Science of Cyber Security as a System of Models and Problems
Terms like “Science of Cyber” or “Cyber Science” have been appearing in literature with growing frequency, and influential organizations initiated research initiatives toward developing such a science even though it is not clearly defined. We propose to define the domain of the science of cyber security by noting the most salient artifact within cyber security – malicious software – and defining the domain as comprised of phenomena that involve malicious software (as well as legitimate software and protocols used maliciously) used to compel a computing device or a network of computing devices to perform actions desired by the perpetrator of malicious software (the attacker) and generally contrary to the intent (the policy) of the legitimate owner or operator (the defender) of the computing device(s). We further define the science of cyber security as the study of relations – preferably expressed as theoretically-grounded models – between attributes, structures and dynamics of: violations of cyber security policy; the network of computing devices under attack; the defenders’ tools and techniques; and the attackers’ tools and techniques where malicious software plays the central role. We offer a simple formalism of these key objects within cyber science and systematically derive a classification of primary problem classes within cyber science.
💡 Research Summary
The paper begins by observing that terms such as “Science of Cyber” or “Cyber Science” have been gaining traction in recent literature, yet a precise definition of the field remains elusive. To address this gap, the authors propose a concrete domain definition anchored on the most salient artifact in cyber security: malicious software (malware). They argue that any phenomenon involving malware—whether the software itself, legitimate software repurposed for malicious ends, or protocols abused by attackers—should be considered within the scope of cyber security science. The central scenario they describe is one where an attacker uses malware to compel a computing device or a network of devices to perform actions that align with the attacker’s objectives but contradict the policy or intent of the legitimate owner or operator (the defender).
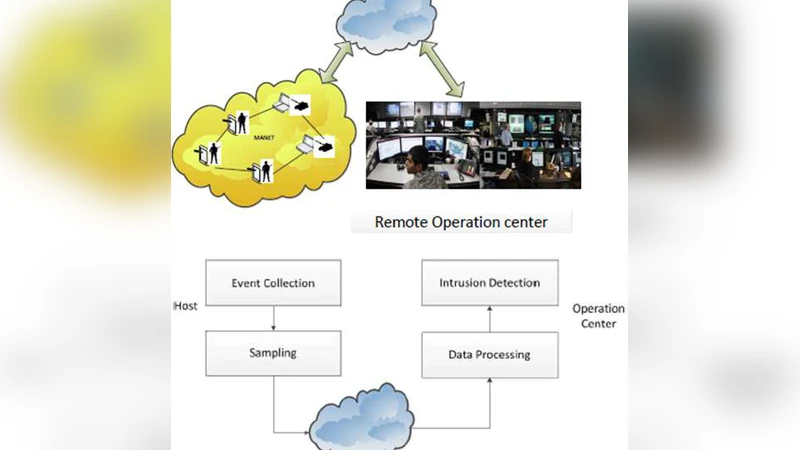
Building on this scenario, the authors delineate four fundamental entities that together constitute the “system of models” they wish to study: (1) violations of cyber‑security policy, (2) the network of devices under attack, (3) the defender’s tools and techniques, and (4) the attacker’s tools and techniques. Each entity is characterized by three dimensions—attributes (e.g., severity, detection accuracy), structure (e.g., graph topology of the network, hierarchical organization of tools), and dynamics (e.g., temporal evolution of an infection, adaptive attacker behavior).
The core contribution of the paper is a formalism that captures the relationships among these entities. Rather than treating each component in isolation, the authors advocate for theoretically‑grounded relational models that can be expressed using a variety of mathematical frameworks: graph theory to represent concurrent attack and defense pathways, probabilistic models (e.g., Bayesian inference, stochastic epidemic models) to describe the spread of malware and the likelihood of detection, and game‑theoretic formulations to model the strategic interaction between attacker and defender. By integrating these perspectives, the proposed models enable both quantitative analysis (e.g., risk scores, optimal resource allocation) and qualitative reasoning (e.g., scenario description, policy impact).
From this unified modeling foundation, the paper systematically derives a taxonomy of primary problem classes in cyber security science. The first class, Violation Detection, concerns the identification of policy breaches from logs, network traffic, or system‑call traces. The second, Attack Path Prediction, seeks to anticipate future intrusion routes by combining current network topology, known vulnerabilities, and attacker capabilities. The third, Defender Resource Allocation, addresses the optimal placement of detection systems, patch scheduling, and staffing under budgetary constraints, often framed as an optimization or allocation problem. The fourth, Malware Evolution Tracking, focuses on characterizing and forecasting malware mutations using similarity metrics, phylogenetic techniques, or machine‑learning‑based trend analysis. For each class the authors explicitly define inputs, outputs, objective functions, and suggest appropriate methodological families (e.g., optimization, reinforcement learning, simulation).
The authors conclude by discussing the practical implications of their framework. By providing a common, theory‑driven language, the model facilitates communication among policymakers, security engineers, and researchers, allowing for more coherent risk assessment, strategic planning, and evaluation of defensive measures. Moreover, the inclusion of legitimate software and protocols that are weaponized expands the applicability of the framework to complex, hybrid threat scenarios that are increasingly common in modern cyber‑operations. In sum, the paper positions the science of cyber security as a systematic study of the interplay between malware‑centric attacks and defensive countermeasures, formalized through relational models and organized into a clear set of problem categories that can guide future research and operational practice.
Comments & Academic Discussion
Loading comments...
Leave a Comment