In previous work, we demonstrated how decoding of a non-binary linear code could be formulated as a linear-programming problem. In this paper, we study different polytopes for use with linear-programming decoding, and show that for many classes of codes these polytopes yield a complexity advantage for decoding. These representations lead to polynomial-time decoders for a wide variety of classical non-binary linear codes.
Deep Dive into Polytope Representations for Linear-Programming Decoding of Non-Binary Linear Codes.
In previous work, we demonstrated how decoding of a non-binary linear code could be formulated as a linear-programming problem. In this paper, we study different polytopes for use with linear-programming decoding, and show that for many classes of codes these polytopes yield a complexity advantage for decoding. These representations lead to polynomial-time decoders for a wide variety of classical non-binary linear codes.
In [1] and [2], the decoding of binary LDPC codes using linear-programming decoding was proposed, and the connections between linear-programming decoding and classical belief propagation decoding were established. In [3], the approach of [2] was extended to coded modulation, in particular to codes over rings mapped to non-binary modulation signals. In both cases, the principal advantage of the linearprogramming framework is its mathematical tractability [2], [3].
For the binary coding framework, alternative polytope representations were studied which gave a complexity advantage in certain scenarios [1], [2], [4], [5]. Analagous to the work of [1], [2], [4], [5] for binary codes, we define two polytope representations alternative to that proposed in [3] which offer a smaller number of variables and constraints for many classes of nonbinary codes. We compare these representations with the polytope in [3]. These representations are also shown to have equal error-correcting performance to the polytope in [3].
Consider codes over finite quasi-Frobenius rings (this includes codes over finite fields, but may be more general). Denote by R such a ring with q elements, by 0 its additive identity, and let R -= R{0}. Let C be a linear code of length n over R with m × n parity-check matrix H.
Denote the set of column indices and the set of row indices of H by I = {1, 2, • • • , n} and J = {1, 2, • • • , m}, respectively. The notation H j will be used for the j-th row of H. Denote by supp(c) the support of a vector c. For each j ∈ J , let I j = supp(H j ) and d j = |I j |, and let d = max j∈J {d j }. 1 These authors are also affiliated with the Claude Shannon Institute for Discrete Mathematics, Coding and Cryptography.
Given any c ∈ R n , parity check j ∈ J is satisfied by c if and only if the following equality holds over R:
For j ∈ J , define the single parity check code C j by
Note that while the symbols of the codewords in C are indexed by I, the symbols of the codewords in C j are indexed by I j .
Observe that c ∈ C if and only if all parity checks j ∈ J are satisfied by c. Assume that the codeword c = (c 1 , c2 , • • • , cn ) ∈ C has been transmitted over a q-ary input memoryless channel, and a corrupted word y = (y 1 , y 2 , • • • , y n ) ∈ Σ n has been received. Here Σ denotes the set of channel output symbols. In addition, assume that all codewords are transmitted with equal probability.
For vectors f ∈ R (q-1)n , the notation
will be used, where
and p(y|c) denotes the channel output probability (density) conditioned on the channel input. Extend λ to a map on Σ n by λ(y) = (λ(y
The LP decoder in [3] performs the following cost function minimization:
where the polytope Q is a relaxation of the convex hull of all points f ∈ R (q-1)n , which correspond to codewords; this polytope is defined as the set of f ∈ R (q-1)n , together with the auxiliary variables
which satisfy the following constraints:
The minimization of the objective function (2) over Q forms the relaxed LP decoding problem. The number of variables and constraints for this LP are upper-bounded by n(q-1)+mq d-1 and m(q d-1 + d(q -1) + 1) respectively.
It is shown in [3] that if f is integral, the decoder output corresponds to the maximum-likelihood (ML) codeword. Otherwise, the decoder outputs an ’error'.
The results in this section are a generalization of the highdensity polytope representation [2, Appendix II]. Recall that the ring R contains q -1 non-zero elements. Correspondingly, for vectors k ∈ N q-1 , we adopt the notation k = (k α ) α∈R - Now, for any j ∈ J , we define the mapping
for all α ∈ R -. We may then characterize the image of κ j , which we denote by T j , as
for each j ∈ J , where, for any k ∈ N, α ∈ R,
.
The set T j is equal to the set of all possible vectors κ j (b) for b ∈ C j . Note that κ j is not a bijection, in general. We say that a
Next, for any index set Γ ⊆ I, we introduce the following definitions. Let N = |Γ|. We define the single-parity-checkcode, over vectors indexed by Γ, by
Also define a mapping κ Γ : C Γ -→ N q-1 by
and define, for k ∈ T j ,
Below, we define a new polytope for decoding. Recall that y = (y 1 , y 2 , • • • , y n ) ∈ Σ n stands for the received (corrupted) word. In the sequel, we make use of the following variables:
• For all i ∈ I and all α ∈ R -, we have a variable f (α) i . This variable is an indicator of the event y i = α.
• For all j ∈ J and k ∈ T j , we have a variable σ j,k .
Similarly to its counterpart in [2], this variable indicates the contribution to parity check j of k-constrained local codewords over
i,j,k . This variable indicates the portion of f (α) i assigned to k-constrained local codewords over C j . Motivated by these variable definitions, for all j ∈ J we impose the following set of constraints:
We note that the further constraints
and
i,j,k ≤ σ j,k , (14) follow from constraints (7)-(11). We denote by U the polytope formed by constraints (7)-(11).
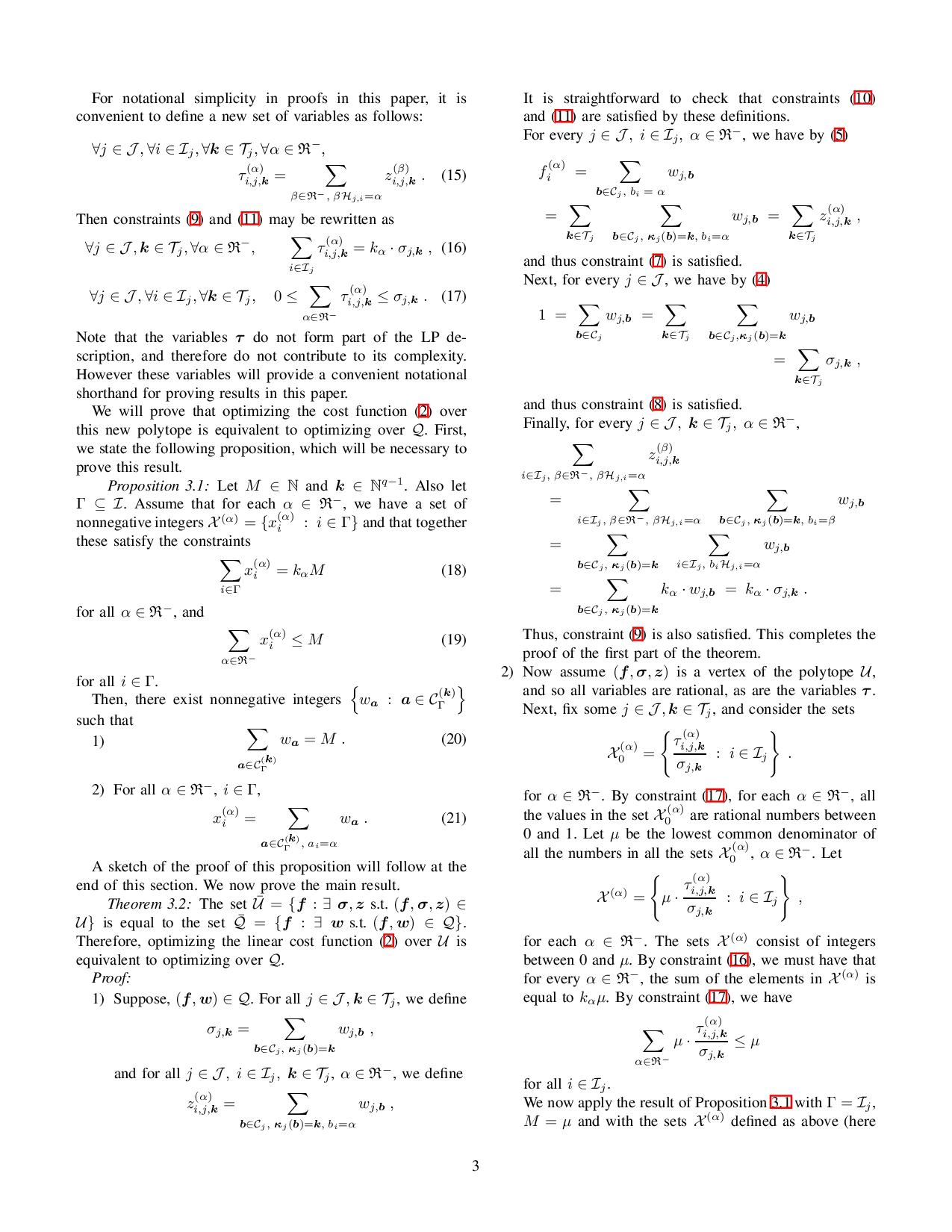
…(Full text truncated)…
This content is AI-processed based on ArXiv data.