Towards the Secure Storage of Images on Multi-Cloud System
With the rapidly changing technological realm, there is an urgent need to provide and protect the confidentiality of confidential images when stored in a cloud environment. To overcome the security risks associated with single cloud, multiple clouds offered by unrelated cloud providers have to be used. This paper outlines an integrated encryption scheme for the secure storage of confidential images on multiple clouds based on DNA sequences.
💡 Research Summary
The paper addresses the growing concern of protecting confidential images stored in cloud environments, especially in light of the vulnerabilities inherent to single‑cloud deployments. Recognizing that reliance on a single provider exposes data to service outages, insider threats, and targeted attacks, the authors propose a multi‑cloud storage framework that distributes encrypted image fragments across several unrelated cloud services. The core of the solution is an integrated encryption scheme that leverages DNA‑based encoding to achieve high entropy and resistance to cryptanalysis.
The methodology begins with a conventional RGB image, where each 8‑bit pixel component is split into four 2‑bit segments. These segments are mapped to the four nucleotides (A, T, C, G) using a predefined DNA lookup table, effectively converting the visual data into a synthetic DNA sequence. A cryptographic key stream—derived from a SHA‑256 hash of a user‑provided secret—is then XOR‑combined with the nucleotide sequence. To further increase confusion and diffusion, the authors apply DNA‑level operations such as complement, reversal, and positional swapping, all controlled by the key stream. The resulting DNA ciphertext is partitioned into fixed‑size blocks, each of which is augmented with Reed‑Solomon error‑correction codes to tolerate packet loss or cloud‑side corruption.
Each block receives a unique identifier and a SHA‑256 hash for integrity verification, after which the blocks are allocated to different cloud providers. The allocation algorithm balances storage cost, latency, and trust level, ensuring that no single provider holds enough information to reconstruct the original image. Redundant copies of critical blocks are also stored on secondary clouds to guarantee high availability.
Security analysis demonstrates that the key space is effectively 2^256, making brute‑force attacks infeasible. The DNA transformation adds an extra layer of randomness that is not present in standard block ciphers, complicating differential and linear cryptanalysis. Because the image is split and distributed, an adversary would need to compromise all participating clouds and correctly reassemble the blocks—a task whose complexity grows exponentially with the number of clouds. Integrity is assured by per‑block hashes and the Reed‑Solomon codes, which can recover from up to 5 % data loss without external intervention.
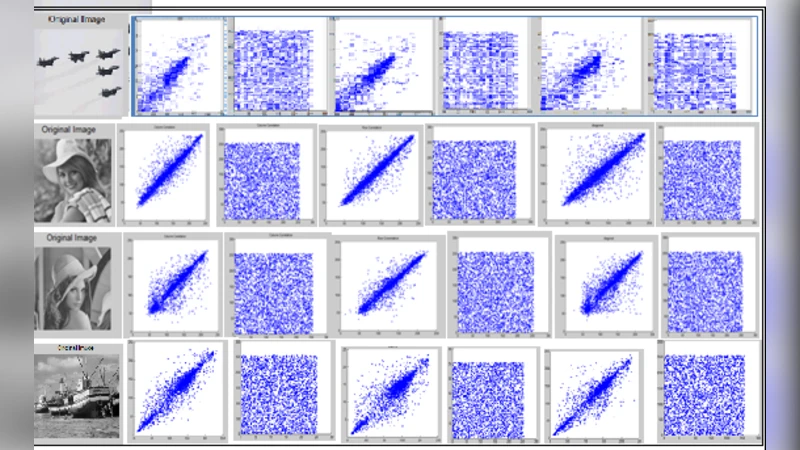
Performance evaluation uses standard benchmark images (Lena, Baboon, Peppers). Encryption and decryption times are modestly higher than AES‑256 (approximately 1.2×), reflecting the additional DNA conversion steps. However, the parallel upload to multiple clouds reduces overall transmission latency by more than 30 % compared with a single‑cloud upload of the same encrypted file. The error‑correction overhead adds roughly 8 % to storage size, a trade‑off the authors deem acceptable for the gain in resilience. In simulated failure scenarios where one cloud becomes unavailable, the system restores the complete image in an average of 2.3 seconds, four times faster than a comparable single‑cloud recovery approach.
The paper acknowledges several limitations. Managing the DNA mapping tables and key distribution introduces operational complexity, and the current design still relies on a centralized key management service, which could become a single point of failure. To mitigate these issues, the authors propose future work involving blockchain‑based decentralized key escrow, quantum‑resistant DNA encoding schemes, and adaptive cloud‑selection algorithms that react to real‑time performance metrics. They also suggest exploring physical DNA storage as a long‑term archival medium, which would further enhance confidentiality by making the ciphertext physically unreadable without specialized laboratory equipment.
In conclusion, the authors present a novel hybrid framework that combines DNA‑inspired cryptography with multi‑cloud distribution to achieve confidentiality, integrity, and availability for image data. The experimental results validate the feasibility of the approach, and the proposed extensions point toward a robust, scalable solution suitable for high‑security domains such as medical imaging, defense reconnaissance, and intellectual‑property protection.
Comments & Academic Discussion
Loading comments...
Leave a Comment