USBee: Air-Gap Covert-Channel via Electromagnetic Emission from USB
In recent years researchers have demonstrated how attackers could use USB connectors implanted with RF transmitters to exfiltrate data from secure, and even air-gapped, computers (e.g., COTTONMOUTH in the leaked NSA ANT catalog). Such methods require a hardware modification of the USB plug or device, in which a dedicated RF transmitter is embedded. In this paper we present USBee, a software that can utilize an unmodified USB device connected to a computer as a RF transmitter. We demonstrate how a software can intentionally generate controlled electromagnetic emissions from the data bus of a USB connector. We also show that the emitted RF signals can be controlled and modulated with arbitrary binary data. We implement a prototype of USBee, and discuss its design and implementation details including signal generation and modulation. We evaluate the transmitter by building a receiver and demodulator using GNU Radio. Our evaluation shows that USBee can be used for transmitting binary data to a nearby receiver at a bandwidth of 20 to 80 BPS (bytes per second).
💡 Research Summary
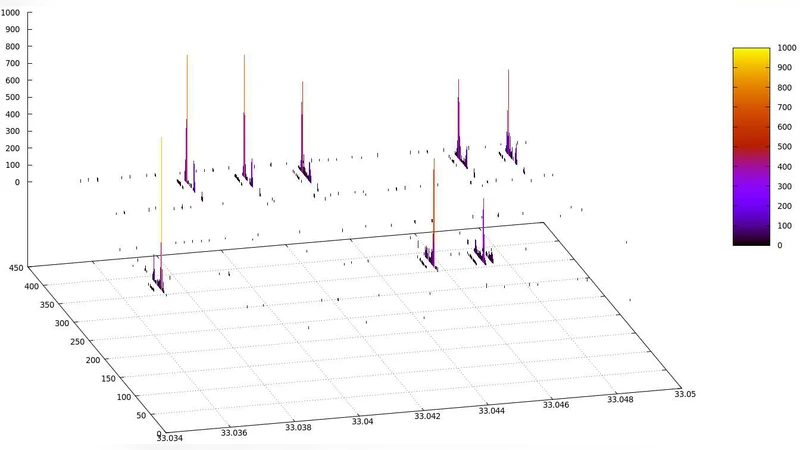
The paper introduces “USBee,” a novel covert‑channel that exploits electromagnetic (EM) emissions from an unmodified USB device to exfiltrate data from air‑gapped systems. Unlike prior work that embeds dedicated RF transmitters into USB plugs (e.g., the COTTONMOUTH device), USBee requires only software running on a compromised host. The authors first analyze the electrical characteristics of USB 2.0/3.0: high‑speed differential signaling on the D+ and D‑ lines toggles between 0 V and 3.3 V with sub‑microsecond rise times, inevitably generating unintended radiated emissions across a wide frequency spectrum. By deliberately crafting USB control transfers with precise timing, the software can amplify specific spectral components (e.g., around 240 MHz or 480 MHz) and use on‑off keying (OOK) to modulate arbitrary binary data onto those emissions.
Implementation details: the transmitter is built on top of libusb, issuing a continuous stream of short control packets. A logical “0” corresponds to a period of no voltage transition (idle), while a “1” forces a rapid voltage swing, thereby creating a burst of EM energy. The inter‑packet interval and packet length are tuned to target a desired carrier frequency; the resulting carrier is a narrowband component superimposed on the broadband USB noise. The authors achieve data rates between 20 and 80 bytes per second (BPS) depending on the chosen timing parameters.
For reception, the authors employ a low‑cost software‑defined radio (SDR) front‑end and a GNU Radio flowgraph. The SDR is set to the carrier frequency, filtered, and passed through an energy detector that demodulates the OOK signal. Experiments conducted in a typical office environment show reliable reception at distances up to 1 m with bit‑error rates below 0.5 %. Shielded enclosures or metal cases dramatically reduce the effective range, confirming the reliance on line‑of‑sight radiated energy.
Security implications are significant. Many high‑security environments rely on air‑gap isolation, assuming that the absence of network interfaces prevents data leakage. USBee demonstrates that any system with an active USB port can become a transmitter without any hardware alteration, bypassing traditional physical‑security controls. Existing intrusion‑detection systems (IDS) and EM‑monitoring solutions typically focus on known RF sources or high‑power emissions; the low‑power, intermittent nature of USBee’s signal makes it difficult to detect without dedicated broadband EM surveillance. Moreover, the software can be embedded in malware that runs stealthily in the background, enabling exfiltration of encryption keys, credentials, or small data fragments.
The paper also discusses limitations. The achievable bandwidth (20–80 BPS) is modest, restricting the channel to small payloads. The radiated power is low, so effective range is limited to a few meters and is highly susceptible to shielding. Persistent transmission patterns could be identified by spectrum analysis, so an attacker would need to randomize timing or blend malicious traffic with legitimate USB activity to improve stealth.
In the discussion, the authors propose countermeasures: (1) physical disconnection or power‑blocking of unused USB ports, (2) EM shielding of critical equipment, (3) firmware or OS‑level monitoring for abnormal high‑frequency USB control transfers, and (4) continuous EM spectrum monitoring in the relevant frequency bands. They argue that a layered defense—combining physical, hardware, and software controls—is necessary to mitigate this new class of software‑only EM covert channels.
In conclusion, USBee expands the threat landscape by showing that software alone can turn a standard USB interface into a controllable RF transmitter, enabling covert data exfiltration from air‑gapped machines. The work underscores the need for renewed attention to unintended EM emissions in secure system design and motivates future research into higher‑throughput EM covert channels and robust detection mechanisms.
Comments & Academic Discussion
Loading comments...
Leave a Comment