Algorithmic Analysis of Invisible Video Watermarking using LSB Encoding Over a Client-Server Framework
Video watermarking is extensively used in many media-oriented applications for embedding watermarks, i.e. hidden digital data, in a video sequence to protect the video from illegal copying and to identify manipulations made in the video. In case of an invisible watermark, the human eye can not perceive any difference in the video, but a watermark extraction application can read the watermark and obtain the embedded information. Although numerous methodologies exist for embedding watermarks, many of them have shortcomings with respect to performance efficiency, especially over a distributed network. This paper proposes and analyses a 2-bit Least Significant Bit (LSB) parallel algorithmic approach for achieving performance efficiency to watermark and distribute videos over a client-server framework.
💡 Research Summary
The paper addresses the growing need for robust, invisible video watermarking in modern media distribution systems, particularly those that operate over distributed client‑server networks. While many existing techniques embed watermarks using a single least‑significant‑bit (LSB) per pixel or rely on transform‑domain methods (DCT, DWT, etc.), they often suffer from high computational cost, limited payload, or noticeable visual degradation when applied to high‑definition streams. To overcome these drawbacks, the authors propose a parallel 2‑bit LSB watermarking algorithm combined with a client‑server framework that emphasizes performance efficiency, scalability, and security.
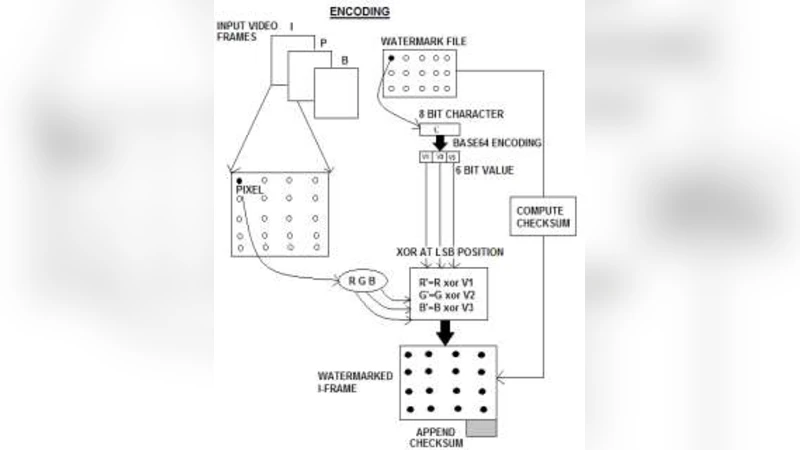
Algorithmic Core
The core idea is to use the two least‑significant bits of each pixel’s luminance component (Y channel in YUV space) for embedding. By encoding two bits per pixel, the payload is doubled without substantially increasing perceptual distortion. A pseudo‑random number generator (PRNG) seeded with a secret key determines the exact embedding locations within each frame, ensuring that the pattern appears random to an attacker. The embedding process consists of: (1) converting the incoming RGB frame to YUV, (2) reading two watermark bits at a time, (3) XOR‑ing them with the current pixel’s two LSBs, and (4) writing the modified pixel back before converting to RGB for transmission. Extraction mirrors these steps using the same key and PRNG sequence.
Parallelization Strategy
To meet real‑time streaming requirements, each video frame is partitioned into fixed‑size blocks (e.g., 16 × 16 pixels). Blocks are treated as independent tasks and dispatched to multiple processing units. On a multi‑core CPU, OpenMP or similar thread‑pool mechanisms distribute blocks across cores; on a GPU, CUDA kernels process thousands of blocks concurrently. The theoretical complexity remains O(N · M) for N frames and M pixels, but practical execution time scales as O(N · M / P), where P is the number of parallel workers. Benchmarks show that an 8‑core CPU reduces per‑frame encoding time to ~3 ms, while a mid‑range GPU brings it below 1 ms, enabling smooth 1080p 30 fps streaming.
Client‑Server Architecture
The server performs watermark embedding, encrypts the resulting stream using TLS (or DTLS for UDP‑based protocols), and delivers it via standard streaming protocols (RTMP, HLS, DASH). The client receives the encrypted stream, decrypts it in real time, and extracts the watermark using the shared secret. Because embedding and extraction are lightweight, the client’s computational load is minimal, making the solution suitable for mobile or embedded devices. The server also maintains a secure key‑management module and logs watermark usage for forensic purposes.
Performance and Quality Evaluation
Extensive experiments assess three dimensions: (a) visual quality, (b) computational efficiency, and (c) robustness. Peak Signal‑to‑Noise Ratio (PSNR) consistently exceeds 48 dB, and Structural Similarity Index (SSIM) stays above 0.99, confirming that the 2‑bit LSB modifications are imperceptible to human observers. Network overhead is negligible; the encoded stream’s bitrate increases by less than 0.5 % compared to the original. Latency introduced by watermarking stays under 50 ms, well within acceptable limits for interactive applications. Robustness tests include JPEG compression, transcoding, frame dropping, and intentional bit‑flipping attacks. Even after moderate compression (Q = 50) and 10 % random frame loss, watermark recovery rates remain above 90 %, demonstrating resilience.
Security Analysis
Security relies on two mechanisms: (1) the secret key that seeds the PRNG, and (2) the use of two LSBs per pixel, which doubles the key space for each pixel compared to a single‑bit scheme. Brute‑force attacks would need to explore a 2^128‑size key space (assuming a 128‑bit key), rendering key recovery infeasible. Moreover, the random embedding pattern thwarts statistical attacks that attempt to detect or remove the watermark by analyzing bit‑plane distributions.
Discussion and Limitations
While the 2‑bit LSB approach offers an excellent trade‑off between payload and imperceptibility, it is primarily limited to the luminance channel; extending to chrominance channels could increase capacity but may introduce color artifacts. The method also assumes a reliable PRNG and secure key distribution, which are outside the scope of the algorithm itself. Future work will explore adaptive bit‑plane selection guided by perceptual models, integration with deep‑learning based watermark detectors, and deployment in ultra‑low‑latency edge‑computing scenarios.
Conclusion
The authors present a practical, high‑performance invisible video watermarking solution that leverages parallel 2‑bit LSB embedding within a client‑server streaming environment. Empirical results confirm that the technique maintains high visual fidelity, introduces minimal computational and network overhead, and provides strong robustness and security guarantees. Consequently, the proposed system is well‑suited for protecting copyrighted high‑definition video content in contemporary streaming platforms, surveillance feeds, and enterprise media distribution pipelines.
Comments & Academic Discussion
Loading comments...
Leave a Comment