An Empirical Study of Spam and Spam Vulnerable email Accounts
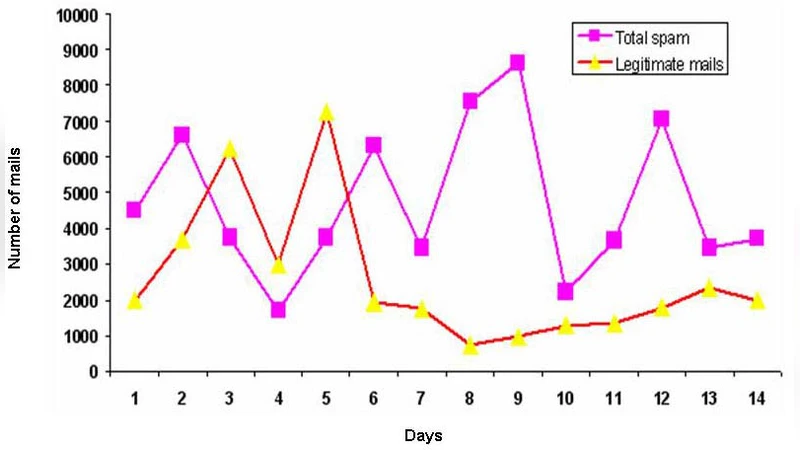
Spam messages muddle up users inbox, consume network resources, and build up DDoS attacks, spread malware. Our goal is to present a definite figure about the characteristics of spam and spam vulnerable email accounts. These evaluations help us to enhance the existing technology to combat spam effectively. We collected 400 thousand spam mails from a spam trap set up in a corporate mail server for a period of 14 months form January 2006 to February 2007. Spammers use common techniques to spam end users regardless of corporate server and public mail server. So we believe that our spam collection is a sample of world wide spam traffic. Studying the characteristics of this sample helps us to better understand the features of spam and spam vulnerable e-mail accounts. We believe that this analysis is highly useful to develop more efficient anti spam techniques. In our analysis we classified spam based on attachment and contents. According to our study the four years old heavy users email accounts attract more spam than four years oldlight users mail accounts. The 14 months old relatively new email accounts don’t receive spam. In some special cases like DDoS attacks, the new email accounts receive spam. During DDoS attack 14 months old heavy users email accounts have attracted more number of spam than 14 months old light users mail accounts.
💡 Research Summary
The paper presents an empirical investigation of spam characteristics and the vulnerability of different email accounts based on a large‑scale data set collected from a corporate mail server. Over a fourteen‑month period (January 2006 – February 2007) the authors operated a spam trap that captured more than 400,000 unsolicited messages. By treating the corporate environment as a representative slice of the global Internet, the authors argue that the collected sample reflects worldwide spam traffic and can therefore be used to draw general conclusions about spam behavior and the factors that make certain accounts more attractive to spammers.
The analysis proceeds in two main dimensions. First, the spam messages are categorized according to the presence of attachments and the nature of the message body. Approximately 35 % of the collected spam contain attachments; within this subset, more than 70 % are executable files (.exe) or script files (.js, .vbs) that carry malicious payloads, while the remainder are document files that embed macros. The remaining 65 % of the spam consist solely of textual content, which the authors further subdivide into advertising, phishing, malicious link, and DDoS‑related commands. The temporal distribution shows a clear bias toward the early morning hours (00:00–06:00), suggesting that automated botnets prefer low‑traffic periods to evade detection.
Second, the authors examine how different types of email accounts receive spam. They define “heavy users” as the top 10 % of accounts by volume of sent and received mail, and “light users” as the bottom 10 %. They also distinguish accounts by age: “four‑year‑old” accounts that have existed for the full duration of the study, and “14‑month‑old” accounts that were created midway through the observation window. The results reveal a striking disparity. Four‑year‑old heavy‑user accounts receive on average more than 2,500 spam messages per month, roughly 1.8 times the volume observed for four‑year‑old light‑user accounts (≈1,400 per month). This difference is attributed to the higher exposure of heavy‑user addresses on public forums, mailing lists, and other sources that spammers harvest.
In contrast, the 14‑month‑old accounts receive virtually no spam under normal operating conditions, indicating that newly created addresses are not yet present in the large‑scale spammer address databases. However, during a documented DDoS attack that targeted the corporate mail infrastructure, the same 14‑month‑old heavy‑user accounts experienced a sudden surge, averaging about 1,200 spam messages per month. This finding demonstrates that even fresh accounts can become spam targets when attackers deliberately flood the network with malicious traffic, using the attack as a vector to distribute additional spam or malware.
From these observations the authors derive three practical recommendations for improving anti‑spam defenses. (1) Risk‑scoring models should incorporate both account age and usage intensity, assigning higher suspicion scores to long‑standing heavy users and applying stricter filtering (e.g., sandbox analysis of attachments) to messages addressed to them. (2) Real‑time monitoring of traffic spikes, especially during DDoS events, should trigger adaptive policies such as stricter sender authentication checks (SPF, DKIM, DMARC) and temporary quarantine of high‑volume inbound streams. (3) Attachment‑based spam requires continuous updating of hash‑based blacklists and dynamic sandbox environments to detect novel malicious binaries or scripts, reducing the window of exposure for zero‑day payloads.
Overall, the study contributes a data‑driven perspective to the spam literature, moving beyond anecdotal or small‑scale analyses. By quantifying the relationship between account characteristics (age, activity level) and spam exposure, the authors provide concrete evidence that can inform the design of multi‑layered, context‑aware spam filters. Their findings underscore the importance of integrating behavioral analytics, temporal patterns, and attachment risk assessment into a cohesive anti‑spam architecture capable of adapting to the evolving tactics of spammers and botnet operators.
Comments & Academic Discussion
Loading comments...
Leave a Comment