On the Capacity Bounds of Undirected Networks
In this work we improve on the bounds presented by Li&Li for network coding gain in the undirected case. A tightened bound for the undirected multicast problem with three terminals is derived. An interesting result shows that with fractional routing,…
Authors: Ali Al-Bashabsheh, Abbas Yongacoglu
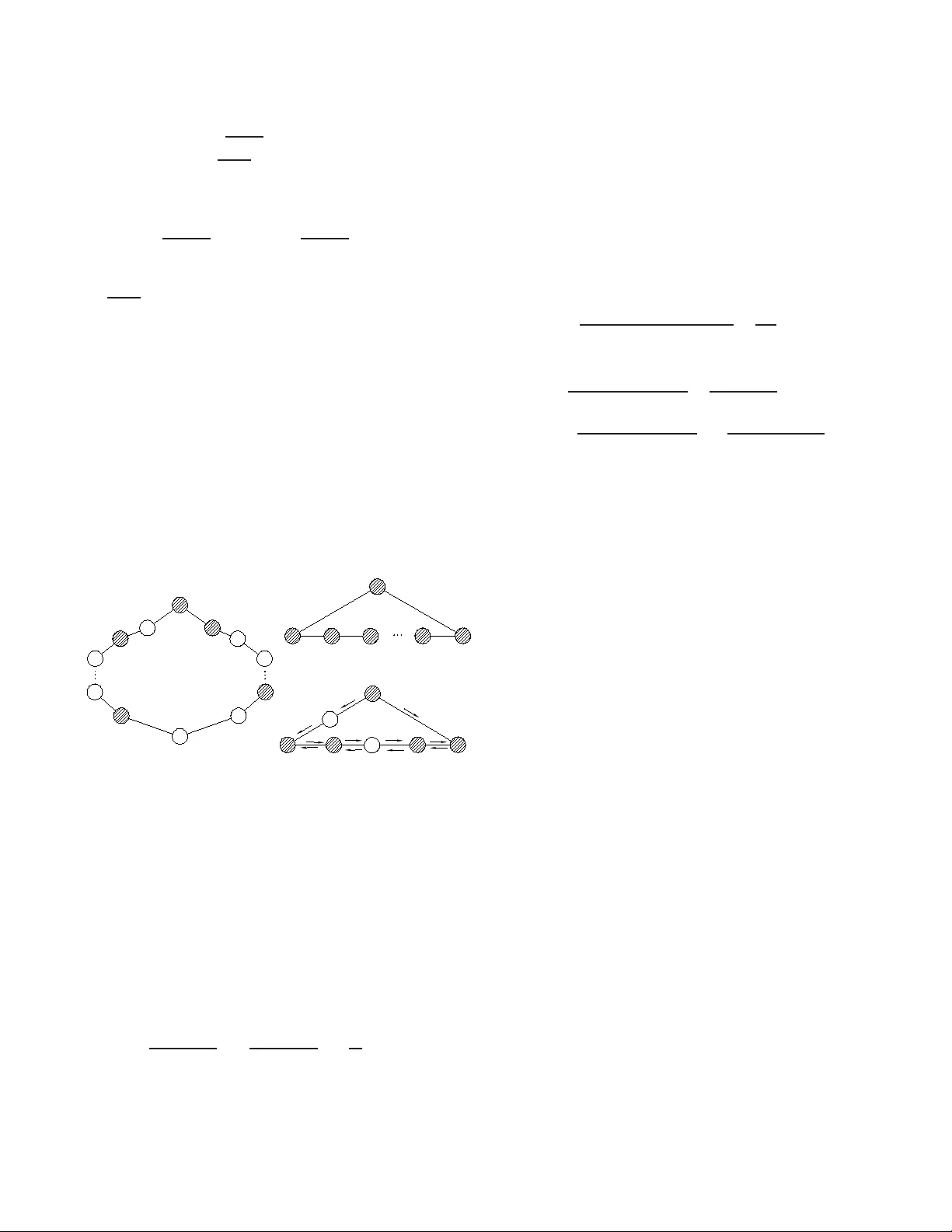
On the Capacity Bounds of Und irecte d Networks Ali Al-Bashabsh eh and Abbas Y ongaco glu School of Information T echnology and Engineering Univ ersity of Ottawa, Ottawa, Canada { aalba059, yongaco g } @site.uottawa.ca Abstract — In this work we improv e on the bounds presented in [ 1] fo r network coding gain in the undirected case. A tightened bound for the undirected multicast problem with three terminals is derive d. An interesting result sho ws that with f ractional routing, routing throughput can achiev e at least 75% of th e coding throughput. A tighter bound f or the general multicast problem with any number of terminals shows that coding gain is strictly less than 2. Our d eriv ed bound depen ds on the nu mber of terminals in the multicast n etwork and approaches 2 for arbitrarily large number of terminals. I . I N T R O D U C T I O N Network codin g gain , G , is d efined as the improvement in network thro ughp ut due to codin g compare d to routing throug hput. It is well known that network cod ing increases the space over which through put is maxim ized and th us provides a capacity a t least as high as the ro uting one. In this work , capacity of a network refers to the max imum achiev able throug hput und er a cer tain co ding scheme (routing can be considered as a co ding schem e with iden tity map ping) . For a set of sinks in a directed m ulticast network , it was shown in [2] that if the network c an achieve a certain thr ough put to eac h receiver ind ividually , then it can achieve the sam e throug hput to all the sinks simultaneously by allowing coding at inter mediate node s and thu s, ach iev e a thro ughp ut gain . This has ign ited an area o f research try ing to answer m any questions; one of them is how much gain is po ssible? Th ere has been some instan ces in th e literature where the network coding gain can be unb ound ed fo r directed networks [3] [4]. Relating coding gain to the in tegrality gap o f linear progr amming form ulation for minimum weig ht Steiner tree [5], furth er examples of directed networks with arbitrar ily high coding gain can b e obtained [6] [ 7]. For undirected n etworks, it was shown in [1] that network cod ing gain is bo unded by 2 w hen half integer rou ting is possible. Such a dramatic difference between dir ected and undire cted multicast n etworks results because directed networks ca n be oriented in a way such th at routing can o ffer little compared to co ding. I n th is work we further in vestigate achiev able routing throughputs and derive tigh ter b ound s on th e possible cod ing gain . This work is organ ized as f ollows. Section I I introduc es some necessary de finitions. I n Section III we use a Steiner tree p acking argue to present b ound s on the achiev able routing throug hput and d erive upper bo unds on coding gain. I I . D E FI N I T I O N S An und irected network G on V node s an d E links can b e modeled as an u ndirected grap h G ( V , E ) that might co ntain multiple edges, i.e. a multigrap h. At c ertain places we m ight refer to th e sets of vertices and ed ges o f a g raph H (especially if they are not explicitly specified) as V ( H ) and E ( H ) , respectively . A mu lticast n etwork with a so urce nod e s ∈ V and a set of sinks R = { R 1 , . . . , R |R| } ⊆ V − s is a network where s bro adcasts d ata to all the receivers in R . At certain places in this work we might not distinguish between a so urce or a sink n ode and simply refer to such a node as a terminal . If |R| = V − 1 then we call G a br oadcast network. W e assume that edg es capa cities are defined over the same base as the so urce sym bols. In other words, an ed ge with capacity C can carry at most C symbols. Integer ro uting throug hput ref ers to th e routing throughp ut ach ieved by routing scalar symbo ls throu gh edges of the network. Considering multiple time units in a network, fr actional routing through put denotes the th roug hput ach iev ed by upscalin g edge capac ities by n d ivided by n . S uch a rou ting scheme may also be referred to as vector routing and it was s hown in [8] that doub ling edges capacities can re sult in a throug hput more than twice as good . If we let h denote the number of symbols a multicast network can d eliv er f rom the so urce to all sinks, we can define co ding and fractional and integer rou ting capacities as: γ = sup h/n ∈ Q + : h/n is an achiev a ble codin g rate π f = sup h/n ∈ Q + : h/n is an achiev a ble routin g rate π i = sup h ∈ Z + : h is an achiev able integer rou ting rate where Z + and Q + are the sets of po siti ve integers and positive rational n umbers, respectiv ely . A fractional routing sch eme with n = 2 will be ref erred to as half integer routing and the corr espondin g capac ity will be denoted by π 1 2 . In th e following, if a statement is true for both integer and fraction al routing , we ma y d rop the subscripts a nd simply write π . The gain in th roug hput due to coding compar ed to integer , half- integer and fractional routing is defined as G i = γ π i , G 1 2 = γ π 1 2 and G f = γ π f , respectiv ely . For a g raph G = ( V , E ) , an induced subg raph T is called a span ning tr ee if and only if T is a tree a nd V ( T ) = V ( G ) . For A ⊆ V , a subtree T of G is c alled an A -Stein er tr ee ( A - Spanning tree) if and only if A ⊆ V ( T ) . Steiner tree pac king refers to fin ding the maximum nu mber of ed ge disjoint A - Steiner tr ees in G . Edge co nnectivity , λ ( G ) , of a con nected g raph G is the size of th e smallest set F ⊆ E ( G ) such that G − F is disconnected ( G − F d enotes the graph induced from G b y deleting all edges e ∈ F ). A graph G is l -e dge connected for any integer l ≤ λ ( G ) . For A ⊆ V ( G ) , λ G ( A ) denotes the edge connec tivity of A in G . The minimum size o f a cut between a pair of vertices u, v ∈ V ( G ) is the edge connectivity , λ G ( u, v ) , of u and v in G which by Menger’ s theo rem equals the maxim um number of edge disjoint paths between u and v . A cu t-edge (bridg e) is an e dge e ∈ E ( G ) such that G − e is disconn ected (clearly , λ ( G ) must be 1 for such an ed ge to exist). Th e degree of u ∈ V is the num ber of incid ent ed ges to u and is d enoted as d ( u ) . If the u nderlyin g grap h G is clear from the con text, we might dr op the subscript G from the previous quantities. Let e = r x and f = xt be two edge s in G ( V , E ) . Splitting off the pair o f ed ges e an d f refers to deleting e and f an d introdu cing a new edge g = rt . W e refer to the pair e, f and g as the splitted and the splitting ed ges, respectively . W e also den ote the resulting gra ph af ter splitting off edge s e, f as G ef . A pa ir of edg es e, f inciden t with x is ad missible if λ G ef ( u, v ) = λ G ( u, v ) for every u 6 = v ∈ V − x . An incide nt edge to x is admissible if it belongs to an admissible pair, otherwise it is n on-ad missible. A comp lete splitting at x ∈ V (when d ( x ) is even) refer s to: 1) repeated ly splitting off pairs of inciden t e dges to x u ntil x is iso lated, and 2) deleting x . W e den ote the graph resulting f rom a complete splitting at x as G x and call such a splitting a suita ble one if every splitting in step 1 ) is admissible, i.e. all edg es incid ent to x belong to disjoint admissible pairs. I I I . B O U N D S O N A C H I E V A B L E R AT E S F O R U N D I R E C T E D N E T WO R K S For netw ork G mod eled as an undirected graph G ( V , E ) and a set of term inals A ⊆ V , using a max- flow min-cut argument, the network coding capacity is trivially up per bounde d by λ ( A ) . Note that un like d irected networks (where the min-cu t throug hput is always achievable v ia coding over a suffi ciently large field [2] [9]) in the und irected case a throug hput of λ ( A ) m ight no t be achiev able (see exam ple 2). It is also clear that π ≤ γ since routing is a special type o f coding wher e only rep etition and fo rwarding are allowed at re lay nod es. If λ ( A ) = 1 , then it is clear that γ = π = 1 and hen ce we can always assume λ ( A ) ≥ 2 . On the oth er hand, if λ ( G ) = 1 and λ ( A ) ≥ 2 then V ( G ) can be partition ed into two disjoint subsets V ( G 1 ) an d V ( G 2 ) with A ⊆ V ( G 1 ) an d G 1 and G 2 connected via a cut-edge. In this case we c an always de lete G 2 without affecting the thro ughp ut. In con clusion, we can always assume that G is 2- edge connected, i.e. G contain s no cut-edge s. A. Mu lticast Networks with Thr ee T ermina ls Let G = ( V , E ) be a g raph repr esenting a multicast n etwork with a set o f term inals A = { s, R 1 , R 2 } ⊆ V , the f ollowing theorem p rovides a lower boun d on th e routing cap acity , Theorem 1 : F or an un dir ected mu lticast network with thr ee terminals, the inte ger , half inte ger an d fractiona l r o uting capacities ar e bound ed as π i ≥ 6 λ ( A ) − 3 8 π 1 2 ≥ 1 2 12 λ ( A ) − 3 8 π f ≥ 3 λ ( A ) 4 − ǫ wher e ǫ is a rbitrarily small for arbitrarily lar ge n and λ ( A ) is th e connectivity of A in G . Proof : The proof m akes use of the f ollowing th eorem Theorem 2 ( Kriesell, [10]). F or any inte ger k ≥ 1 , let A = { v 1 , v 2 , v 3 } b e 8 k +3 6 -edge conn ected in G , then th er e exists a system of k ed ge disjoint A -Steiner tr ees in G . Let A = { v 1 , v 2 , v 3 } be the set of termina ls and let A be λ ( A ) -edge con nected in G . Noting th at any p ositiv e integer , a , can be written as a = dq + b ; for some cho ice q ∈ { 0 } ∪ Z + , d ∈ { 1 , 2 , . . . , a } and b ∈ { 0 , 1 , 2 , . . . , d − 1 } (1) Consider, 8 k + 3 6 = (6 + 2) k + 3 6 = k + 2 k + 3 6 , ∀ k ∈ Z + From (1 ) with d = 3 , we can write k = 3 q + m , m ∈ { 0 , 1 , 2 } . Thus, 8 k + 3 6 = 3 q + m + 6 q + 2 m + 3 6 = 4 q + m + 2 m + 3 6 , m ∈ { 0 , 1 , 2 } = 4 q , m = 0 4 q + 1 , m = 1 4 q + 3 , m = 2 Thus, if λ ( A ) is any p ositiv e integer such that λ ( A ) = 4 q + j , j ∈ { 0 , 1 , 3 } , we can wr ite λ ( A ) = 8 k +3 6 for some p ositiv e integer k . The only class of positive integers left is the one such that λ ( A ) = 4 q + 2 . For this choice of integers, we can write λ ( A ) = 4 q + 1 + 1 = 8 k +3 6 + 1 for so me positive integer k . Hence, f or any positi ve integer , λ ( A ) , ther e exist a positive integer k for whic h λ ( A ) = 8 k +3 6 + δ , wher e k is the largest in teger such that 8 k +3 6 ≤ λ ( A ) an d δ ∈ { 0 , 1 } . For δ = 0 , T heorem 2 ensures the existence o f k edg e disjoint A -Stein er tre es. Thus, λ ( A ) = 8 k + 3 6 ≤ 8 k + 3 6 Which lead s to k ≥ 6 λ ( A ) − 3 8 ≥ 6 λ ( A ) − 3 8 (2) For δ = 1 , Th eorem 2 also ensures the existence o f at least k ed ge disjoin t A -Steiner trees, where λ ( A ) = 8 k +3 6 + 1 , from wh ich we first obtain k < 6 λ ( A ) − 3 8 (3) we also obtain the following lower b ound on k k ≥ 6( λ ( A ) − 1) − 3 8 (4) Upon combining (3) and (4), k can be bound ed as, 6 λ ( A ) − 3 8 − 6 8 ≤ k < 6 λ ( A ) − 3 8 Noting that 6 λ ( A ) − 3 8 = 6 λ ( A ) − 3 8 + ∆ 8 , ∆ ∈ S ⊂ { 1 , 2 , . . . , 7 } (5) (More specifically , it can be shown tha t for any integer λ ( A ) , i.e. δ can be 0 or 1 , ∆ ∈ { 1 , 3 , 5 , 7 } , see p art-A o f the Append ix). Thus the in equality fo r k become s 6 λ ( A ) − 3 8 − 6 − ∆ 8 ≤ k < 6 λ ( A ) − 3 8 + ∆ 8 (6) Note that k is an integer, hence the previous in equality indicates that k = j 6 λ ( A ) − 3 8 k except for ∆ = 7 , where the inequality has n o valid solution. Therefo re, our task is to p rove that δ = 1 dismisses ∆ = 7 . T o prove this, note that for δ = 1 we hav e λ ( A ) = 4 q + 2 , q ∈ { 0 } ∪ Z + . Hence, 6 λ ( A ) − 3 8 = 3 × 8 q + 9 8 = 3 q + 1 + 1 8 = ⇒ ∆ = 1 Which shows that ∆ is a lways 1 for δ = 1 . From this we conclud e th at the solution presented earlier is a valid one. Combining this r esult with the one o btained for the ca se of δ = 0 in (2), we can write k ≥ 6 λ ( A ) − 3 8 , for any λ ( A ) ∈ Z + (7) Sending one symb ol o n each tree, an integral rou ting through- put of k is achievable. Since π i is the supreme of all achiev ab le rates, thus π i ≥ k and the first b ound results. If half-in teger routing is allowed, we can up scale the edge capacity b y 2 and then divide the integer part of the result by 2. Since this is an achievable r outing rate, it represen ts a lower b ound on the half integer rou ting capacity and th us proves the second part o f the theorem. For f ractional rou ting, we upscale edge capacities b y n and then divide the integer p art o f the result by n , i. e. π f ≥ 3 λ ( A ) 4 − 3+∆ 8 n . For sufficiently large n , the second part ap proach es z ero a nd the th ird b ound results. Corollary 1 : F or a thr ee terminal multicast n etwork, the coding g ain is bo unded as G i ≤ λ ( A ) j 6 λ ( A ) − 3 8 k G 1 2 ≤ 2 λ ( A ) j 12 λ ( A ) − 3 8 k G f ≤ 4 3 + ǫ ′ Proof : G = γ π ≤ λ ( A ) π ≤ λ ( A ) Lowe r bound on π . Apply ing the approp riate lower bound from theo rem 1 and th e corollary results. From co rollary 1 , it can be seen tha t the coding gain is always bounded . Mor e specifically , G i is bo unded by 3 for λ ( A ) ≥ 2 while G 1 2 is strictly less than 2 for λ ( A ) > 2 . The bound for G f indicates that with fractional routing, 7 5% of the thr ough put achie vable by codin g is alw ays achiev a ble via routing . B. Mu lticast Networks with Arbitrary Number of T erminals Let G be a multicast n etwork mo deled as an undi- rected graph G ( V , E ) with a set of N − 1 receivers R = { R 1 , . . . , R N − 1 } and th us a set of term inals A = s ∪ R ⊆ V . The set X = V − A repr esents the set of non -terminal ( relay) nodes in G . Lemma 1 : If G x , the graph ob tained fr om G by p erforming a suitable complete splitting at x ∈ V − A , conta ins a system of k edge disjoin t A -Steiner trees, then G con tains k edge disjoint A -stein er trees . Proof : Le t T be a set of k disjoint A -Steiner trees in G x . If d ( x ) = 2 , let w be the added edg e after sp litting off edg es e and f . For a ny T ∈ T , if T con tains w then T − w , the edges e, f and the vertex x form an A -Steiner tree T ′ in G and the set ( T − T ) ∪ T ′ forms a set of k ed ge disjoint A - Steiner tr ees in G . I f no T ∈ T c ontains w , then T is a set of A -Steiner trees in G . If d ( x ) 6 = 2 , let W be the set of splitting ed ges an d e ( w ) , f ( w ) be the splitted pa ir by w . Also let T W = { T ∈ T : T ∩ W 6 = ∅} . For every T ∈ T W , the tree T ′ formed by T − W , S w ∈ W ∩ E ( T ) g w and x is an A -Steiner tree in G , wher e g w ∈ {∅ , { e ( w ) } , { f ( w ) } , { e ( w ) , f ( w ) }} . Let T ′ be the set of such trees, then ( T − T W ) ∪ T ′ forms a set o f k edg e disjoin t A -Steiner trees in G . Alternative proof : Since splitting o ff d oes not in crease con- nectivity and complete splitting is a series of splitting off ’ s then λ G x ( u, v ) ≤ λ G ( u, v ) f or a ll distinct u, v ∈ V ( G ) − x , with equality if and only if the splitting is su itable. Thus, if G x contains k -e dge disjoint A -Steiner trees, then G does as well. The follo wing th eorem provides a lower bou nd o n the fractional r outing c apacity , π f . Theorem 3 : F or a multicast network repr esented by a n undirected g raph G ( V , E ) with a set of termina ls A ⊆ V π f ≥ λ ( A ) 2 | A | | A | − 1 − ǫ wher e ǫ is a rbitrarily small for arbitrarily lar ge n and λ ( A ) is th e connectivity of A in G . Proof : The proof u ses th e fo llowing two theo rems Theorem 4 ( Kriesell, [1 0]): F or any l, k ≥ 2 , let G ( V , E ) be an 2 k l − 1 l + l − 2 l -edge connected graph on l vertices. Then ther e exist a system of k edge d isjoint spanning trees in G . Theorem 5 (Frank , [11]): Let G ( V + x, E ) be a co nnected graph on V + x , d ( x ) 6 = 3 and no cut-edge is in cident to x . Then th er e exist j d ( x ) 2 k disjoint a dmissible p airs at x . Consider a complete splitting at e very relay node x ∈ V − A . Since G is 2 -ed ge connected , then there are no cu t-edges in G . From theo rem 5, if d ( x ) is even then all incident edg es to x can be partitioned into disjoin t admissible pair s. Since half integer routing is allowed, we can make d ( x ) even fo r every x ∈ V − A by up scaling th e capacities of the e dges of G by 2 and then downscaling the solution by 2. Thu s a suitable complete splitting exists at all r elay nod es in G . Let G ′ be the graph o btained after su ch splitting , then V ( G ′ ) = A an d an A -Steiner tr ee in G ′ is a spann ing tree in G ′ . Next we pr ove that λ ( A ) being any integer, it can b e written as λ ( A ) = 2 k ( | A | − 1) + | A | − 2 | A | + δ (8) for any | A | ≥ 2 and som e integer k , w here δ ∈ { 0 , 1 } . Let f | A | ( k ) = j 2 k | A |− 1 | A | + | A |− 2 | A | k , it is easy to check that f | A | ( k + 1) − f | A | ( k ) = 2 + j ∆ − 2 | A | k , ∆ ∈ { 0 , 1 , . . . , | A | − 1 } . No ting that j ∆ − 2 | A | k ∈ { − 1 , 0 } then , f | A | ( k + 1 ) − f | A | ( k ) ∈ { 1 , 2 } . If there exist an integer k such that λ ( A ) = f | A | ( k ) the n δ = 0 and we a re don e. Otherwise, we ch oose k as the largest integer such that λ ( A ) > f | A | ( k ) . By th e choice of k , λ ( A ) < f | A | ( k + 1) and since f | A | ( k + 1) − f | A | ( k ) ≤ 2 for any | A | then λ ( A ) = f | A | ( k ) + 1 . Thus, for any integer λ ( A ) , we can write λ ( A ) = f | A | ( k ) + δ , δ ∈ { 0 , 1 } , proving the claim in(8). For λ ( A ) = j 2 k ( | A |− 1)+ | A | − 2 | A | k + δ , theorem 4 ensures the existence of k e dge disjoint span ning trees in G ′ , where f or δ = 0 we have k ≥ j | A | λ ( A ) −| A | +2 2( | A |− 1) k . If δ = 1 , then λ ( A ) = j 2 k ( | A |− 1)+ | A | − 2 | A | k + 1 > 2 k ( | A |− 1)+ | A | − 2 | A | which results in k < j | A | λ ( A ) −| A | +2 2( | A |− 1) k + ∆ ′ 2( | A |− 1) , ∆ ′ ∈ { 0 , 1 , . . . , 2 ( | A | − 1 ) − 1 } . Also λ ( A ) − 1 = j 2 k ( | A |− 1)+ | A | − 2 | A | k ≤ 2 k ( | A |− 1)+ | A | − 2 | A | results in k ≥ j | A | λ ( A ) −| A | +2 2( | A |− 1) k + ∆ ′ −| A | 2( | A |− 1) . Upon combining the abov e two limits of k , we can write j | A | λ ( A ) −| A | +2 2( | A |− 1) k + ∆ ′ −| A | 2( | A |− 1) ≤ k < j | A | λ ( A ) −| A | +2 2( | A |− 1) k + ∆ ′ 2( | A |− 1) which ind icates that a valid solution for k exists as long as ∆ ′ ∈ { 1 , 2 , . . . , | A |} . But δ = 1 implies that th at this is the case (part-B o f the App endix). Thus fo r δ = 1 , k = j | A | λ ( A ) −| A | +2 2( | A |− 1) k . Combin ing this with the result ob tained for δ = 0 , we conclude that for a ny integer λ ( A ) ≥ 2 , the numb er o f edge- disjoint A -Steiner trees in G ′ is k ≥ j | A | λ ( A ) −| A | +2 2( | A |− 1) k . By Lemm a 1, if G ′ contains k edg e disjoint A -Steiner trees then G does, provided that a suitab le co mplete splitting exists at e very relay node x ∈ V − A . As it was sh own at the beginning of this argum ent, such a splitting exist if we upscale the capacity of every edg e in G by 2 and then d ownscale our result by 2. Thus, we conclu de that G co ntains k edge disjoint A - Steiner trees, where k ≥ 1 2 j 2 | A | λ ( A ) −| A | +2 2( | A |− 1) k . Since this repre sents an achievable thro ughp ut, it also represents a lower bound on the half integer routing capacity . For fractional routing , we u pscale the edge ca pacities by n an d d ivide th e result by n an d for sufficiently large n we obtain π f ≥ λ ( A ) 2 | A | | A |− 1 − ǫ . Corollary 2 : F or a multicast n etwork r epr esented by an undirected g raph G ( V , E ) with a set of termina ls A ⊆ V G f ≤ 2 | A | − 1 | A | + ǫ ′ Proof : Proof is similar to the o ne o f corollary 1. C. Exa mples Example 1 : For the multicast network in Fig.1(a), λ ( A ) = 2 . The graph resulting fr om upscaling edg e capacities by 2 an d then per forming suitable complete splitting at all relay (no n- hatched) nodes is shown in Fig. 1(b), where thick ed ges have double the c apacity of normal ones. G ′ is a broadcast network, and from th eorem 3 with A = V ( G ′ ) the routing cap acity of G ′ can be b ound ed as π f ≥ 4 3 . From theor em 3, th is also serves as a lower bo und on the routing capacity of G an d thus the codin g g ain in G is boun ded b y G f ≤ 1 . 5 . Note that 4 3 is a lower bo und o n the capacity , a routing scheme achieving a throug hput of 1.5 fo r G ′ using fractiona l r outing with h = 9 and n = 6 is shown in Fig. 1(b). For the network on G , a fractional routin g throu ghpu t of 1 . 8 is possible with h = 9 and n = 5 , Fig.1(a). s s { a 0 , a 1 , . . . , a 8 } { a 0 , a 1 , . . . , a 8 } a 0 ... a 4 a 1 a 2 a 6 a 7 a 8 a 4 a 5 a 6 a 7 a 8 a 0 ... a 4 a 0 ... a 4 a 6 a 7 a 8 a 1 a 2 a 8 a 5 ... a 8 a 4 ... a 7 a 0 a 0 a 5 a 5 a 3 a 3 a 0 ... a 5 a 2 ... a 7 a 3 ... a 8 a 0 a 1 → a 0 a 1 a 2 → a 8 → ← a 6 a 7 a 8 (a) (b) Fig. 1. Example 1: (a)-Multica st Network G . Also s ho wn a fractiona l routing scheme that achie ves a throughput of 1 . 8 . The source has h = 9 messages { a 0 , . . . , a 8 } and the c apacit y of each link i s upscale d by n = 5 . The symbols on the edges represen t the messages carrie d by the edges and the arrows indica te the direction of the flow . All sinks will recov er all the messages and thus a throughput of 9 5 = 1 . 8 is possible. , (b) Splitted graph G ′ togethe r with a fractional routing scheme that ach ie ves a throughput of 9 6 = 1 . 5 . Example 2 : Fig .2(a) r epresents a multicast network with a set of terminals A = { v 0 , v 1 , . . . , v | A |− 1 } and a set of relay nodes X = { x 1 , . . . , x | X | } where X = V − A an d v 0 is assumed to be the so urce node. The gr aph G ′ resulting from perfor ming suitable complete splitting at all relay no des is shown in Fig.2(b). From theorem 3 with λ ( A ) = 2 , the rou ting capacity can be lower b ound ed as π f ≥ | A | | A |− 1 for both G and G ′ . Next we show that for the network G in Fig.2(a), γ = π f = | A | | A |− 1 . From [1], γ ≤ η G ( A ) wher e η G ( A ) is the edge str ength defined as η G ( A ) = min E G ( P ) |P | − 1 and the minimization is over all p ossible par titions P = { V 0 , V 1 , . . . , V |P |− 1 } of V ( G ) suc h that each co mponen t , V i , o f the partition P contains at least one terminal, i.e. V i ∩ A 6 = ∅ . E G ( P ) is the total capacity of edges between distinct com ponen ts. Let us choose a partition P such that V i ∩ A = v i ∀ i ∈ { 0 , 1 , . . . , | A | − 1 } . For such a partition, |P | = | A | . Also since G is a cycle with each edge having unit capacity , then E G ( P ) = | A | . Because η G ( A ) is the minimum of the ratio E G ( P ) |P |− 1 over all p ossible p artitions P , then γ ≤ η G ( A ) ≤ | A | | A |− 1 . Co mbining th is with the lower bound on π f obtained earlier fro m theorem 3 and th e fact that π f ≤ γ , we obtain | A | | A | − 1 ≤ π f ≤ γ ≤ | A | | A | − 1 Thus, for th e multicast ne twork G shown in Fig.2(a), π f = γ = | A | | A |− 1 . A rou ting scheme ach ieving the fractio nal capacity can be advised a s fo llows: Let h = | A | and n = | A | − 1 . No de v i forwards the | A | − ( i + 1) symbols a 0 , a 1 , . . . , a | A |− 1 − ( i +1) to terminal v i +1 , ∀ i ∈ { 0 , 1 , . . . , | A | − 2 } . T ermin al v 0 sends | A | − 1 sym bols, a 1 , . . . , a | A |− 1 , to v | A |− 1 . Finally , termina l v i +1 forwards i symbo ls, a | A |− i , . . . , a | A |− 1 , to ward terminal v i , ∀ i ∈ { 1 , . . . , | A | − 2 } . On the oth er hand, all relay nodes in X do no thing but forward ing whate ver they receiv e at the ir input edg e to their o utput ed ge, Fig.2(c). Note th at with such a ro uting schem e, each ed ge carries | A | − 1 sy mbols and each terminal rec eiv es | A | symbols. Achieving a ro uting throu ghpu t of | A | / ( | A | − 1) . Fig .2(c), shows an example with 5 terminals, { v 0 , v 1 , v 2 , v 3 , v 4 } , an d 2 relay nodes, { x 1 , x 2 } . v 0 v 0 v 0 x 1 v 1 x 2 v j v | A |− 1 v 1 v 2 v 3 v | A |− 2 v | A |− 1 (a) (b) (c) a 0 a 1 a 2 a 3 a 0 a 1 a 2 a 3 a 0 a 1 a 2 a 4 a 0 a 1 a 3 a 4 a 0 a 1 a 3 a 4 a 0 a 2 a 3 a 4 a 1 a 2 a 3 a 4 x 1 v 1 v 2 x 2 v 3 v 4 Fig. 2. Example 2: (a)-Multicast Netw ork G , (b) Splitt ed graph, G ′ , (c) An instanc e of G with 5 terminals and 2 relay nodes. A P P E N D I X W e use the notation ( a ) b to denote a modu lo b A. ∆ ∈ { 1 , 3 , 5 , 7 } for the multica st network with thr ee terminals. Proof : From (1) we can write λ ( A ) = 4 q + c, c ∈ { 0 , 1 , 2 , 3 } . Also from (5) 6 λ ( A ) − 3 8 = 6 λ ( A ) − 3 8 + ∆ 8 In o ther words, ∆ = (6 λ ( A ) − 3) 8 = (3 × 8 q + 6 c − 3) 8 = (6 c − 3) 8 thus, ∆ = 5 , c = 0 3 , c = 1 1 , c = 2 7 , c = 3 Note that fo r the case δ = 1 , th en c = 2 and thus, ∆ = 1 as it was shown before . B. F o r the multica st n etwork with an y number of termina ls, ∆ ′ = 0 if and only if ∆ = 0 a nd δ = 0 . Proof : From (8) λ ( A ) = 2 k ( | A | − 1) + ( | A | − 2 ) | A | − ∆ | A | + δ From which we can write, k = | A | λ ( A ) − | A | + 2 2( | A | − 1) + ∆ − | A | δ 2( | A | − 1) = | A | λ ( A ) − | A | + 2 2( | A | − 1) + ∆ ′ + ∆ − | A | δ 2( | A | − 1) where δ ∈ { 0 , 1 } , ∆ ∈ { 0 , 1 , . . . , | A | − 1 } and ∆ ′ ∈ { 0 , 1 , . . . , 2 ( | A | − 1) − 1 } . This shows th at ∆ ′ + ∆ − | A | δ is d ivisible by 2 ( | A | − 1) . Thus, (∆ ′ + ∆) 2( | A |− 1) = | A | δ From this we n ote that if ∆ = 0 and δ = 0 , then ∆ ′ = 0 , which proves the ’if ’ par t of the claim . Conv ersely , if ∆ ′ = 0 , then ∆ = | A | δ , which shows that if δ = 1 , then ∆ = | A | , a contradictio n (since ∆ ∈ { 0 , 1 , . . . , | A | − 1 } ). Thus, δ = ∆ = 0 an d the claim follows. R E F E R E N C E S [1] Z . Li and B. Li, “Netw ork coding in undirected networ ks, ” in Proc. 38th Annu. Conf . Information Science and Systems (CISS) , Princet on, NJ, Mar . 2004, pp. 257–262. [2] R. Ahlswede, N. Cai, S.-Y . L i, and R. W . Y eung, “Network information flo w , ” IEE E T rans. on Info. Theory . , vol. 46, no. 4, pp. 1204–1216, July 2000. [3] S. Jaggi, P . Sanders, P . Chou, M. Ef fros, S. Egner , K. Jain, and L. T olhuizen, “Polyn omial time algorithms for multicast network code construct ion, ” IEEE T rans. on Info. Theory , vol. 51, no. 6, pp. 1973 – 1982, June 2005. [4] C. Chekuri, C. Fragouli, and E. Soljanin ., “On averag e throughput and alphabe t size in netw ork coding, ” IEEE T rans. on Info. Theory , vol. 52, No. 6, pp. 2410–2424, June 2006. [5] A. Agarwal and M. Charikar , “On the advant age of networrk coding for improvi ng network throughput , ” in Proc . 2004 IEE E Information Theory W orkshop , San Antonio, T exas, Oct. 2004, pp. 247–249. [6] L . Zosin and K. Khuller , “On directe d Steiner trees, ” in Pr oc. 13th Annu. ACM/SIAM Symp. Discr ete Algorithms (SOD A) , San Francisco, CA, Januar y 2002, pp. 59–63. [7] E . Halperi n, G. Kortsarz , R. Krauthgamer , A. Sriniv asan, and N. W ang, “Inte gralit y ratio for group Steiner trees and direct ed Steiner trees, ” in Pr oc. 14th Annu. ACM/ SIAM Symp. Discret e Algorithms (SODA) , Balti more, MD, Jan. 2003, pp. 275–284. [8] S. Riis, “Linear ver sus non-li near Boolean func tions in netw ork flo w , ” T ech. Rep., 2003. [Online]. A vaila ble: http:/ /nick.dcs.qmul.ac .uk/ ∼ smriis. [9] S. -Y . R. Li, R. W . Y eung, and N. Cai, “Linear network coding, ” IEEE T rans. on Info. Theory , vol. 49, no. 2, pp. 371–381, Feb. 2003. [10] M. Kriesel l, “Edge-disjo int trees containi ng some giv en vert ices in a graph, ” J ournal of Combina torial Theory , ser . B 88, pp. 53–65, 2003. [11] A. Frank, “On a theorem of mader , ” Discret e Mathematics, 101, pp. 49–57, 1992.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment