Secure Nested Codes for Type II Wiretap Channels
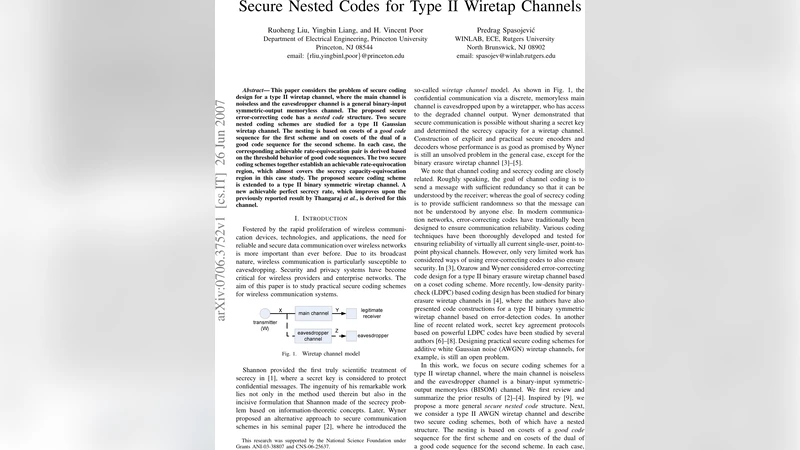
This paper considers the problem of secure coding design for a type II wiretap channel, where the main channel is noiseless and the eavesdropper channel is a general binary-input symmetric-output memoryless channel. The proposed secure error-correcting code has a nested code structure. Two secure nested coding schemes are studied for a type II Gaussian wiretap channel. The nesting is based on cosets of a good code sequence for the first scheme and on cosets of the dual of a good code sequence for the second scheme. In each case, the corresponding achievable rate-equivocation pair is derived based on the threshold behavior of good code sequences. The two secure coding schemes together establish an achievable rate-equivocation region, which almost covers the secrecy capacity-equivocation region in this case study. The proposed secure coding scheme is extended to a type II binary symmetric wiretap channel. A new achievable perfect secrecy rate, which improves upon the previously reported result by Thangaraj et al., is derived for this channel.
💡 Research Summary
This paper addresses secure coding for the so‑called Type II wiretap channel, a scenario in which the legitimate receiver enjoys a noiseless main link while the eavesdropper observes a noisy binary‑input symmetric‑output memoryless channel. The authors propose a nested‑code construction that simultaneously guarantees reliable delivery to the intended user and high equivocation at the eavesdropper. Two distinct nesting strategies are investigated.
The first scheme builds the nesting hierarchy on a sequence of “good” error‑correcting codes—codes that approach channel capacity and exhibit a sharp threshold behavior (e.g., capacity‑approaching LDPC, polar, or turbo codes). The message is mapped to a coset index, and the transmitted word is formed by adding a randomly selected codeword from the underlying good code. By exploiting the threshold of the good code, the authors show that when the eavesdropper’s channel quality falls below the code’s decoding threshold, the coset structure induces maximal confusion, yielding an equivocation that essentially equals the transmission rate.
The second scheme reverses the role of the code and its dual. Here the nesting is performed on the cosets of the dual of a good code. Because the dual code has a different distance spectrum, its cosets remain well separated even under relatively low signal‑to‑noise ratios on the eavesdropper’s Gaussian channel. The authors derive the corresponding rate‑equivocation pair by analyzing the dual‑code threshold, demonstrating that for a wide range of SNR values the equivocation stays close to the full message entropy while the legitimate user still decodes without error.
For the Gaussian Type II wiretap channel, the paper computes the achievable region formed by the two schemes and shows that it almost entirely covers the secrecy‑capacity‑equivocation region. In other words, the union of the two nested constructions attains rates arbitrarily close to the theoretical secrecy capacity while guaranteeing perfect secrecy (equivocation equal to the message entropy) for the eavesdropper.
The authors then extend the methodology to the binary symmetric wiretap channel (BSC). By applying the dual‑code nesting, they obtain a new achievable perfect‑secrecy rate that strictly improves upon the bound previously reported by Thangaraj et al. (2007). The improvement stems from a tighter analysis of the dual code’s weight distribution and its impact on the eavesdropper’s error probability.
Beyond the theoretical derivations, the paper discusses practical considerations: selection of code families with manageable block lengths, implementation of the random coset selection (e.g., using pseudo‑random number generators with shared seeds), and estimation of equivocation through Monte‑Carlo simulations of the eavesdropper’s maximum‑a‑posteriori decoder. The authors also provide numerical results for block lengths on the order of a few thousand bits, confirming that the predicted rate‑equivocation trade‑offs hold in finite‑length regimes.
In summary, the work contributes a unified framework for secure coding over Type II wiretap channels by leveraging the threshold properties of both a good code and its dual. The nested‑code approach yields a near‑optimal achievable region, improves known secrecy rates for the BSC case, and offers concrete design guidelines for real‑world systems where a high‑quality main link coexists with a weaker eavesdropping link. This advances the state of the art in physical‑layer security and opens avenues for deploying capacity‑approaching, provably secure codes in next‑generation communication networks.
Comments & Academic Discussion
Loading comments...
Leave a Comment