📝 Original Info
- Title: Impact of Vehicular Communications Security on Transportation Safety
- ArXiv ID: 0808.2666
- Date: 2016-11-17
- Authors: Researchers from original ArXiv paper
📝 Abstract
Transportation safety, one of the main driving forces of the development of vehicular communication (VC) systems, relies on high-rate safety messaging (beaconing). At the same time, there is consensus among authorities, industry, and academia on the need to secure VC systems. With specific proposals in the literature, a critical question must be answered: can secure VC systems be practical and satisfy the requirements of safety applications, in spite of the significant communication and processing overhead and other restrictions security and privacy-enhancing mechanisms impose? To answer this question, we investigate in this paper the following three dimensions for secure and privacy-enhancing VC schemes: the reliability of communication, the processing overhead at each node, and the impact on a safety application. The results indicate that with the appropriate system design, including sufficiently high processing power, applications enabled by secure VC can be in practice as effective as those enabled by unsecured VC.
💡 Deep Analysis
Deep Dive into Impact of Vehicular Communications Security on Transportation Safety.
Transportation safety, one of the main driving forces of the development of vehicular communication (VC) systems, relies on high-rate safety messaging (beaconing). At the same time, there is consensus among authorities, industry, and academia on the need to secure VC systems. With specific proposals in the literature, a critical question must be answered: can secure VC systems be practical and satisfy the requirements of safety applications, in spite of the significant communication and processing overhead and other restrictions security and privacy-enhancing mechanisms impose? To answer this question, we investigate in this paper the following three dimensions for secure and privacy-enhancing VC schemes: the reliability of communication, the processing overhead at each node, and the impact on a safety application. The results indicate that with the appropriate system design, including sufficiently high processing power, applications enabled by secure VC can be in practice as effective
📄 Full Content
arXiv:0808.2666v1 [cs.CR] 19 Aug 2008
Impact of Vehicular Communications Security on
Transportation Safety
Panos Papadimitratos∗, Giorgio Calandriello†, Jean-Pierre Hubaux∗and Antonio Lioy†
∗Laboratory for Computer Communications and Applications
EPFL, Switzerland
Email: {panos.papadimitratos, jean-pierre.hubaux}@epfl.ch
†Dipartimento di Automatica e Informatica
Politecnico di Torino, Italy
Email: {giorgio.calandriello, lioy}@polito.it
Abstract— Transportation safety, one of the main driving
forces of the development of vehicular communication (VC)
systems, relies on high-rate safety messaging (beaconing). At
the same time, there is consensus among authorities, industry,
and academia on the need to secure VC systems. With specific
proposals in the literature, a critical question must be answered:
can secure VC systems be practical and satisfy the requirements
of safety applications, in spite of the significant communication
and processing overhead and other restrictions security and
privacy-enhancing mechanisms impose? To answer this question,
we investigate in this paper the following three dimensions for
secure and privacy-enhancing VC schemes: the reliability of
communication, the processing overhead at each node, and the
impact on a safety application. The results indicate that with the
appropriate system design, including sufficiently high processing
power, applications enabled by secure VC can be in practice as
effective as those enabled by unsecured VC.
I. INTRODUCTION
Vehicular communication (VC) systems are developed as
a means to enhance transportation safety and efficiency. Ve-
hicles and road-side infrastructure units (RSUs) are equipped
with on-board sensors, computers, and wireless transceivers.
Vehicle-to-vehicle (V2V) and vehicle-to-infrastructure (V2I)
communication enable primarily safety applications. Many
research and development projects, including the Car-to-Car
Communication Consortium in Europe and the US Department
of Transportation VII initiative, converge towards a design
with vehicles frequently beaconing their position along with
warnings on their condition or the environment. Typical bea-
coning periods considered are in the order of one beacon per
100 milliseconds per vehicle.
At the same time, it has been understood that VC systems
are vulnerable to attacks and that the privacy of their users is
at stake. For example, an attacker could inject messages with
false information, or collect vehicle messages to track their
locations and infer sensitive user data. As a result, the research
community in industry and academia, with the endorsement
of authorities, has undertaken three major efforts to design
security and privacy enhancing solutions for VC: the NoW
project [8], the IEEE 1609.2 working group [9], and the
SeVeCom project [11].
A few basic ideas transcend all these efforts to develop VC
security architectures. They all build on top of a currently
well-understood vehicular communication protocol stack that
includes safety beaconing. Moreover, they all utilize a Certifi-
cation Authority (CA) and public key cryptography to protect
V2V and V2I messages. Their primary requirements are
message authentication, integrity, and non-repudiation, as well
as protection of private user information. To address those
apparently contradictory goals, they all rely on the concept of
pseudonymity or pseudonymous authentication [8], [9], [11]:
they require that (i) each vehicle (node) is equipped with
multiple certified public keys (pseudonyms) that do not reveal
the node identity, and (ii) the vehicle uses them alternately,
each for a short period of time, so that messages signed under
different pseudonyms cannot be linked.
It is becoming clear that the security overhead of such
systems will be significant; for example, each safety beacon
has to be signed, and each vehicle has to validate every 100
milliseconds beacons from several dozens of vehicles within
range. Which, not to forget, may essentially change their
identity (pseudonym) at any point in time, thus making it
harder for their neighboring vehicles to validate their signed
beacons.
The immediate question, for designers and users of vehic-
ular communication systems alike, arises: What is the effect
of security and notably these broadly accepted pseudonym-
based mechanisms on safety applications? In plain terms,
can, for example, vehicle collisions still be avoided when an
emergency braking situation arises?
There has been a timid approach to answer this question in
our earlier work [5], whose main contribution was the sim-
plification of key (pseudonym) management while satisfying
privacy and security requirements. But, in terms of evaluating
the impact of security on the VC system effectiveness, we
analyzed only a simple transportation scenario: the distance
at which a fast-approaching vehicle receives an emergency
braking signal from a vehicle ahead.
In this paper, we extend the work in [5] to investigate the
impact of security on trans
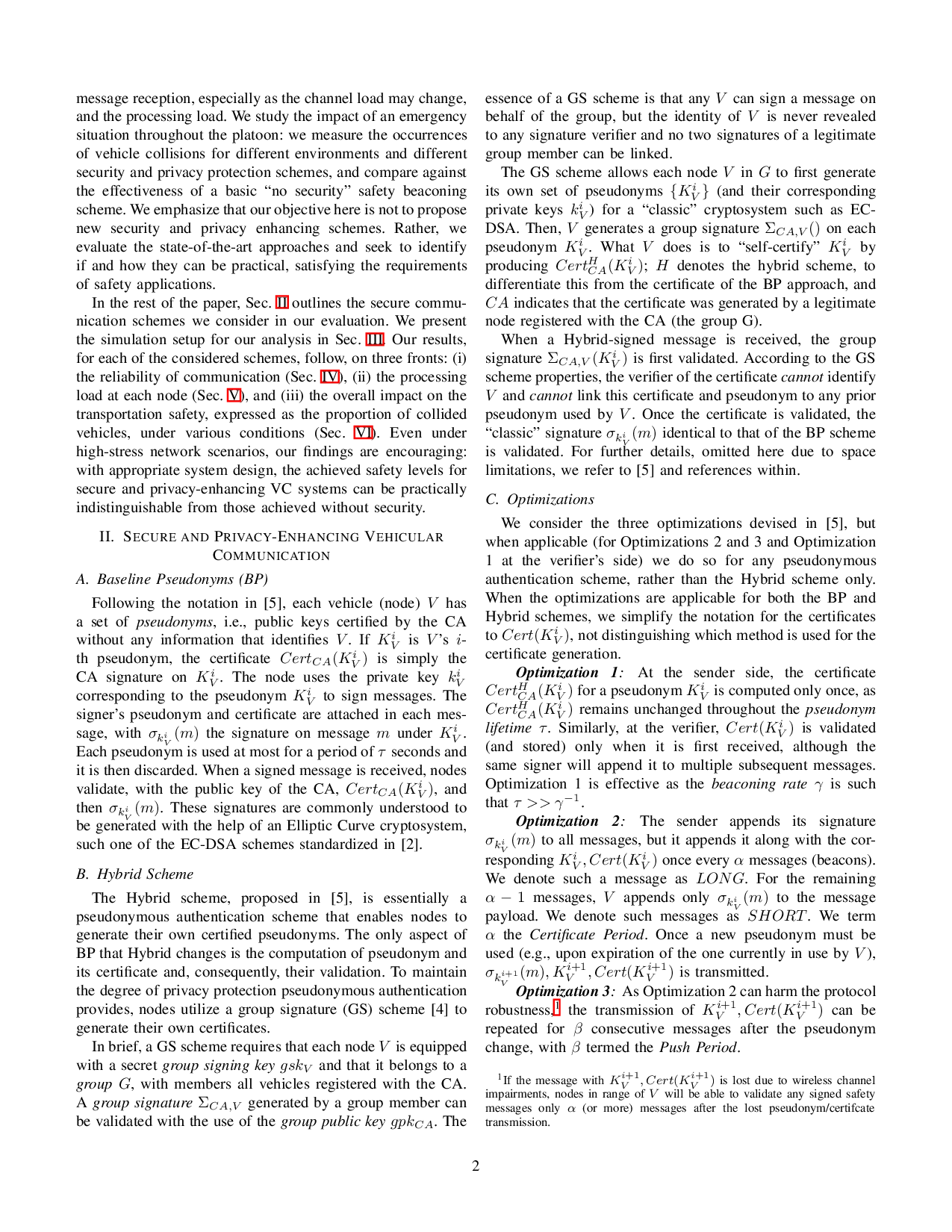
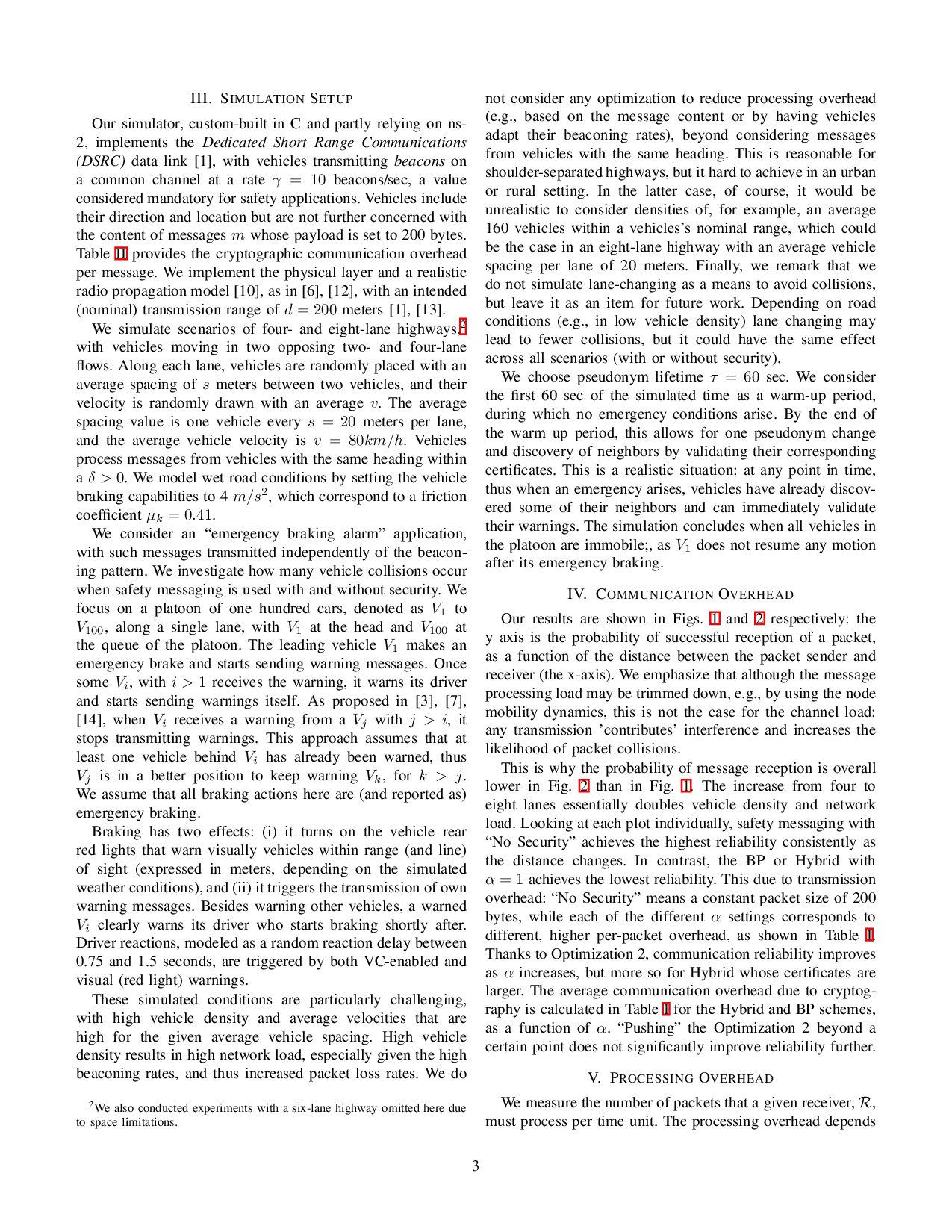
…(Full text truncated)…
📸 Image Gallery
Reference
This content is AI-processed based on ArXiv data.