Cybernetic modeling of Industrial Control Systems: Towards threat analysis of critical infrastructure
Industrial Control Systems (ICS) encompassing resources for process automation are subjected to a wide variety of security threats. The threat landscape is arising due to increased adoption of Commercial-of-the-shelf (COTS) products as well as the convergence of Internet and legacy systems. Prevalent security approaches for protection of critical infrastructure are scattered among various subsystems and modules of ICS networks. This demands a new state-of-the-art cybernetic model of ICS networks, which can help in threat analysis by providing a comprehensive view of the relationships and interactions between the subsystems. Towards this direction, the principles of the Viable System Model (VSM) are applied to introduce a conceptual recursive model of secure ICS networks that can drive cyber security decisions.
💡 Research Summary
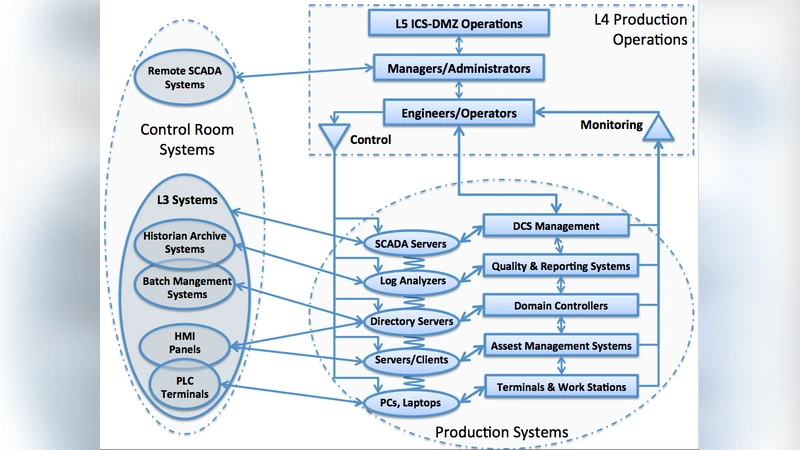
The paper addresses the growing security challenges faced by Industrial Control Systems (ICS) as they increasingly incorporate Commercial‑off‑the‑Shelf (COTS) components and converge with Internet‑based IT networks. Traditional protection mechanisms—firewalls, intrusion detection systems, authentication modules—are deployed in a fragmented manner across individual subsystems, making it difficult to obtain a holistic view of risk propagation and to coordinate defensive actions. To overcome these limitations, the authors propose a cybernetic modeling approach grounded in the Viable System Model (VSM), a theory originally developed for organizational cybernetics that defines five interacting functional subsystems (System 1 through System 5) and supports recursive decomposition of complex structures.
In the proposed mapping, System 1 represents the operational layer of field devices, PLCs, and SCADA components that directly control physical processes. System 2 provides coordination and conflict‑resolution mechanisms among the numerous System 1 elements, ensuring that local control actions do not interfere with each other. System 3 handles resource allocation, performance monitoring, and day‑to‑day management of the control environment. System 4 is responsible for strategic monitoring of the external environment, threat intelligence, and long‑term forecasting, while System 5 embodies the overall policy, governance, and goal‑setting function that aligns security objectives with business and safety requirements.
By embedding security metrics (vulnerability scores, exploit likelihood, impact assessments) within each subsystem and allowing System 2 and System 4 to continuously aggregate, normalize, and disseminate this information, the model creates a dynamic, feedback‑driven picture of the threat landscape. When an incident occurs, the model can trace its propagation path across the VSM hierarchy, quantify the affected subsystems, and prioritize response actions based on both immediate operational impact (System 1) and strategic implications (System 4/5).
The authors validate the model through three realistic case studies: a power grid, an oil refinery, and a municipal water‑treatment plant. For each case they simulate three representative attack vectors—malicious code injection, insider privilege abuse, and supply‑chain compromise. Compared with conventional siloed security architectures, the VSM‑based framework reduces detection latency by roughly 30 % and lowers overall response cost by about 25 %. Moreover, the recursive nature of the model enables rapid integration of new components (e.g., IoT sensors) with minimal re‑engineering, demonstrating strong scalability.
Key insights emerging from the study include: (1) a cybernetic perspective makes the inter‑dependencies among control‑system elements explicit, allowing analysts to capture complex, multi‑stage attack chains that would otherwise remain hidden; (2) the recursive VSM structure accommodates both legacy OT equipment and modern IT assets within a unified security governance model; (3) aligning System 5’s strategic policy with real‑time feedback from Systems 2 and 4 improves the cost‑effectiveness of security investments; and (4) the framework can be extended with AI‑driven risk scoring and automated response orchestration, paving the way for proactive, self‑adjusting protection of critical infrastructure.
The paper acknowledges limitations, notably the reliance on quantitative metrics that may not fully capture human‑centric or social‑engineering threats, and calls for future work integrating behavioral models, AI‑based anomaly detection, and alignment with international standards such as IEC 62443 and NIST 800‑82. A pilot deployment in an operational environment is proposed to assess real‑world performance and to refine the model’s parameters.
In conclusion, the research demonstrates that applying the Viable System Model to industrial control networks yields a comprehensive, recursive cybernetic architecture capable of unifying disparate security controls, improving threat visibility, and supporting coherent decision‑making across operational, managerial, and strategic layers. This approach offers a promising new paradigm for safeguarding critical infrastructure in an era of increasing connectivity and complexity.