A Game Theoretic Framework for Decentralized Power Allocation in IDMA Systems
In this contribution we present a decentralized power allocation algorithm for the uplink interleave division multiple access (IDMA) channel. Within the proposed optimal strategy for power allocation, each user aims at selfishly maximizing its own ut…
Authors: Samir Medina Perlaza, Laura Cottatellucci, Merouane Debbah
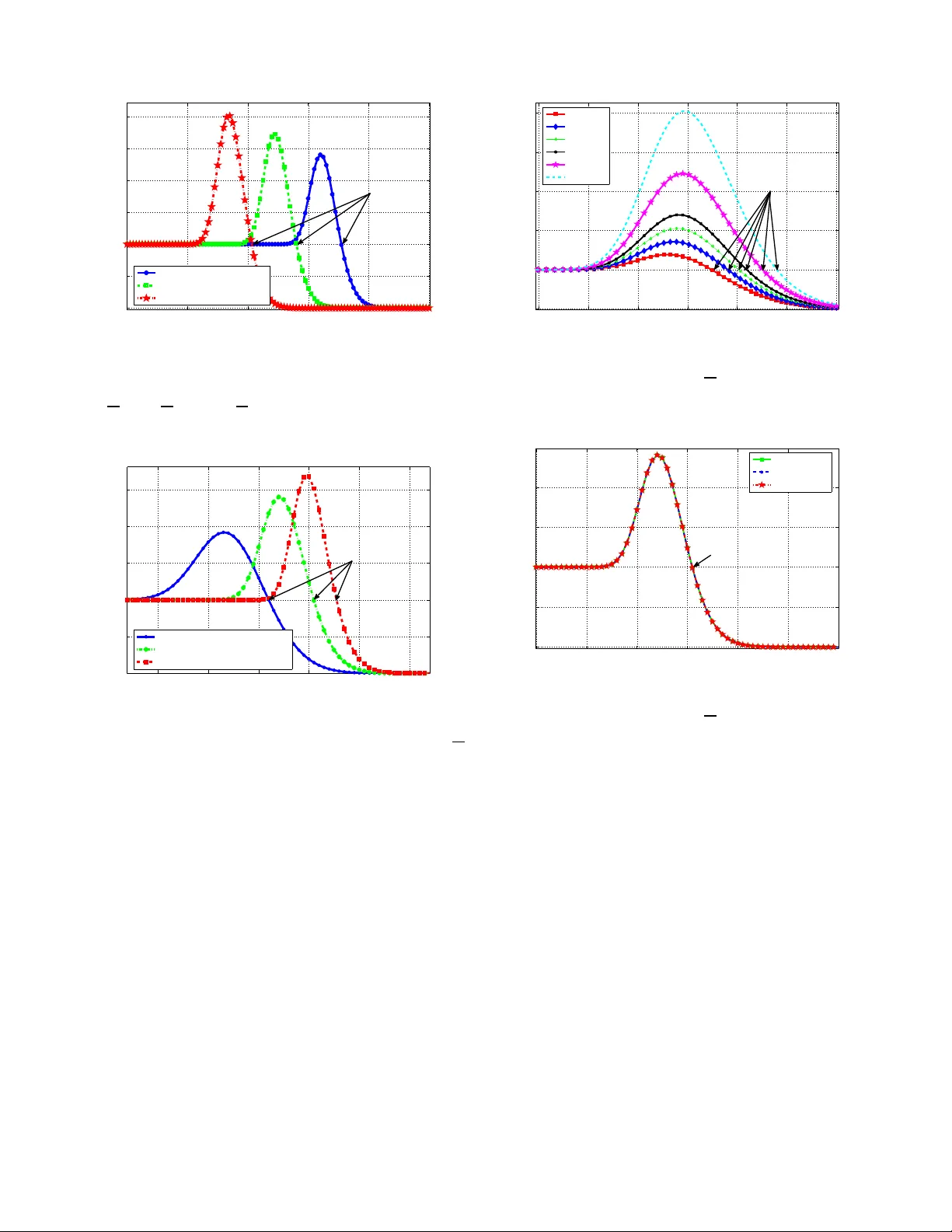
A Game Theoretic Frame work for Decentraliz ed Po wer Allocat ion in IDMA Sys tems Samir Medina Perlaza France T elecom R&D - Orange Labs , France samir .medinaperlaza @orange-ftgroup.com Laura Cottatellucci Institute Eurec om, Franc e Laura.Cottatellucci@eu recom.fr M ´ erouane Debbah SUPELEC, Franc e Merouane.De bbah@sup elec.fr Abstract —In this contribution we present a decentra l- ized power allocatio n alg orithm for the uplink interleave division multiple access (IDMA) channel. Within the pro- posed optimal strategy f o r po wer allocatio n, each user aims a t selfishly max imizing its own utility function. An iterative chip-by-chip (CBC) decoder at the receiver and a rational selfish beha v ior o f all the us ers according to a classical game-theo retical f ramework are the underly ing assumptions of this work. This approach leads to a channel in version policy wher e the o ptimal power level is set loca lly at each terminal based on the knowledge of its own channel realization, t he noise level a t the receiver and t he number of active users in t he network. I . I N T RO D U C T I O N Interleav e d i v ision multiple access (IDMA) has been identified as a promising multiple ac cess technique in the c ontext of ce llular networks [1] and self-or ganizing networks (e.g ad h oc networks ) [2]. In this domain, distrib uted power algorithms play a central practical and theoretical role. Non etheless, the study o f distributed power alloca tion a lgorithms for IDMA is still an u n- solved prob lem. The centralized power alloca tion (CP A) has been tac kled by several authors (see [3], [4], a nd references therein). In these works, iterativ e multiuser detection/chan nel deco ding is assume d at the receiv er and the base station determines the power to be trans - mitted by eac h u ser , acc ording to a global o ptimum criterion and typica lly having complete chann el state information ( CSI). In this co ntrib u tion, a novel frame- work to tackle the DP A prob lem in IDMA systems using tools from game theory is presented. The propo sed approach ass umes it erati ve multiuser detec tion/channel decoding at the recei ver based on the chip-by -chip (CBC) algorithm [1], and relies on the s ignal to noise ratio (SINR) evolution technique [4] for no n-heavily loa ded systems. In o ur a pproach, we a ssume that eac h user allocates the power by max imizing its o wn utility func tion a nd by assuming a c ompetiti ve s elfish an d rational behavior of the other users. The propose d utility function for a giv e n user is the ratio betwee n a power of the user’ s goodput (probab ility of an error -free de tected frame) and its own transmit power . Our decen tralized approach requires only the knowledge of the noise power a t the receiv er , the channe l gain o f the user of interest, and the number o f acti ve users in the syste m. It yields a chann el in version policy for the power allocation. Th is policy is applied to an IDMA system with a repetition c ode o f length N bits. Simulations s how that the alloca ted power is substantially independ ent of the numb er of users in typical operation cond itions for a practica l system. Therefore, the knowledge of the number of a cti ve us ers in the s ystem be comes irrele vant as observed in the centralized cas e in [3]. I I . S Y S T E M M O D E L Consider the uplink of an IDMA system with K chip-synch ronous active us ers. Each mobile and the base s tation a re e quipped with a single antenna. Th e base station performs CB C iterativ e multiuser de coding based on s uccess i ve interf erence cancellation (SIC) or parallel interference c ancellation (PIC) as propose d in [1]. Den ote by b k the information bits of the len gth- M ′ messag e to be transmitted by the k th user . An identical code with low rate R i s a pplied to the messag es o f all the users. The coded information bits, referred to as chips, are permuted by an interleaver π k of leng th M = M ′ R chips. Each interleaver is unique in the n etwork, i.e. π k 6 = π i , ∀ i 6 = k . The ba se band signal r ( j ) sa mpled at the chip-rate at the rec ei ver is r ( j ) = K X i =1 √ p i h i x i ( j ) + n ( j ) , j = 0 . . . M − 1 (1) where j is the discrete time index for the chip interval and h i and p i represent the channel realization and the transmit p ower o f the i th user , respectively . Here, x i ( j ) represents the c hip transmitted by the i th user at chip interval j and n ( j ) is the additi ve wh ite Gaussian noise (A WGN) process with zero mea n and variance σ 2 . For the sake o f simplicity , we introduce our results assuming an antipodal mo dulation, i.e x i ( j ) ∈ {− 1 , 1 } , real valued chan nel realizations, an d real noise samples. The extension to more complex modulation sche mes is straightforward. Th e receiver is ma de o f an elementary multiuser signal estimator (ESE) ba sed o n the p rinciple of maximum a pos teriori (MAP) detection, a set of interleav ers π k and de-interleavers π − 1 k , and a s et of K sing le user a pos teriori probability d ecoders (DEC). The dec oders fee d back s oft information to the ESE module in turbo configuration to iterate and improv e the estimations. This structure is kn own as CBC decode r and is described in [1]. The S INR at the input of the decode r c an be estimated at ea ch iteration of the CBC detection by means of the SINR ev olution tec hnique [4]. It is shown in [3] tha t in the steady state, the SINR of user k , deno ted as γ k , conv erges to the s olution to the follo wing system of eq uations γ ss k = p k | h k | 2 K X i =1 ,i 6 = k p i | h i | 2 f ( γ ss i ) + σ 2 , ∀ k ∈ [1 , K ] , (2) where the supe r -index ss stands for stea dy state. The function f ( x ) ∈ [0 , 1] , ∀ x > 0 repre sents the amount of multiple acces s interference (MAI) that is eliminated at each i teration of the CBC detection [4]. This fun ction depend s o n the coding sch eme and can be obtaine d by Monte Carlo s imulations a s desc ribed in [1]. The system (2) might hav e se veral s olutions. Nonetheless, it has been shown in [3] that in the case of | h i | 2 p i = | h j | 2 p j ∀ i 6 = j , the sys tem ha s a un ique solution given by the fi x point equation γ ss = p k | h k | 2 ( K − 1) | h k | 2 p k f ( γ ss ) + σ 2 ∀ k ∈ [1 , K ] (3) and γ ss k = γ ss , with 1 6 k 6 K . Additionally , it has been shown that the SINR evo- lution technique predicts precise ly the SINR u nder the constraint of non-overloaded s ystems [1], [4]. Howe ver , we have found in our simulations that this is not the case for h eavily ov erloaded sy stems. Under this co nstraint, the SINR evolution techn ique do es not match the SINR obtained at the ou tput of the ESE module. In order to exclude t his case, we res trict our study to non-overloaded systems, i.e. we cons ider tha t K N 6 1 a lw a ys ho lds. I I I . A N O N - C O O P E R A T I V E P OW E R A L L O C AT I O N G A M E W e d efine the power allocation problem as a strategic game denoted by the triplet S , P , ( u k ) k ∈ S , where S = { 1 , . . . , K } is the se t of players o r active mobiles , P rep resents the s et o f strategies, and u k is the utility function o f us er k . In this work, the strategy of eac h user consists of a ll the possible transmittable power levels p k ∈ R + , ∀ k ∈ S . W e follo w the sa me line as in [3], [5] and [6] and enforce constraints on t he maximum transmit power later . Furthermore, the utility function u k of user k is d efined as the ratio between the positiv e power s k of its goodp ut g ( γ k ) , i.e. the probability of an e rror -free detected pa cket, a nd its transmit power 1 u k ( p , h ) = ( g ( γ k )) s k p k ∀ k ∈ S , (4) where p = ( p 1 , p 2 , . . . , p K ) and h = ( h 1 , h 2 , . . . , h K ) are the vectors of transmit power le vels a nd channel realizations, respe cti vely . Expres sion (4 ) ge neralizes the utility function pres ented in [5] a nd [6] when s k = 1 , ∀ k ∈ S . W ith respec t to the reference utility function with s k = 1 the user k will choo se s k > 1 if it is interested in b etter performance a t the exp enses o f a higher transmitted power . On the con trary , if it needs to save power then it will se t s k < 1 . In this study , we as sume that all the us ers are aware o f the fact that they a re all interested on the sa me Q oS profile, i.e. s 1 = . . . = s K = s . The objectiv e of the playe r k is to determine the trans - mit power p ∗ k that selfis hly maximizes its u tilit y function u k ( p ∗ , h ) und er the a ssumption that a similar strategy is adopted by all the other use rs. Thus, the optimum power [7] is obtained as solution to the followi ng sy stem of equations: ∂ ∂ p k u k ( p ∗ , h ) = g ( γ k ) s − 1 ( p k ) 2 sg ′ ( γ k ) p k ∂ ∂ p k γ k − g ( γ k ) = 0 ∀ k ∈ S . (5) Here, g ( γ k ) ′ represents the first deri vativ e of g ( γ k ) . Due to the nature of the c hannel (non-error free ch annel), the term g ( γ k ) s − 1 ( p ∗ k ) 2 , ∀ k ∈ S is always non-zero. Thus, the system in (5) could be s implified as sg ′ ( γ k ) p k ∂ ∂ p k γ k − g ( γ k ) = 0 ∀ k ∈ S . (6) Furthermore, it has bee n s hown in [7] that ∂ ∂ p k γ k = γ k p k 1 + γ k f ( γ k ) 1 − γ 2 k f ′ ( γ k ) q k ( γ ) , ∀ k ∈ S (7) where γ = ( γ 1 , . . . , γ K ) an d q k ( γ ) = 1 − γ k f ( γ k ) + γ 2 k f ′ ( γ k ) 1 − γ 2 k f ′ ( γ k ) (1 + γ k f ( γ k )) ( A + 1) ! and A = K X i =1 γ 2 i f ′ ( γ i ) 1 − γ 2 i f ′ ( γ i ) . Replacing (7) in (6) we obtain the system of e quations sg ′ ( γ k ) γ k 1 + γ k f ( γ k ) 1 − γ 2 k f ′ ( γ k ) q k ( γ ) − g ( γ k ) = 0 , ∀ k ∈ S (8) 1 Further discussions on the definition of this utility function in p k = 0 can be found in [5] and [6]. In (8), the variables are o nly γ k , ∀ k ∈ S . Therefore, the system does no t dep end directly on the channel realizations and the trans mit po we r o f each user . This property was also observed in the centralized approac h [3]. Moreo ver , in the sy stem (8), all the equations are identical a nd the system is in variant to variable permu- tations. This implies that the solutions are also identical, i.e. γ 1 = γ 2 = · · · = γ K = γ . Thus, the system (8) reduces to a single equa tion sg ′ ( γ ) γ q ( γ ) − g ( γ ) = 0 (9) where q ( γ ) = (1 − γ 2 f ′ ( γ ))+( K − 1)( γ 2 f ′ ( γ ) )(1+ γ f ( γ )) (1 − γ 2 f ′ ( γ ))(1+( K − 1) γ 2 f ′ ( γ )) . W e de fine z ( γ ) = sg ′ ( γ ) γ q ( γ ) − g ( γ ) and we n ame it tar get func tion . The zeros of the tar get function are candidates to be the optimal SINR γ ∗ . The optimal SINR correspond s to the SINR at whic h the utility func tion of e ach use r is maximized. If the s et of optimal SINR γ ∗ i = γ ∗ , ∀ i ∈ S is kn own, it is possible to obtain an expression for the op timal transmit power level from expressions (24) and (25 ) in [3], p ∗ k = 1 | h k | 2 σ 2 γ ∗ 1 − ( K − 1) γ ∗ f ( γ ∗ ) ∀ k . (10) Eqn. (10 ) holds under the co nstraint 2 K < 1 γ ∗ f ( γ ∗ ) + 1 (11) since only pos iti ve power levels are meaningful. Note that the expression (10) c ould be also obtained from the fix point equ ation (3) as un ique solution. Interestingly , the power alloca tion for a giv en u ser depend s on the op timal SINR γ ∗ , its channe l gain, a nd the nu mber o f ac ti ve users. The refore, the knowledge of all the other u sers’ c hannel ga ins in the network is no t required. I V . A D E C E N T R A L I Z E D P OW E R A L L O C A T I O N A L G O R I T H M In this sec tion, we propos e a power a llocation algo- rithm based on the game in vestigated in Section III under the cons traint of non-overloaded sy stems, i.e. K N 6 1 . In general, the target function z ( γ ) is not linear a nd the solution to z ( γ ) = 0 requires a nu merical a pproach. The algorithm we p resent here is b ased o n the secant method. The iterati ve search of the optimum SINR γ ∗ is initialized by c hoosing two values γ 1 and γ 2 such that • both γ 1 and γ 2 are not lower than the minimum SINR re quired γ min for reliable communica tions a t rate R without considering SIC or PIC. Ac cording 2 The constraint is widely satisfied since the function f ( γ ) de- creases rapidly with γ [1], [3] to the Shannon capacity la w C = 1 2 log 2 (1 + γ ) . Thus, γ min = 2 2 R − 1 a nd γ min ≤ γ 1 ≤ γ 2 ; • z ( γ 2 ) ≤ z ( γ 1 ) . Furthermore, in practical systems, the u sers ha ve power cons traints. It might happe n that the optimal power p ∗ k for a gi ven optimal SINR γ ∗ exceeds the maximum transmittable power p max . In this case, a user i , ∀ i ∈ S cou ld either trans mit at the max imum power p i = p max or not transmit p i = 0 [3]. Let us deno te as γ p max k , 0 = p max | h k | 2 ( K − 1) p k | h k | 2 + σ 2 the S INR a chiev ed by the i th user before the fi rst iteration of the CBC algorithm when transmitting a t the maximum power p max . Indee d, if γ p max k , 0 enables reliable d ecoding, i.e. γ p max k , 0 > γ min , then the use r transmits at the maximum p ower level p max . In this c ase, the us er does not reac h the optimal γ ∗ . However , a reliable decod ing is always e nsured. If the condition γ p max k , 0 > γ min is n ot satisfied, the k th user does not trans mit a nd is considered in outage . Note that, the condition ov er the SI NR γ p max k , 0 is a necessary b ut not sufficient condition for a user no t to be dec oded. In fact, certain users could attain an SINR γ p max k , 0 higher than γ min after deco ding as a result of the iterati ve d ecoding. Howe ver , a user cann ot ev aluate this p ossibility . In fact, due to the incomplete kn owl edge av ailable ab out other users, it c an n ot determine if iterati ve de coding is ab le to s uf ficiently improve the initi al SINR and en able a reliable decoding. The n, transmitting might r esult in a waste of energy and additional interferenc e for all the other use rs. Therefore, the power allocation rule is p k = p ∗ k if p ∗ k ≤ p max p max if p ∗ k > p max and γ p max k , 0 ≥ γ min 0 otherwise (12) Let us denote with ε > 0 the de sired acc uracy to de ter - mine γ ∗ . The p ower alloca tion algorithm is s ummarized as follows 1) Initi alization of the se cant metho d γ 1 = γ min while ( z ( γ 1 ) > z ( γ min ) ) then γ 1 = γ 1 + ∆ with ∆ ∈ 0 , 1 2 end γ 2 = γ 1 + ∆ with ∆ ∈ 0 , 1 2 2) Iterati ve s tep of the secan t metho d while | γ i +1 − γ i | > ε γ i +1 = γ i − γ i − γ i − 1 z ( γ i ) − z ( γ i − 1 ) z ( γ i ) end 3) End of the secant metho d γ ∗ = γ i +1 . 4) P ower allocation Determine the transmit power according to (12). −10 −8 −6 −4 −2 0 2 4 6 8 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 Minimum SINR Optimal SINR SINR [dB] Utility Function Theoretical Result. K =16 Practical Result. K = 16 Figure 1. A verage Utility Function versu s the SINR in decibels for a st andard IDMA system with K = 16 users, M = 1000 bits and coding rate R = 1 16 . Solid and dashed lines correspond to the SINR e volution and the system simulation, respecti vely . V . P E R F O R M A N C E A S S E S S M E N T The performance of the propose d po wer allocation scheme is as sessed assuming antipod al modu lation and a repetition code with diff erent rates R = 1 N and N = 16 , 32 , 64 . The ch annel gains and the noise are real and Gaussian d istrib u ted with zero mean and u nit variance. W e refer to the SINR at which the utility function (4) is maximized as the optimal ope rating point γ ∗ . An approximate expression for the bit error rate when a repetition c ode with rate R = 1 N is u sed is P e ≈ ⌊ N 2 ⌋ X i =0 N N 2 + i Q p 2 γ k ⌈ N 2 ⌉ + i 1 − Q √ 2 γ k ⌈ N 2 ⌉ − i (13) In (13), the function Q ( . ) is the co mplementary error function of a Ga ussian ran dom variable. It repres ents the probability of error o f one chip in the case of antipodal modulation. He nce, the goodput can be written as: g ( γ k ) = (1 − P e ) M . (14) For the c oding sche me cons idered in t his con trib ution, the fun ction f ( · ) is determined by Monte Carlo simu- lations as de scribed in [ 1]. The obta ined results match those p resented in [3] and [8] perfectly . In Figure 1, we plot the average utilit y function versus the SINR γ wh en s = 1 . The solid line shows the theoretical pe rformance determined by plug ging (14) in (4), while the dashe d lines are o btained with the actual BER at the output of the decode r . W e noticed in all the non-overloaded c ases that the utility has a unique max imum. The effects o f the coding rate, the frame leng th, an d the number of use rs on the optimum operating point are as sessed in Figu res 2, 3, 4, a nd 5. In F igure 2, the target function (9) is plotted as a function of the SINR γ for three diff erent co ding rates while the frame length and the numb er of users are kept constant. Lower coding rates determine lo wer o ptimal SINRs. In Figure 3 , the target function is plotted as a function of the SINR γ con sidering three dif ferent frame lengths, keeping the coding rate and the n umber of users constant. In this case, longer frames lead to higher optimal SINR values. In Figure 4, we plot the target function as a fun ction of the SINR for sev eral exponents s of the g eneralized utility function (4), while keeping the number of use rs, the frame length and the co ding rate constant. When users are interested in b etter pe rformance rather than saving p ower ( s > 1) , the o ptimal SINR increases and vice versa. In Figure 5, the target function is plotted for 4, 8, and 16 acti ve users as a function of the SINR wh en the coding rate a nd frame length a re kept constant. Th e four lines overlap comp letely . Therefore, the v ariation of the nu mber o f acti ve use rs K has a negligible e f fe ct o n the optimal SINR. The n, the optimal operating point is prac tically independe nt of the number of use rs. T his effect was also o bserved in the ce ntralized case in [3]. In gen eral, a con venien t solution for a non-coo perati ve game is the Nash equ ilibrium (NE). By defi nition, the NE is a solution such that no player is interes ted on changing its strategy since no improvement could be obtained in its own utility while keeping the other users’ utilities unchan ged. In this cas e, even thoug h the simulations results sh ow that the re is a unique solution to the game ( γ ∗ ) , we could no t prov e a nalytically the uniquen ess of the NE s ince the functions f ( γ ) and g ( γ ) depe nd on the c oding scheme. Howev er , particular cas es ha ve been already s tudied. In the case where no interference cance llation is p erformed, i.e f ( γ ) = 1 , the p roof is similar to the one pres ented in [5] with s = 1 for the CDMA c ase. V I . C O N C L U S I O N S W e pro vided a novel frame work for decentralized power allocation in IDMA systems bas ed on a game- theoretic approac h. In this context, e ach use r a ims at selfishly maximizing its own utility function a ssuming a similar behavior is adopted by all the other use rs. It leads to a chann el inv e rsion power allocation p olicy where the optimal power level could be s et a t each terminal bas ed on the knowledge of its o wn channel realization, the noise e nergy a t the recei ver , an d the number of acti ve users in the ne twork. Interes tingly , we found that under practical operation conditions, the knowledge of the number of active users beco mes irrele vant a s observed in the centralized case in [3]. −8 −6 −4 −2 0 2 −1 −0.5 0 0.5 1 1.5 2 SINR [dB] Target Function z( γ ) Code Rate: 1/16 Code Rate: 1/32 Code Rate: 1/64 Optimal Points Figure 2 . T arge t function z ( γ ) versus SINR in decibels for a standard IDMA system with parameters K = 16 users, M = 1000 bit s. T he solid, dot-dashed and dashed li nes correspond to the coding rates R = 1 16 , R = 1 32 and R = 1 64 respecti vely . −4 −3 −2 −1 0 1 −1 −0.5 0 0.5 1 1.5 SINR [dB] Target Function z( γ ) Frame Length: 128 Frame Length: 1000 Frame Length: 4096 Optimal Points Figure 3 . T arge t function z ( γ ) versus SINR in decibels for a standard IDMA system with parameters K = 16 users, coding rate R = 1 16 bits. T he solid, dot-dashed and dashed li nes correspond to the frame lengths 128 , 1000 and 4096 bits respecti vely . V I I . A C K N O W L E D G E M E N T S This work is dev eloped in the frame of T amara pr ojec t supported by Gr o upe des Ecoles des T ´ el ´ ecommunic ations (GET , F ran ce) . Samir Medina Perlaza is su pported by Pr ogramme Al β an , the European Union prog ramme of high level scho larships for Latin America, scholarsh ip No . E0 6M101130CO. R E F E R E N C E S [1] L . Ping, L. Liu, K. W u, and W . K. Leung, “Interleave di vision multiple-access, ” W ireless Communications, IEEE T ransactions on , vol. 5, no. 4, pp. 938–9 47, 2006. [2] K. Kusume and G. Bauch, “ A si mple complexity reduction strategy for interlea ve division multiple access, ” in V ehicular T echnolo gy Confer ence, 2006. VTC -2006 F all. 2006 IE EE 64th , 2006, pp. 1–5. −3 −2.5 −2 −1.5 −1 −0.5 0 −1 0 1 2 3 4 SINR [dB] Target Function z( γ ) s: 0.4 s: 0.6 s: 0.8 s: 1 s: 1.6 s: 2.5 Optimal Points Figure 4 . T arge t function z ( γ ) versus SINR in decibels for a standard IDMA system with coding rate R = 1 16 , frame length M = 1000 bits, K = 1 6 users and different values for the parameter s −4 −3 −2 −1 0 1 −1 −0.5 0 0.5 1 SINR [dB] Target Function z( γ ) 4 users 8 users 16 users Optimal Points Figure 5 . T arge t function z ( γ ) versus SINR in decibels for a standard IDMA system with coding rate R = 1 16 , frame length M = 1000 bits. The solid, dashed, and dot-dashed li nes correspond to K = 4 , K = 8 and K = 16 users respecti vely . [3] Z . Rosberg, “Optimal transmitter power control in interleav e di- vision multiple access (idma) spread spectrum uplink channels, ” W ir eless Communications, IEEE T ransactions on , vol. 6, no. 1, pp. 192–201, 2007. [4] L . Ping and L. Liu, “ Analysis and design of idma systems based on snr ev olution and power all ocation, ” in V ehicular T ech nology Confer ence, 2004. VT C2004-F all. 2004 IEEE 60th , vol. 2, 2004, pp. 1068–107 2 V ol. 2. [5] N. Bonneau, M. Debbah, E. Altman, and Are, “Non-atomic games for multi -user systems, ” IEEE JSAC, issue on Game Theory in Communication Systems , 2008. [6] F . Meshkati, H. V . Poor , S. C. Schwartz, and N. B. Mand ayam, “ An energy-ef fi cient approach to power control and receiver design in wireless data netw orks, ” Communications, IE EE T rans- actions on , vol. 53, no. 11, pp. 1885–18 94, 2005. [7] S . M. Perlaza, “Decentralized po wer allocation in idma n et- works, ” Master’ s t hesis, ENST - Paris, December 2007. [8] M. S. Lau and W . Y ue, “ A linear zero-one formulation of optimal po wer allocation of idma systems , ” in W ir eless Communications, Networking and Mobile Computing , 2007. W iCom 2007. Inter- national Confer ence on , 2007, pp. 637–640.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment