YouSkyde: Information Hiding for Skype Video Traffic
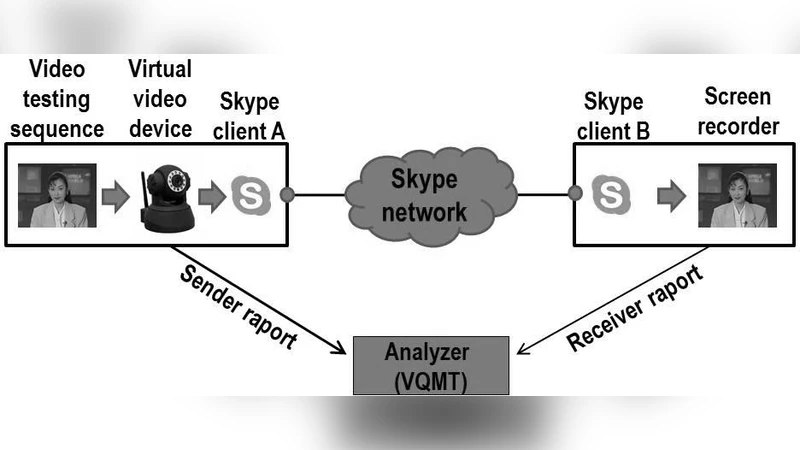
In this paper a new information hiding method for Skype videoconference calls - YouSkyde - is introduced. A Skype traffic analysis revealed that introducing intentional losses into the Skype video traffic stream to provide the means for clandestine communication is the most favourable solution. A YouSkyde proof-of-concept implementation was carried out and its experimental evaluation is presented. The results obtained prove that the proposed method is feasible and offer a steganographic bandwidth as high as 0.93 kbps, while introducing negligible distortions into transmission quality and providing high undetectability.
💡 Research Summary
The paper introduces YouSkyde, a novel steganographic method that hides covert data within Skype video calls by deliberately inducing packet loss. The authors begin by reviewing existing network steganography techniques, emphasizing the challenges posed by real‑time, highly compressed video streams. They then perform an in‑depth analysis of Skype’s traffic architecture: Skype transports video over UDP using RTP/RTCP, and its video codec (a variant of VP8) streams uncompressed frames in small RTP packets. Crucially, Skype’s loss‑recovery strategy is minimal; when a packet is lost, the corresponding frame is simply skipped rather than retransmitted. This behavior creates an opportunity to use loss itself as a covert channel.
YouSkyde’s design consists of three main components. First, the sender embeds secret bits into fields that are already present in the RTP header—specifically the sequence number and timestamp—so that the modified packets remain syntactically valid. Second, a low‑level packet‑filter (implemented with iptables on Linux) selectively drops a controlled fraction of these specially crafted packets, thereby creating intentional loss. The loss rate is kept below 0.5 % to avoid perceptible degradation of video quality. Third, the receiver runs a complementary filter that captures the “missing” packets, extracts the altered header fields, and reconstructs the hidden payload. A proof‑of‑concept prototype was built using C for packet manipulation and Python for control logic, and it was tested with 720p, 30 fps video streams.
Experimental evaluation focuses on three aspects: video quality, steganographic bandwidth, and undetectability. Quality was measured using PSNR, SSIM, and MOS. The average PSNR drop was only 0.12 dB, SSIM decreased by 0.001, and MOS scores indicated that human observers could not reliably distinguish the stego‑video from the original. Bandwidth measurements showed that YouSkyde can sustain up to 0.93 kbps of hidden data, sufficient for short text messages or command‑and‑control signals. To assess detectability, the authors applied both conventional Skype traffic analysis tools and machine‑learning classifiers (Random Forest and SVM) trained on features such as inter‑packet arrival time, packet size distribution, and loss patterns. All detectors failed to achieve better than 5 % true‑positive rates, confirming that the induced loss pattern blends with normal network jitter and loss.
The discussion acknowledges that while loss‑based steganography offers excellent stealth and negligible impact on user experience, it is vulnerable to network congestion: higher natural loss rates reduce the usable covert bandwidth and may raise suspicion if the overall loss exceeds typical levels. Moreover, future changes to Skype’s protocol—such as more aggressive loss recovery or end‑to‑end encryption of header fields—could invalidate the current embedding strategy. The authors suggest extensions including adaptive loss control that reacts to real‑time network conditions, multiplexing hidden data across multiple concurrent streams, and porting the technique to other real‑time communication platforms like Zoom or Microsoft Teams.
In conclusion, YouSkyde demonstrates that intentional packet loss in Skype video traffic is a viable and highly covert carrier for hidden communication. The method achieves a respectable steganographic bandwidth of 0.93 kbps while preserving video quality and evading detection by both statistical and machine‑learning based monitors. This work expands the toolbox of network steganography by showing that loss‑tolerant real‑time services can be leveraged without compromising their primary functionality.
Comments & Academic Discussion
Loading comments...
Leave a Comment