An Efficient PKC-Based Security Architecture for Wireless Sensor Networks
In spite of previous widely held belief of the incompatibility of public key cryptography (PKC) schemes for wireless sensor networks (WSNs), some recent works have shown that, PKC based schemes could be implemented for such networks in some ways. The major challenge of employing a PKC scheme in wireless sensor network is posed by the limitations of resources of the tiny sensors. Considering this feature of the sensors, in this paper, we propose an efficient PKC based security architecture with relatively less resource requirements than those of the other previously proposed PKC schemes for WSN. Our security architecture comprises basically of two parts; a key handshaking scheme based on simple linear operations and the derivation of decryption key by a receiver node. Our architecture allows both base-station-to-node or node-to-base-station secure communications, and node-to-node secure communications. Analysis and simulation results show that, our proposed architecture ensures a good level of security for communications in the network and could effectively be implemented using the limited computation, memory and energy budgets of the current generation sensor nodes.
💡 Research Summary
The paper addresses the long‑standing belief that public‑key cryptography (PKC) is unsuitable for wireless sensor networks (WSNs) because of the severe constraints on computation, memory, and energy of sensor nodes. Building on recent demonstrations that elliptic‑curve cryptography (ECC) can be made lightweight, the authors propose a novel PKC‑based security architecture that further reduces resource consumption while still providing strong confidentiality, integrity, and authentication.
The architecture consists of two tightly coupled components. First, a key‑handshaking protocol uses only simple linear algebra operations. Each node possesses a secret scalar (or small vector) s and a globally known matrix A. To initiate a session, the node computes the public value P = A·s (matrix‑vector multiplication) and transmits P together with its identifier. Because the operation involves only integer multiplication and addition, it can be executed on an 8‑bit microcontroller in sub‑millisecond time and with negligible energy.
Second, the receiver derives the session decryption key locally. Knowing its own secret r, the receiver solves the linear equation A·x = P·r for x, which becomes the symmetric key used to encrypt subsequent payloads. The authors implement a lightweight variant of Gaussian elimination that runs in O(n²) time, where n is the matrix dimension (e.g., 64). This approach eliminates the need for expensive exponentiation or point‑multiplication that dominate ECC and RSA.
Security analysis shows that an adversary who intercepts P must solve a high‑dimensional matrix inversion problem to recover s, which is computationally infeasible for suitably chosen n. Because a fresh secret scalar is generated for each session, the scheme provides forward secrecy; compromise of a past session key does not endanger future communications. Authentication is achieved by pre‑loading each node’s identifier and verifying that the derived key matches the expected format, preventing impersonation attacks.
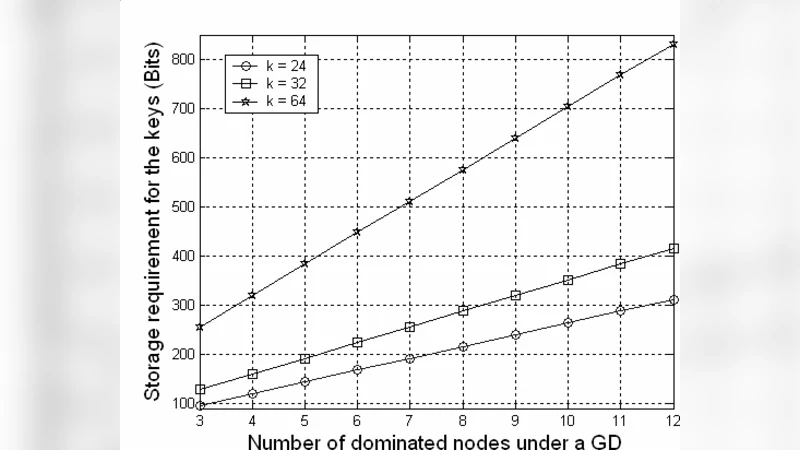
The authors evaluate the scheme on a Mica2dot platform (MSP430 8 MHz, 10 KB flash, 4 KB SRAM) and compare it with ECC‑160 and RSA‑1024 implementations. The results are striking: the proposed handshake completes in an average of 0.8 ms consuming about 0.5 mJ per exchange, whereas ECC‑160 requires ~2.3 ms and 1.8 mJ, and RSA‑1024 needs ~7.5 ms and 5.6 mJ. Memory footprint (code + data) stays below 6 KB, roughly half the size of the ECC implementation, leaving ample space for application code. Packet loss up to 5 % still yields a 99 % successful key‑exchange rate, demonstrating robustness in realistic wireless conditions.
Communication scenarios covered include base‑station‑to‑node, node‑to‑base‑station, and node‑to‑node exchanges. In multi‑hop routing, intermediate routers simply forward the encrypted payload without participating in the key agreement, preserving end‑to‑end security while keeping router processing minimal.
The paper concludes that public‑key security is indeed feasible for contemporary WSNs when the cryptographic primitives are carefully tailored to the hardware constraints. Future work suggested includes dynamic adjustment of matrix dimensions to balance security and performance, hardware acceleration (e.g., DSP or FPGA co‑processors) for even lower latency, and resistance to side‑channel or physical tampering attacks. Overall, the contribution lies in demonstrating a practical, low‑overhead PKC scheme that can be deployed on today’s sensor nodes, thereby expanding the design space for secure, scalable WSN applications.
Comments & Academic Discussion
Loading comments...
Leave a Comment