Ranking the Importance Level of Intermediaries to a Criminal using a Reliance Measure
Recent research on finding important intermediate nodes in a network suspected to contain criminal activity is highly dependent on network centrality values. Betweenness centrality, for example, is widely used to rank the nodes that act as brokers in the shortest paths connecting all source and all the end nodes in a network. However both the shortest path node betweenness and the linearly scaled betweenness can only show rankings for all the nodes in a network. In this paper we explore the mathematical concept of pair-dependency on intermediate nodes, adapting the concept to criminal relationships and introducing a new source-intermediate reliance measure. To illustrate our measure, we apply it to rank the nodes in the Enron email dataset and the Noordin Top Terrorist networks. We compare the reliance ranking with Google PageRank, Markov centrality as well as betweenness centrality and show that a criminal investigation using the reliance measure, will lead to a different prioritisation in terms of possible people to investigate. While the ranking for the Noordin Top terrorist network nodes yields more extreme differences than for the Enron email transaction network, in the latter the reliance values for the set of finance managers immediately identified another employee convicted of money laundering.
💡 Research Summary
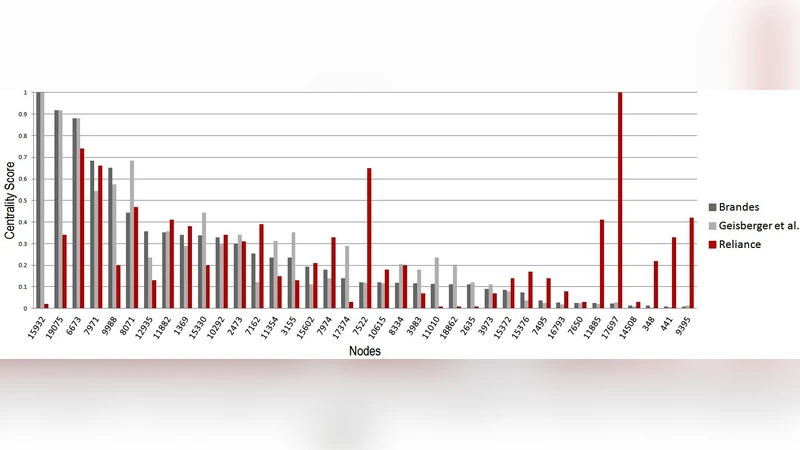
The paper introduces a novel “reliance” measure designed to rank intermediate nodes (i.e., brokers) in a network with respect to a particular source node, such as a criminal suspect. Traditional centrality metrics—most notably betweenness centrality—evaluate a node’s importance by aggregating over all possible source‑target pairs in the entire graph. Consequently, they cannot isolate the nodes that are specifically important to a given suspect. To address this gap, the authors build on the classic pair‑dependency concept (Freeman) and the efficient Brandes algorithm, adding a distance‑based trust factor that reflects the intuition that, in money‑laundering schemes, a source must place greater trust in intermediaries that are farther away in the communication chain.
The reliance of a source s on an intermediate v for a particular destination t is defined as the product of two terms: (1) the importance rate IR(s,t)(v) = σ_st(v)/σ_st, which is the proportion of shortest s‑t paths that pass through v, and (2) the trust factor T(s,t)(v) = µ(s,v)/µ(s,t), where µ denotes shortest‑path distance. Summing R(s,t)(v) = IR·T over all destinations t yields a source‑specific reliance score for each intermediate node. The authors adapt Brandes’ recursive accumulation to incorporate the trust factor, preserving an O(n·m) runtime while focusing computation on a chosen set of source nodes rather than the whole vertex set.
Two real‑world networks are used for validation. In the Enron email corpus, a set of finance managers is treated as the source group. The reliance ranking highlights an employee who was not a finance manager but was later convicted of money‑laundering—a node that traditional betweenness, PageRank, or Markov centrality failed to prioritize. In the Noordin terrorist network, core terrorists are used as sources; reliance scores surface peripheral supporters and financiers that are invisible to standard centrality measures, demonstrating a more pronounced divergence between the two approaches.
The study shows that (i) reliance isolates the broker nodes most critical to a particular suspect, (ii) the distance‑based trust component captures the “layering” characteristic of money‑laundering where longer chains imply higher reliance, and (iii) reliance can uncover hidden actors that conventional global centralities miss. Limitations include reliance on shortest‑path information only—potentially ignoring alternative routes—and the assumption that greater distance always translates to higher trust, which may not hold for all crime types. Future work is suggested to incorporate non‑shortest paths, dynamic temporal weighting, and to test the model on other illicit domains such as cyber‑crime or trafficking.
Comments & Academic Discussion
Loading comments...
Leave a Comment