A Study on Power Side Channels on Mobile Devices
Power side channel is a very important category of side channels, which can be exploited to steal confidential information from a computing system by analyzing its power consumption. In this paper, we demonstrate the existence of various power side channels on popular mobile devices such as smartphones. Based on unprivileged power consumption traces, we present a list of real-world attacks that can be initiated to identify running apps, infer sensitive UIs, guess password lengths, and estimate geo-locations. These attack examples demonstrate that power consumption traces can be used as a practical side channel to gain various confidential information of mobile apps running on smartphones. Based on these power side channels, we discuss possible exploitations and present a general approach to exploit a power side channel on an Android smartphone, which demonstrates that power side channels pose imminent threats to the security and privacy of mobile users. We also discuss possible countermeasures to mitigate the threats of power side channels.
💡 Research Summary
The paper investigates power side channels (PSCs) on Android smartphones, demonstrating that unprivileged applications can obtain fine‑grained power consumption data from the Battery Monitoring Unit (BMU) and use it to infer a variety of sensitive information. The authors employ two measurement approaches: a hardware method using a Monsoon Power Monitor that supplies a constant 4.2 V and records current, and a software method that polls the system files /sys/class/power_supply/battery/voltage_now and current_now to retrieve instantaneous voltage and current values. Experiments are conducted on a Nexus 5 running Android 4.4, and the collected traces reveal four distinct PSCs.
PSC #1 – App Identification: During the loading phase each application exhibits a characteristic power pattern. The authors test three popular apps from different categories (social, e‑commerce, productivity) over more than two dozen runs. The patterns are repeatable across runs and clearly distinguishable between apps, both in hardware‑based and software‑based measurements. This enables a malicious app to infer which foreground app is launching, bypassing the deprecation of getRunningTasks() after Android 5.0.
PSC #2 – UI Inference: Within a single app, different UI states generate distinct power signatures. The study focuses on the Amazon app, collecting traces for the main screen, product detail screen, and login screen. Each UI produces a repeatable pattern that can be recognized by a pattern‑matching algorithm (e.g., Dynamic Time Warping). An attacker can therefore detect when a sensitive UI (such as a login screen) appears, providing a precise trigger for further exploitation.
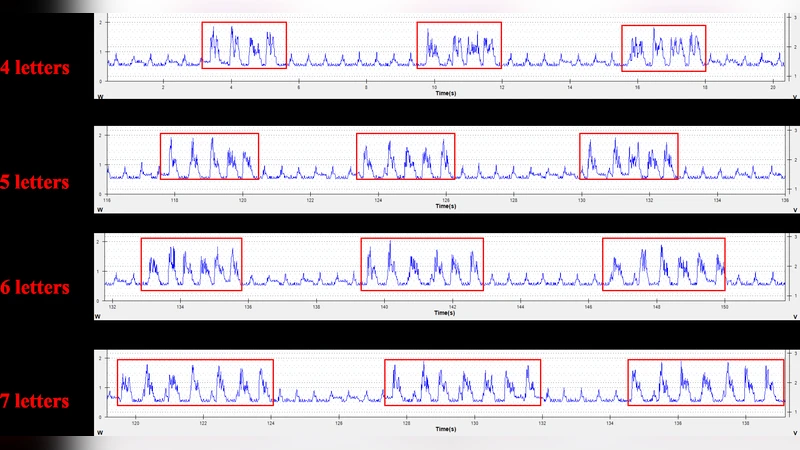
PSC #3 – Password Length Guessing: When a user types a password, each keystroke causes a short, sharp increase in current consumption—a “burst.” By counting these bursts in the power trace, the attacker can reliably determine the password length. Although the actual password characters remain hidden, knowing the length dramatically reduces the search space for offline cracking or dictionary attacks.
PSC #4 – Geo‑location Estimation: Building on prior work (PowerSpy), the authors note that power consumption correlates with radio signal strength and can be used to infer a device’s movement or current location. With a pre‑collected database of location‑specific power signatures, real‑time tracking becomes feasible.
The paper then presents a composite attack scenario that chains PSC #1, PSC #2, and PSC #3. A malicious app first detects the launch of a target app via PSC #1, monitors the power trace to capture the moment the login UI loads (PSC #2), and finally counts the power bursts during password entry to obtain the password length (PSC #3). All steps rely solely on unprivileged access to power data; no special permissions are required. The detection logic can be implemented with lightweight pattern‑matching techniques to minimize additional power consumption and avoid detection.
To mitigate these threats, the authors propose three categories of defenses: (1) tightening OS‑level permissions so that ordinary apps cannot read BMU files; (2) introducing random noise or irregular sampling into power reporting to obscure fine‑grained patterns; and (3) deliberately varying power consumption during sensitive UI transitions (e.g., inserting dummy workloads) to invalidate pre‑learned signatures.
In conclusion, the study shows that power side channels are a practical and potent vector for privacy‑violating attacks on mobile devices. Because power data is universally available on Android devices, PSCs pose a broader risk than previously recognized side channels such as timing, acoustic, or electromagnetic emissions. Future work should explore cross‑device reproducibility, develop machine‑learning models for automated power‑pattern classification, and evaluate the effectiveness of real‑time defensive mechanisms in realistic user environments.
Comments & Academic Discussion
Loading comments...
Leave a Comment