Network Coding for Speedup in Switches
We present a graph theoretic upper bound on speedup needed to achieve 100% throughput in a multicast switch using network coding. By bounding speedup, we show the equivalence between network coding and speedup in multicast switches - i.e. network cod…
Authors: MinJi Kim, Jay Kumar Sundararajan, Muriel Medard
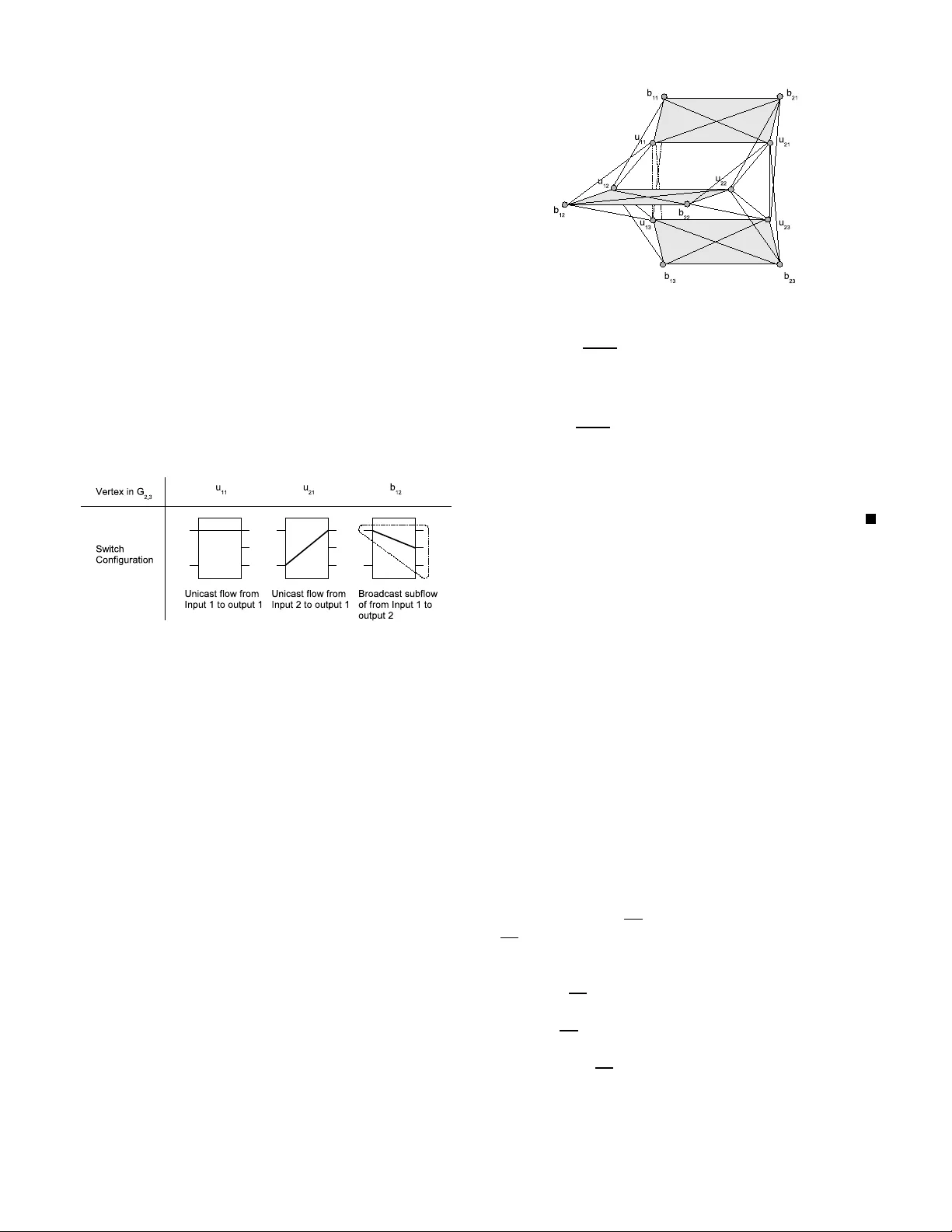
Netw ork Coding for Speedup in Switches MinJi Kim, Jay Kumar Sundararajan, and Muriel M ´ edard Laborato ry for Inform ation and Decision Systems Massachusetts In stitute of T echnology Cambridge, MA 0213 9, USA Email: { minjikim, jay kumar, medard } @mit.edu Abstract — W e present a graph theoretic upper bound on speedup needed to achieve 100 % throughput in a multicast switch using network coding. By bounding speedup, we show the equivalence between network co ding and speed up i n multicast switches - i.e . network coding, which is usually implemented using software, can in many cases sub stitute speedup, which is often achiev ed by adding extra switch fabrics. T his b ound is based on an app roach to n etwork coding problems called the “enhan ced conflict graph”. W e show that the “imperfection ra tio” of the enhanced conflict graph gives an up per boun d on speedup. In particular , we apply th is result to K × N switches with traffic patterns consistin g of unicasts and broadcasts only t o obtain an upper boun d of min( 2 K − 1 K , 2 N N +1 ) . I . I N T RO D U C T I O N The input-queu ed crossbar switch has been studied well, especially in the context o f un icast traffic. It is k nown th at 100% thro ughpu t can be achieved [1], in the sense that as long as no inp ut or output is oversubscribed, traffic can b e supported without c ausing the queu es to grow unb ounde dly . Therefo re, to serve any adm issible u nicast traffic, th e inpu t- queued cro ssbar switch do es not need to proc ess packets faster than the inp ut line rate 1 , i.e. the switch doe s not n eed speedu p . The extension of the p roblem to mu lticast flows, howe ver , is in trinsically more d ifficult. Marsan et al. [5] gave a chara c- terization of the rate r egion achiev ab le in a multicast switch with fano ut splitting 2 , an d also defined the op timal schedulin g policy . Interestingly , this work p roved that unlike in the unicast case, 100 % th rough put cannot be achieved fo r mu lticast flows in an input-q ueued switch. In fact, the minimum speedup needed to achieve 100 % throug hput g rows u nboun dedly with the switch size. In this pape r , we discuss the same prob lem as [5], with the following mod ification. T he inp uts are allowed to send linear combina tions of cells waiting in th e qu eues, i.e. , th ey are allowed to per form lin ear ne twork codin g [9] with fanout splitting. The m ain co ntributions of this paper are: 1) W e sh ow tha t network cod ing can in many c ases substi- tute speedup . 2) W e provid e a simple graph -theoretic u pper b ound o n speedup. 1 The line rate of a switch is the rate at which packets arri ve or leave the switch at any one port. 2 Fanout splitting is the ability to serve partially a multicast cell to only a subset of its destined outputs, and complete the service in subsequent time slots. 3) W e prove an upper bound on speed up of min 2 K − 1 K , 2 N N +1 for an arb itrary K × N switch with traffic pattern restricted to unicasts and bro adcasts only . Our work builds on the work by Sunda rarajan et al. [2], [ 3], which gave a graph -theoretic for mulation o f the rate region of a mu lticast switch with intr a-flow co ding using enha nced conflict graphs . Giv en a traffic pattern, the en hanced co nflict graph G = ( V , E ) is an und irected graph that co ntains o ne vertex for ev ery subflo w . 3 An ed ge exists between two vertices if they repre sent two su bflows f rom the same input or to the same output. Refe rence [3] shows that the stable set polytop e and th e fraction al stable set p olytope of an enhan ced conflict g raph are the rate r egion and the adm issible region of a network co ding switch, respectively . This grap h-theor etic formu lation helps u s tra nsform any given traffic pattern into a conflict g raph, and the pr operties of this grap h can be used to derive insigh t o n the speedup requ ired to achieve 100 % throug hput with coding . A similar gr aph-the oretic formu lation was used b y Caramanis et al. in [4] in the c ontext of unic ast traffic in Banyan networks. Note th at, for the case of fanou t splitting withou t codin g, [5] gave a ch aracterization of th e rate region as the conve x hull o f cer tain modified departu re vectors. Howev er , a graph - theoretic form ulation o f th e same is not known. As a r esult, it is sign ificantly harder to c haracterize th e speedup required to achieve 100 % thro ughpu t for fanout splitting withou t cod ing. The r est of th e paper is o rganized a s fo llows. Section I I states p reliminary definition s that will b e used thr ough out th is paper . Section III shows that network co ding is eq uiv alen t to speedup in a mu lticast switch to some extent. Section IV gives the relatio nship between speedup and imp erfection ratio of a conflict graph , which leads to our main result - an upper boun d on the minimum speedup required to achie ve 1 00% throug hput in a m ulticast switch with cod ing. In Section V, we app ly the resu lt fr om Section IV to a K × N switch with traffic consisting only of un icasts and bro adcasts and give an upper bound on speedup of min( 2 K − 1 K , 2 N N +1 ) . Finally , in Section VI, we summarize the co ntributions of this paper, a nd presen t a conjecture on the actual minimum sp eedup n eeded to achieve 3 A flow is a stream of pack ets that hav e common source and destinat ion set. It is represente d by a 2-tuple ( i, J ) consisting of the input i and a subset J of outputs corresponding to the destination set of the multicast s tream. A subflo w of flow ( i, J ) is a part of a flow from input i that goes to a parti cular output in J . Therefore, a subflow is a 3-tuple ( i, J, j ) consist ing of an input i , a subset of outputs J and one output j ∈ J . 100% throu ghput in a 2 × N m ulticast switch with unicasts and broadca sts on ly . I I . N OTA T I O N A N D D E FI N I T I O N S Let G = ( V , E ) b e an un directed g raph with vertex set V and edge set E . A gr aph G 1 = ( V 1 , E 1 ) is a subgrap h of G if V 1 ⊆ V and E 1 ⊆ E . A graph G 2 = ( V 2 , E 2 ) is an induced subgraph of G if V 2 ⊆ V and ( v 1 , v 2 ) ∈ E 2 if and only if ( v 1 , v 2 ) ∈ E . In addition, G 2 is often d enoted as G ( V 2 ) an d is said to b e induced by V 2 . Th e complement of g raph G is a gra ph G on the same vertex set V such that two vertices of G are adjacent if and only if they are not adjac ent in G . The chr oma tic number of a graph G is the smallest n umber of color s χ ( G ) needed to color the vertices of G so that n o two ad jacent vertices sha re the sam e color . G is a complete graph if for e very pair of vertices in V there exists an edge co nnecting th e two, and V is called a clique . If f or every pair of vertices in V there is no edge conne cting the two, then V is said to be a stab le set . G is a ho le if it is a chord less cycle; G is ca lled an odd hole if it is a h ole o f odd length at least 5. G is an an ti-hole if its complem ent is a hole; G is an o dd an ti-hole if its com plement is an odd hole. G is said to be p erfect if fo r every ind uced subg raph o f G , the size of th e largest clique equals th e chromatic n umber . A. Stab le Set P olytope The stable set po lytope S T AB ( G ) of a grap h G is th e conv ex hull of the incid ence vectors o f the stable sets of the graph G . In this section, we d iscuss how the stable set p olytope of a co nflict graph can tra nslate to the r ate region of a switch. Let r ∈ R f be th e rate vector o f a traffic pattern that has f flows. Suppo se th at the total nu mber of subflows in the pattern is m . The n, the enhan ced rate vecto r e ( r ) ∈ R m correspo nding to r is defined as: e ( i,J,j ) ( r ) = r ( i,J ) , for all j ∈ J. W e use th e enhan ced rate vecto r as weigh ts for vertices of the enhanced conflict graph. A traffic pattern r is said to be achievable if ther e exists a switch schedu le that can serve it; it is called admissible if no input or ou tput is oversubscrib ed. W e also call th e collection of all ach iev ab le a nd ad missible vector s as the achievable rate r egion R ⊆ R f and admissible rate re gion A ⊆ R f respectively . For r ∈ R , we can constru ct a switch schedule, which can b e viewed as a time shar ing between valid switch config urations. In a con flict graph , a valid switch configur ation corr esponds to a stable set, and a switch schedu le correspo nds to a conve x combina tion of stable sets of the conflict gr aph G . Th erefore, if a rate vector r ∈ R , then e ( r ) ∈ S T AB ( G ) ⊆ R m . For a gen eral graph G , a complete character ization of S T AB ( G ) in terms of lin ear inequalities is unknown. How- ev er , several families of necessary condition s are known. One example is th e cliqu e inequ alities 4 . Th e p olytope describ ed b y 4 Clique inequalit ies of a graph say that the total weight on the verti ces of maximal cliques must not exceed 1. In an enhanced conflict graph, the clique inequal ities imply that no input nor any output may be overloa ded. these con ditions along with non-negativity co nstraints 5 is the fractional stable set polytope QS T AB ( G ) . In terms of th e switch, [3] shows that th e cliqu e ineq ualities of the enhan ced conflict grap h corr espond to the admissibility conditio ns . Therefo re, if a rate vector r ∈ A , th en e ( r ) ∈ QS T AB ( G ) ⊆ R m . Note that, f or most gra phs, S T AB ( G ) ( QS T AB ( G ) , since the clique in equalities ar e n ecessary but not sufficient condition s for stable set poly tope. Thu s, the admissible region is of ten a strict superset of the achiev able rate r egion, which implies that it is no t possible to achieve 100% throughpu t e ven with fanou t splitting and codin g - we need speedup. B. P erfect Graph In this section, we focu s o n the properties of perfec t graphs. W e fir st start by stating th ree well-k nown facts that characterize perfect gr aphs. Theor em 2. 1: (W eak P erfect Graph Theorem [7]) A g raph G is perfect if and on ly if its comp lement is perfect. Theor em 2. 2: (Str on g P erfect Graph Theorem [8]) A graph G is perfect if and only if it con tains no odd h ole a nd no odd anti-ho le. Lemma 2 .3: (Replica tion Lemma [7]) Let G = ( V , E ) be a perfect graph a nd v ∈ V . Cr eate a new vertex v ′ and join it to v and to a ll the neighbors of v . Then , the r esulting graph G ′ is perfect. From Section II- A, we have th at S T AB ( G ) ⊆ Q S T AB ( G ) for any g raph with equ ality fo r perfect graph s only . This implies that the admissible region A an d the a chiev ab le rate region R are the same if the enhanced conflict g raph is perfect. Thus, as given in Cor ollary 1 from [3], if an e nhanced conflict graph is per fect, then speedu p is not requ ired to achieve 100% throug hput. From this, we can ob serve that th ere is an intr insic conne c- tion between speed up and the “perfectn ess” of the enhance d conflict gra ph. As a r esult, to com pute the minimum speed up, it is helpf ul to measure how perfect an enhanced conflict grap h is. In this pap er , we use the imperfection ratio introd uced by Gerke and McDiarm id [6] as such a measure. C. Imperfection ratio In [6], the imperfe ction ratio imp ( G ) of graph G is define d as imp ( G ) = min { t : Q S T AB ( G ) ⊆ t S T AB ( G ) } . As we noted in Section II-A, in terms of a switch, th e a dmissible region A and the achievable region R are pro jections o f QS T AB ( G ) and S T AB ( G ) respectively . Th erefore, given the imperfection ratio imp ( G ) of an enh anced conflict graph G , we hav e A ⊆ imp ( G ) R . A usefu l boun d on the imper fection ratio is presented in [6 ], which we reprod uce b elow . Pr opo sition 2.4: (Gerke and McDiarmid [6]) F or a graph G , if ea ch vertex in G can be cover ed p times b y a family of q induced perfect sub graphs, then imp ( G ) ≤ q p . 5 Non-ne gati vity constrai nts of a graph say that the weight on each vert ex is non-ne gati ve. D. Speed up A switch is said to have a spee dup s if the switching fabric can tran sfer p ackets at a r ate s time s the incoming and outgoin g line rate of the switch. If we define a time slot to be the reciprocal of the line rate, then this means the switching fabric can go throug h s con figurations within one tim e slot. W ith this definition , it is easy to see that a r ate vector r is achiev a ble with speedu p s if and on ly if it is a dmissible and 1 s r is within the r ate region . Note that the adm issible and achiev able rates corr espond to A and R r espectiv ely . Th en, s min = min { s | A ⊆ s R } is the minimu m speed up required fo r the switch to ach iev e all admissible ra tes, i.e. it is the minimum of all s such that 1 s r is with in the r ate region for all admissible rate vecto rs r . I I I . N E T W O R K C O D I N G F O R S P E E D U P In this sectio n, we show the e quiv ale nce between network coding and speed up in mu lticast switches - i.e . network codin g, which is usually im plemented using software, can in m any cases substitute spee dup, wh ich is often achieved by addin g extra switch fabrics. In Fig ure 1, we show a special tr affic pattern in a 2 × N switch, wh ich de monstrates the b enefit of intr a-flow coding. At input 1, there is o ne broadca st flo w w ith rate 1 − 1 N ; at input 2, th ere is on e un icast to each output with rate 1 N . Reference [3] shows that this traffic is achiev able if network coding with fanout sp litting is allowed; h owe ver, a sp eedup of 1 . 5 − 1 N is need ed if on ly fanout splittin g is allowed. This example shows that network codin g is equ i valent to a speedu p of at least 1 . 5 − 1 N . Fig. 1. A traf fic pattern which demonstrates the benefit of coding Howe ver, it is importan t to note that network co ding canno t completely re place speedup . As no ted above in Figure 1, there are situation s wh ere network coding red uces spee dup; howe ver, there are situatio ns wher e speed up need ed remains the same for with and without n etwork coding . For in stance, in Figu re 2, we show a traffic patter n that r equires speedup of 1.2 5 with or witho ut network c oding. At input 1 , there is a broadc ast flow and a unicast to ou tput 1 with rate 1 2 each; at input 2, ther e is one unic ast flow to each outp ut 2 and 3 with rate 1 2 . In Figure 2, we show that the enh anced co nflict gr aph for this traffic, wh ere u ij represents th e unicast flow f rom input i to o utput j , and the vertex b ij represents the br oadcast subflow from inp ut i to outp ut j . The enhanc ed conflict gra ph contains an o dd hole; th erefore, it is no t perf ect. Note that the traffic pattern in Figu re 2 giv es a lower bound o n the speedup n eeded to achieve 100% th rough put in Fig. 2. A traffic patte rn which requires speedup in a 2 × 3 switch and its enhanc ed conflict graph a multicast switch using network cod ing. Th erefore, s min ≥ 1 . 25 . I V . I M P E R F E C T I O N R A T I O B O U N D S S P E E D U P This section de velop s o ur main result, w hich relates speedup with imp erfection ratio. Note th at, the definition of imperfec- tion ra tio in Section II-C is very similar to that o f minimum speedup in Section II-D. As a result, Corollary 4.1 follows from Pro position 2 .4. Cor ollary 4.1 : Give n a tr a ffic pattern, let G be its enhanced conflict graph and s min be the minimum speed up r eq uir ed to achieve a ll a dmissible rates. Th en, s min ≤ imp ( G ) . Note that the conv erse of Corollary 4.1 is not true. This is be cause A and R are pro jections of QS T AB ( G ) and S T AB ( G ) such that the s ubflows correspond ing to the same multicast flo w h av e the same weight. As a re- sult, QS T AB ( G ) ⊆ imp ( G ) S T AB ( G ) implies the A ⊆ imp ( G ) R , but A ⊆ s min R may not imply QS T AB ( G ) ⊆ s min S T AB ( G ) . V . B O U N D S O N S P E E D U P F O R K × N S W I T C H W I T H U N I C A S T S A N D B RO A D C A S T S In th is section, we apply Coro llary 4.1 to K × N switches using intra-flow coding with tra ffic p atterns consisting of unicasts an d b roadcasts only . W e show th at the minim um speedup needed f or 1 00% th rough put in this case is bou nded by min( 2 K − 1 K , 2 N N +1 ) . In this section, coding imp lies intra- flow co ding, since en hanced con flict graphs h andle intra-flow , not inter-flow , co ding. The re st o f this section is organiz ed as follows. First, we give a descrip tion of the enh anced conflict graph for a K × N switch. In Section V -B a nd V -C, we show the two bou nds on speedu p of 2 K − 1 K and 2 N N +1 respectively . A. Enh anced confl ict graph for K × N switch Consider traffic pa tterns which consist only o f u nicasts and a broad cast per each inpu t o n a K × N switch . Th e ba sic id ea behind con flict grap h is that vertices re presenting flows that cannot be served simu ltaneously are adjacent. In such a case, the en hanced conflict grap h G K,N = ( V , E ) h as the following structure. The vertex set V = ∪ i ∈ [1 ,K ] U i ∪ ∪ i ∈ [1 ,K ] B i = ∪ j ∈ [1 ,N ] U o j ∪ ∪ j ∈ [1 ,N ] B o j where U i = { u ij | j ∈ [1 , N ] } 6 , B i = { b ij | j ∈ [1 , N ] } , U o j = { u ij | i ∈ [1 , K ] } , and B o j = { b ij | i ∈ [1 , K ] } . The vertex u ij represents the unicast flow fr om inpu t i to o utput j , and the vertex b ij represents the broadca st subflow f rom inpu t i to outp ut j . Theref ore, 6 j ∈ [1 , N ] means j can be inte ger from 1 to N . U i and U o j are collection s o f the unicast flows fro m inp ut i and to outpu t j respe cti vely . B i and B o j are collectio ns of the sub flows of th e bro adcast from in put i and to outp ut j respectively . The edge set E = ∪ i ∈ [1 ,K ] E u i ∪ ∪ i ∈ [1 ,K ] E b i ∪ E o where E u i = { ( u ij , u ik ) | j 6 = k , j, k ∈ [1 , N ] } , E b i = { ( b ij , u ik ) | j, k ∈ [1 , N ] } , and E o = ∪ i ∈ [1 ,N ] E o i where E o i = { ( u j i , u ki ) , ( b j i , b ki ) , ( b j i , u ki ) | j 6 = k , j, k ∈ [1 , K ] } . Each edge set represents a different type of co nflict. E u i represents conflicts among unicasts at input i ; E b i represents conflict betwee n a ny broad cast subflow and any u nicast at input i ; and E o i represents con flicts amon g all flows and subflows a t o utput i . It is impo rtant to note that each vertex in G K,N represents a subflow in a K × N switch. For example, u 11 and u 21 correspo nds to a u nicast traffic to o utput 1 fro m inpu t 1 and input 2 respectively . The vertex b 12 represents a partial service of the bro adcast from input 1 to output 2. In Figure 3, we show the switch configu ration corre sponding to u 11 , u 21 , and b 12 in a 2 × 3 switch. Fig. 3. Switch configuratio n corresponding to u 11 , u 21 , and b 12 in G 2 , 3 The in tuition be hind a conflict graph is that vertices which represent flows that cann ot b e served simultaneo usly ar e adjacent. As shown in [3], if fanou t splitting and network coding ar e a llowed, the switch can simu ltaneously serve two or m ore subflows of th e same broad cast flow and h ence such subflows are not adjacent to each other . For example, in Figure 4 , th ere are edg es between u 11 and b 12 , sinc e they conflict at input 1, and b etween u 11 and u 21 , since th ey conflict at outpu t 1; howe ver u 21 and b 12 are no t adjacen t, since they h av e different input and output. Theref ore, fro m the inp ut perspective, G K,N consists o f K induc ed complete subgrap hs G K,N ( U i ) f or u nicasts from each inpu t i , an d K induced stable sets G K,N ( B i ) for br oadcasts f rom each input i ; fr om the o utput perspective, G K,N consists of 2 N ind uced complete subgra phs G K,N ( U o j ) an d G K,N ( B o j ) fo r unicasts and broadca st sub flows to eac h ou tput j respectively . Here, we note that conflict grap h of a K × N multicast switch with unica sts an d bro adcasts tr affic can be r elaxed to that of u nicasts and sing le multicast per input. This r elaxation just removes vertices that represent broadc ast su bflows, which are n ot p art of th e mu lticast flow , fro m the conflict grap h. This cannot h urt the “perf ectness” o f the con flict graph . Th erefore, any upper bound on the imperfection ratio of the conflict graph for un icasts and bro adcasts bou nds th at of unicasts and single multicast p er input. Fig. 4. G 2 , 3 for a 2 × 3 switch with unicasts and broadcasts only B. Spee dup of 2 K − 1 K In this Section, we give an upp er boun d on speed up fo r K × N switches. W e present 2 K − 1 in duced perfect subgr aphs of G K,N that cover V K tim es. Then, with Propo sition 2.4, we then have 2 K − 1 K as an upper bound for speedup. Lemma 5 .1: Let G u = G K,N ( ∪ i ∈ [1 ,K ] U i ) b e an in duced subgraph of G K,N . Then G u is p erfect. Pr oof: G u is a n en hanced conflict graph for unicast traffic. One may check th at G u is a line graph o f a b ipartite graph, which is k nown to b e per fect [ 8]. Lemma 5.1 also fo llows fr om the result in [1] which shows that 1 00% throughp ut can be ach ie ved in a input-q ueued crossbar switch in th e con text of unicast traffic. Lemma 5 .2: Let G i = G K,N ( ∪ j ∈ [1 ,K ] B j ) ∪ U i for some i ∈ [1 , K ] be a n in duced subg raph of G K,N . Then G i is perfect. Pr oof: Assume that G i is n ot perfec t. So it must have an odd hole or od d anti-h ole as an in duced subg raph. Supp ose it has an odd hole, say H . In G i , any b roadcast su bflow , except the ones from input i , has no conflict on th e in put side. Suppo se such a subflow were p art of H , the n bo th its neighbo rs in H will be du e to ou tput side co nflicts. But in tha t case, the two neig hbors will th emselves co nflict at the o utput, thereby form ing a triangle. Since an odd h ole ca nnot con tain a triangle, we con clude th at H cann ot in clude any b j k , j 6 = i . This m eans H must be an ind uced sub graph of G K,N ( B i ∪ U i ) . Howe ver , B i induces a stable set, while U i induces a clique. Theref ore, G K,N ( B i ∪ U i ) is a split g raph 7 which is known to be per fect [8]. This co ntradiction sh ows that G i cannot co ntain an o dd h ole H . Suppose G i contains an odd anti- hole, say A . T his will happen if and o nly if G i contains an odd hole H A . Note that in G i , tw o vertices are connected if the correspo nding sub flows do not co nflict. Now , H A has to con tain at least one u nicast, say u ij , since the b roadcasts by them selves indu ce a perfect subgrap h in G i (they in duce th e comp lement of a disjoint union o f comp lete graph s, which is k nown to be perfect [ 8]). Now , u ij in G i is adjacent to any b i ′ j ′ , where i 6 = i ′ and j 6 = j ′ . Let b pq and b p ′ q ′ be vertices ad jacent to u ij in H A . Then, using the definition of G i , we can infe r that i 6 = p 6 = p ′ 6 = i and 7 A split graph is a graph whose verte x set can be partiti oned into a stable set and a clique. q = q ′ 6 = j . But this means, a ny vertex that is ad jacent to b pq is also ad jacent to b p ′ q ′ . Hence, H A cannot b e an o dd h ole. This proves that G i is perfect. Using Lemm as 5 .1 and 5.2, we der i ve ou r first u pper bou nd on speed up in K × N multicast switches with traffic patterns consisting of u nicasts and br oadcasts o nly . Pr opo sition 5.3: imp ( G K,N ) ≤ 2 K − 1 K . Pr oof: Consider th e fo llowing co llection of induced subgrap hs: K − 1 cop ies of G u from L emma 5. 1 an d G i from Lemma 5.2 for all i ∈ [1 , K ] . W e know that these subgraph s are all p erfect. In addition , these su bgraph s cover e ach vertex in v ∈ G K,N K times. By Pro position 2. 4, the claim fo llows. C. Sp eedup of 2 N N +1 The proof id ea in this sectio n is sim ilar to that of Section V -B. W e present 2 N induced perfect subgrap hs of G K,N that cover V N + 1 times, and then ap peal to Prop osition 2.4. Howe ver, u nlike Section V -B, here we change ou r focus from the input to o utput. Lemma 5 .4: Let G o 1 ,i = G K,N ( V i ) wher e V i = U o i ∪ ∪ j ∈ [1 ,N ] B o j be a n ind uced subgraph of G K,N . Then G o 1 ,i is p erfect. Pr oof: Assume that G o 1 ,i is n ot pe rfect. So it mu st have an odd hole or od d anti-h ole as an indu ced sub graph . Suppo se it h as an odd hole, say H . Since U o i ∪ B o i forms a com plete graph (kn own to be p erfect), H must co ntain vertice s of B o j , j 6 = i . Su ppose b kj ∈ B o j is part o f H , then H co ntains at least two vertices of B o j . This is because, in G o 1 ,i , b kj has only one conflict on the in put sid e; thus, neighb ors of b kj are u ki (input co nflict) an d B o j (outpu t con flict). Howe ver, note that B o j itself forms a comp lete graph , th erefore H contains at mo st two vertices of B o j . Th us, b kj and b k ′ j , k 6 = k ′ are in H . Th en, u ki and u k ′ i are in H . Howev er , th ese fo ur vertices form a cycle, thus G o 1 ,i cannot contain an odd h ole H . By th e same argument as in th e pro of for Lemma 5.2, we can sh ow that G o 1 ,i cannot co ntain an o dd a nti-hole. Lemma 5 .5: Let G o 2 ,i = G K,N ( V i ) where V i = B o i ∪ ∪ j ∈ [1 ,N ] U o j be a n ind uced subgraph of G K,N . Then, G o 2 ,i is p erfect. Pr oof: G o 2 ,i is an en hanced co nflict graph for un icast traffic in addition to all br oadcast subflows to outp ut i . Consider b 1 i ∈ B o i and u 1 i ∈ ∪ i ∈ [1 ,K ] U i . In a K × N switch, b 1 i and u 1 i represent subflows from inp ut 1 to ou tput i , and thus conflict with the same set o f subflows, i.e. n eighbo rs of u 1 i are neighbo rs o f b 1 i . In addition, b 1 i and u 1 i are in conflict. Therefo re, by Replication L emma (Lemma 2. 3), we know th at G o 2 ,i is perfect if G K,N ( V i \ { b 1 i } ) is per fect. W e can apply this argument rep eatedly for each b j i ∈ B o i , and dedu ce that if G K,N ( ∪ j ∈ [1 ,N ] U o j ) perf ect then G o 2 ,i is perfe ct. Note that from Lemma 5.1, we know that th e enh anced conflict grap h G u = G K,N ( ∪ i ∈ [1 ,K ] U i ) = G K,N ( ∪ j ∈ [1 ,N ] U o j ) fo r un icast traffic is perfect. Th erefore , G o 2 ,i is p erfect. Now , using Lem mas 5. 4 and 5.5, we can der iv e an upper bound for speedu p in K × N mu lticast switches with traffic patterns consisting of u nicasts and br oadcasts o nly . Pr opo sition 5.6: imp ( G K,N ) ≤ 2 N N +1 . Pr oof: Consider th e fo llowing co llection of induced subgrap hs: G o 1 ,i and G o 2 ,i for all i ∈ [1 , N ] . By Lemmas 5.4 and 5.5, we know that these subgrap hs ar e all perfect. In addition, these subgr aphs cover e ach vertex in v ∈ G K,N N + 1 time s. By Prop osition 2.4, the claim follows. V I . C O N C L U S I O N In th is p aper, we introd uce a simple gr aph theo retic boun d on speedup ne eded to achieve 100 % throug hput in a m ulticast network coding switch using the con cept o f conflict gr aphs. W e show that the imperfe ction ratio o f th e con flict gr aph gives an upper boun d on speed up. W e app ly this resu lt to K × N switches with traffic p atterns consisting of unicasts an d broadc asts on ly to o btain an u pper bound o f min( 2 K − 1 K , 2 N N +1 ) . For a 2 × N switch, this giv es a boun d of 3 /2 on speedup ; howe ver, we c onjecture that the actual speedu p req uired to achieve 100% throughp ut in a 2 × N switch with traf fic patterns consisting of unicasts and b roadcasts only is 5/4. W e have verified this conjectur e usin g a compu ter f or N = 3 , 4 and 5. In summary , by allowing n etwork cod ing in multicast switches, we get n ot o nly an insightful char acterization of the speedu p need ed for 100% th rough put, but also a gain in speedup. W e have shown that netw ork coding, which is usually implemented u sing sof tware, can substitute speedu p, which is often ach iev ed by addin g extra switch fabr ics. A C K N O W L E D G M E N T This mater ial is based upon research p artly supp orted by Stanford University un der the Complex Network Inf rastruc- tures for Communication and Power , Sponsor A w ard No. PY -1362; University of Califo rnia under D A WN: Dynamic Adhoc W ireless Networking, Spon sor A ward No. S0 17693 8; Air Force Aero space Research - OSR u nder the Robust Self- Authenticating Network Cod ing, Spo nsor A ward No. F A9550- 06-1- 0155; a nd DARP A ITMANET . R E F E R E N C E S [1] N. McKe own, V . Ananthar am, and J. W alrand, “ Achievi ng 100% through- put in a n input-queu ed s witch” , in Proce edings of IEEE INFOCOM , 1996, pp. 296-302. [2] J.K. S undarara jan, M. M ´ edard, R. Koet ter , and E . Erez, “ A systematic appraoc h to net work coding proble ms using conflict graphs”, in Proce ed- ings of the UCSD W orkshop on Information Theory and its Applications , San Diego, CA, February 2006. [3] J.K. Sundararaja n, M. M ´ edard, M. Kim, A . Eryilmaz, D. Shah, and R. Ko etter , “Network Coding in a Multicast Switch”, in Pr oceedings of IEEE Infocom , 2007 [4] C. Cara manis, M. Rosenblum, M. X. Goemans, and V . T arokh, “Schedul - ing algorithms for provid ing flexibl e, rate-based, quality of service guarant ees for packe t-switchin g in Banyan networks”, in Proce edings of the Confer ence on Informati on Scie nces and Systems , 2004, pp. 160-166. [5] M. A. Marsan, A. Bianco, P . Giaccone , E . Leonardi, and F . Neri, “Mul- ticast traf fic in input-que ued switches: optimal scheduling and m aximum throughput ”, IEE E/AC M T rans. Netw . , vol . 11, no. 3, pp. 465-477, 2003. [6] S. Gerke and C. McDiarmid, “Graph Imperfecti on I, II”, Journal of Combinato rial Theory , Series B 83 (2001), 58-78, 79-101. [7] L. Lov ´ asz, “Normal hypergraphs and the perfect graph conjec ture”, Discr ete Mathematic s 2 (1972) 253-267 [8] A. Schrijv er , Combinatorial Optimizati on: P olyhedra and Effici ency , Springer V erlag, 2003. [9] R. Ahlswede, N. Cai, S. -Y . R. Li and R. W . Y eung, “Network informa tion flo w”, IEEE T rans. on Information Theory , vol . 46, pp. 1204-1 216, 2000.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment