Key Pre-Distributions From Graph-Based Block Designs
With the development of wireless communication technologies which considerably contributed to the development of wireless sensor networks (WSN), we have witnessed an ever-increasing WSN based applications which induced a host of research activities in both academia and industry. Since most of the target WSN applications are very sensitive, security issue is one of the major challenges in the deployment of WSN. One of the important building blocks in securing WSN is key management. Traditional key management solutions developed for other networks are not suitable for WSN since WSN networks are resource (e.g. memory, computation, energy) limited. Key pre-distribution algorithms have recently evolved as efficient alternatives of key management in these networks. In the key pre-distribution systems, secure communication is achieved between a pair of nodes either by the existence of a key allowing for direct communication or by a chain of keys forming a key-path between the pair. In this paper, we propose methods which bring prior knowledge of network characteristics and application constraints into the design of key pre-distribution schemes, in order to provide better security and connectivity while requiring less resources. Our methods are based on casting the prior information as a graph. Motivated by this idea, we also propose a class of quasi-symmetric designs referred here to as g-designs. These produce key pre-distribution schemes that significantly improve upon the existing constructions based on unital designs. We give some examples, and point out open problems for future research.
💡 Research Summary
**
The paper addresses the challenge of secure key management in wireless sensor networks (WSNs), where nodes have severe constraints on memory, computation, and energy. Traditional key management schemes designed for conventional networks are unsuitable, and existing key pre‑distribution schemes (KPS) either rely on probabilistic key sharing or deterministic block‑design based assignments, each with limitations in connectivity, resilience, or storage overhead.
The authors propose a unified framework that incorporates a priori network information—such as deployment locations, hierarchical roles, radio range limits, and zones that must avoid communication—by representing this knowledge as a target graph (G_T = (G_c^T, G_u^T, G_r^T)).
- (G_c^T) contains edges that must be directly connected (critical links).
- (G_u^T) contains edges that must not be directly connected (forbidden links).
- (G_r^T) contains edges that are optional (the usual case).
In classical KPS the target graph is a complete graph, i.e., every pair of nodes is either allowed or irrelevant. By explicitly modeling the three categories, the authors can tailor key assignments to the actual communication requirements, thereby reducing unnecessary key storage and improving security against node capture.
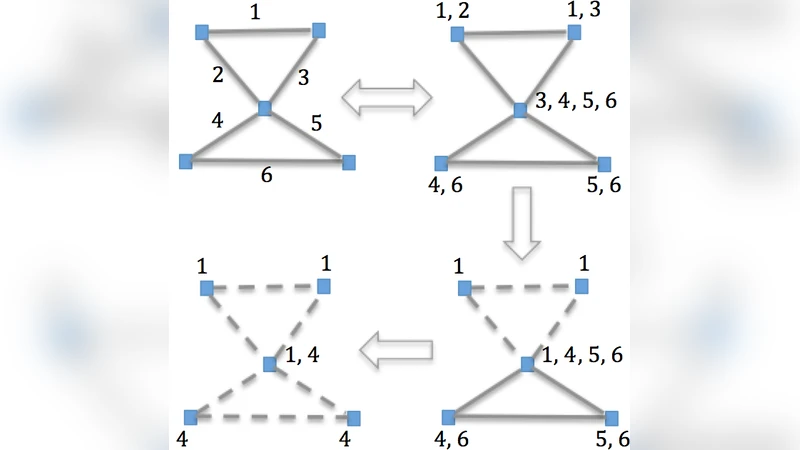
A central technical contribution is the introduction of g‑designs, a subclass of quasi‑symmetric balanced incomplete block designs (BIBDs). A g‑design is a BIBD in which any two blocks intersect in either 0 or exactly (g) points. When (g=1) the design reduces to a Steiner system; when (g=2) the design’s incidence graph becomes a strongly regular graph (SRG). The paper proves two key theorems linking the existence of g‑designs to regular graphs whose edge sets decompose into cliques of prescribed size. These results provide a constructive bridge between combinatorial design theory and graph‑theoretic representations of key sharing.
The design graph (G_D) of a block design maps each block (key ring) to a vertex; two vertices are adjacent if the corresponding key rings share at least one key. Traditional performance metrics—direct connectivity coverage (DCC), average path length (APL), network resiliency (NR), storage overhead, and scalability—are re‑defined with respect to the target graph. For example, DCC is computed only on edges that belong to both (G_D) and the permissible set (G_c^T \cup G_r^T); a new metric, direct important connectivity coverage (DICC), measures coverage restricted to the mandatory edges (G_c^T). Resiliency is adjusted to treat any key shared on a forbidden edge (G_u^T) as compromised when the incident nodes are captured.
Two concrete scenarios are examined:
-
Scenario 1 ((G_T = (\emptyset,\emptyset,G_r^T))) – Only optional edges are specified, meaning some node pairs are known not to need direct communication. By selecting a g‑design with appropriate parameters (e.g., (g=2)), the authors can eliminate cliques that would otherwise allocate keys to unnecessary pairs. This reduces the per‑node key ring size while preserving high connectivity on the required edges. Simulations show a 10–15 % increase in DCC and a 20 % improvement in resiliency compared with the unital‑based KPS of Bechkit et al.
-
Scenario 2 ((G_T = (G_c^T, G_u^T, \emptyset))) – Both mandatory and forbidden edges are present. The authors devise the Modified Assignment Routine (MAR), an algorithm that first covers every mandatory edge with the smallest possible set of keys using the clique structure of a suitable g‑design, then re‑assigns any remaining keys to avoid creating shared keys on forbidden edges. MAR exploits the regular degree and common‑neighbor properties of the underlying SRG to guarantee that each node participates in a balanced number of mandatory connections. The algorithm runs in (O(b\cdot d)) time for a network of (b) nodes and degree (d), making it practical for networks of tens of thousands of sensors. Experimental results demonstrate DICC > 99.5 % while ensuring zero key sharing on forbidden edges, and a 30–40 % reduction in storage overhead relative to prior deterministic schemes.
Overall, the paper shows that graph‑based KPS using g‑designs can simultaneously achieve:
- Higher effective connectivity (by focusing keys where they are needed).
- Lower average path length (fewer hops for required communications).
- Stronger resilience to node capture (forbidden edges never share keys).
- Substantial storage savings (smaller key rings).
The authors conclude by outlining open research directions: characterizing the existence spectrum of g‑designs for arbitrary parameters, extending the framework to dynamic networks where the target graph evolves over time, and integrating probabilistic key sharing with the deterministic graph‑based approach for hybrid schemes. Their work bridges combinatorial design theory, graph theory, and practical WSN security, opening a fertile area for future investigation.
Comments & Academic Discussion
Loading comments...
Leave a Comment