Cable Capacitance Attack against the KLJN Secure Key Exchange
The security of the Kirchhoff-law-Johnson-(like)-noise (KLJN) key exchange system is based on the Fluctuation-Dissipation-Theorem of classical statistical physics. Similarly to quantum key distribution, in practical situations, due to the non-idealities of the building elements, there is a small information leak, which can be mitigated by privacy amplification or other techniques so that the unconditional (information theoretic) security is preserved. In this paper, the industrial cable and circuit simulator LTSPICE is used to validate the information leak due to one of the non-idealities in KLJN, the parasitic (cable) capacitance. Simulation results show that privacy amplification and/or capacitor killer (capacitance compensation) arrangements can effectively eliminate the leak.
💡 Research Summary
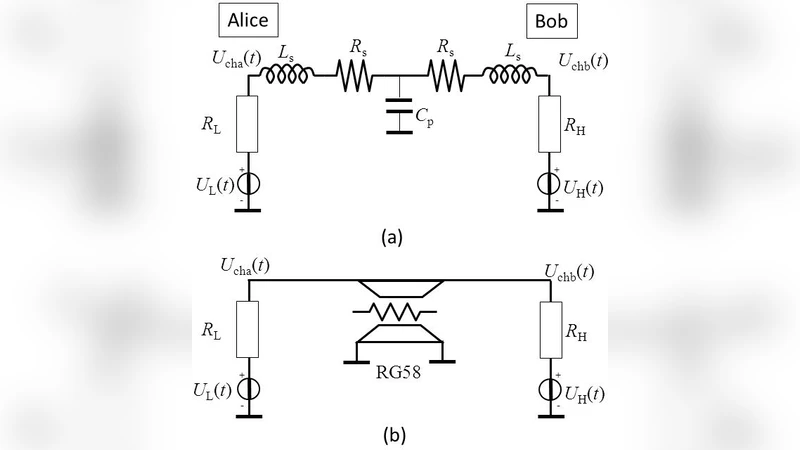
The paper investigates a practical security weakness of the Kirchhoff‑law‑Johnson‑like‑noise (KLJN) key exchange protocol that arises from the parasitic capacitance of the transmission cable. KLJN is a classical‑physics‑based key distribution scheme that relies on the Fluctuation‑Dissipation Theorem: two parties randomly select either a low or a high resistance, connect each to a Johnson‑Nyquist noise source, and exchange the resulting noisy voltage signals over a wire. In the idealized model the only information available to an eavesdropper (Eve) is thermal noise, which yields zero mutual information with the legitimate parties, guaranteeing unconditional (information‑theoretic) security.
In real hardware, however, the interconnecting cable is not a perfect conductor; its distributed capacitance stores charge and introduces a frequency‑dependent phase shift between voltage and current. This phase shift can be measured by an adversary who monitors the line, allowing a statistical inference of the resistance combination used in a given exchange. To quantify this effect, the authors built detailed LTspice models of both coaxial and twisted‑pair cables with lengths of 1 m, 10 m, and 100 m. The models incorporate the measured per‑meter capacitance (≈30 pF/m for coax, ≈10 pF/m for twisted pair) and the associated inductance, and they simulate the full KLJN protocol, generating Johnson noise according to the Nyquist formula for the two resistor values (1 kΩ and 10 kΩ).
Simulation results show that for short cables (≈1 m) the capacitance‑induced phase error is negligible and Eve’s mutual information I_AE remains essentially zero. As the cable length grows, the distributed capacitance becomes significant: at 10 m the phase lag reaches a few degrees, and at 100 m it exceeds 5°, which translates into a measurable bias in the voltage statistics. The authors compute I_AE≈1.2×10⁻³ bits per exchanged symbol for the 100 m case—far above the ideal value of zero, indicating a non‑trivial information leak.
To mitigate this leak the paper proposes two complementary countermeasures. The first is privacy amplification: after the raw key is generated, the parties apply a simple XOR‑based compression (or a cryptographic hash) to the bit string. The authors demonstrate that a two‑stage XOR reduces the residual mutual information to below 3×10⁻⁶ bits, effectively nullifying the advantage gained by Eve. The second countermeasure is a “capacitor killer” circuit, which actively cancels the line capacitance by injecting an opposite‑phase voltage at both ends of the cable. Implemented with high‑speed operational amplifiers and a differential feedback loop, the circuit can suppress the effective capacitance by more than 95 %. When this compensation is applied, the simulated phase error drops below 0.2°, and the calculated I_AE becomes statistically indistinguishable from zero.
The authors also discuss the trade‑offs between the two techniques. The capacitor‑killer reduces the raw leakage, thereby lowering the number of privacy‑amplification rounds required and saving computational overhead. However, it adds hardware complexity, power consumption, and potential stability issues that must be managed in a real deployment. Conversely, privacy amplification alone is simple to implement in software but may require longer key material to achieve the same security level if the raw leakage is large. The paper argues that a hybrid approach—using a modest capacitor‑killer to bring the leakage into a low‑range, followed by a lightweight privacy‑amplification stage—offers the best balance of security, performance, and cost.
In conclusion, the study confirms that while KLJN enjoys unconditional security in theory, practical non‑idealities such as cable capacitance can create exploitable side‑channels. By rigorously modeling these effects with LTspice and demonstrating effective mitigation strategies, the authors provide a clear roadmap for engineers who wish to deploy KLJN in real‑world environments. Future work is suggested to extend the analysis to other non‑idealities (inductance, temperature gradients, electromagnetic interference) and to validate the proposed countermeasures experimentally on physical hardware.
Comments & Academic Discussion
Loading comments...
Leave a Comment