Physical-Layer Security: Combining Error Control Coding and Cryptography
In this paper we consider tandem error control coding and cryptography in the setting of the {\em wiretap channel} due to Wyner. In a typical communications system a cryptographic application is run at a layer above the physical layer and assumes the channel is error free. However, in any real application the channels for friendly users and passive eavesdroppers are not error free and Wyner’s wiretap model addresses this scenario. Using this model, we show the security of a common cryptographic primitive, i.e. a keystream generator based on linear feedback shift registers (LFSR), can be strengthened by exploiting properties of the physical layer. A passive eavesdropper can be made to experience greater difficulty in cracking an LFSR-based cryptographic system insomuch that the computational complexity of discovering the secret key increases by orders of magnitude, or is altogether infeasible. This result is shown for two fast correlation attacks originally presented by Meier and Staffelbach, in the context of channel errors due to the wiretap channel model.
💡 Research Summary
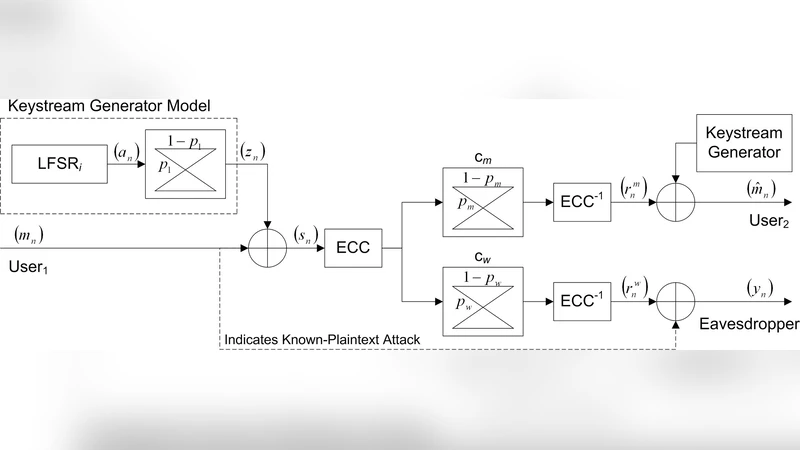
The paper investigates how physical‑layer characteristics can be leveraged to strengthen the security of stream‑cipher systems that use linear feedback shift registers (LFSRs). Building on Wyner’s wiretap channel model, the authors treat the main communication link between legitimate users (channel cm) and the eavesdropper’s degraded link (channel cw) as independent binary symmetric channels (BSCs) with crossover probabilities pm and pw respectively, assuming pw > pm.
A keystream generator composed of M LFSRs combined by a Boolean function is simplified to a single LFSR model for analytical tractability. The correlation between the LFSR output sequence a n and the generated keystream z n is characterized by a crossover probability p1. After applying error‑control coding (ECC) on the transmitted data, the eavesdropper’s residual error probability after decoding is denoted p2. The overall effect on the eavesdropper’s observation y n can be modeled as two cascaded BSCs, yielding an effective error probability
p′ = p1 + p2 − 2 p1 p2.
The attacker is assumed to have a known‑plaintext segment of length N, enabling reconstruction of the first N bits of the keystream (z n). Because of the channel errors, the attacker actually observes a noisy version y n of the LFSR output a n, where each bit is flipped with probability p′.
The authors focus on two fast correlation attacks originally described by Meier and Staffelbach (referred to as Attack A and Attack B). Both attacks exploit the linear relations imposed by the LFSR feedback polynomial g(x) to generate a large set of parity‑check equations. For each observed bit y j, the number of satisfied checks c j^s and the total number of checks involving y j, c j^t, are used to compute a conditional reliability metric p* j = Pr(y j = a j | c j^s, c j^t).
Attack A selects the k bits with the highest p* values, constructs a system of k linear equations in GF(2) that relate these bits to the unknown initial state, and solves it (e.g., via LU decomposition). If the selected bits contain r errors, an exhaustive search over all error patterns of weight ≤ r is required, leading to a worst‑case complexity bounded by
A(k, r) ≤ 2^{H(r/k)·k},
where H(·) is the binary entropy function. The expected number of erroneous bits among the k most reliable positions, denoted \bar r, can be estimated from p′ and the average check degree. As p′ approaches 0.5, \bar r/k → 0.5, and the bound approaches 2^k, i.e., a brute‑force search.
Attack B adopts an iterative belief‑propagation‑like procedure reminiscent of Gallager’s LDPC decoding. Starting from the p* vector, a threshold p_thr is chosen so that bits with p* j < p_thr are flipped. After each flip, the p* values are recomputed using the updated a priori probability. The process repeats until either a sufficient number of low‑confidence bits (N_thr) have been flipped or convergence is achieved. The effectiveness of the attack is largely determined by the first iteration: if p′ is large enough that the fraction of bits correctly identified after the first thresholding is close to 0.5, subsequent iterations provide little improvement, and the attack fails.
The paper provides both theoretical analysis and Monte‑Carlo simulations to quantify how p2 (the residual error after ECC) influences p′ and consequently the attack complexities. For a 32‑stage LFSR (k = 32) and an observed plaintext length N = 10^6·k, the authors show that even modest values of p2 (e.g., 0.1) dramatically increase the expected number of trials for Attack A, pushing it into the range of 2^{30} operations. Similarly, Attack B’s first‑iteration correction probability drops sharply as p′ grows, rendering the iterative decoder ineffective.
The key insight is that by selecting an appropriate error‑control code that guarantees reliable communication for the legitimate users while leaving the eavesdropper with a residual error probability p2 that drives p′ close to 0.5, the physical layer itself contributes a substantial security margin. This margin manifests as an exponential increase in the computational effort required for known‑plaintext correlation attacks, effectively turning a previously feasible attack into an impractical one.
In conclusion, the work demonstrates that physical‑layer design—specifically, the intentional introduction of controlled errors through coding—can be synergistically combined with traditional cryptographic primitives to achieve higher overall security. The analysis bridges information‑theoretic secrecy (Wyner’s wiretap model) and practical stream‑cipher cryptanalysis, offering a concrete methodology for enhancing the robustness of LFSR‑based systems in realistic noisy environments.
Comments & Academic Discussion
Loading comments...
Leave a Comment