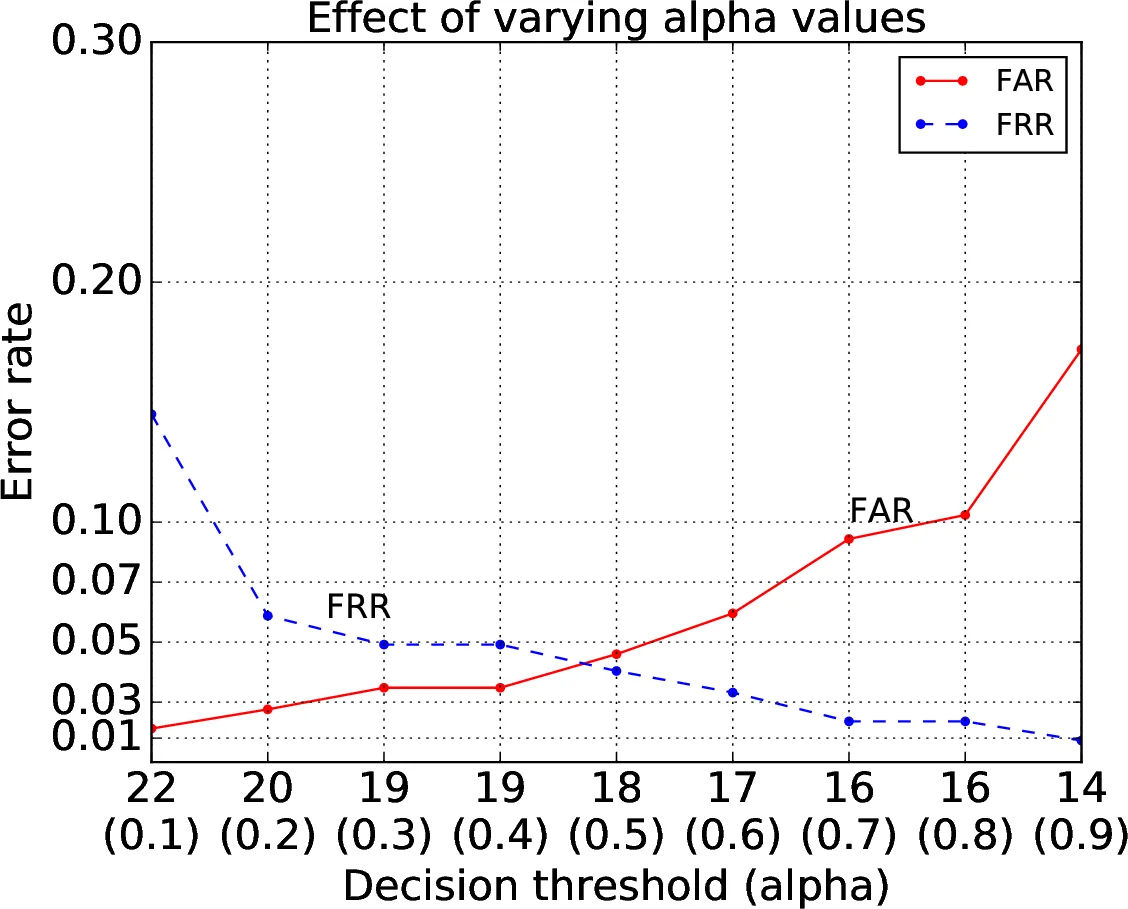
Threshold selection is critical because it balances usability (false‑reject rate, FRR) against security (false‑accept rate, FAR). STASH starts with an initial threshold derived from offline experiments. During operation, it collects both successful and failed comparison outcomes to compute a “local” threshold for each reference path, based on within‑class and between‑class similarity distributions. To avoid over‑fitting when only a few samples are available, the final “mixed” threshold is a convex combination of the initial and local thresholds, weighted by a confidence factor λ = (n‑1)/n, where n is the number of observed instances of that path. This scheme gradually increases confidence as more data are gathered.
The authors implemented STASH as an Android application. To conserve power, the app puts the device to sleep after five minutes of inactivity and acquires a wake‑lock only when significant motion is detected. The prototype continuously streams raw accelerometer and gyroscope data, extracts primitives, and performs NW similarity calculations locally, requiring no network or cloud resources.
Evaluation was conducted with 20 distinct routes (totaling 123 km) collected in two cities by multiple participants using a bicycle‑mounted device. The results show an FRR of roughly 5 % and an FAR of about 2 %, indicating that legitimate users are rarely blocked while relay attacks are effectively thwarted. Energy measurements reveal that STASH consumes only 4–7 % of a typical smartphone battery over an eight‑hour workday, and the computational latency per verification is on the order of tens of milliseconds.
The paper discusses limitations, such as reduced accuracy for highly dynamic motions (e.g., car driving) and the possibility of sensor‑spoofing attacks. Future work is suggested in the direction of multi‑sensor fusion (magnetometer, barometer) and advanced machine‑learning based anomaly detection to further harden the system.
In summary, STASH demonstrates that low‑cost MEMS inertial sensors can provide a reliable, privacy‑preserving, and deployable proximity verification mechanism for transparent authentication. By shifting the trust anchor to the prover and using trajectory‑based string similarity, STASH eliminates the fundamental relay‑attack vulnerability of RSSI‑ or TOF‑based schemes while maintaining the usability and efficiency required for real‑world adoption.
Comments & Academic Discussion
Loading comments...
Leave a Comment