Tight exponential analysis of universally composable privacy amplification and its applications
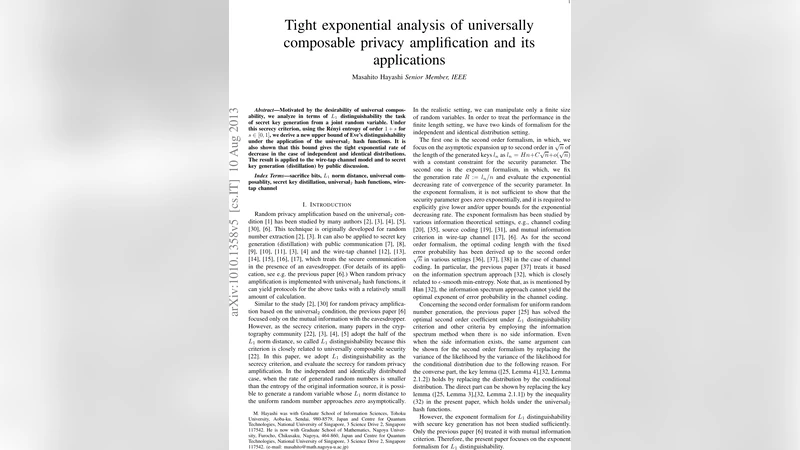
Motivated by the desirability of universal composability, we analyze in terms of L_1 distinguishability the task of secret key generation from a joint random variable. Under this secrecy criterion, using the Renyi entropy of order 1+s for s in [0,1, we derive a new upper bound of Eve’s distinguishability under the application of the universal2 hash functions. It is also shown that this bound gives the tight exponential rate of decrease in the case of independent and identical distributions. The result is applied to the wire-tap channel model and to secret key generation (distillation) by public discussion.
💡 Research Summary
The paper addresses the problem of secret‑key generation under the universally composable (UC) security framework, where the adversary’s advantage is measured by the L₁‑distance (total variation) between the joint distribution of the key and the eavesdropper’s side‑information and the ideal product of a uniform key and the eavesdropper’s marginal. Let (X,E) denote the joint random variable observed by the legitimate parties and the eavesdropper, respectively, and let F be a universal₂ hash function that maps X to a key K of length ℓ bits. The authors introduce a bound that depends on the conditional Rényi entropy of order 1 + s, H₁₊ₛ(X|E), with s∈
Comments & Academic Discussion
Loading comments...
Leave a Comment