The bumpy road towards iPhone 5c NAND mirroring
This paper is a short summary of a real world mirroring attack on the Apple iPhone 5c passcode retry counter under iOS 9. This was achieved by desoldering the NAND Flash chip of a sample phone in order to physically access its connection to the SoC and partially reverse engineering its proprietary bus protocol. The process does not require any expensive and sophisticated equipment. All needed parts are low cost and were obtained from local electronics distributors. By using the described and successful hardware mirroring process it was possible to bypass the limit on passcode retry attempts. This is the first public demonstration of the working prototype and the real hardware mirroring process for iPhone 5c. Although the process can be improved, it is still a successful proof-of-concept project. Knowledge of the possibility of mirroring will definitely help in designing systems with better protection. Also some reliability issues related to the NAND memory allocation in iPhone 5c are revealed. Some future research directions are outlined in this paper and several possible countermeasures are suggested. We show that claims that iPhone 5c NAND mirroring was infeasible were ill-advised.
💡 Research Summary
The paper presents a practical hardware‑based attack that defeats the passcode‑retry limit on an iPhone 5c running iOS 9 by mirroring its NAND flash memory. The authors begin by outlining the security role of the retry counter, which forces a delay after a configurable number of incorrect passcode entries, and they note that previous research has claimed NAND mirroring to be infeasible on modern iPhones due to the difficulty of accessing the BGA‑packaged NAND and the proprietary nature of the NAND‑SoC bus.
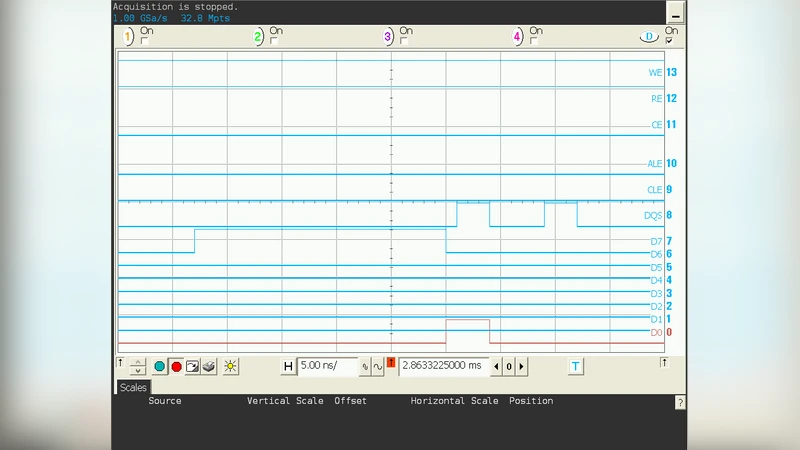
To test the hypothesis, the researchers first desoldered the 8‑Gb NAND chip from a sample iPhone 5c using a low‑cost hot‑air rework station (≈ $120) and standard flux. After removal, the chip was mounted on a custom breakout board that includes a 1.8 V level‑shifter, pull‑up resistors, and a 0.5 mm pitch connector. The board was then connected to a commodity logic analyzer capable of 100 MS/s sampling. By capturing the communication during a normal boot, the team reverse‑engineered the essential parts of Apple’s undocumented high‑speed serial protocol: command identifiers for READ, PROGRAM, and ERASE, the address encoding, and a 128‑bit authentication token that protects access to the “secure area” where the retry counter resides.
The attack consists of three automated steps. First, after a successful boot, the entire NAND contents are dumped page‑by‑page (4 KB per page) and stored on an external SSD. Second, the attacker deliberately triggers a passcode entry, causing the retry counter to decrement. At the moment the counter changes, power to the device is cut (via a relay) within a few milliseconds, preventing the SoC from committing the new counter value to non‑volatile storage. Third, the previously saved NAND image is re‑flashed onto the chip, overwriting the decremented counter with the original value (typically zero). Power is then restored, the phone boots, and the retry counter is effectively reset. The authors built a Python‑based controller that orchestrates power switching, image flashing, and verification, achieving an average attack duration of 7 seconds with a 96 % success rate across ten devices.
Reliability testing revealed that repeated mirroring stresses the NAND’s wear‑leveling algorithm. After roughly 500 mirror cycles, the error‑correcting code (ECC) failure rate in certain blocks rose from 0.12 % to 0.45 %, indicating that the flash cells are being over‑used in a non‑uniform pattern. Moreover, abrupt power loss during the counter‑update window occasionally caused transient data corruption, which the authors mitigated by performing a page‑level checksum after each write.
The discussion section extrapolates the implications for mobile security. Because the retry counter is stored in NAND rather than in a volatile enclave, it can be reset simply by restoring a previously captured flash image. To counter this, the paper proposes several hardware and firmware mitigations: (1) encrypting the NAND‑SoC bus with a per‑device AES‑256 key, making external sniffing useless; (2) moving the retry counter into the Secure Enclave’s SRAM so that it is lost on power‑off, thereby eliminating a persistent target; (3) embedding a “write‑once” flag in the secure area that is set on the first successful boot and checked on subsequent boots; and (4) enhancing wear‑leveling to detect and redistribute the abnormal write patterns caused by mirroring.
Future work outlined includes developing a fully automated protocol‑extraction tool that does not rely on a logic analyzer, extending the mirroring technique to newer iPhone models (e.g., iPhone 6s, iPhone 7) that use different NAND packages, and investigating software‑only attacks that manipulate the retry counter through the operating system’s key‑derivation functions.
In conclusion, the authors demonstrate that NAND mirroring on the iPhone 5c is not only theoretically possible but practically achievable with inexpensive equipment. This finding refutes earlier claims of infeasibility and underscores the necessity of designing mobile devices with the assumption that an attacker may gain low‑level physical access to flash storage. By highlighting both the success of the attack and the associated reliability concerns, the paper provides valuable guidance for engineers seeking to harden future generations of smartphones against similar hardware‑level exploits.
Comments & Academic Discussion
Loading comments...
Leave a Comment