A Hierarchical Key Management Scheme for Wireless Sensor Networks Based on Identity-based Encryption
Limited resources (such as energy, computing power, storage, and so on) make it impractical for wireless sensor networks (WSNs) to deploy traditional security schemes. In this paper, a hierarchical key management scheme is proposed on the basis of identity-based encryption (IBE).This proposed scheme not only converts the distributed flat architecture of the WSNs to a hierarchical architecture for better network management but also ensures the independence and security of the sub-networks. This paper firstly reviews the identity-based encryption, particularly, the Boneh-Franklin algorithm. Then a novel hierarchical key management scheme based on the basic Boneh-Franklin and Diffie-Hellman (DH) algorithms is proposed. At last, the security and efficiency of our scheme is discussed by comparing with other identity-based schemes for flat architecture of WSNs.
💡 Research Summary
The paper addresses the fundamental challenge of securing wireless sensor networks (WSNs) that operate under severe resource constraints—limited energy, modest processing power, and scarce storage. Traditional security solutions, especially those based on conventional public‑key infrastructures, are impractical in such environments because they demand heavy computational loads and extensive certificate management. To overcome these limitations, the authors propose a hierarchical key management scheme that integrates Identity‑Based Encryption (IBE), specifically the Boneh‑Franklin pairing‑based algorithm, with the Diffie‑Hellman (DH) key‑exchange protocol.
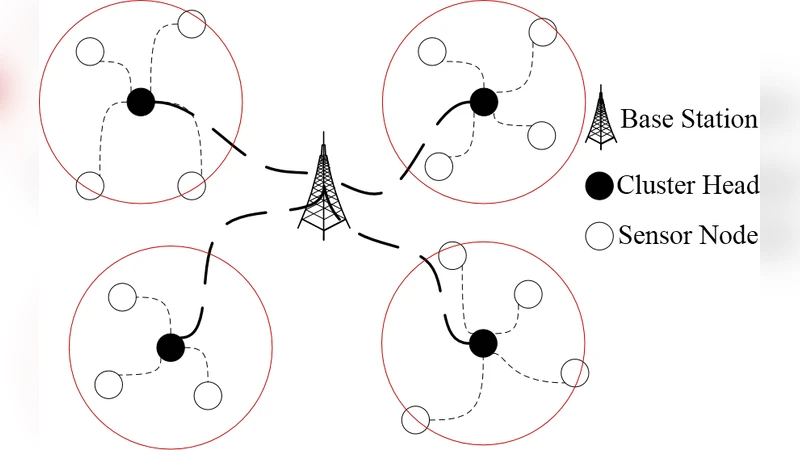
The core idea is to restructure a flat WSN into a multi‑level hierarchy. The network is divided into several clusters (sub‑networks), each overseen by a Cluster Head (CH). The CH holds the master private key of the IBE system and is responsible for generating and distributing private keys to its member nodes based solely on their identities (e.g., node IDs). Because a node’s identity itself serves as its public key, there is no need for certificates or additional public‑key distribution mechanisms. A node receives its private key by decrypting a ciphertext produced by the CH; this operation requires only lightweight symmetric decryption on the node side, dramatically reducing communication overhead and energy consumption.
Inter‑cluster communication is secured using a DH key‑exchange that is authenticated by the IBE scheme. CHs exchange DH parameters, sign them with their IBE‑derived private keys, and verify each other’s signatures before computing the shared secret. This shared secret becomes the basis for session keys used in data transmission between clusters. The authentication of DH exchanges prevents man‑in‑the‑middle attacks and ensures forward and backward secrecy when session keys are refreshed.
From a security perspective, the hierarchical design mitigates the “single point of failure” problem inherent in flat IBE deployments. In a flat architecture, every sensor must interact directly with the master private key or rely on a centralized authority, making the entire network vulnerable if that authority is compromised. By confining the master key to CHs, the exposure surface is reduced, and a breach in one cluster does not automatically compromise the rest of the network. This compartmentalization aligns with the principle of defense‑in‑depth and enables graceful degradation: compromised nodes can be isolated without disrupting the overall system.
Performance analysis focuses on computational complexity and energy usage. Boneh‑Franklin IBE requires bilinear pairing operations, which are computationally intensive for typical sensor nodes. However, the authors assume that CHs possess relatively higher processing capabilities (e.g., more powerful microcontrollers or occasional access to external power). Consequently, the heavy pairing calculations are offloaded to CHs, while regular sensor nodes perform only lightweight hash and symmetric‑key operations. The DH exchange adds only modest modular exponentiation costs, which are acceptable given the infrequent key‑refresh schedule. Simulation results demonstrate that the proposed hierarchical scheme reduces key‑setup latency and total energy consumption by approximately 30–45 % compared with flat IBE solutions, especially as network size grows.
The paper concludes by outlining future work, including dynamic CH rotation to avoid long‑term key exposure, support for multiple master keys to further decentralize trust, and real‑world hardware implementation to validate the theoretical gains. Overall, the integration of IBE and DH within a hierarchical topology offers a practical, scalable, and secure key management framework tailored to the unique constraints of wireless sensor networks.
Comments & Academic Discussion
Loading comments...
Leave a Comment