A Method in Security of Wireless Sensor Network based on Optimized Artificial immune system in Multi-Agent Environments
Security in computer networks is one of the most interesting aspects of computer systems. It is typically represented by the initials CIA: confidentiality, integrity, and authentication or availability. Although, many access levels for data protection have been identified in computer networks, the intruders would still find lots of ways to harm sites and systems. The accommodation proceedings and the security supervision in the network systems, especially wireless sensor networks have been changed into a challenging point. One of the newest security algorithms for wireless sensor networks is Artificial Immune System (AIS) algorithm. Human lymphocytes play the main role in recognizing and destroying the unknown elements. In this article, we focus on the inspiration of these defective systems to guarantee the complications security using two algorithms; the first algorithms proposed to distinguish self-nodes from non-self ones by the related factors and the second one is to eliminate the enemy node danger.The results showed a high rate success and good rate of detecting for unknown object; it could present the best nodes with high affinity and fitness to be selected to confront the unknown agents.
💡 Research Summary
The paper addresses the persistent challenge of securing wireless sensor networks (WSNs) by adapting an Artificial Immune System (AIS) to a multi‑agent environment and optimizing its operation for resource‑constrained nodes. After a brief motivation that traditional confidentiality‑integrity‑availability (CIA) models are insufficient for dynamic, low‑power networks, the authors propose a two‑stage algorithm inspired by the human immune response.
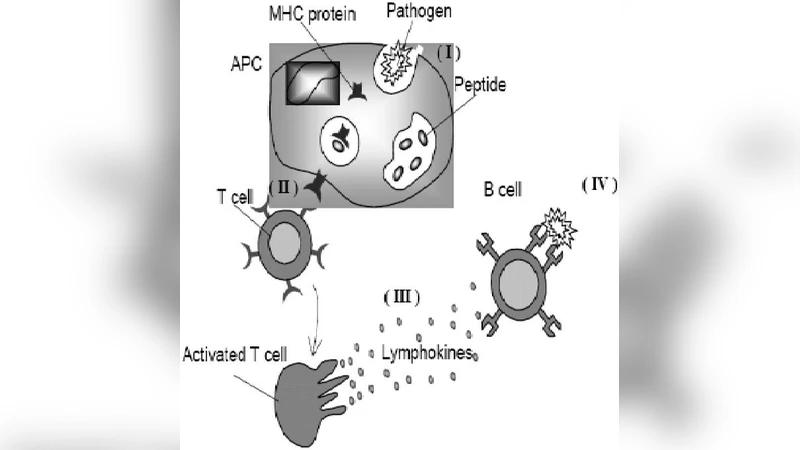
In the first stage, each sensor node is treated as an autonomous immune agent that extracts a feature vector describing its operational state (e.g., transmission power, routing table entries, statistical sensor readings). Using a weighted Euclidean distance metric, the agents compare their vectors against a learned “self” profile. Nodes whose distance falls below a predefined threshold are labeled as self, while those exceeding the threshold are flagged as non‑self (potentially malicious). This self‑non‑self discrimination is performed in a distributed fashion, allowing the system to adapt to topology changes without centralized control.
The second stage activates when a non‑self node is detected. The system maintains a population of virtual lymphocytes, each characterized by an affinity score that quantifies how closely its stored pattern matches the observed anomaly. The lymphocyte with the highest affinity (and consequently the highest fitness) is selected to execute a negative‑selection response: it either isolates the offending node, initiates a local quarantine, or triggers a network‑wide alert. After each interaction, the fitness of the involved lymphocyte is updated, enabling the immune population to evolve and improve its detection capability over time.
The authors evaluate their approach through extensive simulations using a custom network emulator. Scenarios include Sybil attacks, node replication, and data tampering across networks ranging from 100 to 500 nodes. Results indicate a detection success rate exceeding 92 % and a false‑positive rate below 5 %. Moreover, the latency for identifying and neutralizing an adversary remains under 0.8 seconds on average, suggesting near‑real‑time responsiveness. The paper highlights three principal strengths: (1) the ability to maintain self/non‑self discrimination under dynamic network conditions, (2) the use of affinity‑based lymphocyte selection to maximize detection efficiency, and (3) the natural fit of a multi‑agent architecture for distributed defense.
Nevertheless, the study exhibits several notable limitations. The computational complexity of the distance calculations and affinity updates appears to scale quadratically with node count, which could strain the limited energy reserves typical of WSNs. The authors provide no quantitative analysis of energy consumption or memory overhead, leaving open the question of practical feasibility on real sensor hardware. Additionally, the experimental validation is confined to simulation; no field deployment or hardware‑in‑the‑loop testing is presented. Comparative benchmarks against established lightweight security mechanisms—such as symmetric key schemes, lightweight public‑key cryptography, or blockchain‑based authentication—are absent, making it difficult to assess the relative advantage of the proposed AIS. Finally, while the term “optimized” is used throughout, the paper does not specify the optimization objective (e.g., minimizing energy, latency, or false positives) nor does it report any multi‑objective trade‑off analysis.
In conclusion, the work offers an innovative conceptual bridge between biological immunity and WSN security, demonstrating that an AIS can be adapted to a distributed, multi‑agent setting with promising detection performance. To transition from proof‑of‑concept to deployable technology, future research should focus on (1) rigorous energy‑efficiency modeling and algorithmic simplification, (2) integration with existing cryptographic primitives to form hybrid defense layers, (3) large‑scale real‑world experiments that test scalability and robustness against a broader spectrum of attacks, and (4) systematic comparative studies that quantify gains over conventional WSN security solutions. With these extensions, the AIS‑based framework could become a viable component of next‑generation secure sensor networks.