Dandelion: Redesigning the Bitcoin Network for Anonymity
Bitcoin and other cryptocurrencies have surged in popularity over the last decade. Although Bitcoin does not claim to provide anonymity for its users, it enjoys a public perception of being a `privacy-preserving’ financial system. In reality, cryptocurrencies publish users’ entire transaction histories in plaintext, albeit under a pseudonym; this is required for transaction validation. Therefore, if a user’s pseudonym can be linked to their human identity, the privacy fallout can be significant. Recently, researchers have demonstrated deanonymization attacks that exploit weaknesses in the Bitcoin network’s peer-to-peer (P2P) networking protocols. In particular, the P2P network currently forwards content in a structured way that allows observers to deanonymize users. In this work, we redesign the P2P network from first principles with the goal of providing strong, provable anonymity guarantees. We propose a simple networking policy called Dandelion, which achieves nearly-optimal anonymity guarantees at minimal cost to the network’s utility. We also provide a practical implementation of Dandelion.
💡 Research Summary
The paper addresses a fundamental privacy weakness in Bitcoin and many other cryptocurrencies: although transactions are recorded on a public ledger under pseudonymous public keys, the network‑level propagation of those transactions leaks information that can link a public key to the originating IP address. Existing deanonymization attacks exploit the symmetric diffusion protocol used by the Bitcoin peer‑to‑peer (P2P) layer, where each node forwards a newly received transaction to all of its neighbors after an independent exponential delay. By monitoring a modest fraction of the network (the “super‑node” attack), researchers have shown that the source of a transaction can be identified with up to 30 % accuracy, and the authors argue that more sophisticated estimators could do even better.
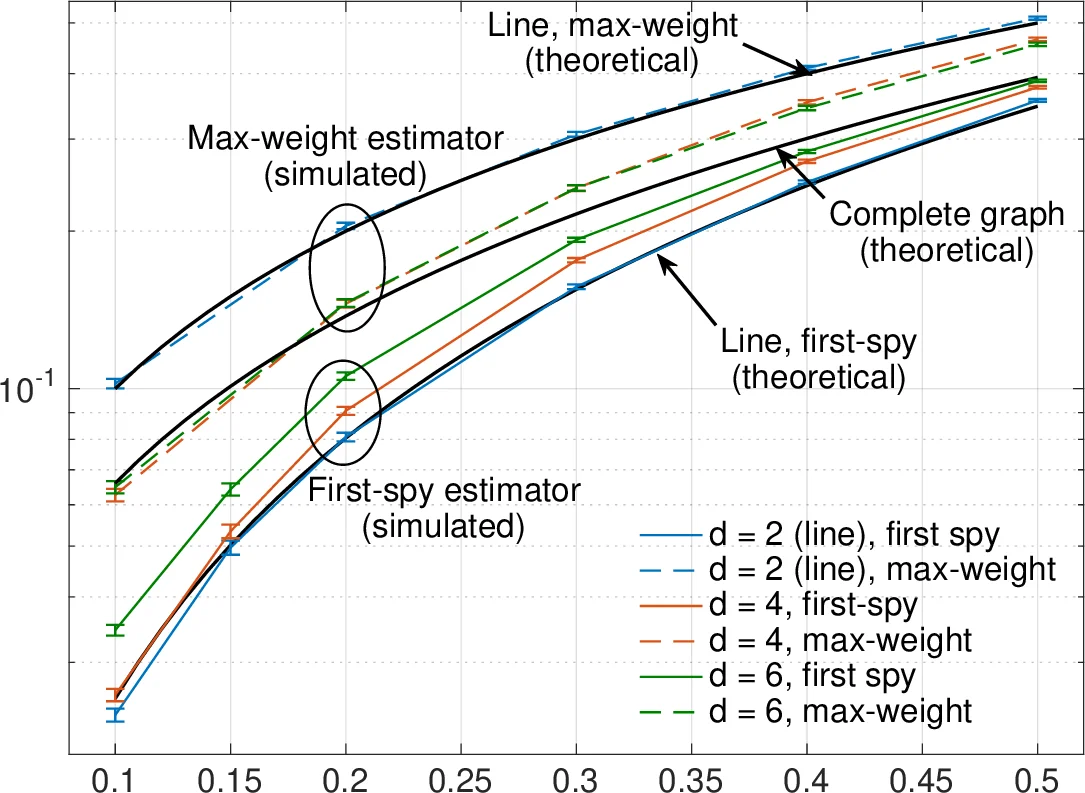
To reason about anonymity in a principled way, the authors introduce two metrics: precision (the probability that a node identified as the source is indeed the true source) and recall (the probability that the true source is identified at all). They model the Bitcoin network as a random 16‑regular graph of server nodes, assume a fraction p of nodes are colluding adversaries, and derive fundamental lower bounds on the achievable (precision, recall) pairs for any propagation protocol. These bounds are visualized as red and blue lines in Figure 1; any protocol’s achievable region must intersect the shaded area between them. The standard diffusion protocol lies far from the lower bound, offering high recall but low precision.
The core contribution is Dandelion, a two‑phase propagation scheme designed to approach the theoretical lower bound while preserving low latency. In the first “stem” phase, each transaction is forwarded along a single randomly chosen line (a directed path) for a random number of hops, after which it enters the second “fluff” phase where it is broadcast using the usual diffusion mechanism. The stem phase hides the source because only one neighbor receives the message at each hop, preventing the adversary from observing the branching pattern that reveals the origin. The fluff phase ensures that the transaction still reaches the entire network quickly, keeping latency comparable to diffusion.
The authors prove that Dandelion’s achievable (precision, recall) region lies on the Pareto frontier of the theoretical limits, i.e., it is nearly optimal: no other protocol can simultaneously achieve better precision for a given recall. They also discuss practical issues such as avoiding loops and ensuring that all transactions share the same underlying line graph without exposing its structure to adversaries. Their solution builds the line graph as a random subgraph of the underlying 16‑regular network and periodically rewires it to prevent long‑term learning by attackers.
Implementation challenges are addressed in Section 6. Constructing and maintaining the line graph in a fully distributed manner requires nodes to exchange limited topology information while preventing adversarial nodes from learning the full line. The authors propose simple heuristics: (a) each node periodically selects a new “stem” neighbor uniformly at random from its outgoing connections, (b) a lightweight “watchdog” mechanism detects suspicious patterns that could reveal the line, and (c) a small extension to the Bitcoin message header distinguishes stem from fluff messages, preserving compatibility with existing clients. Using a snapshot of the 2015 Bitcoin server network, they simulate Dandelion and compare it with pure diffusion. The results show that Dandelion reduces recall to roughly 5–10 % of the diffusion baseline while increasing average propagation delay by only about 20 % (≈1.2×), demonstrating a favorable trade‑off between anonymity and performance.
In the broader context, Dandelion complements higher‑layer privacy techniques such as coin mixing, CoinJoin, or Tor routing, which protect transaction contents but not network‑level metadata. By mitigating the source‑linkage attack at the P2P layer, Dandelion can be combined with these methods to provide end‑to‑end anonymity. The paper concludes with open problems, including adaptive adversaries that may try to infer the line graph over time, optimal parameter selection for the stem length distribution, and real‑world deployment considerations.
Overall, the work offers a rigorous theoretical framework for anonymity in cryptocurrency networks, proposes a practically implementable protocol that nearly attains the theoretical optimum, and validates its effectiveness through simulation on realistic network topologies. Dandelion represents a significant step toward privacy‑preserving P2P designs for Bitcoin and its many derivatives.
Comments & Academic Discussion
Loading comments...
Leave a Comment