A Trust Domains Taxonomy for Securely Sharing Information: A Preliminary Investigation
Information sharing has become a vital part in our day-to-day life due to the pervasiveness of Internet technology. In any given collaboration, information needs to flow from one participant to another. While participants may be interested in sharing information with one another, it is often necessary for them to establish the impact of sharing certain kinds of information. This is because certain information could have detrimental effects when it ends up in wrong hands. For this reason, any would-be participant in a given collaboration may need to establish the guarantees that the collaboration provides, in terms of protecting sensitive information, before joining the collaboration as well as evaluating the impact of sharing a given piece of information with a given set of entities. In order to address this issue, earlier work introduced a trust domains taxonomy that aims at managing trust-related issues in information sharing. This paper attempts to empirically investigate the proposed taxonomy through a possible scenario (e.g. the ConfiChair system). The study results determined that Role, Policy, Action, Control, Evidence and Asset elements should be incorporated into the taxonomy for securely sharing information among others. Additionally, the study results showed that the ConfiChair, a novel cloud-based conference management system, offers strong privacy and confidentiality guarantees.
💡 Research Summary
The paper addresses the growing need for secure information sharing in collaborative environments, where the misuse of sensitive data can have serious consequences. Existing security approaches focus mainly on technical safeguards such as encryption and access control lists, but they often overlook the contextual trust relationships among participants. To fill this gap, the authors propose a “Trust Domains” taxonomy that structures trust‑related concerns into six inter‑dependent elements: Role, Policy, Action, Control, Evidence, and Asset.
Each element serves a specific purpose. Roles define the actors (e.g., authors, reviewers, program chairs) and their authority within a system. Policies articulate the rules governing data handling, such as confidentiality requirements, retention periods, and anonymity constraints. Actions are the concrete operations performed on data—uploading, reviewing, modifying, or deleting. Controls are the mechanisms that enforce policies, including authentication, authorization, encryption, and logging. Evidence consists of audit trails, digital signatures, and other records that can be examined to verify compliance. Assets are the protected pieces of information themselves, such as manuscript files, reviewer comments, and participant profiles.
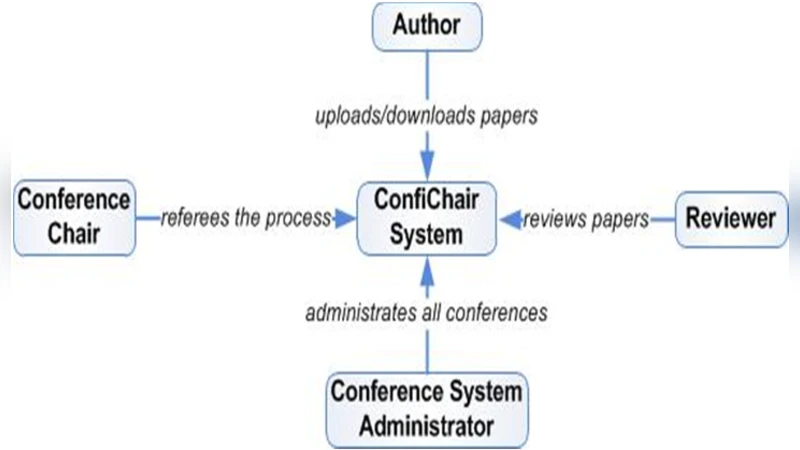
To evaluate the practicality of the taxonomy, the authors conduct an empirical study using ConfiChair, a cloud‑based conference management system that exemplifies a complex, multi‑stakeholder collaboration. ConfiChair handles manuscript submission, peer review, and program scheduling, all of which involve highly sensitive data that must remain confidential while still supporting transparent processes.
The research methodology combines surveys and semi‑structured interviews with participants occupying different roles in the conference workflow. Survey items assess participants’ awareness of policies, acceptance of control mechanisms, and perceived usefulness of evidence. Interviews probe concrete scenarios, challenges, and expectations. Findings reveal that participants feel more trust when roles and policies are explicitly defined. Multi‑factor authentication and end‑to‑end encryption are viewed as the most effective controls. Audit logs (Evidence) are valued for real‑time detection of policy violations and for post‑incident analysis. Moreover, the sensitivity of assets dictates differentiated retention and access rules, confirming the need for a nuanced policy layer.
Based on these results, the authors conclude that all six taxonomy elements are essential for securely sharing information. The application of the Trust Domains model to ConfiChair demonstrates strong privacy and confidentiality guarantees, outperforming traditional conference management platforms in terms of data‑leak risk mitigation.
The paper acknowledges several limitations. The case study is limited to a single system, which restricts the generalizability of the findings. The evidence component’s long‑term storage and integrity verification mechanisms are not fully fleshed out. Future work is proposed to include multiple domains such as healthcare and finance, to test the taxonomy across diverse risk environments, and to develop automated evidence management and dynamic policy‑update capabilities. By extending the model in these directions, the authors aim to solidify the taxonomy as a robust, adaptable framework for trustworthy information sharing across a wide range of collaborative contexts.
Comments & Academic Discussion
Loading comments...
Leave a Comment