WhatsApp security and role of metadata in preserving privacy
WhatsApp messenger is arguably the most popular mobile app available on all smart-phones. Over one billion people worldwide for free messaging, calling, and media sharing use it. In April 2016, WhatsApp switched to a default end-to-end encrypted service. This means that all messages (SMS), phone calls, videos, audios, and any other form of information exchanged cannot be read by any unauthorized entity since WhatsApp. In this paper we analyze the WhatsApp messaging platform and critique its security architecture along with a focus on its privacy preservation mechanisms. We report that the Signal Protocol, which forms the basis of WhatsApp end-to-end encryption, does offer protection against forward secrecy, and MITM to a large extent. Finally, we argue that simply encrypting the end-to-end channel cannot preserve privacy. The metadata can reveal just enough information to show connections between people, their patterns, and personal information. This paper elaborates on the security architecture of WhatsApp and performs an analysis on the various protocols used. This enlightens us on the status quo of the app security and what further measures can be used to fill existing gaps without compromising the usability. We start by describing the following (i) important concepts that need to be understood to properly understand security, (ii) the security architecture, (iii) security evaluation, (iv) followed by a summary of our work. Some of the important concepts that we cover in this paper before evaluating the architecture are - end-to-end encryption (E2EE), signal protocol, and curve25519. The description of the security architecture covers key management, end-to-end encryption in WhatsApp, Authentication Mechanism, Message Exchange, and finally the security evaluation. We then cover importance of metadata and role it plays in conserving privacy with respect to whatsapp.
💡 Research Summary
The paper provides a comprehensive examination of WhatsApp’s security architecture, focusing on the end‑to‑end encryption (E2EE) that has been mandatory since April 2016 and the role of metadata in preserving—or undermining—user privacy. It begins by introducing essential cryptographic concepts such as the Signal Protocol, the X3DH key‑agreement scheme, the Double Ratchet algorithm, and the use of Curve25519 for elliptic‑curve Diffie‑Hellman operations. These components together enable WhatsApp to generate a unique session key for each conversation, to rotate keys after every message, and to provide forward secrecy: even if a long‑term private key is later compromised, previously exchanged messages remain unreadable.
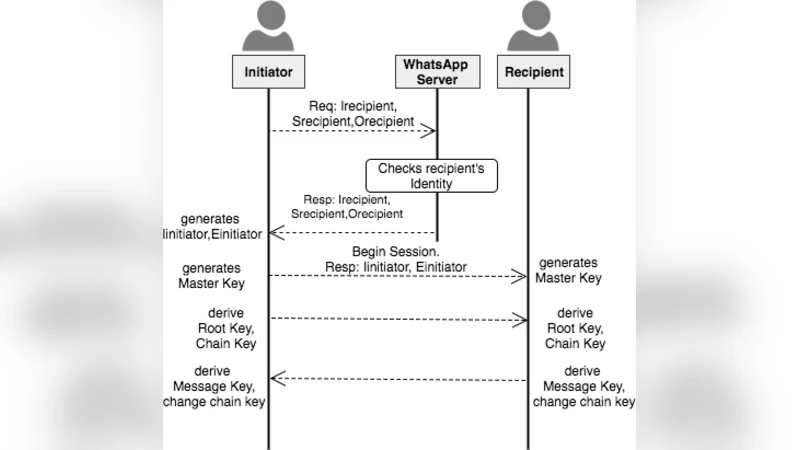
The authors dissect WhatsApp’s key‑management workflow. When a user registers, the client generates a long‑term identity key pair and a signed pre‑key bundle (including a one‑time pre‑key). The bundle is uploaded to WhatsApp’s server. During the first message exchange, the sender retrieves the recipient’s bundle, performs an X3DH exchange, and derives a shared secret that seeds the Double Ratchet. Subsequent messages are encrypted with AES‑256‑CTR and authenticated with HMAC‑SHA‑256. The paper notes that this design offers strong protection against man‑in‑the‑middle (MITM) attacks provided the user verifies the safety number (key fingerprint). In practice, however, most users never perform this verification, leaving the initial key exchange vulnerable to a “trust‑on‑first‑use” (TOFU) attack where a malicious server could substitute a forged pre‑key.
Group chat security is examined in detail. WhatsApp employs a “Sender Keys” mechanism: a single symmetric key is generated by the group creator, encrypted with each member’s public key, and distributed to the group. While this approach reduces computational overhead, it creates a single point of failure. When a participant leaves or a new member joins, the sender key must be regenerated and redistributed. The paper highlights that delayed or incomplete key rotation can expose past messages to newly added members, weakening forward secrecy within groups.
Beyond message content, the authors argue that privacy cannot be guaranteed solely by encrypting the communication channel. WhatsApp retains extensive metadata—including sender and receiver phone numbers, timestamps, message sizes, and server‑side connection logs—in plaintext. Even though the server cannot read message bodies, this metadata can be correlated to reconstruct social graphs, infer user habits, and potentially de‑anonymize individuals. The paper cites academic work showing that metadata alone can reveal more about a user’s identity than the encrypted content.
To address these shortcomings, the authors propose several technical and policy‑level mitigations:
- Metadata Encryption or Pseudonymisation – Adopt protocols such as DC‑nets or Private Information Retrieval (PIR) to hide routing information, or replace phone numbers with temporary identifiers that are periodically refreshed.
- Enhanced Group Key Management – Replace the single‑sender‑key model with a multi‑key scheme where each participant holds a distinct encryption key, enabling immediate re‑keying when membership changes.
- Server‑Side Log Minimisation – Enforce strict data‑retention policies that automatically purge connection logs after a short, predefined window, and store only cryptographic hashes of identifiers rather than raw numbers.
- User‑Centred Transparency – Provide clear UI elements that disclose what metadata is collected, allow users to opt‑out of certain logging features, and present the safety numbers in an easily verifiable format.
The paper concludes that WhatsApp’s adoption of the Signal Protocol places it among the most secure consumer messaging platforms available today. Nevertheless, the reliance on TOFU for initial key verification, the simplistic group‑key distribution, and the unencrypted handling of metadata constitute notable privacy gaps. By implementing the suggested enhancements, WhatsApp could move from “secure messaging” to a truly privacy‑preserving communication service without sacrificing the usability that has driven its massive global adoption.
Comments & Academic Discussion
Loading comments...
Leave a Comment