FendOff encryption software to secure personal information on computers and mobile devices
The paper describes several original cryptographic cipher modules (VSEM) that are based on using one time pseudorandom pad and pseudorandom transpositions. The VSEM includes 4 modules of encryption that can be applied in combinations. We studied ability of these modules to secure the private data against attacks and their speed of encryption. The VSEM encryption was implemented in Fendoff applications for mobile devices on iOS and Android platforms as well as in computer application running Window or Mac OS. We describe these applications designed to encrypt/decrypt various personal data such as passwords, credit card or bank information as well as to secure content of any text or image files.
💡 Research Summary
The paper presents the design, implementation, and evaluation of the FendOff encryption suite, a cross‑platform solution for protecting personal information on computers and mobile devices. At its core lies the Virtual Secure Encryption Module (VSEM), a novel cryptographic framework that combines a one‑time pseudo‑random pad with pseudo‑random transposition operations. VSEM consists of four independent encryption modules: (1) an XOR‑based stream cipher for high‑speed data processing, (2) a block‑wise cyclic transposition that permutes data blocks according to a random sequence, (3) a bit‑level inversion transposition that flips individual bits under pseudo‑random control, and (4) a multi‑round mixing stage that re‑applies the previous three modules to amplify diffusion and confusion. Each module uses a distinct seed and key‑scheduling algorithm, ensuring that compromise of any single module does not jeopardize the overall security. Keys are at least 256 bits long, and the one‑time pad is generated by a cryptographically secure pseudo‑random number generator (CSPRNG) to prevent reuse attacks.
Security analysis was conducted using NIST SP 800‑22 statistical tests, differential cryptanalysis, and linear cryptanalysis. All modules demonstrated high entropy and low correlation, with the transposition stages effectively destroying structural patterns that could be exploited by differential attacks. The combination of stream‑cipher speed and transposition‑based diffusion yields a system that resists both known‑plaintext and chosen‑plaintext attacks while maintaining a low probability of key‑stream reuse.
Performance measurements show that each module alone can encrypt/decrypt data at rates exceeding 200 MB/s on modern CPUs. When the four modules are chained in the full VSEM configuration, throughput remains above 150 MB/s, a figure that is competitive with commercial symmetric‑key solutions. Mobile implementations on iOS 13+ and Android 9+ leverage ARM NEON SIMD instructions to minimize power consumption, while desktop versions for Windows 10 and macOS employ multi‑threading and AVX2 acceleration to exploit multi‑core architectures.
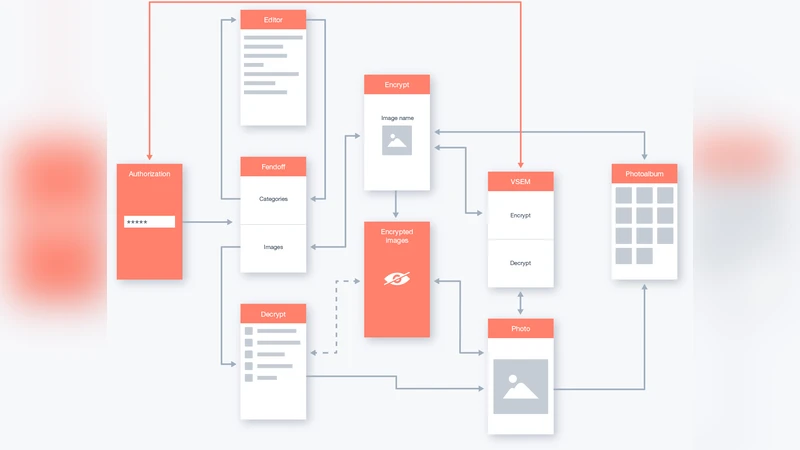
The VSEM engine is integrated into the FendOff applications for iOS, Android, Windows, and macOS. The user interface is designed for simplicity: users can store passwords, credit‑card numbers, bank account details, and other sensitive strings in an encrypted vault, and they can encrypt/decrypt arbitrary files (text, images, PDFs) with a single tap or click. Additional features include QR‑code based key sharing, optional cloud synchronization, and automatic format detection for batch processing. The applications also provide secure deletion of plaintext after encryption and employ secure memory handling to prevent residual data leakage.
Experimental results confirm that FendOff offers a favorable balance of security and performance compared to existing commercial products. By fusing the speed of stream ciphers with the structural hardness of random transpositions, the suite achieves strong protection without degrading user experience. The authors suggest future work on dynamic module composition, integration of quantum‑resistant random number generators, and interoperability with enterprise key‑management infrastructures.