The feasibility of launching physical layer attacks in visible light communication networks
One of the areas in which wireless networks based on visible light communication (VLC) are considered superior to traditional radio-based communication is security. The common slogan summarizing VLC security features is: WYSIWYS - “What You See Is What You Send”. However, especially in the case of infrastructure downlink communication, security with respect to data snooping, jamming and modification must be carefully provided for. This paper examines the physical layer aspects of VLC networks with respect to possible disruptions caused by rogue transmitters. We present the theoretical system model that we use in simulations to evaluate various rogue transmission scenarios in a typical office environment. We use estimated Bit Error Rate (BER) as a measure of the effectiveness of jamming and rogue data transmission. We find that it is quite easy to disrupt, and in some cases to even hijack legitimate transmission.
💡 Research Summary
The paper investigates the vulnerability of visible‑light communication (VLC) networks to physical‑layer attacks, focusing on the downlink scenario where a ceiling‑mounted LED array serves as the legitimate transmitter. While VLC is often touted for its “What You See Is What You Send” (WYSIWYS) security property—because light does not penetrate walls and is directly observable—the authors argue that the same characteristics can be exploited by an adversary who can place a rogue light source within the illuminated space.
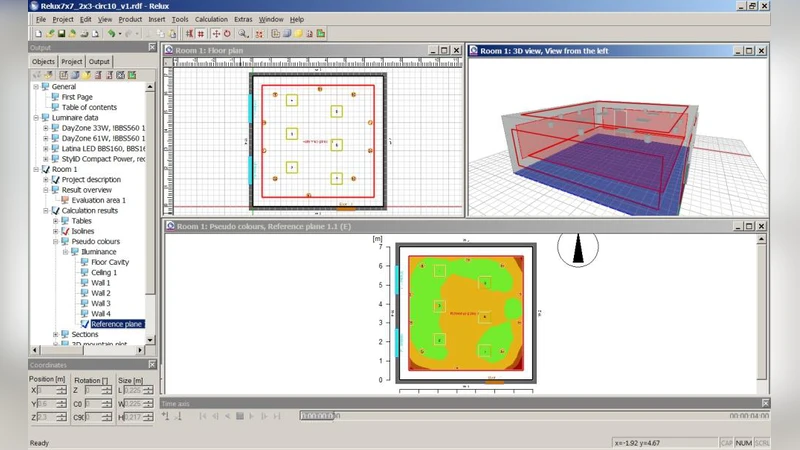
A realistic office environment is modeled in three dimensions. The legitimate transmitter is a standard ceiling LED panel delivering ≥400 lux illumination and using on‑off keying (OOK) at data rates between 100 kbps and 1 Mbps. The receiver is a photodiode with a 60° field of view and a sensitivity of –30 dBm. The rogue transmitter is represented by compact laser diodes or high‑brightness LEDs that can be positioned on desks, shelves, or even handheld. Their optical power is varied from 10 mW to 100 mW, and two operational modes are examined: (1) asynchronous transmission, where the rogue signal is uncoordinated with the legitimate one, and (2) synchronized transmission, where the rogue device matches the carrier frequency, phase, and symbol timing of the legitimate link.
The authors employ a MATLAB‑based optical propagation model combined with Monte‑Carlo bit‑error‑rate (BER) estimation. BER ≤ 10⁻³ is taken as the threshold for acceptable communication quality. The simulation sweeps the rogue power, distance to the receiver, and angular placement, producing a multidimensional map of attack effectiveness.
Key findings include:
- Jamming is trivial – When the rogue source emits comparable optical power to the ceiling LEDs, the superposition of the two light streams reduces the signal‑to‑noise ratio (SNR) at the photodiode, driving BER up to 10⁻¹. Even modest power (≈30 mW) can cause service disruption if the rogue device is within 30 cm of the receiver’s line of sight.
- Data hijacking is feasible – In the synchronized mode, the rogue transmitter can embed counterfeit symbols into the legitimate data stream. The BER remains low during legitimate symbols but spikes dramatically during the injected symbols, prompting error detection and retransmission cycles that effectively give the attacker control over the channel.
- Geometric dependence – The impact is strongest when the rogue source lies near the center of the receiver’s field of view. Placement at right angles to the receiver’s axis benefits from the natural optical shielding of walls and furniture, reducing the attack’s potency.
- Power‑distance trade‑off – A high‑power rogue source can jam from several meters away, whereas a low‑power device must be positioned very close to the receiver. This relationship is quantified in the paper’s contour plots.
To mitigate these threats, the authors propose several physical‑layer defenses: (a) spectral filtering to reject wavelengths not used by the legitimate system; (b) multi‑wavelength division multiplexing (MWDM) so that an attacker would need to replicate multiple channels simultaneously; (c) dynamic modulation schemes (e.g., random phase hopping) that make synchronization difficult; and (d) receiver‑side monitoring of optical spectra and intensity fluctuations to detect anomalous sources in real time. Implementing these measures, however, incurs additional hardware cost, power consumption, and processing overhead, which the authors acknowledge as a design trade‑off.
The conclusion re‑examines the common belief that VLC is inherently more secure than radio‑frequency (RF) wireless. By providing a quantitative analysis of how a simple, low‑cost rogue light source can either jam or hijack a VLC link, the paper demonstrates that security must be addressed at the physical layer, not assumed from the medium’s properties alone. The authors also note limitations: the study relies on simulated environments and does not yet incorporate complex multipath reflections or moving obstacles that occur in real offices. Future work is suggested to validate the findings with experimental testbeds and to explore adaptive countermeasures that can respond to dynamic attack scenarios.
Comments & Academic Discussion
Loading comments...
Leave a Comment