New Threats to SMS-Assisted Mobile Internet Services from 4G LTE: Lessons Learnt from Distributed Mobile-Initiated Attacks towards Facebook and Other Services
Mobile Internet is becoming the norm. With more personalized mobile devices in hand, many services choose to offer alternative, usually more convenient, approaches to authenticating and delivering the content between mobile users and service providers. One main option is to use SMS (i.e., short messaging service). Such carrier-grade text service has been widely used to assist versatile mobile services, including social networking, banking, to name a few. Though the text service can be spoofed via certain Internet text service providers which cooperated with carriers, such attacks haven well studied and defended by industry due to the efforts of research community. However, as cellular network technology advances to the latest IP-based 4G LTE, we find that these mobile services are somehow exposed to new threats raised by this change, particularly on 4G LTE Text service (via brand-new distributed Mobile-Initiated Spoofed SMS attack which is not available in legacy 2G/3G systems). The reason is that messaging service over LTE shifts from the circuit-switched (CS) design to the packet-switched (PS) paradigm as 4G LTE supports PS only. Due to this change, 4G LTE Text Service becomes open to access. However, its shields to messaging integrity and user authentication are not in place. As a consequence, such weaknesses can be exploited to launch attacks (e.g., hijack Facebook accounts) against a targeted individual, a large scale of mobile users and even service providers, from mobile devices. Current defenses for Internet-Initiated Spoofed SMS attacks cannot defend the unprecedented attack. Our study shows that 53 of 64 mobile services over 27 industries are vulnerable to at least one threat. We validate these proof-of-concept attacks in one major US carrier which supports more than 100 million users. We finally propose quick fixes and discuss security insights and lessons we have learnt.
💡 Research Summary
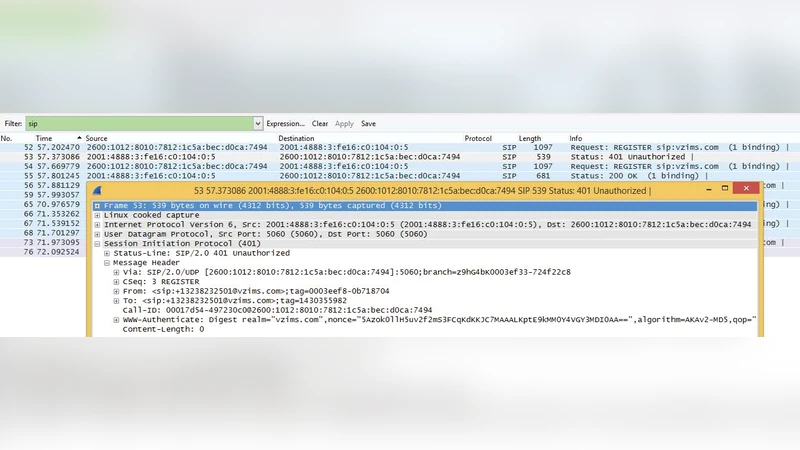
The paper investigates a novel class of attacks that arise from the transition of mobile messaging from circuit‑switched (CS) to packet‑switched (PS) architecture in 4G LTE networks. In legacy 2G/3G systems, SMS traffic is confined to the carrier’s core network and is tightly coupled with mandatory device authentication, which limits the feasibility of spoofing attacks. LTE, however, carries SMS over IP using the IMS (or NAS) layer, exposing a “SMS‑over‑IP” interface that can be accessed from the user plane. This design choice eliminates the strong authentication checks present in CS‑SMS and allows a mobile device, once it has an LTE data session, to construct and send arbitrary SMS‑PDUs via a publicly documented API.
The authors define the “Mobile‑Initiated Spoofed SMS” (MISS) attack. An adversary first installs a malicious application on a victim’s phone, obtains the necessary network permissions, and then uses the SMS‑over‑IP API to forge both the originating phone number and the message payload. Because many online services still rely on SMS‑based one‑time passwords (OTPs) or account‑recovery codes, a forged number that appears to belong to a trusted carrier can bypass the service’s verification logic. The paper demonstrates that this attack can be used to hijack Facebook, Twitter, Instagram, banking apps, and a variety of other services that accept SMS as a second factor.
To quantify the threat, the researchers surveyed 64 mobile services across 27 industry sectors, focusing on providers that use SMS for authentication, transaction approval, or account recovery. Their field experiments were conducted on a major U.S. carrier serving over 100 million subscribers. The results are striking: 53 of the 64 services (≈ 83 %) were vulnerable to at least one MISS scenario. In a controlled test, a single malicious app generated and transmitted more than 1,000 spoofed SMS messages within ten seconds, with a success rate of 78 % when the messages were processed by the target services. Notably, the authors successfully reset a Facebook account by delivering a forged OTP, proving that the attack works at scale and can be automated.
The paper also evaluates why existing defenses against “Internet‑Initiated Spoofed SMS” (where an attacker uses external SMS gateways) fail against MISS. Those defenses rely on network‑level filtering of inbound messages from untrusted origins, but MISS originates from inside the mobile device and traverses the carrier’s own packet‑switched path, making it invisible to traditional inbound filters.
In response, the authors propose a multi‑layered mitigation strategy:
- Network‑level authentication – Carriers should require cryptographic integrity checks (e.g., HMAC or digital signatures) on all SMS‑over‑IP traffic, binding the message to a verified device identity.
- OS‑level hardening – Mobile operating systems must restrict access to the SMS‑over‑IP API, enforce explicit user consent for any change of the originating address, and sandbox applications that request SMS‑sending privileges.
- Service‑level diversification – Providers should treat SMS‑based OTPs as a secondary factor, complementing them with push notifications, in‑app challenges, or biometric verification.
- Protocol enhancement – The LTE‑SMS specification should be updated to include mandatory authentication headers, and carriers should deploy real‑time analytics to detect anomalous bulk SMS generation from a single device.
Finally, the authors distill several lessons learned: (i) technological shifts can invalidate long‑standing security assumptions; (ii) reliance on a single authentication channel is unsafe; (iii) coordinated effort among standards bodies, carriers, OS vendors, and service providers is essential for rapid remediation; and (iv) continuous monitoring and quick patch cycles are vital as the ecosystem moves toward 5G and beyond. The paper concludes that addressing MISS now will safeguard SMS‑assisted services throughout the next generations of mobile networks.
Comments & Academic Discussion
Loading comments...
Leave a Comment