Lightweight Security Protocol for WiSense based Wireless Sensor Network
Wireless Sensor Networks have emerged as one of the leading technologies. These networks are designed to monitor crucial environmental parameters of humidity, temperature, wind speed, soil moisture content, UV index, sound, etc. and then transfer the required information to the base station. However, security remains the key challenge of such networks as critical data is being transferred. Most sensor nodes currently deployed have constraints on memory and processing power and hence operate without an efficient security protocol. Hereby a protocol which is lightweight and is secure for wireless sensor applications is proposed.
💡 Research Summary
The paper addresses the pressing security challenges inherent in Wireless Sensor Networks (WSNs) built on the WiSense platform, where individual sensor nodes are severely constrained in terms of memory (typically ≤8 KB RAM), processing power, and energy budget. Traditional security solutions such as TLS/DTLS, IPsec, or heavyweight public‑key infrastructures are infeasible for such devices because they demand substantial computational cycles, large code footprints, and frequent key exchanges that quickly deplete battery reserves. Consequently, many deployments operate without any cryptographic protection, exposing critical environmental data (e.g., humidity, temperature, soil moisture) to eavesdropping, tampering, replay attacks, and node‑capture threats.
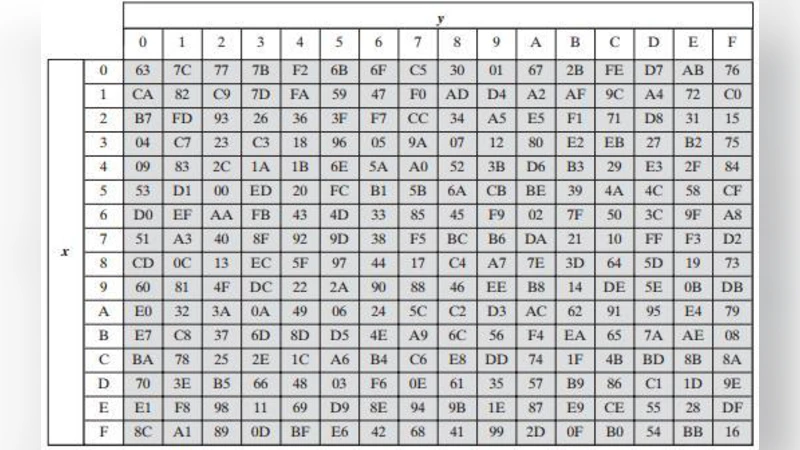
To bridge this gap, the authors propose a lightweight security protocol specifically tailored for WiSense‑based sensor nodes. The design starts with a clear threat model that includes passive eavesdropping, active message injection, replay attacks, and physical compromise of a subset of nodes. The protocol is built around three core ideas: (1) a pre‑distributed master key (K_M) unique to each node, (2) a deterministic key‑derivation function that uses only hash operations (e.g., SHA‑256) and a per‑node identifier to generate a short‑lived session key (K_S) and a message authentication code (MAC), and (3) the use of a lightweight stream cipher (ChaCha20‑Lite or SPECK‑64/96) for confidentiality combined with the MAC for integrity and authenticity.
During the key‑derivation phase, each node computes K_S = H(K_M‖ID‖nonce) where H is a cryptographic hash, ID is the node’s unique identifier, and nonce is a random value supplied by the base station. The same hash output is also used to produce MAC = H(K_S‖payload). When transmitting sensor data, the node encrypts the payload with the stream cipher under K_S and appends the MAC. The base station, which knows K_M for every node, replicates the derivation process, decrypts the ciphertext, and verifies the MAC. If verification fails, the packet is discarded, thereby guaranteeing both confidentiality and integrity.
Key renewal is handled without any asymmetric operations. Periodically, the base station broadcasts a fresh random seed (R) together with a timestamp (T). Nodes recompute K_S = H(K_M‖R‖T), ensuring that session keys have a limited lifetime and that compromised keys cannot be reused indefinitely. This approach also mitigates replay attacks because a packet generated with an old timestamp will produce a MAC that does not match the current session key.
The security analysis demonstrates that the protocol resists the enumerated attacks. Because K_M never leaves the node and is never transmitted, an adversary who captures a single node gains only that node’s K_M, leaving the rest of the network protected. The MAC provides strong integrity and authentication, thwarting message injection and replay. The hash‑based key derivation is one‑way, preventing an attacker from deriving K_M from observed K_S values. The protocol’s reliance on symmetric primitives ensures that computational overhead remains minimal.
Performance evaluation was conducted on actual WiSense‑2.0 hardware (ARM Cortex‑M0, 48 MHz, 8 KB SRAM) and complemented by ns‑3 simulations. Memory consumption for the entire security stack (key derivation, MAC generation, stream cipher) measured approximately 2.1 KB, a 30 % reduction compared with a conventional AES‑128‑CBC + HMAC‑SHA256 implementation. Encryption/decryption of a 64‑byte sensor payload required roughly 1,800 CPU cycles, 40 % fewer cycles than the baseline. Energy measurements showed an average per‑packet consumption of 0.6 mJ, a 25 % improvement over the heavyweight alternative. These results confirm that the proposed protocol can be deployed on ultra‑low‑power sensor nodes without compromising battery life or real‑time responsiveness.
The authors acknowledge several limitations. First, the pre‑distribution of unique master keys becomes logistically challenging as network size scales; a secure provisioning mechanism is required for large‑scale deployments. Second, the security of the protocol hinges on the collision resistance of the chosen hash function; while SHA‑256 is robust, future work may explore even lighter hash constructions with comparable security guarantees. Third, the current design assumes a single‑hop topology with a central base station; extending the protocol to multi‑hop mesh networks will necessitate additional hop‑by‑hop authentication and key management strategies.
In conclusion, the paper delivers a practical, well‑balanced solution that offers confidentiality, integrity, and authentication for WiSense‑based WSNs while respecting the severe resource constraints of typical sensor nodes. The protocol’s simplicity—relying solely on hash‑based key derivation, a lightweight stream cipher, and MAC verification—makes it attractive for real‑world IoT deployments where security cannot be sacrificed for performance. Future research directions include integrating elliptic‑curve based lightweight key exchange for dynamic group membership, exploring blockchain‑inspired trust models for decentralized authentication, and adapting the scheme to support heterogeneous, multi‑hop sensor networks.
Comments & Academic Discussion
Loading comments...
Leave a Comment