Fansmitter: Acoustic Data Exfiltration from (Speakerless) Air-Gapped Computers
Because computers may contain or interact with sensitive information, they are often air-gapped and in this way kept isolated and disconnected from the Internet. In recent years the ability of malware to communicate over an air-gap by transmitting sonic and ultrasonic signals from a computer speaker to a nearby receiver has been shown. In order to eliminate such acoustic channels, current best practice recommends the elimination of speakers (internal or external) in secure computers, thereby creating a so-called ‘audio-gap’. In this paper, we present Fansmitter, a malware that can acoustically exfiltrate data from air-gapped computers, even when audio hardware and speakers are not present. Our method utilizes the noise emitted from the CPU and chassis fans which are present in virtually every computer today. We show that a software can regulate the internal fans’ speed in order to control the acoustic waveform emitted from a computer. Binary data can be modulated and transmitted over these audio signals to a remote microphone (e.g., on a nearby mobile phone). We present Fansmitter’s design considerations, including acoustic signature analysis, data modulation, and data transmission. We also evaluate the acoustic channel, present our results, and discuss countermeasures. Using our method we successfully transmitted data from air-gapped computer without audio hardware, to a smartphone receiver in the same room. We demonstrated the effective transmission of encryption keys and passwords from a distance of zero to eight meters, with bit rate of up to 900 bits/hour. We show that our method can also be used to leak data from different types of IT equipment, embedded systems, and IoT devices that have no audio hardware, but contain fans of various types and sizes.
💡 Research Summary
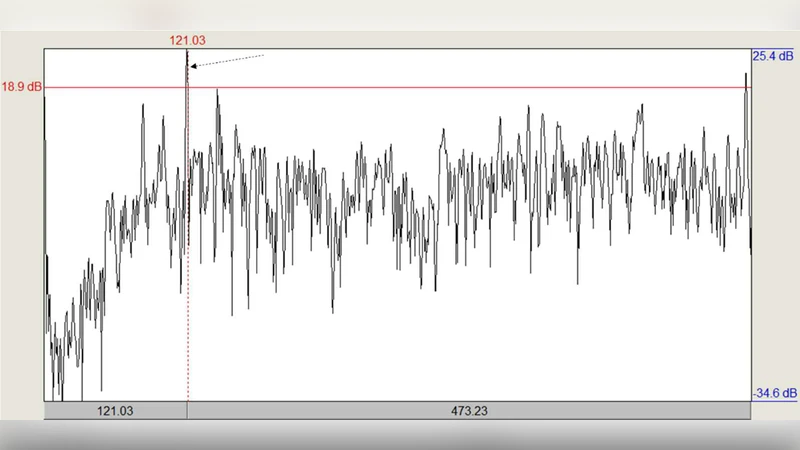
The paper introduces Fansmitter, a novel malware framework that enables acoustic data exfiltration from air‑gapped computers even when they have no speakers or any other audio hardware. The authors observe that virtually every modern computer contains one or more cooling fans (CPU, power‑supply, chassis) that generate audible and ultrasonic noise as a by‑product of their rotation. By precisely controlling fan speed through standard operating‑system APIs or BIOS/UEFI interfaces, malicious code can synthesize acoustic waveforms with controllable frequency, amplitude, and timing. These waveforms are then used to modulate binary data, which can be captured by a nearby microphone—typically a smartphone placed in the same room.
Three modulation schemes are described. The simplest is On‑Off Keying (OOK), where the fan is switched between a high‑speed “1” state and a low‑speed “0” state. Frequency‑Shift Keying (FSK) maps two distinct rotation speeds to two separate carrier frequencies, allowing more robust detection in noisy environments. Finally, multi‑level Pulse‑Width Modulation (PWM) varies the fan speed across several discrete levels, encoding multiple bits per symbol. The authors also discuss synchronization preambles, error‑detecting CRC, and lightweight forward error correction (e.g., Hamming codes) to improve reliability.
Experimental evaluation was performed on four desktop PCs (Windows 10 and Linux) and two network appliances (router and NAS) equipped with fans of various sizes (80 mm to 140 mm) and speed ranges (≈800–4000 RPM). A smartphone running Android and a USB microphone were used as receivers, sampling at 44.1 kHz. Results show that at a distance of 0 m (direct contact) the system achieved up to 900 bits per hour (≈0.25 bits / s) with a bit‑error‑rate (BER) below 0.5 %. At 8 m the throughput dropped to about 300 bits per hour while keeping BER under 3 %. The transmitted payloads included 128‑bit AES keys, 12‑character passwords, and short text files, demonstrating that sensitive information can be leaked without any audio output device.
From a security perspective, the work invalidates the common “audio‑gap” mitigation that simply removes speakers from high‑security machines. Fan speed control is often exposed through standard power‑management interfaces, and many systems allow unprivileged applications to adjust fan curves via drivers or user‑space utilities. Because fans are essential for thermal management, they cannot be removed, making the acoustic side‑channel difficult to eliminate. The authors propose several counter‑measures: (1) restricting or auditing access to fan‑control APIs, (2) deploying hardware‑level monitoring that flags abnormal fan‑speed oscillations, and (3) implementing sound‑based intrusion‑detection systems that analyze ambient noise for the characteristic modulation patterns used by Fansmitter. However, these defenses incur performance overhead and may not be feasible in all environments.
The paper also extends the attack model to embedded and IoT devices that contain fans—such as routers, industrial PLCs, and smart thermostats—showing that the technique is not limited to traditional PCs. The authors suggest future work on simultaneous control of multiple fans to increase bandwidth, exploitation of higher ultrasonic frequencies for better stealth, and machine‑learning classifiers for automated detection of malicious fan‑noise patterns.
In summary, Fansmitter demonstrates a practical, speaker‑less acoustic covert channel that leverages the unavoidable presence of cooling fans. By turning a benign thermal management component into a data‑transmission antenna, the authors expose a new class of side‑channel threats that challenge existing physical‑isolation defenses and call for more comprehensive, hardware‑aware security strategies.
Comments & Academic Discussion
Loading comments...
Leave a Comment