High-Assurance Separation Kernels: A Survey on Formal Methods
Separation kernels provide temporal/spatial separation and controlled information flow to their hosted applications. They are introduced to decouple the analysis of applications in partitions from the analysis of the kernel itself. More than 20 implementations of separation kernels have been developed and widely applied in critical domains, e.g., avionics/aerospace, military/defense, and medical devices. Formal methods are mandated by the security/safety certification of separation kernels and have been carried out since this concept emerged. However, this field lacks a survey to systematically study, compare, and analyze related work. On the other hand, high-assurance separation kernels by formal methods still face big challenges. In this paper, an analytical framework is first proposed to clarify the functionalities, implementations, properties and standards, and formal methods application of separation kernels. Based on the proposed analytical framework, a taxonomy is designed according to formal methods application, functionalities, and properties of separation kernels. Research works in the literature are then categorized and overviewed by the taxonomy. In accordance with the analytical framework, a comprehensive analysis and discussion of related work are presented. Finally, four challenges and their possible technical directions for future research are identified, e.g. specification bottleneck, multicore and concurrency, and automation of full formal verification.
💡 Research Summary
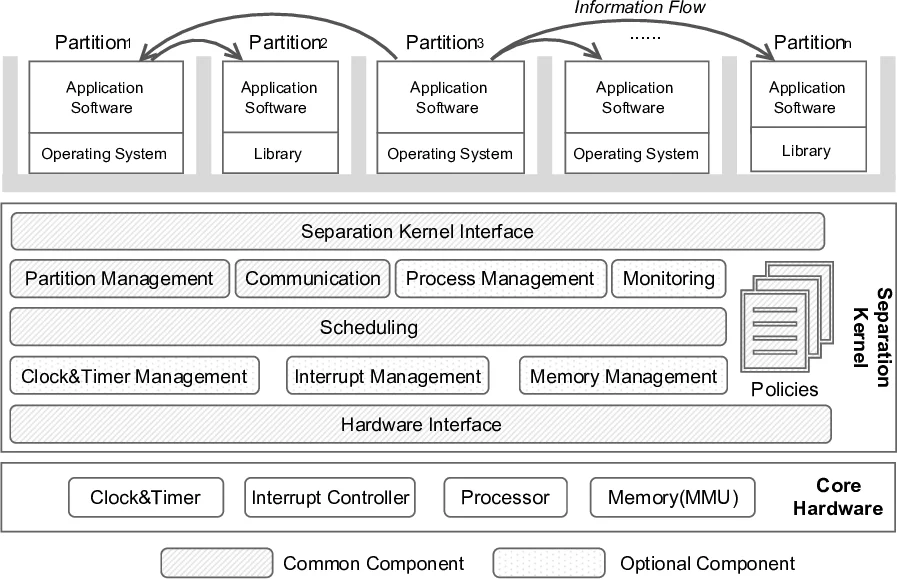
The paper presents the first comprehensive survey of formal methods applied to high‑assurance separation kernels, a class of minimal operating system kernels that enforce spatial and temporal isolation between partitions and control information flow. Recognizing that safety‑critical (DO‑178C) and security‑critical (Common Criteria, SKPP) certifications mandate the use of formal techniques, the authors first construct an analytical framework that structures the domain along four dimensions: (1) concepts and reference architecture, (2) implementations, (3) critical properties and standards, and (4) formal‑methods application schema. The reference architecture distinguishes common components (hardware interface, partition management, policy enforcement, communication, etc.) from optional extensions (advanced scheduling, fault‑tolerance, etc.), and clarifies the relationships among security kernels, separation kernels, partitioning kernels, micro‑kernels, and embedded hypervisors.
Using this framework, the authors compile a comparative table of twenty separation‑kernel implementations, both commercial (e.g., PikeOS, VxWorks MILS, INTEGRITY) and academic (e.g., seL4, XtratuM, Muen, PROSPER). The survey shows that most kernels are under 10 kLOC, are written in C with some assembly, support multiple ISAs (ARM, PowerPC, SP‑ARC) and increasingly target multicore platforms. Open‑source projects are predominantly academic, while commercial products tend to be closed source.
The core contribution is a taxonomy that first classifies works by the stage of formal‑methods application—formal specification, formal modeling, formal verification, and formal code generation—and then refines the classification by the architectural components and the security/safety properties they address (e.g., memory isolation, scheduling, information‑flow control). This taxonomy enables a systematic mapping of existing literature: seL4, for instance, provides a full pipeline from Isabelle/HOL specification through machine‑checked proofs to verified code; XtratuM and Muen combine B‑Method or Coq with model‑checking for core kernels but leave real‑time scheduling largely informal; many commercial kernels formalize policies and interfaces but rely on manual proof effort for the kernel core.
The analysis highlights several gaps. First, a “specification bottleneck” exists because writing precise, machine‑checkable policies and real‑time schedules is labor‑intensive. Second, most formal work targets single‑core models, leaving multicore concurrency, memory‑consistency, and interrupt handling under‑explored. Third, full automation of verification is lacking; proof assistants still require substantial expert interaction. Fourth, there is no mature end‑to‑end pipeline that guarantees traceability from formal specification through to generated binary code, which hampers certification efficiency.
To address these challenges, the authors propose four research directions: (a) develop domain‑specific specification languages or DSLs for policies and schedules to reduce authoring effort; (b) extend modeling frameworks (e.g., TLA+, Isabelle/HOL) with explicit multicore semantics and integrate model‑checking for concurrency; (c) enhance proof automation by tighter integration with SMT solvers and automated theorem provers, reducing manual proof steps; (d) build formally verified compilers or code‑generation toolchains (e.g., SPARK→Ada, Coq→C) that preserve correctness guarantees from specification to executable code.
In conclusion, the paper delivers a structured overview of the state‑of‑the‑art in formal methods for separation kernels, provides a useful taxonomy for researchers and practitioners, and outlines concrete technical avenues to overcome current limitations, thereby charting a roadmap toward fully verified, multicore‑capable, high‑assurance separation kernels suitable for future safety‑ and security‑critical systems.
Comments & Academic Discussion
Loading comments...
Leave a Comment