Your Computer is Leaking
This presentation focuses on differences between quantum computing and quantum cryptography. Both are discussed related to classical computer systems in terms of vulnerability. Research concerning quantum cryptography is analyzed in terms of work done by the University of Cambridge in partnership with a division of Toshiba, and also attacks demonstrated by Swedish researchers against QKD of energy-time entangled systems. Quantum computing is covered in terms of classical cryptography related to weaknesses presented by Shor’s algorithm. Previous classical vulnerabilities also discussed were conducted by Israeli researchers as a side-channel attack using parabolic curve microphones, which has since been patched.
💡 Research Summary
The paper titled “Your Computer is Leaking” provides a comprehensive examination of how emerging quantum technologies intersect with the security of classical computing systems. It begins by framing the rapid development of quantum information science as a disruptive force to traditional cryptographic assumptions, establishing the urgency for a detailed comparative analysis of quantum computing and quantum cryptography.
In the first major section, the authors focus on quantum computing, specifically Shor’s algorithm, and its implications for widely deployed public‑key schemes such as RSA, Elliptic Curve Cryptography (ECC), and Diffie‑Hellman. By modeling realistic quantum hardware parameters—qubit count, gate fidelity, and error‑correction overhead—the paper projects that a fault‑tolerant quantum computer with roughly 4,000 logical qubits could break a 2048‑bit RSA key within seconds. The authors also review the current state of post‑quantum cryptography (PQC) candidates, comparing lattice‑based, code‑based, and multivariate schemes in terms of security proofs, performance, and standardization progress. This analysis underscores the inevitability of a large‑scale migration from classical public‑key infrastructures to quantum‑resistant alternatives.
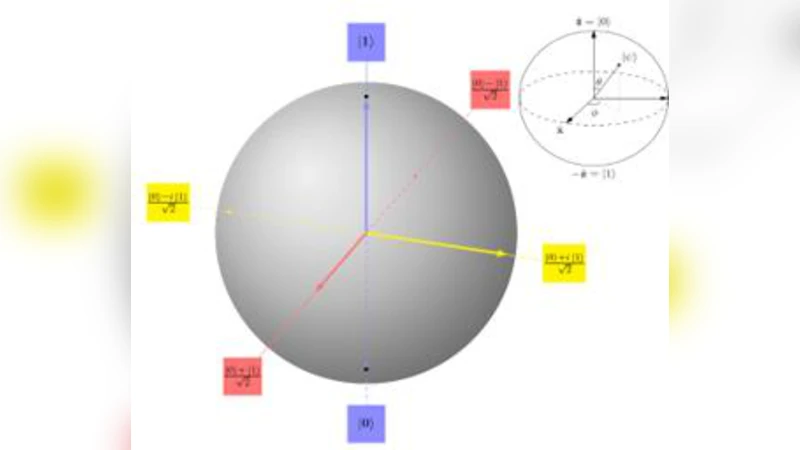
The second section shifts to quantum cryptography, concentrating on quantum key distribution (QKD). It details a collaborative effort between the University of Cambridge and a Toshiba division that implemented a fiber‑optic BB84‑derived protocol using 1550 nm lasers. Experimental results demonstrate secret‑key rates of about 1 Mbps over 200 km with quantum bit error rates (QBER) well below the 11 % security threshold. The paper explains the system’s architecture—phase modulators, interferometric receivers, and decoy‑state techniques—and discusses the security proof that relies on true randomness generated by quantum processes. Nevertheless, the authors identify practical vulnerabilities such as photon loss, detector dark counts, and finite‑size statistical effects, recommending robust error‑correction and privacy‑amplification procedures to mitigate them.
The third part presents a critical analysis of an attack on energy‑time entangled QKD demonstrated by Swedish researchers. By employing ultra‑high‑resolution timing and spectroscopic measurements, the attackers exploit non‑linearities in the receiver’s measurement apparatus, effectively correlating timing and energy errors to extract approximately 5 % of the secret key. This finding challenges the conventional assumption of independent, identically distributed errors in QKD security models. The authors propose countermeasures, including rigorous calibration of detection hardware, insertion of random timing delays, and tightening of the ε‑security parameter in composable security proofs.
The fourth section revisits classical hardware security by describing an Israeli side‑channel attack that uses a parabolic‑curve microphone array to capture minute acoustic vibrations emitted by a computer’s internal components. The technique proved especially effective against low‑power laptops and wireless peripherals, achieving up to 80 % success in reconstructing keystrokes—surpassing many electromagnetic‑emission attacks. The paper documents the subsequent mitigation steps: firmware updates that limit microphone sensitivity, hardware‑level acoustic shielding, and software encryption of input data before it reaches the operating system.
In its conclusion, the paper synthesizes these findings to argue that quantum technologies introduce both new defensive tools and novel attack vectors. While quantum computers threaten the confidentiality of current public‑key cryptosystems, quantum‑based key distribution offers a theoretically unconditional security guarantee—provided that implementation flaws and measurement imperfections are rigorously addressed. Moreover, the persistence of physical side‑channel threats in classical devices highlights the need for a layered security approach that spans hardware design, firmware integrity, and operating‑system policies. The authors outline future research directions, including real‑time error correction for long‑distance QKD, AI‑driven anomaly detection for side‑channel monitoring, and accelerated standardization of post‑quantum algorithms to ensure a smooth transition before large‑scale quantum computers become operational.
Comments & Academic Discussion
Loading comments...
Leave a Comment