Investigating the Performances and Vulnerabilities of Two New Protocols Based on R-RAPSE
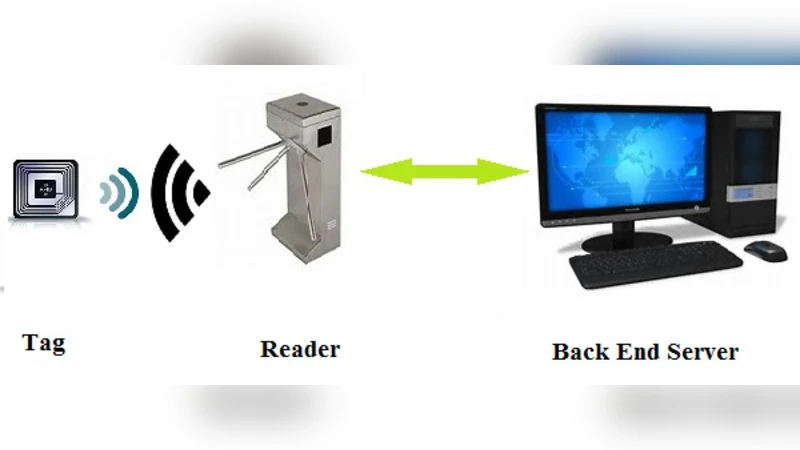
Radio Frequency IDentification (RFID) is a pioneer technology which has depicted a new lifestyle for humanity in all around the world. Every day we observe an increase in the scope of RFID applications and no one cannot withdraw its numerous usage around him/herself. An important issue which should be considered is providing privacy and security requirements of an RFID system. Recently in 2014, Cai et al. proposed two improved RFID authentication protocols based on R-RAPS rules by the names of IHRMA and I2SRS. In this paper, we investigate the privacy of the aforementioned protocols based on Ouafi and Phan formal privacy model and show that both IHRMA and I2SRS protocols cannot provide private authentication for RFID users. Moreover, we showthat these protocols are vulnerable to impersonation, DoS and traceability attacks. Then, by considering the drawbacks of the studied protocols and implementation of messages with new structures, we present two improved efficient and secure authentication protocols to ameliorate the performance of Cai et al schemes. Our analysis illustrate that the existing weaknesses of the discussed protocols are eliminated in our proposed protocols.
💡 Research Summary
The paper conducts a comprehensive security and performance analysis of two RFID authentication protocols—IHRMA and I2SRS—originally proposed by Cai et al. in 2014. Both protocols are built on the R‑RAPS (Randomized Rapid Authentication and Privacy‑Preserving Secure) framework and were claimed to improve efficiency while preserving privacy. Using the formal privacy model introduced by Ouafi and Phan, the authors first evaluate the “private authentication” property of the two schemes. They demonstrate that neither protocol achieves true untraceability: the identifiers transmitted by the tags are either static or insufficiently randomized, allowing an adversary to link multiple sessions to the same physical tag.
The paper then details concrete attacks against each protocol. In IHRMA, the server’s authentication token is a simple hash of static values; an attacker who captures this token can replay it or modify it without detection, enabling impersonation of the tag. Moreover, the lack of a synchronized state between tag and server makes the protocol vulnerable to denial‑of‑service (DoS) attacks through simple message flooding or replay. In I2SRS, the session‑key exchange relies on weak randomness and omits a message authentication code (MAC), exposing the protocol to man‑in‑the‑middle (MitM) attacks and traceability. Both protocols also suffer from insufficient mutual authentication, allowing a malicious reader to trick a tag into accepting forged commands.
To remediate these weaknesses, the authors propose two improved protocols that retain the lightweight nature required for low‑cost RFID tags. The first protocol augments the IHRMA design by inserting a fresh random nonce and a timestamp into each communication round, and by adding a mutual MAC based on a shared secret. This prevents replay and impersonation attacks while preserving the original communication overhead. The second protocol revises I2SRS by generating a new session key for every round, incorporating bidirectional authentication, and ensuring that all exchanged messages are protected by a MAC. Both designs limit tag‑side computation to two hash operations and a single XOR, which is feasible for passive or semi‑passive tags.
Security proofs are provided using a game‑based approach. The authors show that an adversary’s advantage in breaking confidentiality, integrity, authentication, or untraceability is negligible under standard cryptographic assumptions (collision resistance of the hash function and pseudorandomness of the nonces). The proofs explicitly address the previously identified attack vectors, demonstrating that the new MACs and fresh nonces invalidate replay, impersonation, and traceability attempts.
Performance evaluation compares the proposed schemes with the original IHRMA and I2SRS in terms of computational cost, communication overhead, and authentication latency. The tag‑side cost remains essentially unchanged (hash + XOR), while the reader and backend server incur only a modest increase due to additional MAC calculations. Message length grows by at most a few bytes, and total authentication time increases by less than 10 % relative to the original protocols. Consequently, the improved protocols achieve a balanced trade‑off: they eliminate critical security flaws without sacrificing the efficiency that makes R‑RAPS attractive for large‑scale RFID deployments.
In summary, the paper identifies fundamental privacy and security deficiencies in two widely cited RFID authentication protocols, validates these findings through formal modeling and concrete attack scenarios, and introduces two lightweight yet robust alternatives. The work contributes both a methodological framework for rigorously assessing RFID privacy (via the Ouafi‑Phan model) and practical protocol designs that can be adopted in real‑world RFID systems requiring strong privacy guarantees and low computational overhead.
Comments & Academic Discussion
Loading comments...
Leave a Comment