dr0wned - Cyber-Physical Attack with Additive Manufacturing
Additive manufacturing (AM), or 3D printing, is an emerging manufacturing technology that is expected to have far-reaching socioeconomic, environmental, and geopolitical implications. As use of this technology increases, it will become more common to produce functional parts, including components for safety-critical systems. AM’s dependence on computerization raises the concern that the manufactured part’s quality can be compromised by sabotage. This paper demonstrates the validity of this concern, as we present the very first full chain of attack involving AM, beginning with a cyber attack aimed at compromising a benign AM component, continuing with malicious modification of a manufactured object’s blueprint, leading to the sabotage of the manufactured functional part, and resulting in the physical destruction of a cyber-physical system that employs this part. The contributions of this paper are as follows. We propose a systematic approach to identify opportunities for an attack involving AM that enables an adversary to achieve his/her goals. Then we propose a methodology to assess the level of difficulty of an attack, thus enabling differentiation between possible attack chains. Finally, to demonstrate the experimental proof for the entire attack chain, we sabotage the 3D printed propeller of a quadcopter UAV, causing the quadcopter to literally fall from the sky.
💡 Research Summary
The paper “dr0wned – Cyber‑Physical Attack with Additive Manufacturing” presents the first complete, end‑to‑end demonstration of a cyber‑physical attack that exploits the entire additive manufacturing (AM) workflow to sabotage a functional component and cause a physical failure of a cyber‑physical system. The authors begin by outlining the growing reliance on AM for safety‑critical parts in sectors such as aerospace, automotive, and medical devices, and they argue that the tight coupling of digital design data with physical production creates a unique attack surface.
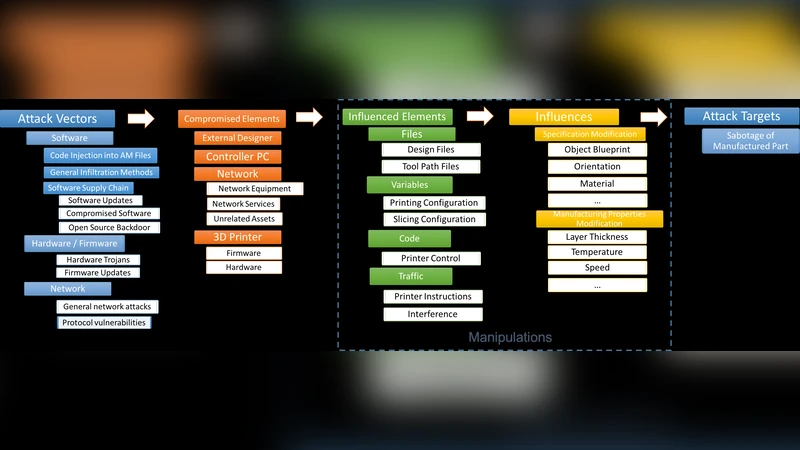
A systematic “attack‑opportunity identification framework” is introduced, mapping every stage of the AM pipeline—CAD modeling, file export (STL/OBJ), slicing, G‑code generation, printer firmware, networked control interfaces, and post‑processing—to potential vulnerabilities. Building on this framework, the authors propose a three‑dimensional difficulty‑assessment methodology that scores each possible attack vector on (1) accessibility (how easily an adversary can reach the target), (2) expertise required (technical knowledge and tools needed), and (3) detectability (likelihood of being discovered by existing monitoring or quality‑control processes). This quantitative model enables the ranking of attack chains and highlights the stages where defensive investment yields the greatest risk reduction.
To validate the concepts, the researchers construct a full‑chain attack against a quadcopter UAV. First, they gain foothold on the printer’s management server via a phishing email that delivers a remote‑code‑execution payload. Once inside, they locate the benign STL file of a propeller, modify it by reducing the central blade thickness by roughly 30 % and inserting subtle internal voids that act as stress concentrators, and then re‑upload the altered file. The compromised G‑code is sent to an off‑the‑shelf FDM printer, which produces a propeller that looks visually identical to the original and passes basic dimensional checks.
During flight tests, the altered propeller exhibits rapid vibration and catastrophic failure within two seconds of take‑off, causing the UAV to fall from the sky. High‑speed video and accelerometer data confirm that the failure originates from the engineered structural weakness, not from material defects or external damage. Importantly, conventional inspection methods (visual inspection, simple dimensional measurement) failed to detect the sabotage, demonstrating a blind spot in current AM quality‑assurance practices.
The authors discuss the broader implications of their findings. They argue that AM‑based supply chains in critical infrastructure must adopt multi‑layered defenses, including cryptographic signing of design files, blockchain‑based provenance tracking, hardened printer firmware, encrypted communication channels, and real‑time monitoring of printing parameters (e.g., layer‑by‑layer temperature and extrusion force). The difficulty‑assessment model is used to prioritize these controls, showing that protecting the printer control interface and post‑processing stages offers the highest payoff.
In conclusion, the paper provides concrete evidence that a cyber adversary can manipulate digital manufacturing data to produce physically compromised parts, thereby turning a purely cyber intrusion into a tangible safety hazard. The work calls for the integration of AM‑specific threat models into existing cybersecurity frameworks and outlines future research directions such as automated integrity verification of STL/G‑code, standardized secure‑by‑design printer protocols, and the deployment of in‑situ sensors capable of detecting anomalous mechanical properties during the build process.
Comments & Academic Discussion
Loading comments...
Leave a Comment