The Secrecy Graph and Some of its Properties
A new random geometric graph model, the so-called secrecy graph, is introduced and studied. The graph represents a wireless network and includes only edges over which secure communication in the presence of eavesdroppers is possible. The underlying point process models considered are lattices and Poisson point processes. In the lattice case, analogies to standard bond and site percolation can be exploited to determine percolation thresholds. In the Poisson case, the node degrees are determined and percolation is studied using analytical bounds and simulations. It turns out that a small density of eavesdroppers already has a drastic impact on the connectivity of the secrecy graph.
💡 Research Summary
**
The paper introduces a novel random geometric graph model called the secrecy graph to capture the effect of eavesdroppers on the connectivity of wireless ad‑hoc networks. Two underlying point processes are considered: (i) a deterministic lattice and (ii) a homogeneous Poisson point process (PPP). In both cases the “good” nodes (Φ) represent legitimate transmitters/receivers, while the “bad” nodes (Ψ) model eavesdroppers whose locations are assumed known to the legitimate parties.
Model definition.
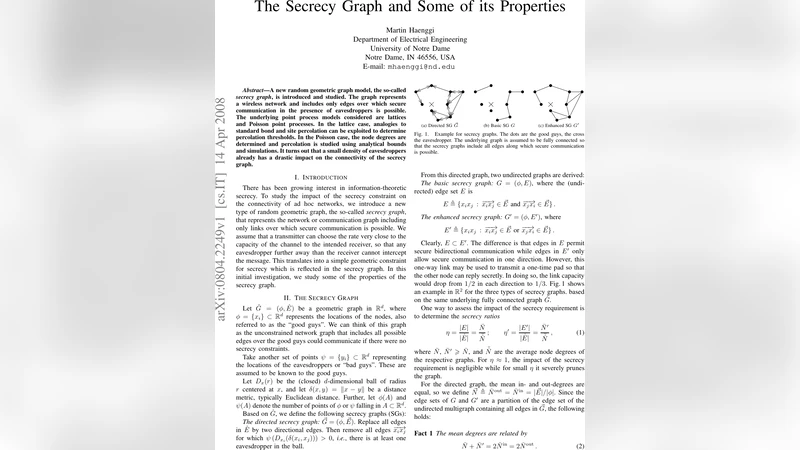
Start from an unconstrained geometric graph (\hat G) that contains every possible link between good nodes. For each ordered pair ((x_i,x_j)) of good nodes, the directed edge (x_i!\to!x_j) is removed if there exists at least one eavesdropper inside the closed ball centered at (x_i) with radius equal to the Euclidean distance (|x_i-x_j|). The resulting directed graph is denoted (\tilde G). From (\tilde G) two undirected graphs are derived: the basic secrecy graph (G) (an edge exists only if both opposite directed edges survive) and the enhanced secrecy graph (G’) (an edge exists if at least one direction survives). The ratios (\eta=|E|/|\hat E|) and (\eta’ = |E’|/|\hat E|) quantify how much of the original connectivity remains.
Lattice case.
When (\hat G) is the standard square lattice (L_2) and eavesdroppers are placed on the mid‑points of edges with probability (p), the problem reduces to classical bond percolation. Consequently the percolation threshold for the enhanced graph (G’_p) is exactly (p_c=1/2). If eavesdroppers are placed on lattice vertices (site percolation) the critical probability is numerically around (p_c\approx0.41). These results show that even when the density of eavesdroppers is only a fraction of the legitimate node density, an infinite connected component can still exist.
Poisson case.
The underlying graph (\hat G_r) is Gilbert’s disk graph: two good nodes are linked if their distance does not exceed a transmission radius (r). Good nodes form a PPP of intensity 1, eavesdroppers form an independent PPP of intensity (\lambda). The paper derives closed‑form expressions for several key quantities:
Out‑degree distribution. For (r=\infty) the out‑degree of a typical node in (\tilde G_{\lambda,\infty}) is geometric with mean (1/\lambda). For finite (r) the distribution is given by (14), a mixture of a Poisson term (when no eavesdropper lies inside the transmission disk) and a truncated Poisson term conditioned on the distance to the nearest eavesdropper. The mean out‑ and in‑degrees coincide:
\
Comments & Academic Discussion
Loading comments...
Leave a Comment