Tandem Coding and Cryptography on Wiretap Channels: EXIT Chart Analysis
Traditional cryptography assumes an eavesdropper receives an error-free copy of the transmitted ciphertext. Wyner’s wiretap channel model recognizes that at the physical layer both the intended receiver and the passive eavesdropper inevitably receive an error-prone version of the transmitted message which must be corrected prior to decryption. This paper considers the implications of using both channel and cryptographic codes under the wiretap channel model in a way that enhances the \emph{information-theoretic} security for the friendly parties by keeping the information transfer to the eavesdropper small. We consider a secret-key cryptographic system with a linear feedback shift register (LFSR)-based keystream generator and observe the mutual information between an LFSR-generated sequence and the received noise-corrupted ciphertext sequence under a known-plaintext scenario. The effectiveness of a noniterative fast correlation attack, which reduces the search time in a brute-force attack, is shown to be correlated with this mutual information. For an iterative fast correlation attack on this cryptographic system, it is shown that an EXIT chart and mutual information are very good predictors of decoding success and failure by a passive eavesdropper.
💡 Research Summary
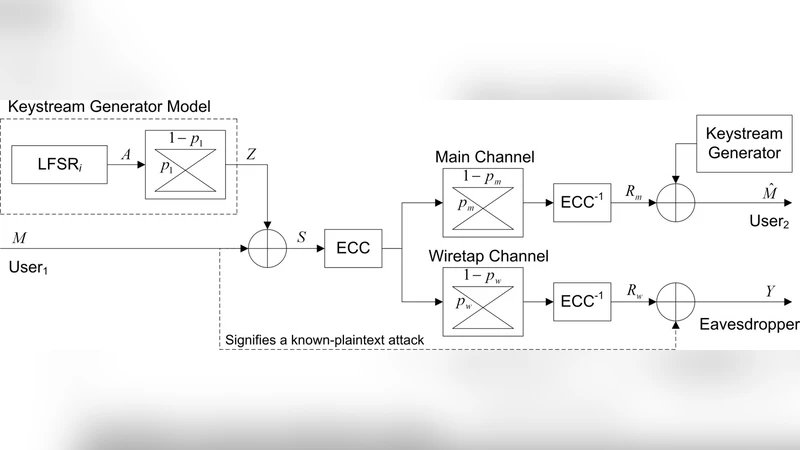
This paper investigates how the physical‑layer characteristics of a Wyner wiretap channel can be exploited to strengthen the information‑theoretic security of a conventional secret‑key cryptosystem when channel coding and stream encryption are applied in tandem. The authors consider a secret‑key system that generates a keystream with a linear feedback shift register (LFSR) and encrypts a known plaintext by XORing it with the keystream. The ciphertext is then encoded with a forward error‑correction code (e.g., LDPC or Polar) and transmitted over two independent binary symmetric channels: a relatively clean channel to the legitimate receiver (Bob) and a noisier channel to a passive eavesdropper (Eve).
The core analytical tool is the mutual information (I(s; y)) between the LFSR output sequence (s) and the noise‑corrupted ciphertext sequence (y) observed by Eve. By modeling the eavesdropper’s channel as a BSC with crossover probability (p_E), the authors derive a closed‑form expression that links (I(s; y)) to the binary entropy function (H_2(p_E)) and the LFSR length (k). This relationship shows that as (p_E) increases, the mutual information drops sharply, which directly inflates the complexity of a non‑iterative fast correlation attack (FCA). Specifically, the attack’s expected work factor scales as (2^{k(1-H_2(p_E))}); therefore, modest physical noise can render the attack infeasible even for modestly sized LFSRs.
For iterative attacks, the paper introduces EXIT (Extrinsic Information Transfer) chart analysis. Each iteration of an iterative FCA consists of a soft‑decision decoding step that exchanges extrinsic information between a channel decoder and a cryptographic decoder. By plotting the input mutual information versus the output mutual information for both decoders, the authors obtain two curves whose intersection (or lack thereof) predicts convergence. Simulation results reveal a clear threshold crossover probability (p_{th}): when (p_E < p_{th}) the EXIT curves intersect, the iterative decoder converges, and Eve successfully recovers the keystream; when (p_E > p_{th}) the curves remain disjoint, the decoder diverges, and the attack fails. The threshold depends on the chosen channel code; LDPC codes with lower rates produce higher (p_{th}) (i.e., stronger security) than higher‑rate Polar codes.
The paper also discusses how to design the tandem system. By selecting a low‑rate, strong error‑correcting code, the legitimate receiver can correct almost all errors (target BER ≈ 10⁻⁴), while the residual errors left for Eve are sufficient to drive (I(s; y)) below the attack’s success region. This design creates a trade‑off between transmission efficiency (code rate) and security (residual error level). The authors provide numerical examples with a 128‑bit LFSR, showing that for LDPC (rate ½) the non‑iterative FCA succeeds only when (p_E ≤ 0.07), while the iterative FCA fails for (p_E ≥ 0.09). For Polar (rate ¾) the corresponding thresholds are slightly higher, reflecting weaker physical‑layer protection.
In conclusion, the study demonstrates that physical‑layer noise, when properly quantified through mutual information and visualized via EXIT charts, can be harnessed to augment the security of conventional cryptographic primitives. The combined analysis offers a practical methodology for engineers designing next‑generation wireless systems (5G/6G, IoT) where low‑complexity LFSR‑based stream ciphers and lightweight channel codes are attractive. Future work is suggested on multi‑antenna wiretap models, non‑binary modulation, and integration with post‑quantum stream ciphers, aiming to broaden the applicability of the tandem coding‑cryptography paradigm.
Comments & Academic Discussion
Loading comments...
Leave a Comment