RSA algorithm with a new approach encryption and decryption message text by ascii
In many research works, there has been an orientation to studying and developing many of the applications of public-key cryptography to secure the data while transmitting in the systems, In this paper we present an approach to encrypt and decrypt the message text according to the ASCII(American Standard Code for Information Interchange) and RSA algorithm by converting the message text into binary representation and dividing this representation to bytes(8s of 0s and 1s) and applying a bijective function between the group of those bytes and the group of characters of ASCII and then using this mechanism to be compatible with using RSA algorithm, finally, Java application was built to apply this approach directly.
💡 Research Summary
The paper proposes a method that integrates the RSA public‑key algorithm with an ASCII‑based representation of text messages. The authors begin by converting each character of the input string into its binary ASCII code (7‑ or 8‑bit). The resulting binary stream is then segmented into 8‑bit blocks (bytes). Each byte, which naturally lies in the range 0–255, is mapped to an ASCII character through a bijective function; in practice this mapping is essentially the identity mapping because ASCII already provides a one‑to‑one correspondence between byte values and characters.
After this conversion, the sequence of integer values (one per byte) is fed directly into the RSA encryption routine. Using a standard RSA key pair (public exponent e, modulus n, private exponent d), each byte m is encrypted as c = m^e mod n, and decryption is performed as m = c^d mod n. The authors argue that this approach preserves compatibility with conventional RSA implementations while allowing a straightforward text‑to‑cipher conversion.
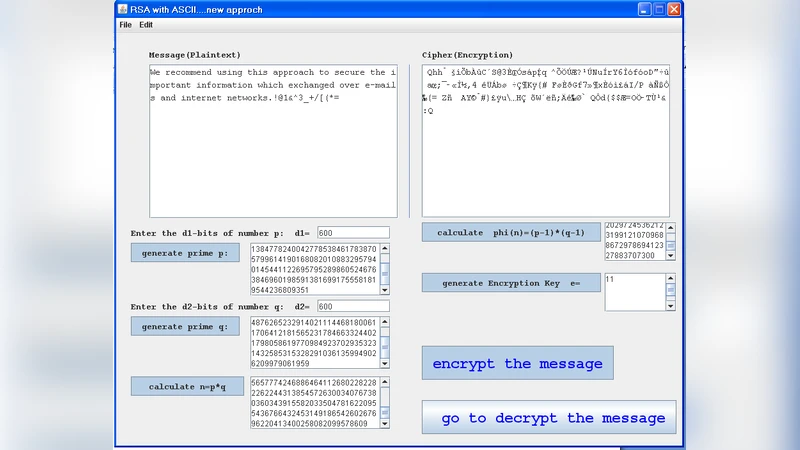
Implementation details are provided for a Java application. The program uses Java’s BigInteger class for modular exponentiation, offers key‑generation for 1024‑bit and 2048‑bit moduli, and presents a graphical user interface where users can input plaintext, generate keys, and trigger encryption or decryption. The encrypted output is displayed as a sequence of large integers (each the size of the RSA modulus), which are considerably longer than the original byte sequence. For example, encrypting the 11‑character string “Hello World” with a 1024‑bit key produces 11 ciphertext blocks, each 128 bytes long, resulting in a total ciphertext of roughly 1.4 KB.
The experimental section consists mainly of illustrative examples; no systematic performance benchmarks, memory‑usage statistics, or comparative analysis with established RSA padding schemes (such as PKCS#1 v1.5 or OAEP) are presented. Consequently, the paper does not address the well‑known inefficiency of encrypting small blocks directly with RSA, nor does it discuss the security implications of using raw bytes without padding (e.g., susceptibility to chosen‑ciphertext attacks or side‑channel leakage).
In the related‑work discussion, the authors mention that many prior studies have applied RSA to secure data transmission, but they claim novelty in the explicit “byte‑to‑ASCII bijection” and the simplicity of their Java prototype. However, this bijection is essentially a restatement of the standard ASCII encoding, and the overall workflow mirrors the classic “text → bytes → RSA” pipeline already covered by existing standards.
The conclusion reiterates the contribution as a proof‑of‑concept integration of ASCII conversion and RSA encryption, and suggests future work on handling larger messages, optimizing block sizes, incorporating standard padding, and conducting a thorough security analysis. While the idea is clearly presented and a functional prototype is delivered, the paper lacks rigorous evaluation, quantitative comparison with existing standards, and a convincing argument that the proposed method offers any security or efficiency advantage over conventional RSA implementations.
Comments & Academic Discussion
Loading comments...
Leave a Comment