On the deployment of Mobile Trusted Modules
In its recently published TCG Mobile Reference Architecture, the TCG Mobile Phone Work Group specifies a new concept to enable trust into future mobile devices. For this purpose, the TCG devises a trusted mobile platform as a set of trusted engines on behalf of different stakeholders supported by a physical trust-anchor. In this paper, we present our perception on this emerging specification. We propose an approach for the practical design and implementation of this concept and how to deploy it to a trustworthy operating platform. In particular we propose a method for the take-ownership of a device by the user and the migration (i.e., portability) of user credentials between devices.
💡 Research Summary
The paper examines the Trusted Computing Group’s (TCG) recently published Mobile Reference Architecture, which introduces a novel trust model for future mobile devices. Traditional mobile security relies on a single root of trust (RoT) controlled by the device manufacturer or carrier, making it difficult to accommodate the diverse security requirements of multiple stakeholders such as manufacturers, carriers, service providers, and end‑users. TCG’s architecture replaces this monolithic model with a physical trust anchor (PTA)—typically a TPM 2.0, ARM TrustZone, or similar hardware security module—and a set of isolated Trusted Engines (TEs) that run on behalf of each stakeholder.
The authors first dissect the architecture’s building blocks. The PTA establishes a measured boot, records platform configuration registers (PCRs), and protects cryptographic material. Each TE receives its own certificate, key store, and policy set, and is isolated from other TEs by hardware‑enforced memory and execution domains. This separation enables, for example, a carrier‑managed network‑authentication TE, a manufacturer‑controlled firmware‑update TE, a DRM TE for content providers, and a user‑data protection TE for the device owner.
Next, the paper outlines a concrete integration pathway for mainstream mobile operating systems (Android, iOS, etc.). The process is divided into four stages: (1) measured boot using the PTA, (2) TE initialization and binding of unique keys, (3) definition of a standardized TE‑to‑TE API and capability‑token based permission model, and (4) secure policy management and OTA updates verified by the PTA. The authors propose a lightweight inter‑engine messaging protocol that respects the principle of least privilege while allowing controlled delegation of capabilities.
A central contribution is the “Take‑Ownership” mechanism that empowers the end‑user to become the true owner of the device. In current devices the manufacturer’s root key remains in the TPM, limiting user control. The proposed method lets the user, during first‑boot, replace the factory root key with a newly generated RSA‑4096 or ECC‑P521 key pair. The new key is stored in the TPM’s Owner Hierarchy, and all TEs are re‑provisioned with certificates signed by this user‑controlled root. The procedure involves authenticated key exchange (Diffie‑Hellman‑based AKE), secure input of an Owner Auth password, and revocation of the original manufacturer key. After completion, every subsequent TE operation is anchored to the user’s key, granting full administrative authority.
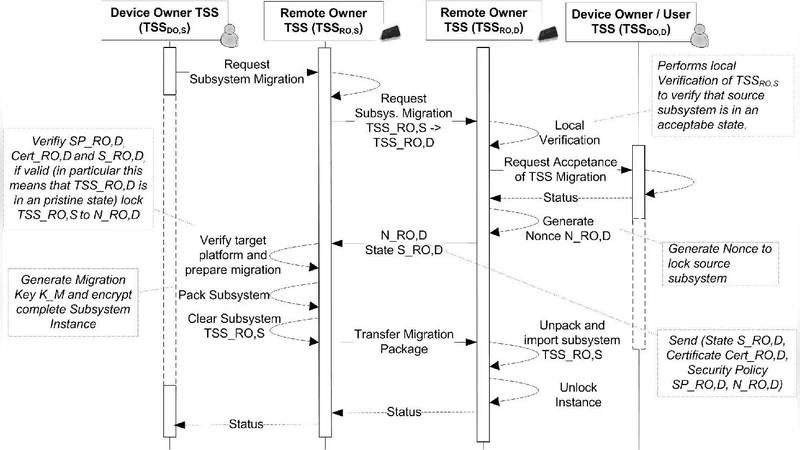
The paper also introduces a migration protocol for portable user credentials. When moving credentials from Device A to Device B, the source TE establishes a TLS 1.3 channel with the destination TE, encrypts the credential bundle, and attaches integrity metadata that includes the source’s PCR values. The destination TE reconstructs an equivalent TE environment, validates the PCR‑based measurements, and only then imports the credentials. This “hand‑over authentication” ensures that even if an attacker intercepts the encrypted bundle, the lack of matching PCR evidence prevents successful replay or tampering.
Security analysis demonstrates that compromising a single TE does not jeopardize the PTA or other engines because each TE’s secrets are sealed to the PTA and verified at launch. The authors measured the performance impact: TE initialization and key exchange add less than 200 ms to the boot sequence, and inter‑engine API calls average 15 µs, which is negligible for real‑time mobile applications.
In conclusion, the paper provides a detailed design and implementation roadmap for deploying TCG’s multi‑engine trust model on real mobile platforms. By enabling user‑centric ownership transfer and secure credential portability, the work moves mobile devices toward a genuinely trusted computing paradigm. Future research directions suggested include dynamic policy negotiation among TEs, integration with cloud‑based attestation services, and the adoption of post‑quantum cryptographic algorithms.
Comments & Academic Discussion
Loading comments...
Leave a Comment