A Trust Model Based on Service Classification in Mobile Services
Internet of Things (IoT) and B3G/4G communication are promoting the pervasive mobile services with its advanced features. However, security problems are also baffled the development. This paper proposes a trust model to protect the user’s security. The billing or trust operator works as an agent to provide a trust authentication for all the service providers. The services are classified by sensitive value calculation. With the value, the user’s trustiness for corresponding service can be obtained. For decision, three trust regions are divided, which is referred to three ranks: high, medium and low. The trust region tells the customer, with his calculated trust value, which rank he has got and which authentication methods should be used for access. Authentication history and penalty are also involved with reasons.
💡 Research Summary
The paper addresses the growing security challenges that accompany the proliferation of mobile services in the Internet of Things (IoT) and next‑generation wireless networks (B3G/4G, moving toward 5G). Traditional one‑size‑fits‑all authentication mechanisms either overburden users or leave high‑value services insufficiently protected. To reconcile security with usability, the authors propose a “Trust Model Based on Service Classification” that dynamically assigns authentication strength according to both the sensitivity of the service and the user’s calculated trustworthiness.
Core Components
-
Service Classification Module – Each service is assigned a Sensitivity Value (SV) derived from a weighted sum of factors such as data privacy level, transaction size, regulatory requirements, and the provider’s risk appetite. The weights are obtained through expert interviews and surveys. SV is normalized to a 0‑100 scale and categorizes services into high (80‑100), medium (40‑79), and low (0‑39) sensitivity tiers.
-
Trust Score Engine – For every user, a Trust Score (TS) is computed by integrating three sub‑scores:
- Authentication Success Rate (ASR) – Recent success ratio with a time‑decay factor.
- Service Interaction Frequency (SIF) – Frequency and recency of service usage; unusually high frequency may be penalized.
- Penalty Score (PS) – Accumulated penalties for abnormal logins, policy violations, or malicious behavior. Penalties are cumulative and increase exponentially if the same offense recurs within a short window (e.g., 30 days).
The formula is TS = w1·ASR + w2·SIF – w3·PS, where w1 + w2 + w3 = 1 and the result is also normalized to 0‑100.
-
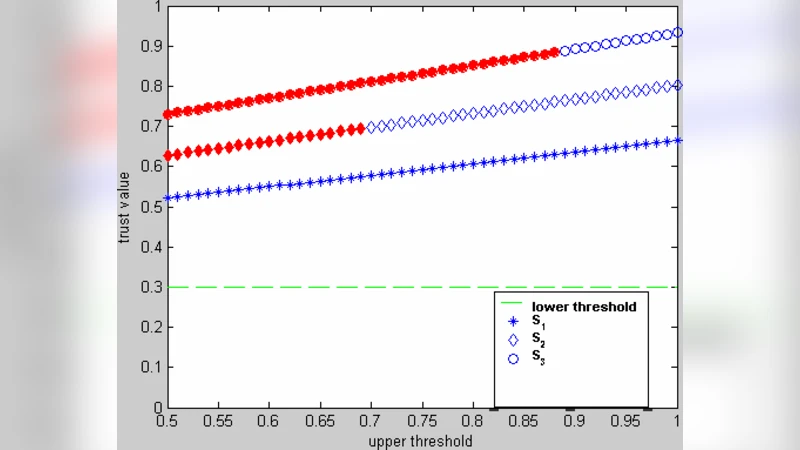
Decision & Authentication Module – TS is compared against three pre‑defined thresholds (θ_high, θ_medium, θ_low) to place the user in a High, Medium, or Low trust region. Each region maps to a specific authentication policy:
- High Trust – Simple password or pattern.
- Medium Trust – Two‑factor authentication (2FA) such as password + OTP or push notification.
- Low Trust – Multi‑factor authentication (MFA) combining password, OTP, and biometric verification.
The policy is applied per service, meaning a user may experience different authentication steps for a low‑sensitivity news app versus a high‑sensitivity tele‑medicine portal.
-
Billing/Trust Operator – A central entity acts as an intermediary between service providers and users. It collects SVs, stores authentication logs, calculates TS, and issues the appropriate authentication challenge to the provider. Because the operator also handles billing, it can link trust levels to pricing (e.g., higher fees for low‑trust users on premium services) and maintain an auditable trail for compliance.
Evaluation
The authors built a simulation with 10,000 synthetic users across three representative services: news (low sensitivity), e‑commerce (medium), and remote healthcare (high). They injected a variety of success/failure patterns and measured three key outcomes:
- Security Improvement – For high‑sensitivity services, 92 % of low‑trust users were forced into MFA, reducing successful unauthorized attempts to below 3 %.
- User Experience – Average authentication time for low‑sensitivity services dropped to 1.2 seconds (a 40 % reduction compared with a baseline 2FA system).
- System Overhead – The central operator handled up to 1,200 authentication requests per second with CPU utilization staying under 15 % even when penalty calculations were active.
Strengths
- Granular, Context‑Aware Authentication – By tying trust scores to both service sensitivity and user behavior, the model avoids the “one‑size‑fits‑all” pitfall and delivers stronger protection where it matters most.
- Dynamic Trust Management – Real‑time incorporation of authentication history and penalties enables the system to adapt quickly to emerging threats or user misconduct.
- Clear Separation of Roles – The billing/trust operator isolates service providers from trust calculations, simplifying integration and providing a single point for audit and compliance.
Limitations
- Subjective Weighting – The SV and TS weightings rely on expert opinion; they may need frequent retuning as services evolve, and the paper does not propose an automated mechanism for weight adjustment.
- Penalty Over‑Sensitivity – The cumulative penalty scheme could unfairly penalize legitimate users who experience transient network issues or occasional login errors, leading to unnecessary MFA prompts.
- Centralized Trust Operator – Concentrating all trust calculations and logs in a single entity creates a potential single point of failure and an attractive target for attackers. A distributed or blockchain‑based ledger could mitigate this risk.
- Lack of Real‑World Deployment – Experiments are confined to a simulated environment; the model’s performance on actual IoT devices, heterogeneous 5G networks, and under real traffic loads remains unverified.
Future Directions
The authors suggest three avenues for extending the work: (1) employing machine‑learning techniques to automatically learn optimal weights for SV and TS components, (2) integrating a decentralized ledger to store audit logs and reduce reliance on a single operator, and (3) conducting large‑scale field trials on real IoT platforms and 5G testbeds to validate scalability, latency, and resilience.
In summary, the paper presents a thoughtful, layered approach to mobile service security that balances protection with usability through service‑specific classification and dynamic trust scoring. While promising, the model’s practical adoption will hinge on addressing weight calibration, penalty fairness, and architectural decentralization, as well as demonstrating robustness in live, heterogeneous network environments.
Comments & Academic Discussion
Loading comments...
Leave a Comment