A Conceptual Framework for Accountability in Cloud Computing Service Provision
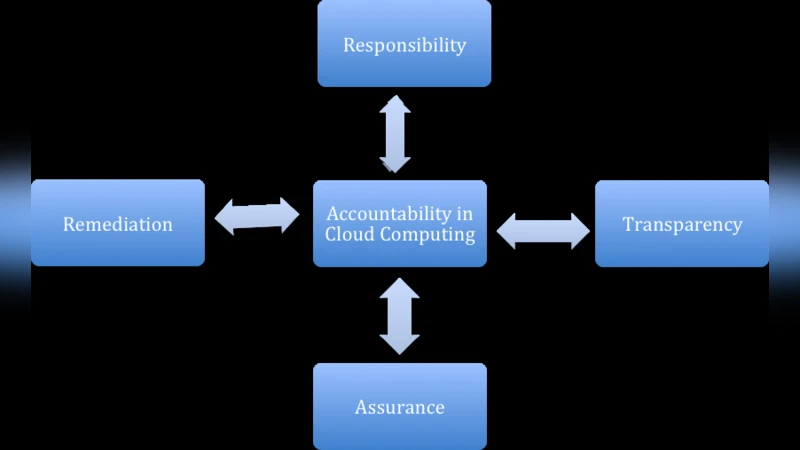
This paper uses a comprehensive review of the academic and professional literature in relation to accountability in the area of cloud computing service provision. It identifies four key conceptual factors that are necessary for an organisation to be considered as accountable. The four factors were found to be: responsibility, assurance, transparency and remediation. A key finding of the paper is that in order to be considered as an accountable cloud service provider, all four factors need to be implemented and be demonstrable by the organisation.
💡 Research Summary
The paper conducts a comprehensive literature review of both academic and professional sources to clarify the concept of accountability in cloud‑computing service provision. By synthesizing definitions, standards, and industry practices, the authors identify four inter‑related conceptual factors that together constitute a complete accountability framework: responsibility, assurance, transparency, and remediation.
Responsibility is defined as the explicit acknowledgment and internalization of contractual, legal, and regulatory obligations. It requires that cloud providers embed these obligations into governance structures, policies, and operational procedures, covering issues such as data sovereignty, access control, service‑level agreements (SLAs), and privacy mandates.
Assurance refers to external validation mechanisms that demonstrate the trustworthiness of the service. The paper highlights the role of independent audits, certifications (e.g., ISO/IEC 27001, SOC 2, CSA STAR), and third‑party assessments in providing objective evidence that the provider’s controls meet recognized standards. Assurance thus bridges the gap between internal responsibility and external stakeholder confidence.
Transparency is the systematic disclosure of service architecture, data flows, logging practices, and incident‑response processes. The authors argue that transparency must be operationalized through regular reports, real‑time dashboards, API‑exposed metadata, and publicly available documentation, enabling customers and regulators to understand how the service functions and to assess risk continuously.
Remediation encompasses the full lifecycle of incident handling: rapid detection, root‑cause analysis, corrective action, and post‑incident verification. The paper stresses that remediation must be documented, auditable, and demonstrably effective, with lessons learned feeding back into governance to prevent recurrence.
Through a meta‑analysis of standards and a case‑study examination of major cloud providers (Amazon Web Services, Microsoft Azure, Google Cloud Platform), the authors find that while responsibility, assurance, and transparency are relatively well‑implemented, remediation practices are often the weakest link. Providers typically disclose high‑level incident‑response policies but lack detailed, verifiable post‑mortem reports and systematic evidence of corrective measures.
The central thesis is that accountability is not a checklist of isolated items; rather, it is a dynamic, interdependent system where the absence of any single factor undermines the entire framework. For example, a provider may have robust responsibility and assurance mechanisms, but without transparent reporting, customers cannot verify that those mechanisms are operating as intended, and any remediation effort becomes opaque. Conversely, strong transparency without assurance leaves stakeholders uncertain about the actual security posture.
Based on these findings, the paper proposes actionable recommendations:
- Holistic Implementation – Organizations must implement all four factors concurrently and ensure each is demonstrably verifiable to external parties.
- Evidence‑Based Remediation – Providers should publish detailed incident analyses, corrective action plans, and verification results, subject to independent audit.
- Continuous Monitoring – Assurance and transparency should be supported by real‑time monitoring and automated reporting to adapt to evolving threat landscapes.
- Dynamic Governance – Accountability should be treated as an ongoing management cycle, with regular reviews, updates to policies, and integration of lessons learned from remediation activities.
In conclusion, the paper argues that a cloud service provider can be considered truly accountable only when responsibility, assurance, transparency, and remediation are fully realized and openly demonstrated. This integrated framework serves as a foundational governance model for safeguarding data, meeting regulatory requirements, and building lasting trust in cloud environments.
Comments & Academic Discussion
Loading comments...
Leave a Comment