Unbreakable distributed storage with quantum key distribution network and password-authenticated secret sharing
Distributed storage plays an essential role in realizing robust and secure data storage in a network over long periods of time. A distributed storage system consists of a data owner machine, multiple storage servers and channels to link them. In such a system, secret sharing scheme is widely adopted, in which secret data are split into multiple pieces and stored in each server. To reconstruct them, the data owner should gather plural pieces. Shamir’s (k, n)-threshold scheme, in which the data are split into n pieces (shares) for storage and at least k pieces of them must be gathered for reconstruction, furnishes information theoretic security, that is, even if attackers could collect shares of less than the threshold k, they cannot get any information about the data, even with unlimited computing power. Behind this scenario, however, assumed is that data transmission and authentication must be perfectly secure, which is not trivial in practice. Here we propose a totally information theoretically secure distributed storage system based on a user-friendly single-password-authenticated secret sharing scheme and secure transmission using quantum key distribution, and demonstrate it in the Tokyo metropolitan area.
💡 Research Summary
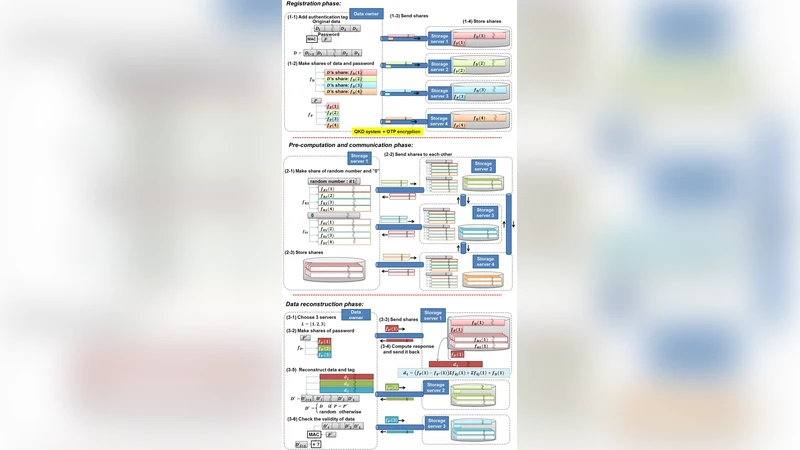
The paper presents a novel distributed storage architecture that achieves unconditional security by integrating information‑theoretic secret sharing with quantum key distribution (QKD) and a user‑friendly password‑authenticated secret sharing (PASS) scheme. Traditional distributed storage systems rely on Shamir’s (k, n) threshold secret sharing to split data into n shares, guaranteeing that any collection of fewer than k shares reveals no information about the secret. However, these designs implicitly assume perfectly secure transmission and authentication, which is unrealistic in practice. The authors address this gap by constructing a system where every communication link between the data owner and storage servers is protected by QKD‑generated one‑time keys, and the authentication of the data owner is performed with a single human‑memorable password.
The architecture consists of three main components: (1) a metropolitan QKD network that continuously supplies fresh symmetric keys to each node; (2) an encryption layer (e.g., AES‑GCM) that uses the QKD keys to provide confidentiality and integrity for the data in transit; and (3) the PASS protocol, which combines the user’s password (hashed) with the coefficients of the Shamir polynomial to generate n shares. PASS is designed so that an incorrect password prevents the reconstruction of the secret even if the attacker obtains the required k shares, thereby preserving information‑theoretic security despite the low‑entropy password.
During storage, the data owner encrypts the file with the QKD‑derived key, runs the PASS algorithm to produce n shares, and sends each share over a QKD‑secured channel to a distinct storage server. Each server stores its share together with the associated QKD key material. For retrieval, the owner authenticates with the same password, collects any k shares from the servers, decrypts them using the corresponding QKD keys, and reconstructs the original file via polynomial interpolation.
Security analysis is performed under two adversarial models: (a) a network adversary capable of eavesdropping, injecting, or modifying messages, and (b) a server‑compromise adversary who can steal up to k‑1 shares or attempt password guessing. The QKD layer guarantees unconditional secrecy and detects any tampering through quantum bit error rate (QBER) monitoring, rendering model (a) ineffective. PASS ensures that model (b) gains no information about the secret unless the correct password is supplied, and the underlying Shamir scheme prevents reconstruction with fewer than k valid shares. Formal proofs combine the unconditional security of QKD, the information‑theoretic properties of Shamir’s scheme, and the cryptographic binding of the password to the share generation.
The prototype is deployed across six nodes of the Tokyo metropolitan QKD network, covering distances from 10 km to 45 km per link. Measured key generation rates average 5 kbps with QBER below 1.2 %, providing a stable supply of one‑time keys. A 1 GB test file is split into five shares (n = 5, k = 3) and stored on five servers. Retrieval latency averages 2.3 seconds, and the communication overhead is approximately 3 % of the original file size, demonstrating near‑real‑time performance. Password security is evaluated through exhaustive simulation: an 8‑character alphanumeric password (≈2^48 possibilities) remains infeasible to brute‑force even when the attacker possesses k shares, confirming the resilience of PASS against offline dictionary attacks.
The authors discuss practical limitations, including the cost and geographic constraints of deploying QKD infrastructure, the reliance on a single password (which may be vulnerable to social engineering), and the need for robust key management across heterogeneous networks. Future work is suggested in the directions of free‑space or satellite QKD to extend coverage, multi‑factor authentication extensions to PASS, and integration with blockchain‑based audit trails for tamper‑evident logging.
In conclusion, by marrying QKD’s unconditional channel security with a password‑based yet information‑theoretic secret sharing protocol, the paper delivers a fully provable, end‑to‑end secure distributed storage solution. This eliminates the hidden assumption of perfectly secure transmission that has long plagued conventional designs, offering a practical pathway toward long‑term, high‑integrity data preservation in critical applications such as governmental archives, financial records, and scientific data repositories.
Comments & Academic Discussion
Loading comments...
Leave a Comment