Cryptographically secure multiparty evaluation of system reliability
The precise design of a system may be considered a trade secret which should be protected, whilst at the same time component manufacturers are sometimes reluctant to release full test data (perhaps only providing mean time to failure data). In this s…
Authors: Louis J. M. Aslett
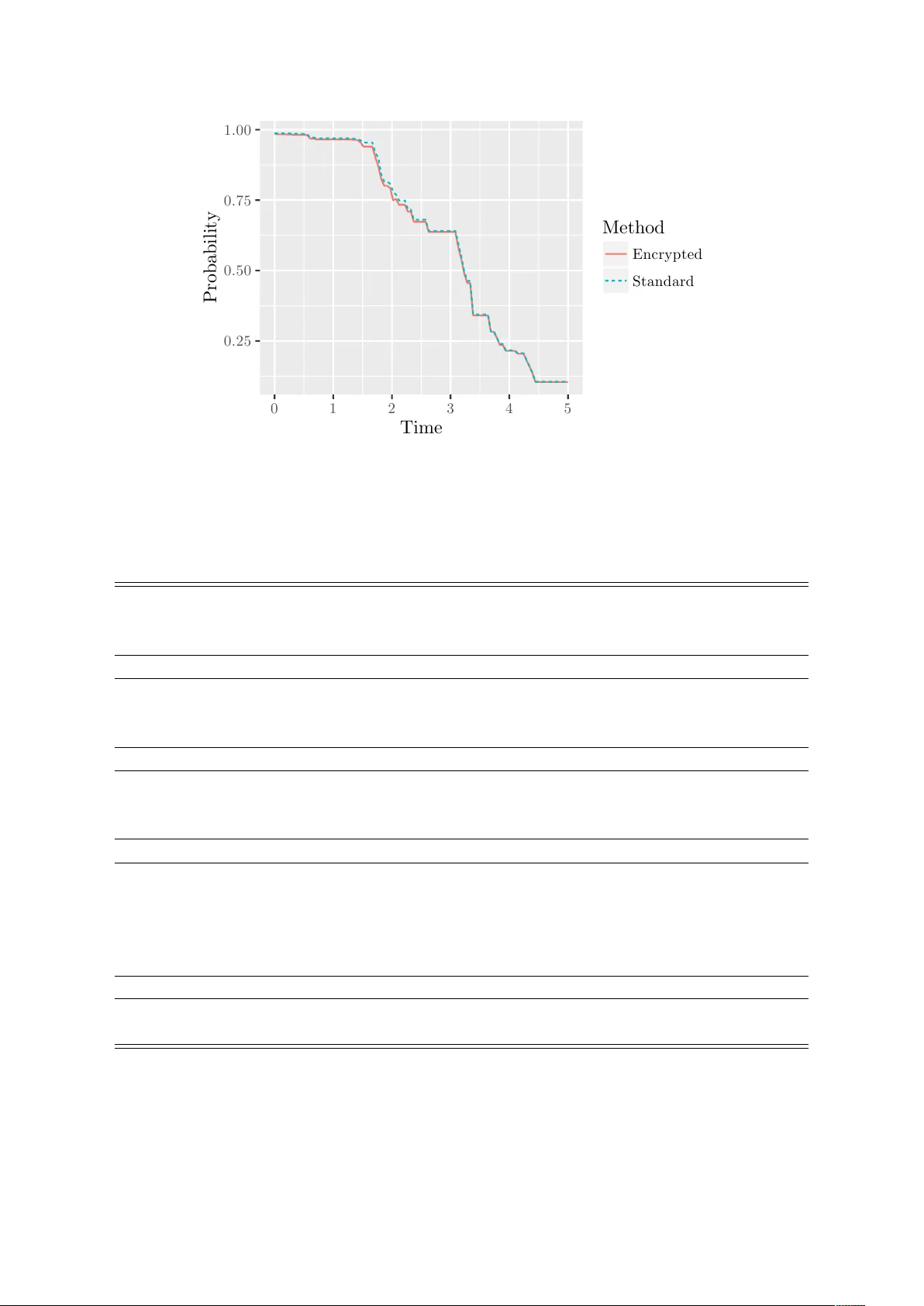
Cryptographically secure m ultipart y ev aluation of system reliabilit y Louis J. M. Aslett Departmen t of Statistics, Univ ersity of Oxford Abstract The precise design of a system ma y b e considered a trade secret which should b e protected, whilst at the same time comp onent man ufacturers are sometimes re- luctan t to release full test data (p erhaps only providing mean time to failure data). In this situation it seems impractical to b oth pro duce an accurate reliability as- sessmen t and satisfy all parties’ priv acy requiremen ts. Ho wev er, we present recent dev elopments in cryptography which, when combined with the recen tly dev elop ed surviv al signature in reliabilit y theory , allo ws almost total priv acy to be maintained in a cryptographically strong manner in precisely this setting. Th us, the system designer do es not ha ve to reveal their trade secret design and the comp onent man- ufacturer can retain comp onen t test data in-house. Keyw ords: homomorphic encryption; priv acy preserving statistics; reliability the- ory . 1 In tro duction A standard part of dev eloping any critical system is a thorough assessmen t of the reliabil- it y characteristics. This in v olves a careful assessmen t of the reliability of the comp onents whic h will comprise the system and then propagation of all the uncertain ty in these estimates through to an assessmen t of the reliabilit y of the whole system. A common imp ediment to the ab ov e best practice is commercial priv acy concerns: the system designer will typically consider the exact design of their system to b e a trade secret, while comp onen t man ufacturers are frequently reluctant to make full test data on their components a v ailable, often preferring to giv e summary statistics suc h as mean time to failure or other similarly sub optimal measures of reliability . Ac hieving a full and frank assessmen t of ov erall system reliability while resp ecting such priv acy concerns app ears to presen t a significant challenge. Sensitiv e data is often kept priv ate b y encrypting it. T raditional metho ds of encryp- tion are primarily in tended for transmission of sensitiv e information and do not allo w an y meaningful computation using the encrypted data without first decrypting it and risk- ing rev ealing ev erything. Ho wev er, recen t developmen ts in the cryptograph y literature (Gen try, 2009) ha ve pro vided metho ds of encryption which allow computation on the encrypted con tent and has b een sho wn to hold substan tial promise in ac hieving priv acy preserving statistical analyses (Graep el et al., 2012; Aslett et al., 2015c). Herein these tec hniques are used to solv e the widespread priv acy problem of relia- bilit y ev aluation in industrial settings where priv acy of test data and system design are 1 commercial requiremen ts. Section 2 pro vides a high-lev el introduction to homomorphic encryption , a voiding any technicalities that are not directly relev an t. Section 3 describ es the surviv al signature and sho ws its imp ortance in this con text as a reliability decomp o- sition which is amenable to encrypted computation. This leads to the priv acy preserving proto col describ ed in Section 4, whic h enables ev aluation of the full surviv al curve of a system without disclosure of component test data or system design. There is a practical example discussed in Section 5 to provide practitioners with a clear demonstration of the practicalit y of the metho d. The paper concludes with a short discussion in Section 6. 2 Homomorphic encryption In this section a high-lev el introduction to homomorphic encryption schemes is pro vided a voiding an y unnecessary tec hnicalities. Later it will b e sho wn that the form of the surviv al signature is v ery sp ecial from the p ersp ectiv e of performing homomorphic com- putations in reliabilit y problems, providing the motiv ation for the priv acy preserving proto col presented in Section 4. 2.1 Standard cryptograph y All encryption schemes are either so-called ‘public’ or ‘secret’ k ey in nature. The proto- col to b e presented in the sequel requires a public key sc heme. A public key encryption sc heme has t wo algorithms Enc ( · , · ) and Dec ( · , · ), whic h perform encryption and decryp- tion resp ectiv ely , together with t w o k eys: the public key , k p , can b e distributed widely and any one ma y use it to encrypt a message; the secret k ey , k s , is required to decrypt an y message encrypted using k p and so k ept priv ate. The principal iden tity is: Dec ( k s , Enc ( k p , m )) = m ∀ m The data to b e encrypted, m , is referred to as the message and after transformation by Enc ( · , · ) is referred to as the ciphertext . Encryption is a common tec hnique for ensuring the priv acy of data, but t ypically once one wishes to p erform an analysis it is necessary to first decrypt and risk exp osing the data. In 1978 Riv est et al. proposed that encryption sc hemes capable of theoretically arbitrary computation on encrypted data ma y b e p ossible, but it was not until 2009 that Gen try (2009) provided the first such scheme. An explosion of adv ances in cryptography ha ve ensued, each enabling a limited amoun t of computation to b e p erformed directly on the encrypted con tent, rendering the correct result up on decryption. 2.2 F ully homomorphic sc hemes Encryption sc hemes are said to b e ful ly homomorphic if they also p ossesses tw o op era- tions, ⊕ and ⊗ , that can b e applied a theoretically arbitrary n umber of times and satisfy: Dec ( k s , Enc ( k p , m 1 ) ⊕ Enc ( k p , m 2 )) = m 1 + m 2 Dec ( k s , Enc ( k p , m 1 ) ⊗ Enc ( k p , m 2 )) = m 1 × m 2 for all m 1 , m 2 . In other w ords, a homomorphic encryption scheme allows computation directly on ciphertexts, whic h will correctly decrypt the result as if it had b een applied to the original messages. 2 Ho wev er there are many constrain ts in practical implemen tation, reviewed in Aslett et al. (2015b). F or the purp oses of this work they may b e synopsised as: 1. T ypically m can only naturally represent binary ( m ∈ GF(2)) or limited in teger ranges ( m ∈ Z /n Z ). 2. Data size after encryption is substan tially inflated, b y orders of magnitude. 3. Computational costs for ⊕ , ⊗ are orders of magnitude higher than standard + , × . 4. Comparisons (= , <, > ) and division are not p ossible under curren t schemes. 5. Implemen tation of curren t schemes necessitate a h ugely computationally exp ensiv e ‘b o otstrap’ op eration (not related to statistical b o otstrapping) whic h m ust b e ap- plied frequently b et w een ⊗ op erations to con trol the noise in the ciphertext. Indeed, b o otstrap op erations are so exp ensive that it is typical to av oid them completely b y constraining the algorithm to a small n umber of successive m ultiplications. In essence then, homomorphic schemes are capable of ev aluating m ultiv ariate p oly- nomials of the ciphertexts. In other words, if f ( m 1 , . . . , m n ) is a multiv ariate p olynomial in m 1 , . . . , m n then a homomorphic scheme ensures Dec k s , g Enc ( k p , m 1 ) , . . . , Enc ( k p , m n ) = f ( m 1 , . . . , m n ) where g ( · ) is the function f ( · ) with + replaced b y ⊕ and × replaced by ⊗ . Hence, any algorithm to b e computed encrypted must b e expressible as a p olynomial function. Accordingly , constrain t 5 abov e implies that the degree of the p olynomial to b e ev al- uated is a crucial quantit y: if the degree is k ept small then b o otstrap might b e av oidable and the algorithm will b e fast. Herein this quan tity is referred to as the multiplic ative depth of the algorithm. In particular, note that the total n umber of m ultiplications is not the issue, rather the num b er of successiv e m ultiplications. The final p oin t to note is that all homomorphic encryption schemes in volv e fixing some parameters b efore generating the public and secret k eys. These parameters influence ho w secure the scheme is and often ha ve other side effects suc h as con trolling the multiplicativ e depth which is p ossible. Often there are theoretical analyses of homomorphic schemes to enable specification of a desired securit y and m ultiplicative depth to then w ork bac kwards to an appropriate parameter c hoice. Despite such restrictions, fully homomorphic encryption is theoretically exciting b e- cause for binary messages + and × corresp ond to logical OR and X OR resp ectiv ely . These t wo logical op erations are sufficient for construction of an y logical circuit and therefore sufficien t for theoretically arbitrary computation. Practical usage of homomorphic sc hemes It is curren tly impractical to encrypt all data as binary and compute the corresp onding logical circuits b ecause the computational burden is to o great (see Aslett et al., 2015b, for a fuller discussion). Herein, an integer enco ding of real v alues is used of a nature similar to (Aslett et al., 2015c). Let y ∈ R , then an enco ding m ∈ Z of y is required which can b e encrypted. Let µ κ : R → Z b e the enco ding function used to represent real v alued data as a message with m = µ κ ( y ) , b 10 κ y e , where b·e denotes rounding to the nearest in teger. Then 3 this transformation, parameterised by κ , preserves κ decimal places of the real v alue y with represen tation in in teger form. y can b e appro ximately reco vered b y µ − 1 κ ( µ κ ( y )) = 10 − κ µ κ ( y ) ≈ y This enco ding w orks w ell for addition and multiplication, since µ − 1 κ µ κ ( y 1 ) + µ κ ( y 2 ) ≈ y 1 + y 2 µ − 1 2 κ µ κ ( y 1 ) µ κ ( y 2 ) ≈ y 1 y 2 (1) Note the precision adjustmen t, 2 κ , required in (1). How ever, care is clearly needed since enco dings with differing precision parameters cannot b e summed without adjustment. The ab o v e discussion makes clear that standard statistical metho ds often cannot b e applied unmo dified on encrypted conten t. Ho w ever, as will b e shown below the form of the surviv al signature is particularly well suited to encrypted reliabilit y analysis. F or further details, the reader is directed to fuller reviews of homomorphic encryption (Gen try, 2010; Aslett et al., 2015b). 3 Encrypted computabilit y and surviv al signatures The surviv al signature was in tro duced by Co olen and Co olen-Maturi (2012) as a general- isation of the system signature (Samaniego, 1985; Ko c har et al., 1999), enabling multiple differen t types of comp onent. This relaxed the restrictive assumption of i.i.d comp onents found in the system signature, whilst retaining the separation of comp onen t lifetime and the effect of system structure on reliability . This separation of comp onen ts and structure is the first critical prop ert y of the surviv al signature which enables the priv acy preserving proto col to b e implemented in the sequel. The structure function (Birn baum et al., 1961) of an M comp onent system is the function φ : { 0 , 1 } M → { 0 , 1 } which maps the binary operational state of the M comp o- nen ts to the op erational state of the whole system. Letting x = ( x 1 , . . . , x M ) ∈ { 0 , 1 } M b e the vector of comp onen t states, φ ( x ) is then the non-decreasing structure function represen ting the system state. In particular, note that for coheren t systems φ ( x ) is al- w ays a m ultiv ariate p olynomial in x , so that given x encrypted the op erational state of the system can b e computed without decrypting the individual comp onent states. Indeed, it is v alid to replace the binary op erational state v ector x with probabilities of correct function at some mission time of interest and the structure function will then render the probability of correct system op eration. How ev er, note that in this instance, if the probabilities are enco ded as in § 2.2, then ev aluation b ecomes awkw ard due to the v arying precisions κ . Much more problematically , the form of the p olynomial to b e ev aluated is itself an enco ding of the system design, so that rev ealing the algorithm to ev aluate the reliability is equiv alen t to revealing the design, rendering it un usable for the problem considered here. Let the system in question ha ve K ≥ 1 differen t comp onen t types, with M k com- p onen ts of type k , so that P K k =1 M k = M . It then follows (Co olen and Co olen-Maturi, 2012) that the probability the system w orks giv en that l = ( l 1 , . . . , l K ) of eac h of the M = ( M 1 , . . . , M K ) comp onents is working is: Φ( l ) = " M k l k − 1 # X x ∈ S l φ ( x ) (2) 4 where S l is the set of all comp onen t states x with exactly l = ( l 1 , . . . , l K ) comp onents of eac h t yp e working, S l 1 ,...,l K = { x : P M k i =1 x k i = l k ∀ k } . Equation (2) is called the survival signatur e . If C k t ∈ { 0 , 1 , . . . , M k } is the random v ariable denoting the n umber of components of t yp e k whic h are still op erational at time t in a future system with surviv al signature Φ( · ), then the surviv al signature allo ws decomp osition of the surviv al function of the ov erall system lifetime T S as: P ( T S > t ) = M 1 X l 1 =0 · · · M K X l K =0 Φ( l 1 , . . . , l K ) P K \ k =1 { C k t = l k } ! = M 1 X l 1 =0 · · · M K X l K =0 Φ( l 1 , . . . , l K ) K Y k =1 P C k t = l k if types are indep endent (3) Notably , (3) is also a p olynomial in Φ( · ) and the comp onen t probabilities. Moreo ver, it is a homo gene ous p olynomial. Therefore, under the scaling of § 2.2, ev ery term of the p olynomial in (3) has precision ( K + 1) κ , so that the terms can b e summed without an y rescaling required. This makes the surviv al signature particularly w ell suited to computation under a homomorphic encryption sc heme. F urther still, the p olynomial form of (3) is identical for all systems containing K types of comp onent so that it reveals little ab out the design of the system as long as the v alues of Φ( l ) ∀ l are not revealed. A recen t detailed survey of the surviv al signature with a more expansive in tro duction can b e found in (Co olen et al., 2016). 4 The priv acy preserving proto col The exp osition herein b efore highlighted the crucial asp ects of homomorphic encryption and the surviv al signature whic h no w enable a no vel approach to preserving the priv acy of comp onent man ufacturers and system designers when ev aluating the reliability of a new system. 4.1 Priv acy framework The form of priv acy proto col now presented falls under the so-called ‘honest but curious’ mo del of securit y without collusion. That is, it is assumed that all the parties partici- pating in the proto col are honest in following the sp ecification, honest in the data they input and do not collude with one another (rather are in comp etition). How ev er, it is assumed that all parties are curious to determine the secret information b elonging to the other parties and will seek to learn it b y an y means p ossible outside the protocol. An interesting op en question is to extend this to the case of malicious parties, where there are no guaran tees that the proto col has b een follow ed and so trust in the final answ er m ust b e dynamically established. 4.2 Setup Let the system designer who wishes to ev aluate the reliability of their design b e called δ . The design inv olv es K different t yp es of component, made by manufacturers called χ 1 , . . . , χ K . 5 There are certain initial setup actions whic h m ust b e p erformed: 1. δ first creates public and secret keys ( k p , k s ) for a homomorphic encryption scheme of their choice which supp orts in teger encryption. The sch eme parameters used to generate the k eys m ust supp ort multiplicativ e depth of at least K . 2. δ selects a grid of time p oin ts at whic h they wish to ev aluate the surviv al curv e of the system, t = { t 1 , . . . , t T } . 3. δ next creates an encrypted lo okup table, Ξ, for the system design. P art will b e encrypted and part unencrypted: (a) F orm a table, Ξ ( l ) , comprising of columns l 1 , . . . , l K with rows enumerating all p ossible combinations of v alues that can be tak en (i.e. Q K k =1 ( M K + 1) rows). Ξ ( l ) = 0 · · · 0 0 · · · 1 . . . l 1 · · · l K . . . m 1 · · · m K (b) F orm another table, Ξ (Φ) , con taining T identical columns, where all en tries on ro w i are Φ Ξ ( l ) i, · . That is, each row contains the surviv al signature for eac h corresp onding input row in Ξ ( l ) . Note this requires only kno wledge of the system design. Ξ (Φ) = Φ(0 , . . . , 0) · · · Φ(0 , . . . , 0) Φ(0 , . . . , 1) · · · Φ(0 , . . . , 1) . . . . . . Φ( l 1 , . . . , l K ) · · · Φ( l 1 , . . . , l K ) . . . . . . Φ( m 1 , . . . , m K ) · · · Φ( m 1 , . . . , m K ) Although all columns are identical at the start of the proto col, eac h column will differ as the proto col pro ceeds once manufacturers in teract test data for the T different time p oin ts. That is, each column will b e the reliability ev aluation for a differen t lev el of function at each time { t 1 , . . . , t T } . (c) δ then decides on an acceptable precision lev el, κ , and m utates Ξ (Φ) , Φ(Ξ ( l ) i, · ) → Enc k p , µ κ Φ Ξ ( l ) i, · , so that the lo okup columns l 1 , . . . , l K in Ξ ( l ) are unencrypted and the surviv al signature v alues in Ξ (Φ) are encrypted. T ogether these form an encrypted represen tation of the system structure that reveals the n um b er of comp onents, but keeps the design secret. 6 Ξ (Φ) = Enc k p , µ κ Φ(0 , . . . , 0) · · · Enc k p , µ κ Φ(0 , . . . , 0) Enc k p , µ κ Φ(0 , . . . , 1) · · · Enc k p , µ κ Φ(0 , . . . , 1) . . . . . . Enc k p , µ κ Φ( l 1 , . . . , l K ) · · · Enc k p , µ κ Φ( l 1 , . . . , l K ) . . . . . . Enc k p , µ κ Φ( m 1 , . . . , m K ) · · · Enc k p , µ κ Φ( m 1 , . . . , m K ) 4.3 Comp onen t inference Since χ 1 , . . . , χ K w ant to keep the comp onent test data secret, inference on comp onent reliabilit y is p erformed by each manufacturer prior to an y encryption. This corresp onds to eac h χ k estimating P C k t = l k for eac h t ∈ { t 1 , . . . , t n } . Given that δ cannot v alidate the inference approach tak en to estimate P C k t = l k from the test data, one might argue a non-parametric metho d should b e sp ecified as part of the proto col. This is the approac h used in the example in the next section. 4.4 The proto col The priv acy preserving proto col then pro ceeds as follo ws: 1. δ sends k p , t and κ to all χ k . Eac h χ k is also sent only the k -th column of Ξ ( l ) . Finally , Ξ (Φ) is sent to χ 1 to start the proto col. 2. F or k = { 1 , . . . , K } : (a) F or t = { 1 , . . . , T } : • Up date Ξ (Φ) i,t = Ξ (Φ) i,t ⊗ Enc k p , µ κ P ( C k t = Ξ ( l ) i,k ) ∀ i (4) (b) After fully up dating Ξ (Φ) , if k < K then χ k sends Ξ (Φ) to χ k +1 . 3. The final participan t χ K computes the final result, the encrypted column sums of Ξ (Φ) , ξ j , Q K k =1 ( M K +1) M i =1 Ξ (Φ) i,t ∀ j ∈ { 1 , . . . , T } (5) χ K then sends ξ = ( ξ 1 , . . . , ξ T ) to δ . 4. δ finally computes 10 − ( K +1) κ Dec ( k s , ξ j ) ≈ P ( T S > t j ), rendering the surviv al curv e v alues computed on the required grid of times t . Note that due to the system lifetime decomposition via the surviv al signature b eing a homogeneous p olynomial in the surviv al signature and comp onen t surviv al probabilities, the adjustment required in the final step abov e is kno wn a priori to b e 10 − ( K +1) κ . 7 C1 C2 C3 C4 P1 P2 P3 P4 M H Figure 1: Simple automotiv e braking system. The master brake cylinder (M) engages all the four wheel brake cylinders (C1 – C4). These in turn each trigger a braking pad assembly (P1 – P4). The hand brak e (H) go es directly to the rear brake pad assem blies P3 and P4; the v ehicle brak es when at least one of the brake pad assem blies is engaged. 5 Exp erimen tal results In order to provide an insigh t in to the metho d for practitioners, a fully encrypted surviv al analysis w as conducted on the simple automotiv e braking system example from (W alter et al., 2016), depicted in Figure 1. This system comprises four different component t yp es which are tak en to b e manufactured by different parties, all of whom wish their test data to remain secret. It is assumed that the system design is also secret and b elongs to a different part y . The full co de required to run this example is provided in the supplemen tary material, programmed in the easy to use R language (R Core T eam, 2015). 5.1 Comp onen t inference Man ufacturer of component k is tak en to ha v e n k > 0 observ ations of lifetime test data on the comp onen t type they manufacture, t k = { t k 1 , . . . , t k n k } , k ∈ { C , H , M , P } . It is a well studied problem to infer the comp onent lifetime distributions, either non-parametrically or b y inferring parameter uncertaint y in a family of mo dels suc h as the W eibull. Aslett et al. (2015a) considered b oth situations with the surviv al signature, but in this example only the non-parametric approach is used: b oth metho ds would w ork with the priv acy preserving protocol describ ed herein b efore, but in the presen t context it w ould seem unlik ely manufacturers w ould b e willing to disclose the parametric family they are fitting and the system designer may therefore wish to guard against inappropriate choices whic h (s)he cannot v alidate — if all man ufacturers use the same non-parametric metho d then the context of all results is well understo o d. 5.2 Example setup T o make the example usage of the technique as realistic as p ossible, 5 compute serv ers w ere launched in 5 different con tinents around the world using the Amazon W eb Services EC2 cloud platform, to mimic a globally distributed supply chain. This also pro vides an empirical example of the cost of the metho d if a designer/man ufacturer do es not hav e 8 a sufficiently p o werful machine to run the algorithm. The servers for eac h part y w ere launc hed as follows: Role Ph ysical Server Lo cation Serv er Type System designer Dublin, Ireland m4.10xlarge Man ufacturer C Northern California, USA m4.10xlarge Man ufacturer H S˜ ao Paulo, Brazil c3.8xlarge Man ufacturer M Sydney , Australia r3.4xlarge Man ufacturer P T okyo, Japan i2.8xlarge The servers ab o ve hav e the follo wing tec hnical sp ecification: Serv er Type In tel Xeon CPU Memory (GB) Hourly Cost (US$) m4.10xlarge 40 cores, 2.4 GHz Hasw ell 160 2.61 – 2.79 c3.8xlarge 32 cores, Ivy Bridge 60 2.60 r3.4xlarge 16 cores, Ivy Bridge 244 1.60 i2.8xlarge 32 cores, Ivy Bridge 244 8.00 ‘Cores’ refers to hyper-threaded cores and hourly costs quoted are on-demand in the region launched. Much c heap er ‘sp ot’ prices are commonly av ailable. See the Amazon W eb Services website for further details. The F an and V ercauteren (2012) homomorphic encryption sc heme w as used via the HomomorphicEncryption R pac k age (Aslett, 2014), with surviv al signature computed b y the system designer using the ReliabilityTheory R pac k age (Aslett, 2012). T o ensure reasonable transmission times b et ween continen ts the cipher texts m ust b e compressed. Typically , the size of Ξ (Φ) in this example reac hed nearly 12GB and although the standard Unix gzip to ol provides go o d compression, it can take up to 20 minutes to compress such a large file. Therefore pigz (Adler, 2015) w as used for high sp eed parallel compression whic h w as more than an order of magnitude faster on the m ulti-core Amazon EC2 servers. 5.3 The encrypted analysis run The system designer set precision κ = 5; set 100 ev enly spaced times for ev aluation b et ween 0 and 5, t = { 5 i 99 : i = 0 , 1 , . . . , 99 } ; and generated public/secret k eypairs pro viding at least 128-bit securit y (that is, a brute force attack er would ha ve to p erform order 2 128 op erations to decrypt). The computational c haracteristics of this actual analysis run were as follo ws: Role Action Timing / Size System designer Dublin, Ireland Generation of ( k p , k s ) 0.3 secs Encryption of Ξ (Φ) 1 min 41.1 secs Sa ving Ξ (Φ) to disk 2 min 41.3 secs Compressing Ξ (Φ) on disk 48.0 secs Size of Ξ (Φ) on disk 5.5GB T r ansfer Ξ (Φ) to Manufactur er C 11 min 37.5 secs 9 0 . 2 5 0 . 5 0 0 . 7 5 1 . 0 0 0 1 2 3 4 5 Time Probability Method E n c r y p t e d S t a n d a r d Figure 2: Comparison of the system surviv al curv es as estimated using the soft ware function in Aslett et al. (2015a) and as decrypted after the encrypted estimation on the global net work of serv ers. Role Action Timing / Size Man ufacturer C Northern California, USA Decompress & load Ξ (Φ) from disk 10 min 22.4 secs Up date Ξ (Φ) , eq (4) 6 min 18.3 secs Sa ving & compressing Ξ (Φ) to disk 2 min 9.8 secs T r ansfer Ξ (Φ) to Manufactur er H 11 min 24.4 secs Man ufacturer H S˜ ao Paulo, Brazil Decompress & load Ξ (Φ) from disk 10 min 13.2 secs Up date Ξ (Φ) , eq (4) 7 min 23.1 secs Sa ving & compressing Ξ (Φ) to disk 4 min 45.2 secs T r ansfer Ξ (Φ) to Manufactur er H 20 min 16.5 secs Man ufacturer M Sydney , Australia Decompress & load Ξ (Φ) from disk 9 min 41.0 secs Up date Ξ (Φ) , eq (4) 11 min 28.2 secs Sa ving & compressing Ξ (Φ) to disk 2 min 54.2 secs T r ansfer Ξ (Φ) to Manufactur er H 6 min 40.7 secs Man ufacturer P T okyo, Japan Decompress & load Ξ (Φ) from disk 9 min 57.1 secs Up date Ξ (Φ) , eq (4) 7 min 13.5 secs Compute ξ , eq (5) 6.1 secs Sa ving & compressing ξ to disk 2.5 secs Size of ξ on disk 58.4MB T r ansfer ξ to System Designer 39.5 secs System designer Dublin, Ireland Decompress & load ξ from disk 5.9 secs Decryption of ξ 8.6 secs T otal: 2 hr 18 min 38.4 secs Clearly the most v ariable timing element of this analysis stems from the data transfer time betw een man ufacturers, whic h ranged from under 7 minutes to o ver 20 min utes. A total run time of under 3 hours means that this proto col is entirely feasible to run ev en 10 if manufacturer or designer need to outsource the compute p ow er to accomplish it. In particular, none of the machines needs to b e on for more than 1 hour and at the time of writing the most exp ensive of the instances used costs US$ 7.50 p er hour, though using so-called sp ot-instances there is usually a suitable instance type av ailable for less than US$ 1 p er hour. Up on decryption, the surviv al curve whic h is yielded can b e seen in Figure 2. Com- pared to the baseline result which is computed unencrypted, there is a very small dis- crepancy resulting from the rounding asso ciated with the integer encoding µ κ : R → Z . An empirical estimate of the total v ariation distance b et ween the true and encrypted surviv al probabilit y measures is 0.029, representing a small discrepancy . 6 Conclusions This w ork has developed a priv acy preserving proto col for conducting a full system relia- bilit y analysis. The use of homomorphic encryption metho ds pro vides cryptographically strong guarantees on the security of the raw system design and component test data. The metho d has b een demonstrated to b e practical despite the tremendous compu- tational burden which traditionally accompanies encrypted statistical analysis and is a metho d whic h can b e implemented b y businesses ev en where they lack in-house com- pute servers by a v ailing of inexp ensiv e cloud computing options (where priv acy is still preserv ed since all material is encrypted). Supplemen tary materials There are extensiv e supplementary materials pro vided in a compressed zip file. The con tents are as follows: designer.R : An extensively commented script file containing the co de which a system designer would run in order derive the surviv al signature and homomorphically encrypt Ξ (Φ) as describ ed in Section 4, using the automotive braking system of Section 5. (R script file) manufacturer_ { C,H,M,P } .R : F our script files, one p er man ufacturer, containing the co de in order to execute the steps of the proto col describ ed in 4 for the braking system example of Section 5. (R script file) utility.R : defines utility functions used in the ab o v e scripts to compute µ κ ( · ), µ − 1 κ ( · ) and to compute the non-parametric comp onent inference estimate. (R script file) AmazonEC2-xi_m.RData : the decrypted results of the full exp eriment run in Section 5. (R image file) compare_to_truth.R : a script whic h plots the exp erimen tal results which were run en- crypted across a global net w ork to the result of p erforming the exp erimen t unen- crypted in one session. (R script file) 11 Ac kno wledgemen ts The author is supported b y the i-lik e programme gran t (EPSRC grant reference n umber EP/K014463/1 http://www.i-lik e.org.uk). References M. Adler. pigz: A p ar al lel implementation of gzip for mo dern multi-pr o c essor, multi-c or e machines . Jet Propulsion Lab oratory , 2015. URL http://www.zlib.net/pigz/ . L. J. M. Aslett. R eliabilityThe ory: T o ols for structur al r eliability analysis , 2012. URL http://cran.r- project.org/package=ReliabilityTheory . R pac k age. L. J. M. Aslett. HomomorphicEncryption: F ul ly Homomorphic Encryption , 2014. URL http://www.louisaslett.com/HomomorphicEncryption/ . R pac k age. L. J. M. Aslett, F. P . A. Co olen, and S. P . Wilson. Bay esian inference for reliability of systems and net works using the surviv al signature. Risk A nalysis , 35(9):1640–1651, 2015a. doi: 10.1111/risa.12228. URL http://doi.org/10.1111/risa.12228 . L. J. M. Aslett, P . M. Esperan¸ ca, and C. C. Holmes. A review of homomorphic encryp- tion and softw are tools for encrypted statistical mac hine learning. T ec hnical rep ort, Univ ersity of Oxford, 2015b. URL . L. J. M. Aslett, P . M. Esp eran¸ ca, and C. C. Holmes. Encrypted statistical machine learning: new priv acy preserving metho ds. arXiv , 2015c. URL abs/1508.06845 . Z. W. Birnbaum, J. D. Esary , and S. C. Saunders. Multi-comp onent systems and struc- tures and their reliability . T e chnometrics , 3(1):55–77, 1961. F. P . A. Coolen and T. Coolen-Maturi. Generalizing the signature to systems with m ul- tiple types of comp onen ts. In W. Zamo jski, J. Mazurkiewicz, J. Sugier, T. W alk owiak, and J. Kacprzyk, editors, Complex Systems and Dep endability , volume 170 of A dvanc es in Intel ligent and Soft Computing , pages 115–130. Springer Berlin Heidelberg, 2012. doi: 10/b dxb. F. P . A. Co olen, T. Co olen-Maturi, L. J. M. Aslett, and G. W alter. Imprecise system reliabilit y using the surviv al signature. In ICAMER 2016 Pr o c e e dings , 2016. J. F an and F. V ercauteren. Somewhat practical fully homomorphic encryption. IACR Cryptolo gy ePrint Ar chive , 2012. C. Gen try . A ful ly homomorphic encryption scheme . PhD thesis, Stanford Universit y , 2009. URL http://crypto.stanford.edu/craig/ . C. Gentry . Computing arbitrary functions of encrypted data. Communic ations of the A CM , 53(3):97–105, 2010. doi: 10.1145/1666420.1666444. T. Graep el, K. Lauter, and M. Naehrig. Ml confidential: Mac hine learning on encrypted data. In Pr o c e e dings of the 15th International Confer enc e on Information Se curity and Cryptolo gy , v olume 7839 of L e ctur e Notes in Computer Scienc e , pages 1–21. Springer- V erlag, 2012. doi: 10/b dxc. 12 S. Ko c har, H. Mukerjee, and F. J. Samaniego. The “signature” of a coheren t system and its application to comparisons among systems. Naval R ese ar ch L o gistics , 46(5): 507–523, 1999. doi: 10/cqnmhj. R Core T eam. R: A L anguage and Envir onment for Statistic al Computing . R F oundation for Statistical Computing, Vienna, Austria, 2015. URL https://www.R- project. org/ . R. L. Riv est, L. Adleman, and M. L. Dertouzos. On data banks and priv acy homomor- phisms. F oundations of Se cur e Computation , 4(11):169–180, 1978. F. J. Samaniego. On closure of the IFR class under formation of coherent systems. IEEE T r ansactions on R eliability , 34(1):69–72, 1985. doi: 10.1109/TR.1985.5221935. G. W alter, L. J. M. Aslett, and F. P . A. Co olen. Ba y esian nonparametric system reliability using sets of priors. arXiv , 2016. URL . 13
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment