BYOD Security: A New Business Challenge
Bring Your Own Device (BYOD) is a rapidly growing trend in businesses concerned with information technology. BYOD presents a unique list of security concerns for businesses implementing BYOD policies. Recent publications indicate a definite awareness of risks involved in incorporating BYOD into business, however it is still an underrated issue compared to other IT security concerns. This paper focuses on two key BYOD security issues: security challenges and available frameworks. A taxonomy specifically classifying BYOD security challenges is introduced alongside comprehensive frameworks and solutions which are also analysed to gauge their limitations.
💡 Research Summary
The paper “BYOD Security: A New Business Challenge” examines the rapid adoption of Bring‑Your‑Own‑Device (BYOD) policies in modern enterprises and the accompanying security challenges that have emerged as a result. While BYOD offers clear business benefits—cost savings, increased employee productivity, and flexibility—the authors argue that it simultaneously undermines traditional perimeter‑based security models, creating a complex risk landscape that is often under‑appreciated compared to other IT security concerns.
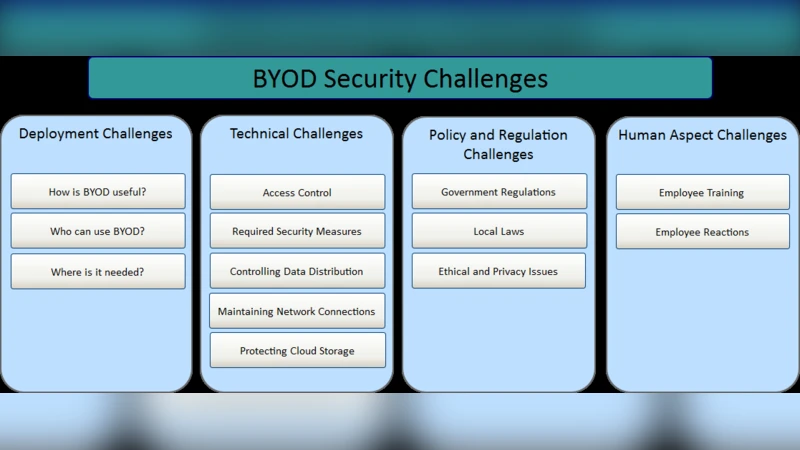
The authors first introduce a taxonomy that classifies BYOD security challenges into four primary domains: (1) device heterogeneity, (2) data protection, (3) access control and authentication, and (4) management and policy enforcement. Device heterogeneity refers to the wide variety of operating systems, hardware specifications, and patch cycles across employee‑owned smartphones, tablets, and laptops. This diversity hampers unified policy deployment and makes it difficult to guarantee a consistent security baseline. Data protection concerns focus on the lifecycle of corporate information once it resides on personal devices, emphasizing the need for both in‑transit encryption (e.g., TLS) and at‑rest encryption, as well as reliable remote‑wipe capabilities. The paper notes that many organizations secure data only during transmission, leaving stored data vulnerable.
Access control and authentication challenges arise because the traditional network edge becomes blurred in a BYOD environment. The authors advocate for multi‑factor authentication (MFA), context‑aware authentication, and Zero‑Trust principles that continuously evaluate user identity, device posture, location, and application context. However, real‑world surveys reveal low MFA adoption rates due to perceived user inconvenience, and an over‑reliance on VPNs that does not address the underlying trust issues.
Management and policy enforcement are addressed through Mobile Device Management (MDM) and Enterprise Mobility Management (EMM) solutions. While these tools enable remote configuration, policy compliance checks, and device inventory, they also raise privacy concerns and legal constraints (e.g., GDPR) when corporate IT attempts to control personal devices. The authors discuss containerization as a compromise that isolates corporate workloads without full device control.
The paper then critiques existing security frameworks and standards—NIST SP 800‑124, ISO/IEC 27001/27002—arguing that they lack specific guidance for BYOD’s dynamic risk profile, especially in integrating User and Entity Behavior Analytics (UEBA) and real‑time threat intelligence feeds. To illustrate contemporary approaches, the authors compare two modern frameworks: Google’s BeyondCorp and Microsoft’s Enterprise Mobility + Security (EMS). BeyondCorp implements a pure Zero‑Trust model that authenticates every request based on device and user context, eliminating the need for a traditional VPN. Its strengths lie in cloud scalability and reduced perimeter reliance, but it suffers from complex initial deployment and limited compatibility with legacy systems. EMS offers a tightly integrated suite of Azure Active Directory, Intune, and Cloud App Security, providing robust MDM, Identity and Access Management (IAM), and Data Loss Prevention (DLP) capabilities. EMS excels in Windows‑centric environments and offers AI‑driven risk assessment, yet its high licensing costs, limited support for non‑Windows devices, and intricate licensing structure can deter smaller enterprises.
Building on these analyses, the authors propose a hybrid security model that combines containerization with Zero‑Trust principles. Corporate applications and data are placed inside an enterprise‑managed container on the personal device; each container access request triggers real‑time authentication, policy evaluation, and continuous posture assessment. This approach limits data exposure while preserving user privacy. The model also integrates UEBA and threat‑intel feeds into a Security Information and Event Management (SIEM) platform to provide automated anomaly detection and rapid incident response.
Beyond technology, the paper stresses the importance of organizational culture and employee education. Survey data indicate that regular security awareness training reduces policy violations by over 30 %. Clear BYOD usage policies, ongoing communication between IT and end‑users, and a culture that encourages reporting of security incidents are essential for the success of any technical controls.
In conclusion, the authors reaffirm that BYOD is a double‑edged sword: it can boost competitiveness but also introduces significant security liabilities that, if ignored, may lead to costly data breaches and regulatory penalties. They recommend a multi‑layered defense strategy—encompassing device management, encryption, Zero‑Trust access, automated policy enforcement, and continuous user education—to mitigate these risks effectively. The paper serves as a comprehensive guide for enterprises seeking to balance the benefits of BYOD with the imperative of robust security.
Comments & Academic Discussion
Loading comments...
Leave a Comment