SGXIO: Generic Trusted I/O Path for Intel SGX
Application security traditionally strongly relies upon security of the underlying operating system. However, operating systems often fall victim to software attacks, compromising security of applications as well. To overcome this dependency, Intel introduced SGX, which allows to protect application code against a subverted or malicious OS by running it in a hardware-protected enclave. However, SGX lacks support for generic trusted I/O paths to protect user input and output between enclaves and I/O devices. This work presents SGXIO, a generic trusted path architecture for SGX, allowing user applications to run securely on top of an untrusted OS, while at the same time supporting trusted paths to generic I/O devices. To achieve this, SGXIO combines the benefits of SGX’s easy programming model with traditional hypervisor-based trusted path architectures. Moreover, SGXIO can tweak insecure debug enclaves to behave like secure production enclaves. SGXIO surpasses traditional use cases in cloud computing and makes SGX technology usable for protecting user-centric, local applications against kernel-level keyloggers and likewise. It is compatible to unmodified operating systems and works on a modern commodity notebook out of the box. Hence, SGXIO is particularly promising for the broad x86 community to which SGX is readily available.
💡 Research Summary
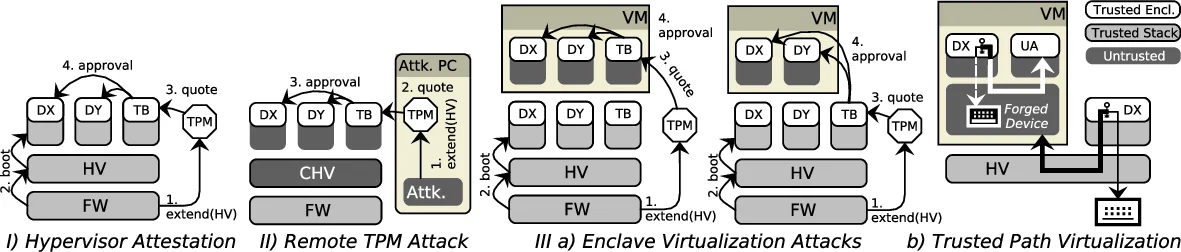
The paper introduces SGXIO, a novel architecture that augments Intel Software Guard Extensions (SGX) with a lightweight trusted hypervisor to provide generic trusted I/O paths for user applications running on an untrusted operating system. While SGX offers strong memory isolation and attestation, it lacks mechanisms to protect user input and output devices such as keyboards, displays, and USB peripherals. Existing solutions either rely on proprietary paths like Intel’s Protected Audio Video Path (PAVP), which are device‑specific and opaque, or require a full‑blown trusted OS, inflating the trusted computing base (TCB).
SGXIO’s design goal is to keep the OS completely untrusted, let SGX handle enclave creation, verification, and sealing, and delegate all device‑level protection to a minimal hypervisor. The hypervisor owns exclusive control over physical I/O devices, configures the IOMMU to block unauthorized DMA, and routes interrupts only to authenticated enclaves. Communication between an enclave and the hypervisor uses SGX’s ECALL/OCALL mechanism, extended with a secure request/response protocol that encrypts payloads and authenticates the hypervisor before granting device access.
A key contribution is the “debug‑enclave tweak”: SGX distinguishes debug and production enclaves via a launch token signed by Intel‑controlled launch enclaves. SGXIO’s hypervisor intercepts token generation and clears the debug flag, allowing developers to use debug enclaves during development while ensuring they behave indistinguishably from production enclaves at runtime. This eliminates the need for costly Intel licensing for production deployment.
The authors also propose a zero‑overhead, non‑interactive key‑exchange protocol for establishing a 128‑bit symmetric key between two local enclaves. The protocol embeds random data in SGX’s local attestation report, uses the report’s signature as proof of enclave identity, and derives the shared key without any external key‑distribution infrastructure.
The threat model assumes a powerful adversary who controls the OS, can launch arbitrary kernel modules, and may attempt DMA or interrupt spoofing, but does not have physical access to the user’s peripherals. Under this model, SGXIO guarantees confidentiality and integrity of I/O data: the hypervisor’s exclusive device ownership prevents the OS from reading or tampering with input events, while SGX’s memory encryption protects enclave state from the OS. Both the user and a remote party (e.g., a bank) can verify the integrity of the trusted path through remote attestation of the hypervisor and the enclave.
Implementation on a modern Skylake notebook demonstrates that SGXIO works with unmodified operating systems and commodity hardware. Performance measurements show only microsecond‑scale overhead for enclave‑hypervisor I/O calls and key exchange, making the solution suitable for interactive applications such as secure document viewers, password managers, and online banking clients.
In summary, SGXIO bridges a critical gap in SGX’s security model by delivering a generic, low‑TCB trusted I/O path without requiring proprietary hardware or a full trusted OS. It enables a wide range of user‑centric security applications to protect against kernel‑level keyloggers and other malware, while preserving SGX’s easy programming model and attestation capabilities. The work paves the way for broader adoption of SGX‑based protection in everyday desktop environments.
Comments & Academic Discussion
Loading comments...
Leave a Comment