Using the Physical Layer for Wireless Authentication in Time-Variant Channels
The wireless medium contains domain-specific information that can be used to complement and enhance traditional security mechanisms. In this paper we propose ways to exploit the spatial variability of the radio channel response in a rich scattering e…
Authors: Liang Xiao, Larry Greenstein, Narayan M
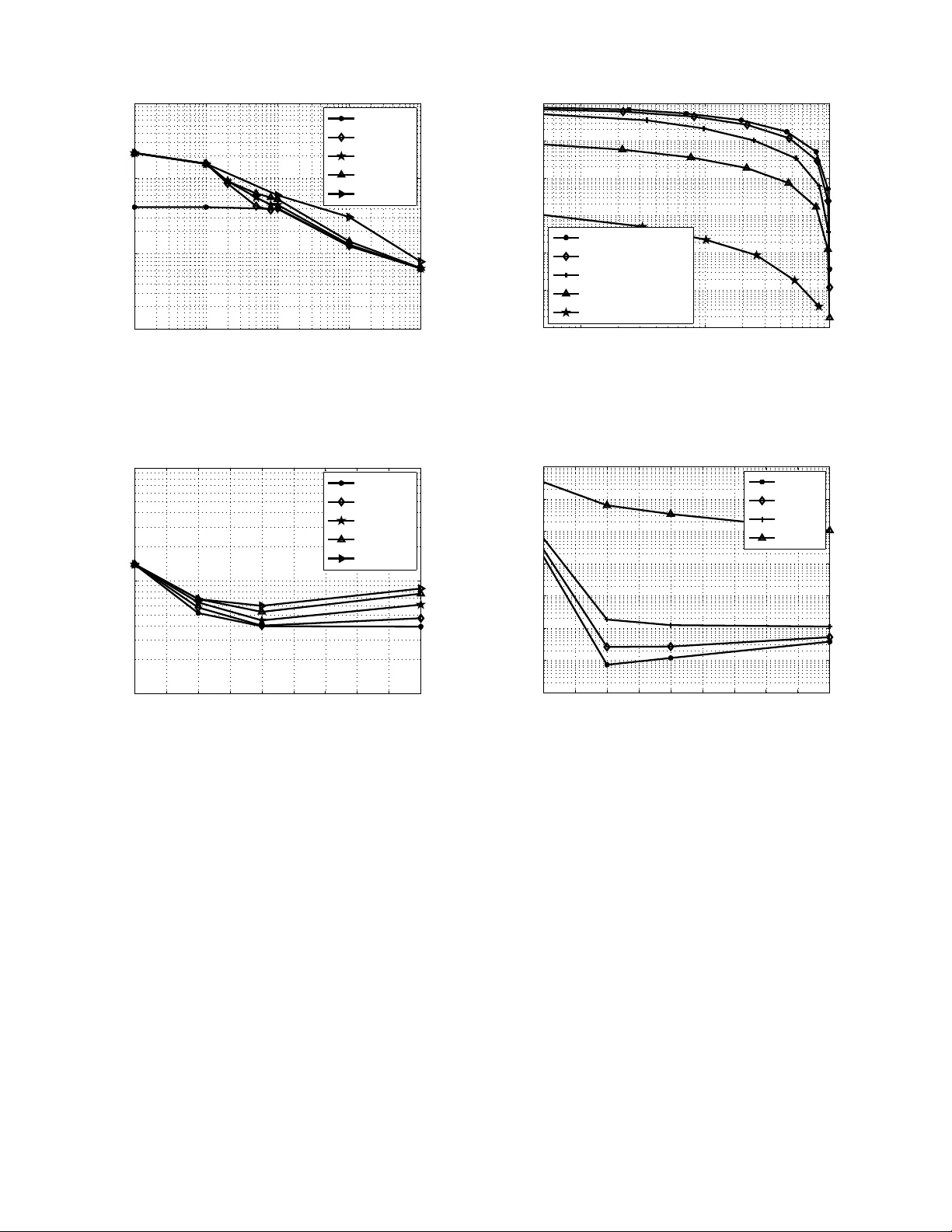
1 Using the Physical Layer for W ireless Authenticati on in T ime-V ariant Channels Liang Xiao, Student Member , IEEE, Larry J. Greenstein, Life F ellow , IEEE , Narayan B. Mandaya m, Senior Member , IEEE and W ade Trappe, Member , IEEE, Abstract — The wireless medi um contains d omain-specific in- fo rmation th at can be u sed to complement and enhance tradi- tional security mechanisms. In this paper we propose ways to exploit the spatial variability of th e radio channel response in a rich scattering en vironment, as is typical of indoor en vironments. Specifically , we describe a physical-lay er authentication algorithm that u tilizes chann el probing and hypothesis testing to determine whether current and prior communication attempts are made by the same transmit terminal. In this way , legitimate users can be r eliably authenticated a nd false users ca n be reliably detected. W e analyze the ab ility of a receiv er to discriminate between transmitters (users) according to their channel fr equency responses. Th is work is based on a generalized channel response with both spatial and temporal var iability , an d consid ers correla- tions among the ti me, frequency and spatial domains. Simulation results, using th e ray-tracing tool WiSE to generate the time- a vera ged response, verify the efficacy of the approach u nder realistic channel conditions, as well as its capability to work under unk nown channel variations. I . I N T RO D U C T I O N As wireless devices become increasingly pervasi ve and essential, they are beco ming b oth a target for attack and the very weapon with which su ch an attack can be carried ou t. T raditional high -level compu ter and network security tech- niques can, and must, play an importan t role in combating such attacks, but the wir eless en vironment presents both the me ans and the o pportu nity for new forms of intrusion. The devices that co mprise a wireless n etwork are low-cost commod ity items that are easily av ailable to po tential in truders and also easily modifiable fo r such intrusion. In par ticular , wireless networks ar e op en to intr usion fro m the o utside with out th e need f or a physical co nnection and , as a resu lt, tech niques tha t would provide a h igh level of security in a wired n etwork have proven inadequate in a wireless n etwork, as m any motiv ated group s of stude nts have readily demonstrated [1] –[3]. Although conv entional cry ptograp hic security mechanisms are essential to securing wireless n etworks, these techniqu es do not directly leverage the uniqu e pro perties o f the wir eless domain to address security threats. The physical prop erties of the wireless medium are a p owerful sourc e o f domain- specific informa tion tha t can be u sed to complement and enhance traditional security mechan isms. In this paper, we p ropo se a cross-layer appr oach to augm ent th e secur ity of wireless The authors are with WINL AB, the Department of Electrica l and Computer Engineeri ng, Rutgers Unive rsity , North Brunswick, NJ, 08902 USA e-mail: { lxiao , ljg,narayan,t rappe } @wi nlab .rutgers.edu This research is s upported , in part, through a grant CNS-0626439 from the Nationa l Science Founda tion. Manuscript recei ve d February 2007; revised August 2007. networks f or indo or wireless e n vironmen ts. I n particular, we believe that the natu re of the wire less medium can b e turned to the advantage of the network engine er when try ing to secure wireless co mmunicatio ns. The en abling factor in our ap proach is that, in th e rich mu ltipath e n vironmen t ty pical of wireless scenarios, the respo nse of the m edium alo ng any tra nsmit- receive path is fr equency-selective (or in the time domain , dispersive ) in a way that is loca tion-specifi c . T his m eans: 1) The channel can b e specified by a n umber of comp lex samples either i n the frequen cy do main (a set of complex gains at a set of frequ encies) or the time dom ain (a set of imp ulse resp onse samp les at a set of time delays). 2) Such sets of numb ers de correlate from one tr ansmit- receive p ath to another if the p aths a re separated by th e order o f an RF wa velength or more. While u sing the ph ysical layer to enh ance security might seem to be a radical p aradigm shift for wireless systems, we note that this is n ot th e first time that m ultipath an d a dvanced physical layer method s have pr oven advantageou s. Specifi- cally , we ar e encoura ged in our belief by two n otable pa rallel paradigm shif ts in wir eless system s: ( 1) cod e division multiple access (CDMA) systems [4], where the use of Rake processing transform s mu ltipath into a diversity-enhancing ben efit; and (2) multiple-inpu t m ultiple-ou tput (MI MO) antenna techniques [5], which transform scatter-induc ed Rayleigh fadin g in to a capacity-en hancing b enefit. Note that th ere h av e been recen t efforts in stud ying th e informa tion and secrecy ca pacity [ 6]–[8] , that can b e achie ved by using th e radio ch annel informatio n. I n con trast, this pap er studies th e fe asibility of using such rad io ch annel in formation . It does so b y explicitly d evising h ypothesis testing pro cedures to estimate and track the rad io ch annel fo r au thentication purpo ses. W e begin (Section II) by r evie wing some r elated work. Then (Section I II), we pr ovide an overview of our p roposed PHY -layer au thentication ser vice. W e next p resent a gen eral time-variant chann el model (Section IV) that we will use as the basis f or our discussions in th is paper . In Section V, we d escribe a hyp othesis testing framework for ph ysical layer au thentication. In Section VI, we p resent an overview of ou r simulation appro ach. W e present o ur simulatio n results in Section VII, and wr ap up the pap er in Section VIII with conclud ing remarks. I I . R E L AT E D W O R K In com modity networks, such as 802 .11 networks, it is easy for a device to alter its M A C ad dress and cla im to b e 2 another device by simp ly issuing an ifconfig co mmand. This weakness is a serio us threat, and ther e are numer ous attacks, rang ing fro m session hijacking [9] to attack s on access con trol lists [ 2], which are facilitated by the fact that an ad versarial device may masquerad e as another d evice. In response, researche rs have prop osed using phy sical layer informa tion to enhance wireless security . F or e xample, spectral analysis h as been used to id entify th e typ e of wir eless n etwork interface card (NI C), an d thus to discr iminate among users with different NICs [1 0]. A similar method , rad io f requen cy fingerpr inting, discriminates wirele ss d evices accordin g to th e transient beh avior of their tran smitted signals [1 1]. For mo re general networks, th e clock skew charac teristic of devices has be en v iewed as a remote fin gerprin t of devices over the Internet [1 2]. In a ddition, the inheren t variability in th e construction of various digital d evices h as been used to detect intrusion [1 3]. More recen tly , the wireless chan nel h as been explored as a new form of fingerp rint fo r wireless secu rity . The recipro city and rich multipath o f the ultrawideband channel h as been used as a means to estab lish enc ryption keys [6]. In [14], a p ractical scheme to discrimin ate between transmitters was proposed and identifies mob ile d evices by tra cking measurements of signal strength fro m multiple acc ess po ints. A similar approach was considered f or sensor n etworks in [ 15]. Concurr ent to these efforts, the pr esent au thors have built a significance test that exploits the spatial variability of pro pagation to en hance the authenticatio n in th e station ary , time -in variant channel [16] . In this pap er , we hav e significantly expanded the metho d to cover a more gener alized ch annel, where there ar e time variations due to chang es in the environment. As in [16] , however , the ends o f the link remain stationar y , as might be the case for a populatio n of u sers sitting in a room or airp ort termin al. W e will see that, in some c ases, the time variations impr ove the authenticatio n. I I I . P RO B L E M O V E RV I E W Authentication is tr aditionally a ssociated with the assurance that a commu nication com es fr om a specific entity [1 7]. In the co ntext o f phy sical layer au thentication, howe ver , we ar e not in terested in id entity , p er se , but rather are interested in recogn izing a par ticular tr ansmitting device. Th e ability to distinguish between different tra nsmitters would n ot replace traditional identity -based authentication , but would be partic- ularly valuable a s a wireless system enhanc ement. Su ch an approa ch would be beneficia l f or scen arios where man aging cryptog raphic key m aterial is difficult, and further would reduce the load place d on higher-layer authentication buffers. Here, we borr ow from the conv entional term inology of the security c ommun ity by introd ucing three different p arties: Alice, Bob and Eve. For our purpo ses, these three en tities may be tho ught of as wir eless transmitters/rece i vers th at are potentially located in spatially separated positions, as depicted in Fig . 1. Our two “legal” protago nists are the usual Alice and Bob, and for the sake of discussion thro ughou t this paper, Alice will serve as the transmitter that initiates communication, while Bo b will serve as the intended r eceiv er . Th eir n efarious A B Scattering Cluster1 Scattering Cluster2 Scattering Cluster3 E Fig. 1. The adversari al multipat h en vironment in vol ving multip le scatt ering surfac es. The transmission from Alice (A) to Bob (B) exp erienc es dif fere nt multipat h effe cts than the transmission by the adv ersary , Eve (E ). adversary , Eve, will serve as an active adversary that in jects undesirab le co mmunicatio ns in to the me dium in the ho pes of spoofing Alice. Our security ob jectiv e, br oadly speaking, is to provide authenticatio n between Alice an d Bo b, despite the pr esence of Eve. Since Eve is within range of Alice and Bob, a nd capable of injecting her own signals into the en vironmen t to impersona te Alice, Bob must h av e the ab ility to differentiate between legitimate signals fr om Alice and illegitimate signals from Eve. Consider a simple tran smitter identification pro tocol in which Bob seek s to verify that Alice is th e transmitter . Suppose that Alice transmits probes into the channel at a rate sufficient to assure temporal co herence between chann el estimates and that, p rior to Eve’ s arriv al, Bob has estimated the Alice- Bob channel. Eve wishes to convince Bob that she is Alice. Bob will re quire that each in formation -carry ing tran smission be accompan ied by an authen ticator signal. The ch annel re sponse to a transmitted sign al between Alice and Bob is a result of the multipath environmen t. Bob m ay u se the received version of the authen ticator signal to estima te the c hannel r esponse and compare this with a previous record for the Alice-Bob channel. If the two ch annel estimates are “close” to each othe r , then Bob will conclud e th at the source of the messag e is th e same as the source of the previously sent message. If th e chan nel estimates are not similar, then Bob shou ld conclu de that the source is likely n ot Alice. There ar e several imp ortant issues related to such a pro- cedure tha t should be add ressed be fore it ca n be a viable authenticatio n mechanism. First is the specification of th e authenticato r sig nal that is used to probe the channel. There are many stand ardized techniqu es to probe the ch annel, ranging from p ulse-style pro bing (in cluding PN seq uences) to multi- tonal probin g [18 ], an d we may use these tech niques to estimate the ch annel response. Regardless o f what p robing method is employed, th e channel response can be characterized in the freque ncy do main, and th rough out this paper we will represent ou r ch annels in that domain. A secon d issue is that in a richly scattered multip ath en vironmen t (typical o f indo or wireless environments), it is difficult for an adversary to crea te or p recisely mo del a wave- form that is tran smitted and received b y entities that are m ore 3 than a wavelength away from the adversar y . This assertion is supported by the well-known Jakes unifo rm scattering mod el [19], which states that the r eceiv ed signal rapid ly decorre lates over a distance of rough ly half a wavelength, and that spatial separation of one to two wav elengths is sufficient for assuming indepen dent fading paths. The imp lication o f su ch a scatterin g model in a transmitter id entification app lication rem ains to be tested, and a key objective of this study is to examine the utility of a typical in door m ultipath environment for discriminating between Alice-Bob an d Eve-Bob c hannels. Finally , it should also be no ted that the chann el r esponse may change with time due to chang es in the en vironmen t (p eo- ple moving, door s o pening or closing ) and in p ractice it will be necessary to guaran tee th e continuity of th e auth entication proced ure by probing the channel at time intervals less than the channel’ s “coherence time”. Th is paper examin es the ability to authenticate tr ansmitters in such a time-variant environment, and serves to illustrate the potential for new f orms of physical layer secu rity . I V . C H A N N E L M O D E L A. Basic F orm W e assume that Bob first m easures and stores the f requen cy response of the chann el c onnecting Alice with h im. Due to his receiver th ermal noise, Bob stores a n oisy version o f the chann el response, H A ( f ) . After awhile, he has to decide whether a tr ansmitting terminal is still Alice, based on a noisy measured version , H t ( f ) , o f that termin al’ s chan nel respon se to Bob . By s ampling H A ( f ) and H t ( f ) at f ∈ ( f o − W / 2 , f o + W/ 2 ] , Bob obtains two frequ ency respon se vectors, H A and H t , of length M , where W is the measur ement b andwidth ; f o is the center frequ ency of the measureme nt; an d the vector elements are f requen cy response samples at M unifor mly spaced f requen cies over the measurem ent bandw idth. W e consider a gener alized time- variant chan nel response, where eac h f requen cy respon se sample is made u p o f three parts: the fixed part that is th e average ch annel response over tim e and contains the spatial variability inform ation, the variable part with zero mean, and the receiver noise. Thu s the m -th element of H A at time k T from some arbitrary time origin can be written a s H A,m [ k ] = H A,m + ǫ A,m [ k ] + N A,m [ k ] , 1 ≤ m ≤ M , (1) where we use the notation that X m [ k ] is the samp le fro m X ( t ; f ) at the m -th to ne at a samp ling time of k T . More specifically , X m [ k ] = X ( kT ; f o − W / 2 + m ∆ f ) , m = 1 , · · · , M , wh ere ∆ f = W / M ; M is the sample size in the frequen cy d omain; and T is the sampling interval. T he term H A,m is the average value of the m - th tone over time, ǫ A,m [ k ] is the zero-mean variable part at time k T , and N A,m [ k ] represents thermal no ise sam ple at the m -th tone a t tim e k T . The n oises are modelled by C N (0 , σ 2 N ) , i.e., zero-mea n complex Gaussian samples with variance σ 2 N . Without lo ss of realism, we can assume th at they are in depend ent acr oss time, tone ( frequen cy) and termin al (space) , and that ǫ A,m [ k ] is ind ependen t o f N A,m [ k ] . B. Delay Pr o file an d Doppler Spectrum (T empo ral F ad ing) o f the V ariable P art W e model the v ariable part of the chann el respon se as wide- sense statio nary un corr elated sca ttering (WSSUS), and can thus use a multipa th tapp ed delay line to mo del its impulse response, h ( t, τ ) [20]: h ( t, τ ) = ∞ X l =0 A l ( t ) δ ( t − l ∆ τ ) , (2) where t is the obser vation time, and l ∆ τ and A l ( t ) are, respectively , the delay and comp lex amplitude of th e l -th multipath com ponen t, with E [ A l ( t )] = 0 over time. W e set ∆ τ = 1 /W , since the receiver cannot resolve two compo nents with time d ifference s maller than th e in verse of the b andwidth . The freq uency response of the variable part is the Fourier transform o f h ( t ; τ ) in te rms of τ , ǫ A,m [ k ] = F { h ( t ; τ ) }| t = kT ,f = f o − W/ 2+ m ∆ f = ∞ X l =0 A l [ k ] e − j 2 π ( f o − W/ 2+ m ∆ f ) l ∆ , (3) where A l [ k ] = A l ( k T ) is the amplitude sample o f the multipath co mponen t at time k T . For illustrative pu rposes, we use th e one-sided exponential distribution to mo del the power d elay spectrum of A l [ k ] 1 , i.e., P τ [ l ] = V ar [ A l [ k ]] = σ 2 T (1 − e − γ ∆ τ ) e − γ ∆ τ l , (4) where γ = 2 π B c is the inverse of the average dela y spr ead, B c is the co herence ban dwidth of the variable p art, and σ 2 T is the average power of A l [ k ] over all taps. Also for illustrati ve pur poses, we use a n autoregressiv e model of ord er 1 (AR-1 ) to character ize the temp oral process of A l [ k ] , i.e., A l [ k ] = aA l [ k − 1] + p (1 − a 2 ) P τ [ l ] u l [ k ] , (5) where the AR coefficient a denotes the similarity of two A l values spaced b y T and the rando m co mponen t u l [ k ] ∼ C N (0 , 1) is ind ependen t o f A l [ k − 1] . C. Spatial Corr ela tions As po inted out in Section I, in a typically rich scattering en vironmen t, th e radio ch annel response decor relates q uite rapidly in space. Later, we will cite the use of the ray-tracin g software W iSE to emulate the sp atial cor relation character is- tics o f the fixed part o f th e channe l respo nse ( H ). As to the variable part, howe ver , we consider the two extreme cases: 1) S patially independ ent a nd id entically distributed ǫ . The frequen cy response sample of the chan nel between Eve and Bob can be written a s H E ,m [ k ] = H E ,m + ǫ E ,m [ k ] + N E ,m [ k ] , (6) 1 The litera ture abounds with empirical data [21] and theoretica l exampl es [22] in which the exp onenti al dela y profile appea rs. W e in vo ke it here for the sake of concre teness, which will allo w us to compute numerica l results, but we also recognize it to be a realisti c condition. 4 where 1 ≤ m ≤ M , H E ,m = E [ H E ,m [ k ]] is the time av erage; therm al noise N E ,m [ k ] ∼ C N (0 , σ 2 N ) ; and ǫ E ,m [ k ] and ǫ A,m [ k ] are independ ent id entically distributed ( i.i.d.). 2) Complete spatially corr elated variation ( ǫ E ,m [ k ] = ǫ A,m [ k ] ). Here, we have H E ,m [ k ] = H E ,m + ǫ A,m [ k ] + N E ,m [ k ] , 1 ≤ m ≤ M . (7) D. Importan t Relationships T wo impo rtant relationships we will use in the h ypoth esis testing later a re as follows (pro ofs are provided in the Ap- pendix) : Relationship 1 : H A [ k ] − H A [ k − 1] ∼ C N (0 , R ) , (8) where R = Cov [ H A [ k ] − H A [ k − 1]] = [ r ( m − n )] mn , 1 ≤ m, n ≤ M , (9) r (0) = 2(1 − a ) σ 2 T + 2 σ 2 N , and r ( m ) = 2 σ 2 T (1 − a )(1 − e − 2 π B c /W ) 1 − e − 2 π B c /W − j 2 π m/ M , 1 − M ≤ m ≤ M − 1 . (10) Relationship 2 : For th e case with sp atially in depend ent time variation, H E [ k ] − H A [ k − 1] ∼ C N (( H E − H A ) , G ) , (11) where G = Cov [ H E [ k ] − H A [ k − 1]] = 2 σ 2 T + 2 σ 2 N r ( − 1) 1 − a · · · r (1 − M ) 1 − a r (1) 1 − a 2 σ 2 T + 2 σ 2 N · · · r (2 − M ) 1 − a · · · · · · · · · · · · r ( M − 1) 1 − a r ( M − 2) 1 − a · · · 2 σ 2 T + 2 σ 2 N . (12) V . H Y P O T H E S I S T E S T I N G Here, we presen t f ormulas fo r h ypothesis testing th at will be red uced later to numerical results. A. General Case As in [16], Bob u ses a simple hy pothesis test to de cide if the transmittin g terminal is Alice or a would -be intrud er , E ve. The nu ll hy pothesis, H 0 , is that th e ter minal is not an intruder, i.e. th e claiman t is Alice; and Bob accepts th is hypoth esis if the test statistic he comp utes, Z , is below som e th reshold, T . Otherwise, h e accep ts the alter native hyp othesis, H 1 , that the claimant ter minal is someon e else. Thus, H 0 : H t [ k ] = H A [ k ] (13) H 1 : H t [ k ] 6 = H A [ k ] , (14) First, we assum e spatially inde penden t time variations and assume Bob kn ows the key channel variation parame ters a , B c and σ T . (W e will d iscuss other cases in the later parts o f this section.) W e choo se the test statistic in this default setting as Z = z H z = 2( H t [ k ] − H A [ k − 1]) H R − 1 ( H t [ k ] − H A [ k − 1]) , (15) where z = √ 2( R H d ) − 1 ( H t [ k ] − H A [ k − 1]) , R and R d are the covariance matrix of H A [ k ] − H A [ k − 1] , (9), and its Cholesky factorization (i.e. , R = R H d R d ). It can b e shown th at, when the tran smitting terminal is Al- ice, each elemen t of z is i.i.d. , fo llowing a n ormal distrib ution, z = √ 2( R H d ) − 1 ( H A [ k ] − H A [ k − 1]) , where the elem ents are i.i.d., an d z i ∼ C N (0 , 2) , 1 ≤ i ≤ M . Thus the te st statistic Z is a chi-square r andom variable with 2 M degrees of freedom [23], i.e ., Z = z H z ∼ χ 2 2 M . W e d efine th e rejection region f or H 0 as Z > T . Thus, the “false alarm r ate” (o r T y pe I error) is α = P r { Z > T |H 0 } = 1 − F χ 2 2 M ( T ) ; and the “miss rate” (or T y pe II error) is given by (16), where F X ( · ) is the CDF of the ran dom variable X and F − 1 X ( · ) is the inv erse f unction of F X ( · ) . For a specified α , the thr eshold of the test is T = F − 1 χ 2 2 M (1 − α ) , and the miss rate can be obtained by nu merical metho ds. B. Asymptotic Results fo r Low Corr elation Ba ndwidth When the variation is indepen dent over tones (i.e., B c /W ≪ 1 ), th e covariance matrices o f E q. ( 9) and (12) become R = Cov [ H A [ k ] − H A [ k − 1]] = (2(1 − a ) σ 2 T + 2 σ 2 N ) I G = Cov [ H E [ k ] − H A [ k − 1]] = (2 σ 2 T + 2 σ 2 N ) I , (17) where I is the identity m atrix. T hus the test statistic Eq. (15) becomes Z = | H t [ k ] − H A [ k − 1] | 2 (1 − a ) σ 2 T + σ 2 N = Z 2 /ρ, (18) where ρ = (1 − a ) σ 2 T + σ 2 N σ 2 T + σ 2 N . (19) It is easy to see th at, under H 1 , the test statistic is a non-ce ntral chi-squ are distribution with ord er 2 M , i.e., Z 2 ∼ χ 2 2 M ,µ with non-cen tral p arameter µ = P M m =1 | H E ,m − H A,m | 2 σ 2 T + σ 2 N (20) Thus, th e miss rate for specified α , (16), can be written as β = P r { Z < T |H 1 } = F χ 2 2 M,µ ( ρ F − 1 χ 2 2 M (1 − α )) . (21) C. Asymptotic Re sults for High Corr ela tion B andwidth When the variation is totally cor related over tones (i.e., B c /W ≫ 1 ) , the covariance matrices of (9) and ( 12) d egrade to R = 2 σ 2 N I + 2(1 − a ) σ 2 T 1 (22) G = 2 σ 2 N I + 2 σ 2 T 1 , (23) where 1 is a M × M matrix with eac h elem ent eq uals to 1. Again, we can use Eq. (16) to num erically calculate th e miss rate β for specified false alarm rate α . 5 β = P r { Z < T |H 1 } = P r { 2( H E [ k ] − H A [ k − 1]) H R − 1 ( H E ,t [ k ] − H A [ k − 1]) < F − 1 χ 2 2 M (1 − α ) } , (16) D. Unknown P arameters When Bob do es not know th e par ameters a , B c and σ T , it is rea sonable for him to u se as the test statistic Z = 1 σ 2 N | H t [ k ] − H A [ k − 1] | 2 . (24) In this case, we can obtain numerica l results for the false alarm rate and m iss rate f or specified th reshold T , plotting β v s. α with T as an implicit parameter . E. Full S patial Corr elatio n Now we co nsider the oth er extreme case o f spatial cor re- lation, n amely , ǫ E ,m [ k ] = ǫ A,m [ k ] ( full spatial corre lation). The spatial correlatio n h as no impact un der the hypoth esis H 0 . Howe ver , under the hypothesis H 1 , the correlation matrix of the difference between two m easurements become s R , and H E [ k ] − H A [ k − 1] ∼ C N (( H E − H A ) , R ) . Thus, the test statistic un der H 1 is non -central chi-squa re distributed, Z = | √ 2( R H d ) − 1 ( H E [ k ] − H A [ k − 1]) | 2 ∼ χ 2 2 M ,µ , with non- central parameter µ = | √ 2( R H d ) − 1 ( H E − H A ) | 2 . Therefo re, the miss rate for the f ully spatially correlated temporal variation can be written as β = F χ 2 2 M,µ ( F − 1 χ 2 2 M (1 − α )) . (25) F . Discussion: I mpact of T ime V ariations As a b enchmar k, fro m ( 21) we have the miss r ate fo r the time-inv ar iant channel as [1 6], β = F χ 2 2 M,µ ( F − 1 χ 2 2 M (1 − α )) , (26) where µ = P M m =1 | H E ,m − H A,m | 2 /σ 2 N . In the pre sence of time variation, h owe ver, the m iss rate may become smaller . The asymptotic miss rate for the time- variant channel at high band width, (21), increases with ρ , ( 19), and decreases with µ , (2 0). As th e time variation σ 2 T rises from 0 to ∞ , ρ d ecreases from 1 to 1 − a and µ falls from P M m =1 | H E ,m − H A,m | 2 /σ 2 N to 0, which ma y results in a smaller miss rate. Actually , the tem poral-variation h as a two-fo ld imp act: 1) It add s uncertainty to the channel from Alice, and thus Bob has to increase the test threshold to accept Alice (negative impact on the performance) ; 2) the variation is usually strongly correlated in time while very weakly corr elated in sp ace, and thus ǫ A [ k ] − ǫ A [ k − 1] < ǫ E [ k ] − ǫ A [ k − 1] ( positive impac t on p erform ance). When σ T is negligible, the channel can be viewed ap- proxim ately as a time- in variant on e, wh erein the miss rate is given by (2 6). As σ T rises, the miss ra te falls sin ce the positive impact dominates. If the v ariation continues to rise and becomes very large, th e miss rate begins to rise, as the need to raise the thresho ld h elps Eve an d counter acts the positive impact. When σ T becomes so large that bo th the fixed part Bob Room # 1 Room # 2 Room # 3 Room # 4 ... ... ... ... ... ... 0.2 m 0.2 m 120 m 14 m Fig. 2. System topology assumed in the simulations. Bob is locat ed at 2-m height near the cent er of a 120 m × 14 m × 4 m office building. Alice and Eve are located on dense grids at a height of 2 m. The sizes of the grids are N s = 150 , 713, 315, and 348, respecti vely , for Room # 1, 2, 3 and 4. of th e chann el respon se and the the rmal n oise are relatively negligible (i.e., σ 2 T ≫ σ 2 N , σ 2 T ≫ P M m =1 | H E ,m − H A,m | 2 ), then u sing (2 1) we can r ewrite the m iss rate as β ≈ F χ 2 2 M ((1 − a ) F − 1 χ 2 2 M (1 − α )) , (27) which is a f unction of the time-corre lation of the tempora l variation par ameter ( a ), freq uency sample size ( M ), and the false alarm rate ( α ). If th e variation is stron gly corr elated in time ( a ≈ 1 ), the miss r ate can be less tha n that f or the no ise- dominated case, (26), wher e the thermal noise is usually no t negligible du e to the limited transmit power . An illustration of this tr end will be giv en later . Finally , we conside r the im pact of the spatial co rrelation of time variations. The miss r ate with total spatial c orrelation, (25), decrea ses with µ in a man ner that is propo rtional to th e in verse of R , (9), and thus rises with σ T . Since a strong spatial correlation of th e time variation damages the spatial v ariability character o f the channel, wh ich is the b asis of our sche me, it will d egrade the sy stem p erform ance. V I . S I M U L A T I O N M E T H O D O L O G Y A. Simulatin g the T ransfer Function s In order to tes t the proposed s cheme, it is necessary to model not on ly “typical” chan nel responses, but the spatial v ariability of these responses. Only in this way can we discern the success in detecting would- be intruders like Eve. T o th at end, we ma ke use of the W iSE T ool, a ra y-tracing software p ackage d ev el- oped by Bell L aborator ies [24] . One input to WiSE is the 3- dimensiona l plan of a specific building, including w alls, floors, ceilings and their material proper ties. W ith this inform ation, W iSE can p redict the rays at any receiver from any transmitter, including their amplitudes, phases and delays. Fro m this, it is straig htforward to co nstruct the transmit- receive f requency response over any spec ified freq uency interval (bandw idth). W e have don e th is for o ne particular o ffice building (the Alcatel-Lucen t Crawford Hill Labo ratory in Holmd el, NJ), for which a top view of the first floor is shown in Fig. 2. This floor of this building is 120 meters lon g, 14 meters wide and 6 4 meter s high. For our numerical exper iment, we placed Bob in the hallway (the filled-in circ le) a t a h eight o f 3 m . For the positions of Alice and Eve, we co nsidered four room s at the extremities of the building (shown shaded) . For each room, we assumed Alice and Eve bo th transmitted from a height of 2 m, each of them bein g anywhere on a un iform horizon tal grid o f points with 0.2 -meter separations. W ith N s grid points in a room, there we re N s ( N s − 1) / 2 possible pairs of Alice-E ve positions. For Rooms 1, 2, 3 a nd 4, the number s of grid points were N s = 150 , 713, 3 15 and 348, respectiv ely . For ea ch Alice- Eve pair, (1) W iSE was u sed to gen erate th e Alice-Bob and Eve-Bob average ch annel responses ( H A ( f ) and H E ( f ) ); and (2) the hypo thesis test described above was used to compute β for a specified α . The s et of all β -values in a room were used to compute a room-specific m ean, β , for each of several selected combina tions o f ban dwidth ( W ), number of fr equency-d omain samples ( M ), transmit power ( P T ), an d channel variation mo dels. B. T ransmit P ower , Receiver No ise, and T ime V ariation Str ength Assume th at, in conjunctio n with W iSE, we obtain the var - ious tr ansfer fu nctions as dimension less ratios (e. g., received E -field/transmitted E -field ). Then the pro per treatment of the noise variance, σ 2 N , in the h ypoth esis test is to define it as the receiver n oise power p er tone , P N , divided by the tra nsmit power per tone, P T / M , wh ere P T is the total tran smit power . Noting th at P N = κ T N F b , where κ T is th e therm al noise density in m W/Hz, N F is the receiver no ise figure, an d b is the measuremen t noise band width per tone in Hz [18], we ca n write σ 2 N = κ T N F b P T / M = M Γ , ( 28) where P T is in mW , and Γ = P T /P N . W e will henc eforth refer to Γ by its d ecibel value. Let b 2 T denote the ratio between σ 2 T and the value of | H | 2 av eraged over th e M fr equency samples (or “tones”) and the N s receiver loca tions. W e can thus write the st andard deviation of th e tim e variation as σ T = b T H = b T v u u t 1 M N s M X m =1 N s X l =1 | H l,m | 2 , (29) where H can be regarded as a roo m param eter , and b T represents th e r elativ e magnitud e o f the time variation in a giv en room . V I I . N U M E R I C A L R E S U LT S In our simulations, we set f 0 = 5 GHz, N F = 10 (10 dB no ise figur e), κ T = 10 − 17 . 4 mW/Hz, b = 0 . 25 MHz, a = 0 . 9 , and, un less specified oth erwise, α = 0 . 0 1 [25] . As noted earlier , we place Alice and E ve on dense grid s in each of four rooms at the cor ners o f a particular b uilding, with Bo b in the hallway , Fig. 2. W e obtained a miss rate f or each Alice- Eve pair in each r oom, an d then calculated the a verage mean value for each room in the building. Amo ng them, Room # 4, 10 −2 10 −1 10 0 10 1 10 2 10 3 10 4 10 −7 10 −6 10 −5 10 −4 10 −3 10 −2 10 −1 10 0 b T Average Miss Rate P T =1 mW P T =10 mW P T =100 mW P T =1 W Fig. 3. The av era ge miss rate as function of the relati ve standa rd de viat ion of the time variat ion, for the channel with spatially indepen dent temporal v ariat ion. M = 10 , W = 10 MHz, a = 0 . 9 and B c = 0 . as th e farthest ro om fro m Bob, is likely to have th e poorest perfor mance in rejecting Eve. In that sense, it lower-bounds the capab ilities of o ur PHY - layer auth entication algorithm. For reasons of space, we will only pr esent results for Roo m # 4, keeping in m ind that they are essentially worst-case o r close to it. Figure 3 con firms the efficacy o f the algorithm in the presence o f channel tim e variations. W e assume realistic system p arameter values ( P T = 1 mW ∼ 1 W , M = 10 and W = 10 MHz), and find that most average miss r ates are smaller than 0.01. Th e per to ne signal- to-noise ratio (SNR) in the ch annel measurem ents ranges fro m -12 .8 dB to 1 4.2 dB, with a media v alue o f 6.4 dB, if u sing P T = 10 mW , M = 10 and W = 10 M Hz. A lso, as po inted out in Section V, our propo sed a lgorithm can exploit the time variations to impr ove perfor mance. For exam ple, the miss rate falls f rom ar ound 0.01 to 10 − 5 when b T rises f rom 0 . 01 to 1 , with P T = 10 0 mW . The trend of these curves with time v ariation confirms the discussion in Section V -F, e.g., the min imum a verage miss rate is a trade off b etween the positive impact of the time variation and its negative impact resulting f rom the rise o f the thr eshold. Moreover , the m iss rate falls with th e transmit power P T , as expected, since it reduces the measuremen t noise at th e receiver . Figure 4 demonstrates the im pact of the bandwid th W and the coherenc e bandwidth B c . W e n ote that the results for B c = 0 and B c = ∞ ar e th e lower and upper bound s, respectively , of the miss rates, as well as th e asy mptotic results for the high- and low-bandw idth regions. It is clear that frequ ency correlation s degrad e per forman ce. A related findin g is th at the miss r ate de creases with increa sing band width, W , since the frequen cy resp onse samples are more in depend ent with larger W . Figure 5 ind icates that there is little benefit (or even a deficit) in increasing M beyond ∼ 10 , unless the freq uency correlation is very small (e.g ., B c = 0 ) with h igh tran smit power . Actually , the o ptimal sam ple size M in terms of 7 10 −4 10 −3 10 −2 10 −1 10 0 10 −3 10 −2 10 −1 10 0 Bandwidth (GHz) Average Miss Rate B c =0 B c =1 MHz B c =2 MHz B c =4 MHz B c = ∞ Fig. 4. The aver age miss rate as a function of the measurement bandwith W , for the channel with spatial ly indepen dent temporal varia tion. M = 5 , a = 0 . 9 , b T = 0 . 5 , and P T = 10 mW . 1 2 3 4 5 6 7 8 9 10 10 −2 10 −1 10 0 M Average Miss Rate B c =0 B c =1 MHz B c =2 MHz B c =4 MHz B c = ∞ Fig. 5. The av erage miss rate as a function of the number of frequenc y samples, for the channe l with spatially independent temporal vari ation . W = 10 MHz, a = 0 . 9 , b T = 0 . 5 , and P T = 10 mW . miss rate f or spec ified m easuremen t bandwid th decreases with the coh erence band width B c , becau se the no ise power (28) rises with M a nd the frequ ency-respon se samples are more correlated with larger B c . W e see in Fig. 6 that the alg orithm works ev en when Bob does not know the ke y channel parameters, although it requires either more tran smit power or grea ter to lerance for T ype II errors. Interestingly , the time-variation may still help here, e.g., the miss rate falls as b T rises f rom 0.1 to 1. How to set the test thr eshold T in this case is an open topic. Finally , Fig. 7 shows that the system is very sensiti ve to th e time-variation in a n extrem e case of f ull sp atial cor relation. It requires much m ore transmit p ower ( P T ∼ 0 . 5 W) to r each the same miss rate perf ormance . T he reason is quite simp le: the mechanism o f our sch eme is to utilize the spatial variability of the ch annel responses. Th e spatial co rrelation o f the time variation decreases the overall spatial variability an d thus degrades the perform ance. 10 −2 10 −1 10 0 10 −6 10 −5 10 −4 10 −3 10 −2 10 −1 10 0 Average False Alarm Rate Average Miss Rate b T =0.1, P t =1 mW b T =0.5, P t =1 mW b T =1, P t =1 mW b T =0.5, P t =10 mW b T =0.5, P t =100 mW Fig. 6. A verag e miss rate vs. averag e fal se alarm rate when Bob does not know the channel para meters, for the channel with spatially independ ent temporal varia tion. W = 50 MHz, M = 10 , a = 0 . 9 , and B c = 2 MHz. 1 2 3 4 5 6 7 8 9 10 10 −7 10 −6 10 −5 10 −4 10 −3 10 −2 10 −1 10 0 M Average Miss Rate b T =0.01 b T =0.05 b T =0.1 b T =1 Fig. 7. A v erage miss rate vs. M , for the channel with totally spatially correla ted temporal v aria tion. W = 100 MHz, B c = 2 MHz, P T = 0 . 5 W , and a = 0 . 9 . The above assertions apply a s well to the other sh aded rooms in Fig . 2 an d, we can safely assume, to the o ther ro oms in the building. V I I I . C O N C L U S I O N W e have describ ed an d stud ied a p hysical layer technique for enhancing auth entication in a time-variant wireless en- vironm ent. Specifically , we assum e the user termin als are stationary but changes in the environment p roduce additive time-varying ch anges in the channel respo nses. The techniqu e uses channel frequency response measuremen ts and hypothesis testing to discriminate between a legitimate user (Alice) and a would-be intruder (Eve). W ith the ability to utilize the temporal- variation, it works even wh en the r eceiver does not kn ow the key ch annel variation parameter s, namely , the AR tempo ral co efficient a , the coherenc e ban dwidth B c and the standard d eviation of the v ariation σ T , althoug h the se parameters h elp red uce the miss rate if known. 8 The alg orithm h as been verified in a typica l in-building en vironmen ts, wher e we used the ray-tracing tool W iSE to gen erate realistic average c hannel resp onses and used a multipath tapp ed delay line c hannel model for the tempo ral variation part of the chan nel response. Simu lation results hav e confirmed the efficacy of th e a lgorithm f or rea listic values of the measuremen t ban dwidth (e. g., W ∼ 10 MHz ), nu mber of response samples (e.g ., M ≤ 10 ) and tr ansmit p ower (e.g ., P T > 10 mW). T he miss rate is genera lly smaller th an 0.01, for a specified false alarm rate of 0.0 1, in th e presence of moderate ch annel time variations. W e have found that the ch annel time v ariations can improve the per forman ce, e.g. , the miss rate falls fro m aroun d 0.01 to 10 − 5 when the variation in dex b T rises fro m 0 . 01 to 1 , with P T = 1 00 mW . In ad dition, the miss ra te decr eases with th e transmit power of the probin g sig nal and the mea surement bandwidth , an d usually requires fr equency samples of fewer than 10. W e have also shown that the time correlatio n of the channel variation is help ful, while coherenc e in the freq uency and sp atial d omains are harm ful. Research is c urrently in p rogress to ad dress the ca se of u ser terminal mobility . Ef fort is also needed, for the stationary case, to explore th e par ameter space ( e.g., the tempo ral co herence term a ); d evise means of setting the test threshold T ; consider other buildings; an d co nduct experimen ts to more accura tely characterize the time-variation prop erties of indoo r chann els. Moreover , we are working to integrate p hysical layer au- thentication into a holistic cross-layer fram ew ork for wireless security that will aug ment traditional “h igher-layer” network security m echanisms with phy sical layer me thods. A P P E N D I X I P R O O F O F R E L AT I O N S H I P 1 Since A l [ k ] ∼ C N (0 , P τ [ l ]) , from Eq. ( 3) and (4), we have E [ ǫ A,m [ k ]] = ∞ X l =0 E [ A l [ k ] e − j 2 π ( f o − W/ 2+ m ∆ f ) l ∆ ] = 0 (30 ) and V ar [ ǫ A,m [ k ]] = ∞ X l =0 V ar [ A l [ k ] e − j 2 π ( f o − W/ 2+ m ∆ f ) l ∆ ] = ∞ X l =0 V ar [ A l [ k ]] = ∞ X l =0 σ 2 T (1 − e − γ ∆ τ ) e − γ ∆ τ l = σ 2 T (31) Here we also utilize the fact that any two different mu ltipath compon ents in a WSSUS chann el ar e unco rrelated, i.e ., ∀ l 1 6 = l 2 , ∀ k 1 , k 2 , E [ A l 1 [ k 1 ] A l 2 [ k 2 ]] = 0 ( 32) Considering that A l [ k − 1] and u l [ k ] ar e b oth zero-m ean and independ ent to each o ther, we see fr om Eq. (4) and (5 ) that E [ A l [ k 1 ] A l [ k 2 ]] = a | k 1 − k 2 | V ar [ A l [min( k 1 , k 2 )]] = a | k 1 − k 2 | σ 2 T (1 − e − γ ∆ τ ) e − γ ∆ τ (33) Then fro m (3), (32), and (33), we have E [ ǫ A,m [ k 1 ] ǫ A,n [ k 2 ] ∗ ] = ∞ X l 1 =0 ∞ X l 2 =0 E [ A l 1 [ k 1 ] A l 2 [ k 2 ]] · e − j 2 π [( f o − W/ 2+ m ∆ f ) l 1 − ( f o − W/ 2+ n ∆ f ) l 2 ] /W = ∞ X l =0 E [ A l [ k 1 ] A l [ k 2 ]] e j 2 π ( n − m )∆ f l/W = ∞ X l =0 a | k 1 − k 2 | σ 2 T (1 − e − γ ∆ τ ) e − γ ∆ τ l e j 2 π ( n − m )∆ f l/W = a | k 1 − k 2 | σ 2 T (1 − e − γ ∆ τ ) 1 − e − γ ∆ τ + j 2 π ( n − m )∆ f l ∆ τ (34) By ( 1), (31), and (34), we get V ar [ H A,m [ k ] − H A,m [ k − 1]] = V ar [ ǫ A,m [ k ] − ǫ A,m [ k − 1] + N A,m [ k ] − N A,m [ k − 1]] = V ar [ ǫ A,m [ k ]] + V ar [ ǫ A,m [ k − 1]] − 2 Cov [ ǫ A,m [ k ] , ǫ A,m [ k − 1]] + V ar [ N A,m [ k ]] + V ar [ N A,m [ k − 1]] = 2 σ 2 T − 2 E [ ǫ A,m [ k ] ǫ ∗ A,m [ k − 1]] + 2 σ 2 N = 2 σ 2 T (1 − a ) + 2 σ 2 N (35) The th ermal n oise com ponents are ind ependen t o f each other and all the other variables, and the fixed part of the c hannel can b e viewed as constant, so ∀ m 6 = n r ( m − n ) = Cov [ H A,m [ k ] − H A,m [ k − 1] , H A,n [ k ] − H A,n [ k − 1]] = Cov [ ǫ A,m [ k ] − ǫ A,m [ k − 1] , ǫ A,n [ k ] − ǫ A,n [ k − 1]] = E [ ǫ A,m [ k ] ǫ ∗ A,n [ k ]] + E [ ǫ A,m [ k − 1] ǫ ∗ A,n [ k − 1]] − E [ ǫ A,m [ k ] ǫ ∗ A,n [ k − 1]] − E [ ǫ A,m [ k − 1] ǫ ∗ A,n [ k ]] = 2 σ 2 T (1 − a )(1 − e − γ ∆ τ ) 1 − e − γ ∆ τ + j 2 π ( n − m )∆ τ ∆ f = 2 σ 2 T (1 − a )(1 − e − 2 π B c /W ) 1 − e − 2 π B c /W + j 2 π ( n − m ) / M (36) It can be easily proved th at H A [ k ] − H A [ k − 1] has zero mean an d is a Gaussian random variable, since it is the linear combinatio n of Gaussian ran dom variables. A P P E N D I X I I P R O O F O F R E L A T I O N S H I P 2 For the case with spatially in depend ent t ime variation where ǫ E ,m [ k ] and ǫ A,m [ k ] are indep endent ide ntically distributed, from (1) and (6) we h av e V ar [ H E ,m [ k ] − H A,m [ k − 1]] = V ar [ ǫ E ,m [ k ] − ǫ A,m [ k − 1] + N E ,m [ k ] − N A,m [ k − 1]] = V ar [ ǫ E ,m [ k ]] + V ar [ ǫ A,m [ k − 1]] + V ar [ N A,m [ k ]] + V ar [ N E ,m [ k ]] = 2 σ 2 T + 2 σ 2 N (37) 9 And ∀ m 6 = n , Cov [ H E ,m [ k ] − H A,m [ k − 1] , H E ,n [ k ] − H A,n [ k − 1]] = Cov [ ǫ E ,m [ k ] − ǫ A,m [ k − 1] , ǫ E ,n [ k ] − ǫ A,n [ k − 1]] = E [ ǫ E ,m [ k ] ǫ ∗ E ,n [ k ]] + E [ ǫ A,m [ k − 1] ǫ ∗ A,n [ k − 1]] = 2 σ 2 T (1 − e − γ ∆ τ ) 1 − e − γ ∆ τ + j 2 π ( n − m )∆ τ ∆ f = r ( m − n ) / (1 − a ) (38) From (1) and (6) we also see that E [ H E [ k ] − H A [ k − 1]] = H E − H A . The other part is similar to that of Relation ship 1. R E F E R E N C E S [1] N. Borisov , I. Goldber g, and D. W agne r , “Intercept ing m obile commu- nicat ions: the insecurit y of 802.11, ” in Proc. A CM Annual Internati onal Conferen ce on Mobile Computing and Netwo rking (MOBICOM), pp. 180– 189, Sept. 2002. [2] A. Mishra, M. Shin, and W . A. Arbaugh, “Y our 802.11 network has no clothe s, ” IEEE Communicati ons Magazin e , vol . 9, pp. 44 – 51, Dec. 2002. [3] J. W alk er , “Unsafe at an y k ey si ze: an ana lysis of the WEP encapsula tion, ” IEEE Document 802.11-00/362, 2000. [4] A. J. V iterbi , CDMA: Principles of Spread Spectrum Communicati on , Redwo od City , CA: Addison-W esle y Wire less Communications Series, 1995. [5] G. J. Foschini and M. J. Gans, “On limits of wireless communica tions in a fadi ng en vironment when using multiple ante nnas, ” IEE E W ir ele ss P ersonal Communication s , vol. 6, pp. 311–335, March 1998. [6] R. Wi lson, D. T se, and R. Scholtz, “Channe l identifica tion: Secret sharing using reciprocity in UWB channels, ” IEEE T ransac tions on Information F orensics and Security , vol. 2, pp. 364–375, Sept. 2007. [7] A. E. Hero, “Secure space -time communication, ” IEEE T ransactions on Informatio n Theory , pp. 3235–3249, Decembe r 2003. [8] S. Goel and R. Negi, “Secret communicati on in presence of colluding eav esdrop pers, ” in Proc. IEEE Military Communications Confere nce (MILCOM) , vol. 3, pp. 1501– 1506, Oct. 2005. [9] A. Mishra and W . A. Arbaugh, “ An initia l security analysis of the IEEE 802.1x standard, ” T ech. Rep. CS-TR-4328 , Unive rsity of Maryla nd, Colle ge Park, 2002. [10] C. Corbett, R. Beyah, and J. Copeland, “ A passi ve approach to wireless NIC identific ation , ” in Proc . IEE E Internationa l Confer ence on Communicat ions , vol. 5, pp. 2329–2334, June 2006. [11] J. Hall, M. Barbeau, and E . Kranakis, “Detecti on of transient in radio frequenc y fingerprint ing using signal phase, ” in W irele ss and Optical Communicat ions , A CT A Press, pp. 13-18, July 2003. [12] T . Koh no, A. Broido, and C. Claf fy , “Remote physical device finger - printin g, ” in IEEE T ransactions on Dependable and Secur e Computing , vol. 2, pp. 93– 108, April–June 2005. [13] T . Daniels, M. Mina, and S. F . Russell, “Short paper: a signal fingerprint ing paradigm for general physical layer and s ensor network security and assurance, ” in Pro c. IEE E/Cr eate Net Secur e Commum. , pp. 219– 221, Sept. 2005. [14] D. Fa ria and D. Cheriton, “Detectin g ident ity-ba sed attacks in wireless netw orks using signalprin ts, ” in Proc. ACM W orkshop on W irel ess Security , pp. 43 – 52, Los Angele s, California , Sept. 2006. [15] M. Demirbas and Y . Song, “ An RSSI-based scheme for sybil attack detec tion in wireless sensor networks, ” in Pr oc. Internation al W orkshop on Advanced Experimental Activi ty , pp. 564 – 570, June, 2006. [16] L. Xiao, L. Greenstei n, N. Mandayam, and W . Trapp e, “Fingerprin ts in the ether: Using the physical layer for wireless authentic ation , ” in Pr oc. IEEE International Confer ence on Communicati ons , Glasgo w, Scotla nd, June 2007. [17] W . Trapp e and L.C. W ashington, Intr oduction to Cryptograph y with Coding T heory , Upper Saddle Riv er, NJ: Prentice Hall, 2002. [18] T .S. Rappaport , W ireless Communications- Principles and Practic e , Engle woo d Clif fs, NJ: Prentice Hall, 1996. [19] W .C. Jakes Jr ., Micr owave Mobile Communic ations , Piscataw ay , NJ: W ile y-IEEE Press, 1994. [20] P .A. Bello, “Charac teriz ation of randomly time-va riant linea r channel s, ” IEEE T rans. Commun. Syst. , vol. CS-11, pp. 360–393 , Dec. 1963. [21] V . Erce g, D. G. Michelson, S. S. Ghassemza deh, L. J. Greenstein, A. J. Rustak o, P . B. Guerlain, M. K. Dennison, R. S. Roman, D. J. Barnick el, S. C. W ang, and R.R. Miller , “ A model for the multipat h delay profile of fixed wireless channe ls, ” IEEE J . on Sel. Are as in Commun. , vol. 17, pp. 399–410, 1999. [22] P .A. Bell o and B.D. Nelin, “The effec t of frequenc y selecti ve fading on the binary error probabil ity of incoherent and diff erenti ally coherent matched filter recei v ers, ” IEEE T rans. Commun. Syst. , vol. CS-11, pp. 170–186, June 1963. [23] M. Abramowit z and I A. Steg un, New Y ork: Handbook of Mathema tical Functions, W ith F ormulas, Graphs, and Mathematica l T ables , Courier Dov er Publications, 1965. [24] S. J. Fortune , D. H. Gay , B. W . Kernigh an, O. L andron, M. H. Wright, and R. A. V alenzuela , “W iSE design of indoor wireless systems: Practic al computati on and optimizati on, ” IEEE Computational Science and Engineerin g , vol. 2, pp. 58-68, Mar . 1995. [25] A. T ee, “Clarificati ons on the link budg et ev alu ation, ” IE EE Document C802.20-05/1 8, 2005.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment