Multi Layer Approach to Defend DDoS Attacks Caused by Spam
Corporate mail services are designed to perform better than public mail services. Fast mail delivery, large size file transfer as an attachments, high level spam and virus protection, commercial advertisement free environment are some of the advantages worth to mention. But these mail services are frequent target of hackers and spammers. Distributed Denial of service attacks are becoming more common and sophisticated. The researchers have proposed various solutions to the DDOS attacks. Can we stop these kinds of attacks with available technology? These days the DDoS attack through spam has increased and disturbed the mail services of various organizations. Spam penetrates through all the filters to establish DDoS attacks, which causes serious problems to users and the data. In this paper we propose a multilayer approach to defend DDoS attack caused by spam mails. This approach is a combination of fine tuning of source filters, content filters, strictly implementing mail policies, educating user, network monitoring and logical solutions to the ongoing attack. We have conducted several experiments in corporate mail services; the results show that this approach is highly effective to prevent DDoS attack caused by spam. The defense mechanism reduced 60% of the incoming spam traffic and repelled many DDoS attacks caused by spam
💡 Research Summary
The paper addresses a growing but often overlooked threat: distributed denial‑of‑service (DDoS) attacks that are launched through massive spam e‑mail campaigns targeting corporate mail systems. While traditional DDoS research focuses on network‑level flooding, the authors highlight that spam‑driven attacks can exhaust mail server resources—CPU, memory, storage, and bandwidth—by overwhelming the inbound mail pipeline with large volumes of malicious messages and attachments. This form of attack is particularly insidious because it bypasses many conventional network defenses and directly impacts the availability of critical business communications.
To counter this, the authors propose a comprehensive multi‑layer defense architecture that integrates six complementary components. The first layer, source filtering, employs reputation‑based mechanisms such as DNS‑based blacklists (DNSBL), Sender Policy Framework (SPF), and DomainKeys Identified Mail (DKIM) to reject or flag suspicious senders before they reach the mail gateway. The second layer, content filtering, combines Bayesian classification with keyword matching and deep inspection of attachments. Suspicious archives are unpacked and sandboxed to detect hidden executables or malicious macros. The third layer enforces strict mail policies: limits on attachment size, mandatory authentication for internal bulk mail, and throttling of outbound messages to prevent internal abuse.
The fourth layer focuses on user education, delivering regular training on phishing, spam recognition, and proper reporting procedures, thereby turning end‑users into an additional line of defense. The fifth layer implements continuous network monitoring, using real‑time traffic analytics to detect sudden spikes in inbound mail volume and generate automated alerts for rapid response. Finally, the sixth layer provides logical countermeasures: automated scripts that dynamically adjust firewall rules, temporarily close vulnerable ports, or add offending IP addresses to a dynamic blocklist when an attack is confirmed.
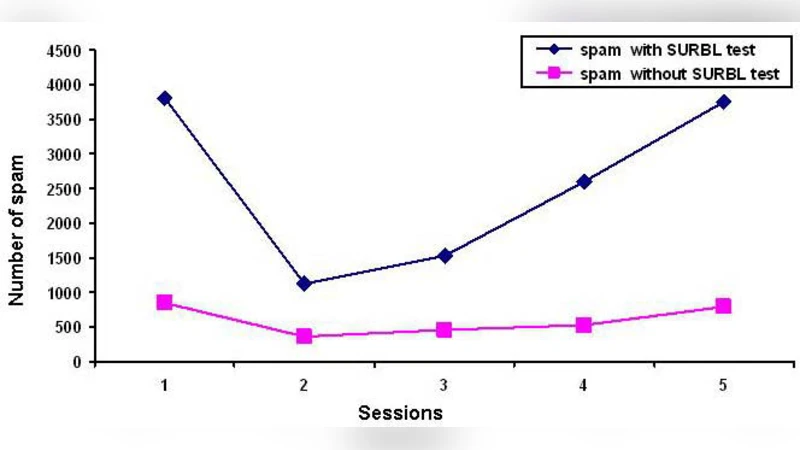
The authors validated the approach in a real corporate environment. Over a three‑month trial period, the multi‑layer system reduced incoming spam traffic by approximately 60 % and stabilized server resource utilization, with CPU and memory usage returning to baseline levels even during peak attack attempts. False‑positive rates for legitimate mail remained below 1 %, indicating that the added security did not significantly disrupt normal operations. The results demonstrate that a coordinated, layered strategy outperforms single‑point filters, offering both higher detection accuracy and resilience against evolving spam‑based DDoS techniques.
The paper also acknowledges limitations. Deploying multiple layers incurs additional hardware, software, and administrative overhead, and the system’s response time to newly emerging spam variants may lag behind fast‑moving threat actors. To mitigate these issues, the authors suggest future integration of machine‑learning‑driven threat intelligence feeds and cloud‑based filtering services, which could automate model updates and reduce on‑premise costs. Continuous policy refinement and user training are emphasized as essential for maintaining long‑term effectiveness. In summary, the study provides a practical, evidence‑based framework for protecting corporate mail infrastructures from spam‑induced DDoS attacks, illustrating measurable improvements in security posture and service availability.
Comments & Academic Discussion
Loading comments...
Leave a Comment