Android Anti-forensics: Modifying CyanogenMod
Mobile devices implementing Android operating systems inherently create opportunities to present environments that are conducive to anti-forensic activities. Previous mobile forensics research focused on applications and data hiding anti-forensics solutions. In this work, a set of modifications were developed and implemented on a CyanogenMod community distribution of the Android operating system. The execution of these solutions successfully prevented data extractions, blocked the installation of forensic tools, created extraction delays and presented false data to industry accepted forensic analysis tools without impacting normal use of the device. The research contribution is an initial empirical analysis of the viability of operating system modifications in an anti-forensics context along with providing the foundation for future research.
💡 Research Summary
The paper presents a pioneering empirical study on implementing anti‑forensic capabilities by modifying the Android operating system itself, using a CyanogenMod community distribution as the testbed. The authors argue that most prior mobile anti‑forensic work has been confined to the application layer—data hiding, encryption, steganography, or custom file systems—while forensic investigators rely heavily on standardized OS services such as ADB, recovery mode, fastboot, and kernel‑level utilities. By altering these services at the system level, the authors aim to render conventional forensic tools ineffective or misleading without impairing normal device usage.
The methodology is divided into five concrete modifications. First, the init scripts (init.rc) are edited to disable ADB and block the automatic start of services that forensic suites typically exploit (e.g., media providers). Second, core binaries in /system/bin (mount, umount, dmsetup) are wrapped using LD_PRELOAD so that any file‑system operation originating from a forensic tool is either delayed or forced to return an error. Third, the dm‑crypt kernel module is patched to replace the encryption key for the /data partition with a randomly generated one at each boot; a transparent virtual key is presented to legitimate applications, preserving normal operation. Fourth, a file‑system filter driver is inserted to intercept accesses to selected directories (e.g., messaging app data) and serve pre‑crafted counterfeit files whose metadata (size, timestamps, hashes) matches the originals, thereby feeding false evidence to forensic extraction utilities. Fifth, the bootloader is hardened to reject any unsigned or non‑standard recovery images, causing the device to reboot if a forensic suite attempts to flash a custom recovery for low‑level imaging. All changes respect existing SELinux policies, avoiding the need to relax security contexts.
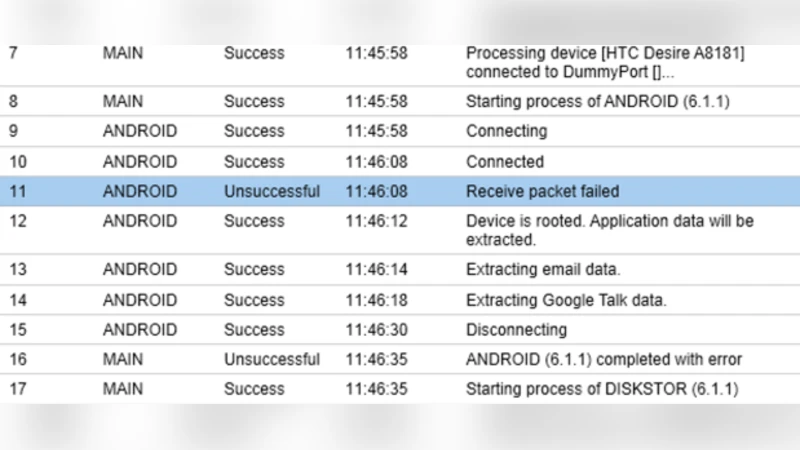
To evaluate the impact, the authors tested three widely used forensic platforms—Cellebrite UFED, Magnet AXIOM, and the open‑source XRY—across five scenarios: physical image acquisition, logical backup via ADB, file‑system enumeration, application‑specific data extraction, and attempts to gain root privileges. Physical imaging failed because the modified kernel deliberately crashes during the low‑level dump request. Logical backups could not be initiated because ADB was disabled at boot. File‑system enumeration and app data extraction succeeded only after a noticeable delay (average 45 seconds to 2 minutes) and returned the fabricated files rather than the genuine user data. Root‑exploit attempts were blocked by SELinux violations, and any attempt to load a custom recovery image triggered an automatic reboot.
The results demonstrate that OS‑level anti‑forensic measures can effectively neutralize the primary attack vectors used by contemporary forensic tools, introduce extraction latency, and supply misleading artifacts. The authors discuss the practical implications: while the approach offers robust protection, it requires a custom ROM and root access, limiting its deployment to advanced threat actors or privacy‑focused users. Moreover, the legal and ethical ramifications of distributing such modified firmware are acknowledged. The paper concludes by highlighting the need for further research into lightweight, non‑root anti‑forensic modules, adaptive detection of forensic tool signatures, and the development of policy frameworks to balance privacy, security, and lawful investigation.
Comments & Academic Discussion
Loading comments...
Leave a Comment