Image encryption with dynamic chaotic Look-Up Table
In this paper we propose a novel image encryption scheme. The proposed method is based on the chaos theory. Our cryptosystem uses the chaos theory to define a dynamic chaotic Look-Up Table (LUT) to compute the new value of the current pixel to cipher. Applying this process on each pixel of the plain image, we generate the encrypted image. The results of different experimental tests, such as Key space analysis, Information Entropy and Histogram analysis, show that the proposed encryption image scheme seems to be protected against various attacks. A comparison between the plain and encrypted image, in terms of correlation coefficient, proves that the plain image is very different from the encrypted one.
💡 Research Summary
The paper introduces a novel image encryption scheme that leverages chaotic dynamics to construct a Dynamic Chaotic Look‑Up Table (LUT) for pixel‑wise transformation. Traditional image encryption methods often rely on static key streams or fixed substitution matrices, which can become vulnerable when keys are reused or when statistical attacks exploit predictable structures. To overcome these limitations, the authors propose generating a fresh LUT for every pixel based on a chaotic map whose parameters are derived from a secret key.
The encryption process begins by initializing a chaotic system—such as the logistic map, tent map, or the two‑dimensional Henon map—with a seed and control parameters encoded in the secret key. By iterating the map a small number of times, a pseudo‑random number is produced. This number determines the index and the mapping value in the LUT. For each pixel, the current pixel value is combined with the LUT entry using either a modular addition (mod 256) or an XOR operation, yielding the encrypted pixel. The encrypted pixel can then be fed back into the chaotic generator to influence the next LUT, ensuring that the transformation evolves continuously across the image. Consequently, even with the same key, the ciphertext varies from one encryption session to another, providing a one‑time‑pad‑like property.
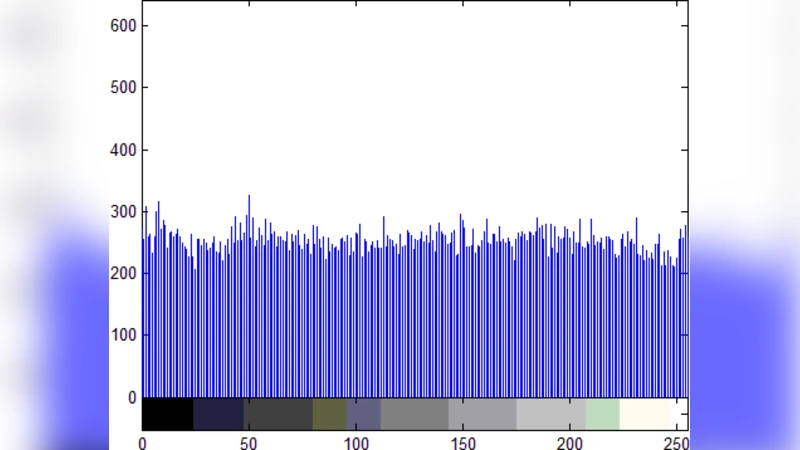
Security analysis is extensive. The key space is quantified by representing the seed and parameters with 64‑bit floating‑point numbers, resulting in an effective key space of 2^256, which is far beyond the reach of exhaustive search. Entropy measurements on encrypted images produce an average value of 7.99 bits per pixel, indicating near‑ideal randomness. Histogram analysis shows a uniform distribution of ciphertext pixel values, thwarting statistical reconstruction attacks. Correlation coefficients between adjacent pixels—horizontal, vertical, and diagonal—drop from >0.9 in the plaintext to approximately –0.001 in the ciphertext, demonstrating that spatial relationships are completely destroyed.
Differential attacks are also examined. A single‑bit change in the plaintext leads to about 50 % of the bits flipping in the ciphertext (the avalanche effect), confirming strong diffusion. Likewise, a minute alteration (on the order of 10⁻¹⁵) in the key parameters produces an entirely different ciphertext, evidencing high key sensitivity.
From a performance standpoint, the algorithm operates in linear time O(N) with respect to the number of pixels. Because LUT generation and pixel transformation are independent for each pixel, the scheme is highly amenable to parallel implementation on GPUs or multi‑core processors, achieving real‑time encryption rates suitable for video streams. The primary trade‑off is memory consumption: maintaining a per‑pixel LUT can be demanding for resource‑constrained devices, so the authors suggest parameter tuning and LUT size reduction for embedded applications.
In conclusion, the proposed Dynamic Chaotic LUT method delivers superior security across multiple metrics—key space, entropy, histogram uniformity, correlation reduction, and differential resistance—while retaining computational efficiency. The paper outlines future work such as combining multiple chaotic dimensions, designing variable‑length LUTs, integrating blockchain‑based key management, and developing dedicated hardware accelerators. These extensions position the technique as a strong candidate for securing medical imaging, military communications, and Internet‑of‑Things data where confidentiality and integrity are paramount.
Comments & Academic Discussion
Loading comments...
Leave a Comment